Antivirus definition ict. What is a Computer virus? 2019-03-08
What does virus mean in ict
It may destroy files on the hard disk or may send the virus automatically to all email addresses saved in the address book. Malware is short for malicious soft ware. In 1989, in , created the first version of back in 1989 he founded only in 1993. A software that detects other developers anti virus software and declare it as virus. Archived from on March 17, 2012. Key fobs, are used to provide. I spent over an hour with 3 incompetent Kaspersky support techs on the phone, and they finally said to send them a log from one of their programs, and they'd get back to me in 24-48 hours.
What is a Virus?
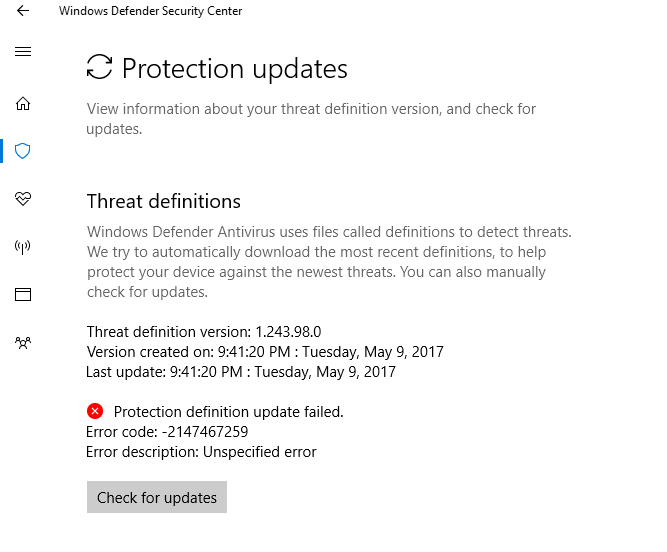
Ransomware is a subset of malware in which the data on a victim's computer is locked, typically by encryption, and payment is. Commercial antivirus utilities have long depended on virus definitions. All definitions on the TechTerms website are written to be technically accurate but also easy to understand. This meant that computers could now also be at risk from infection by opening documents with hidden attached macros. A software that you will pay to give you more virus. Also see and in the section of Webopedia.
What is a Virus?
In 2012 and 2013, antivirus firms reported a new malware samples range from 300,000 to over 500,000 per day. Many viruses are activated on a certain data. If the antivirus software employs heuristic detection, it must be fine-tuned to minimize misidentifying harmless software as malicious. Add My Comment I always run anti-virus software. What are the different types of computer viruses? Direct action virus This type of virus comes into action when you execute a file containing a virus. This includes erasing data or causing permanent damage to your hard disk. Trojan Horses are malignant pieces of software pretending to be benign applications.
Antivirus software

The virus can waste the host's resources, and sometimes destroy or change files. These signatures often contain non-contiguous code, using where differences lie. Rootkit techniques were invented by virus writers to conceal malware, so it could go unnoticed by antivirus detection and removal programs. Copyright © 2019 Symantec Corporation. Retrieved on January 3, 2017. It does this to evade antivirus programs. How does a computer virus find me? In the process, a virus has the potential to cause unexpected or damaging effects, such as harming the system software by corrupting or destroying data.
Teach

If this file is copied to a computer, virus is also copied to the computer. You may become aware of the unfamiliar program when you start your computer. Researchers at antivirus firms study viruses found commonly on the internet, often testing their behavior in a -type set up. . In the same period, in Hungary, also was founded which has recently being incorporated by.
Antispyware
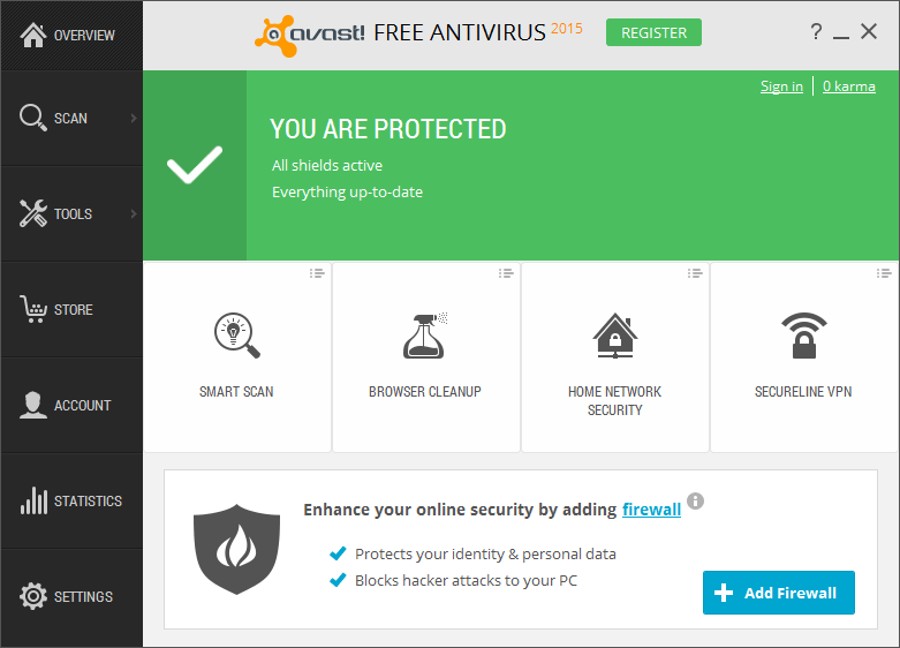
As practical as online shopping and banking are, they also opened a world of opportunities for economic exploitation of both corporations and the ordinary computer user. While some viruses can be playful in intent and effect, others can have profound and damaging effects. In 2008, , of , stated that the anti-virus industry has over-hyped how effective its products are — and so has been misleading customers — for years. Basically malware is software that you really don't want to have on your computer! How antivirus software works Antivirus software typically runs as a background , scanning computers, servers or mobile devices to detect and restrict the spread of malware. How to remove computer viruses You can take two approaches to removing a computer virus. Infected Flash Drives or Disks Flash drives and disks are the main cause of spreading viruses. But since, as we mentioned, most malware regularly morphs in appearance to avoid detection, Webroot works differently.
Computer viruses

A criminal may take control of your account or send emails in your name from another infected computer. A computer virus resides on a host computer and can replicate itself when executed. Such viruses spread when you open an infected document, often through email attachments. While it may be advantageous to identify a specific virus, it can be quicker to detect a virus family through a generic signature or through an inexact match to an existing signature. This was the de facto industry standard virus killer for the and , the last version of which version 9. However, signature-based detection does not usually produce false positive matches. When a user downloads a file infected with virus from the internet, the virus is copied to the computer.
What is Antivirus Protection
On the other hand, in , founded in 1988 by Petri Allas and Risto Siilasmaa — with the name of Data Fellows released the first version of their antivirus product. Instead of storing examples of recognized malware on your device, it stores malware definitions in the. In order to scan systems comprehensively, antivirus software must generally be given access to the entire system. When we see something like that usually we advise to reinstall the operating system or reinstall backups. One approach to implementing cloud antivirus involves scanning suspicious files using multiple antivirus engines.
Antispyware
A computer system can be protected from virus by following these precautions. This is a general name for the computerised tills that you see in shops and supermarkets. Furthermore, inexperienced users can be lulled into a false sense of security when using the computer, considering themselves to be invulnerable, and may have problems understanding the prompts and decisions that antivirus software presents them with. A computer virus attack can produce a variety of symptoms. The other is by enlisting the help of a reputable antivirus program. Journal of Intelligent Information Systems.
Teach

The antivirus software uses these signatures to identify when it encounters viruses that have already been identified and analyzed by security experts. Archived from on May 12, 2011. You'll then be bullied with endless pop-ups into paying a fee to have your computer 'disinfected'. A resident virus can execute anytime when an operating system loads. Finally, at the end of 1987, the first two antivirus utilities were released: Flushot Plus by and Anti4us by Erwin Lanting. Some new viruses, particularly , use to avoid detection by virus scanners.