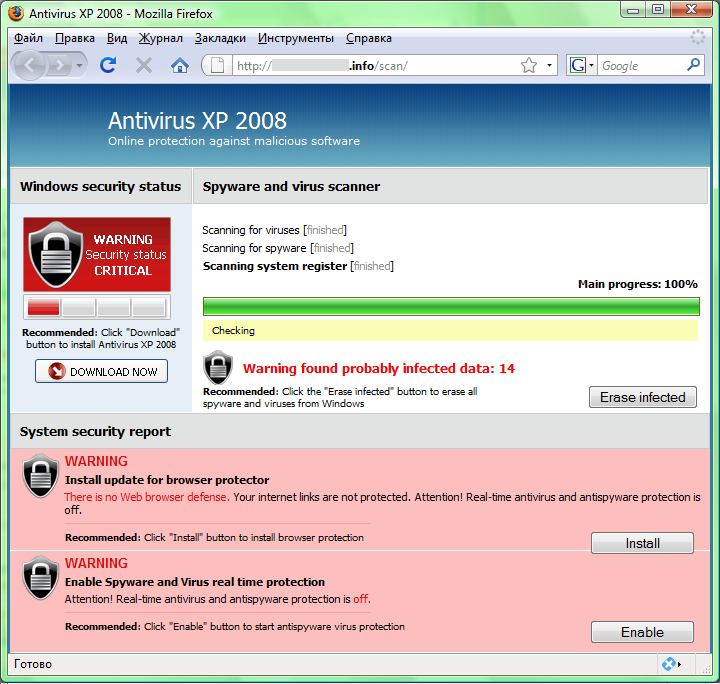
Antivirus xp 2008. Don't Try Removing Antivirus XP 2008 Until You Read This 2019-04-07
Remove XP Antivirus 2008 (Removal Guide)
Begin the removal process by uninstalling the rogue program from Windows. The Properties tab is no longer available - gone, not just greyed out. When you do, you will do things that will cost you time, money and possibly some files on your computer that you inadvertantly erase thinking they are the problem. Now click on the Protection tab at the top of the screen. Update: Revised instructions to include folder deletion. This, it seems, is the only way to rid yourself of your computers gremlins. Each specific level is relative to the threat's consistent assessed behaviors collected from SpyHunter's risk assessment model.
McAfee Support Community

This guide contains advanced information, but has been written in such a way so that anyone can follow it. This is the best solution. Doesn't that mean they are running again? It may be that this web site is blocked also - if so I can pop it up somewhere and post a link here. Install Antivirus An anti-virus is essential in keeping your computer safe while surfing the Internet. The overall ranking of each threat in the Threat Meter is a basic breakdown of how all threats are ranked within our own extensive malware database. Everyone else suffering with this virus should ignore all other posts and download and run Malware Bytes.
Remove Antivirus XP 2008 (Removal Guide)

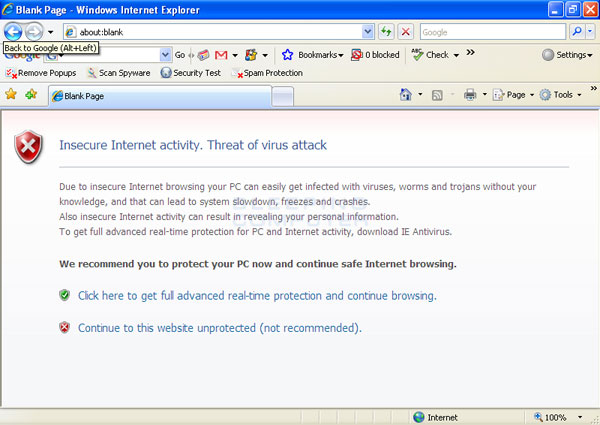
To start in Safe Mode, turn your computer off and the back on. I dont see the ad's as my host file blocks them, but i'm sure they are there. You may require a restart. To enable protection from dangerous sites, please do these steps: 1. The Threat Meter is able to give you a numerical breakdown of each threat's initial Threat Level, Detection Count, Volume Count, Trend Path and Percentage Impact.
Don't Try Removing Antivirus XP 2008 Until You Read This
Does anyone have a solution for the restricted website access? However, the likelihood of an Apple Macintosh user getting a virus when compared to a Microsoft Windows user is very little to none. Unfortunately, I was unable to logon to Windows at all. First, in the Start menu, click on Run. . Up arrows represent an increase, down arrows represent a decline and the equal symbol represent no change to a threat's recent movement.
How to remove Antivirus XP 2008
I would much rather clarify instructions or explain them differently than have something important broken. It was an endless cycle of logon, logoff and restart. In the middle of that tab's window you'll see a Screen Resolution option, most likely set to 800x600. Accessing Control Panel in Windows 8 and Windows 10 - On your keyboard, Press Windows Key + X. When your presented with the list of detections make sure everything is checked and click remove selected, rebooting immediately if prompted. My last resort is going to be a full recovery, but I was hoping to avoid that. Zlob may hijack browsers, display pop up ads and disable key system functions.
Remove Antivirus XP 2008 (Removal Guide)

Thanks to clear me about Leave a Reply. Infact, I cannot go directly to any antispyware or antivirus sites. When it has finished it will display a list of all the items that Hitman has found as shown in the image below. I also went through and forced all the menioned processers to stop so that i could do this. This is very easy to remove. The computer would automatically logoff.
Antivirus 2008, Antivirus 2009, XP Antivirus 2008, & Others Infect Winlogon
If you download and install Hijack-This from Trend Micro, there is a. If you have any questions about this self-help guide then please post those questions in our and someone will help you. A screen will appear that asks you to chose the start-up mode. Thanks in advance, P Neeel1 wrote: Mmmm, sounds good, but nice old Antivirus has this on its list of banned websites. At this screen you should click on the Next button and then if prompted you should click on the Reboot button. Please note that the download page will open in a new browser window or tab.
Remove Antivirus XP 2008

After doing so, please print this page as you may need to close your browser window or reboot your computer. Do you have any idea on how to fix that problem? When program launch, it will run a command prompt to initialize, prepare components, and update the program. Locate Privacy section and mark ' Protect you and your device from dangerous sites'. You will now be shown the settings MalwareBytes will use when scanning your computer. It is a memory editor and an integrated debugger, created specifically for cheating in games, although it may be used for various purposes.
How to remove Antivirus XP 2008
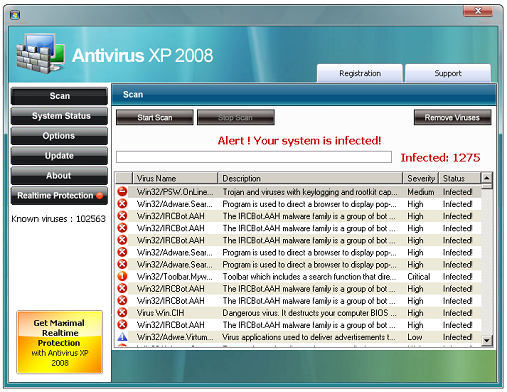
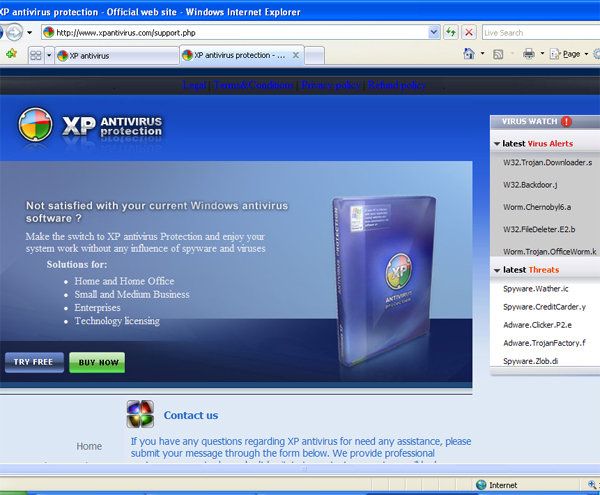
If you would like help with any of these fixes, you can ask for malware removal assistance in our. I managed to get rid of the offending spyware by a combination of the following, all of which can be obtained free of charge. I'm suprised that there's been nothing in the media about this. The scoring for each specific malware threat can be easily compared to other emerging threats to draw a contrast in its particular severity. Mostly, the trojan variations' lock users out of their computers and has several rogue anti-spyware programs appear in a continous loop. It will open a Program and Features window where-in you can uninstall, change, or repair installed software.
Remove XP Antivirus 2008 (Removal Guide)
Viruses, worms, trojans, spyware, adware, and other malware typically spread through one of a few vectors: 1 email… Most computers beep on loading just as they're powering up. When it does restart, I get an error saying its missing a vbs file. This xp 2008 thing autoruns and cannot be deleted. Oh, and by the way, there is now an Antivirus 2009 which I dealt with yesterday. Authors of this fake antivirus see to it that victims will spend money before it can be take out of the system. MalwareFox will detect all the infections in the computer system and list all the threats.