Add exception to sophos firewall. Sophos XG Next 2019-02-27
FYI Sophos Cloud Endpoint Installer can be blocked by SonicWALL Gateway AV

Note: Once deployment is complete we recommend you return some settings to their default configuration. This means that you do not see the notification until you view the desktop. This dramatically simplifies enforcement and reduces redundancy and overall rule count. To make a backup of you configuration follow this 6 click flow. You can create exceptions from checks for certain senders and recipients. Use these results to determine the level of risk posed to your network by releasing these files.
Knowledge Base

By adding these restrictions to policies, you can block websites or display a warning message to users. During this process, I visited the site again and it loaded properly. In the real world however, the web application team or vendor might be slow moving, or they might simply refuse to fix it. With synchronized application control, you can restrict traffic on endpoints that are managed with Sophos Central. Quotas specify access on a cyclical repeat or non-cyclical one-time basis and the access time allowed.
Adding Exceptions to your Sophos XG Mail Filter

Steps 6- In the Destination section, select your destination Zone. You can include file types in web policies to control access to files. Data anonymization lets you encrypt identities in logs and reports. You also get rich on-box reporting and the option to add Sophos iView for centralized reporting across multiple firewalls. About this video Step 1- You must be logged in to the Admin Console as an administrator with Read-Write permissions for the relevant feature Step 2- Log in to Sophos Firewall and go to Objects Policies Web Filter or Protection Web Protection Web Filter Policies. This is normally where you take the information to the application team or application vendor, and ask them to investigate.
Sophos XG Next

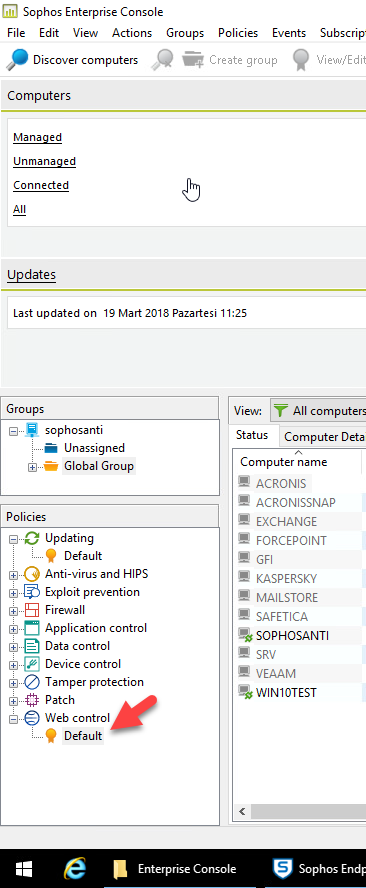
Wireless protection allows you to configure and manage access points, wireless networks, and clients. You might want to allow java. If there is anyone who uses Sophos Endpoint administered from the Enterprise Console. Many of the false positives you encounter will share similarities, but each needs to be treated on its own merits. Thanks for the help and suggestions, and I'm sure they'll come in handy down the road. However, they can bypass the client if you add them as clientless users. The rule table enables centralized management of firewall rules.
FYI Sophos Cloud Endpoint Installer can be blocked by SonicWALL Gateway AV

To work around this problem, install the latest service pack for the operating system. Hopefully, it doesn't block any new install and updates for Sophos Endpoint. No part of this publication may be reproduced, stored in a retrieval system, or transmitted, in any form or by any means, electronic, mechanical, photocopying, recording or otherwise unless you are either a valid licensee where the documentation can be reproduced in accordance with the license terms or you otherwise have the prior permission in writing of the copyright owner. I'm glad I stumbled upon this thread for this. I would also make sure I run this past some sort of governance or risk assessment committee.
Add an exception

Any firewall or proxy administrator who has had to maintain a deployment for any period of time will confirm that the only constant is change. The elements they need to access also tend to vary from site to site. Where are Windows 10 apps located? Not that you will have to click on local a two different points in the process. Managing cloud application traffic is also supported. I recently did that and testing the solution out now.
Error : sophos
Exceptions let you override protection as required for your business needs. User identity-based policies and unique user risk analysis give you the knowledge and power to regain control of your users before they become a serious threat to your network. With Sophos Central you can manage your entire Synchronized Security solution from a single console. I'm going to go through and make some exclusions so we can turn the av back on but I figured it was worth mentioning that this is still an issue. You can open these files and have a look at them and sometimes they contain more details about the vulnerability and sample payloads. Healthy endpoints assist by ignoring all traffic from unhealthy endpoints, enabling complete isolation, even on the same network segment, to prevent threats and active adversaries from spreading or stealing data.
How to block social networking sites sophos XG Firewall
This is applied to the individual firewall profile. This causes Windows to offer the user the ability to re-download and re-install the app. It makes day-to-day setup, monitoring, and management of your network protection easy. Enter a valid email address abc example. If Firewall manager is missing or blank; then we are not managing your system and you should make a backup of your configuration before preceding. In this case, it was determined that the application has the potential to use special characters such as — and! Such exceptions should not negatively affect the overall security because they are too vague or too relaxed. Simply select them from a list, provide some basic information and the template takes care of the rest.
Sophos Endpoint Security and Control 10.2.3 release notes

Using policies, you can define rules that specify an action to take when traffic matches signature criteria. User identity-based policies and unique user risk analysis give you the knowledge and power to regain control of your users before they become a serious threat to your network. The near-infinite options, enable you to apply exceptions without relaxing the security of your general rules. Synchronized Application Control lets you detect and manage applications in your network. Under Malware protection, you can select Malware or Sandstorm. The msg is a brief description of what the vulnerability is. Then you can add the application exception.