Atomic rar password recovery crack. Atomic RAR Password Recovery 2019-01-16
Fsx gold edition rar password trend: Atomic RAR Password Recovery, RAR Password Recovery, RAR Password Recovery Magic

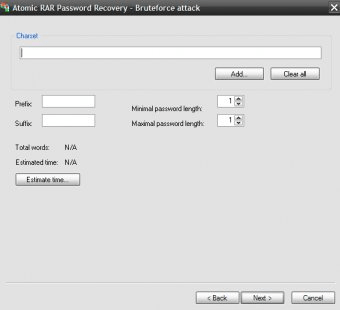
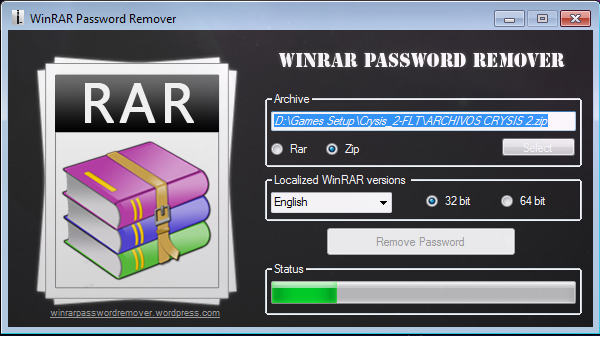
For the Cyclopes have no ships, nor yet shipwrights who could make ships for them; they cannot therefore go from city to city, or sail over the sea to one another's country as people who have ships can do; if they had had these they would have colonised the island, {78} for it is a very good one, and would yield everything in due season. Cara ini memang cukup lama, apalagi jika password yang ada di dalam file rar tersebut cukup panjang. All informations about programs or games on this website have been found in open sources on the Internet. The program fully supports using masks and dictionaries. The speed of the password search depends on the archive version. Two possible ways of recovery The first way of password recovery is a brute-force attack, where the lists of passwords using all available symbols will be checked one by one. It has a wizard which helps you to find the password in the fastest way.
Download Atomic RAR Password Recovery 17.1
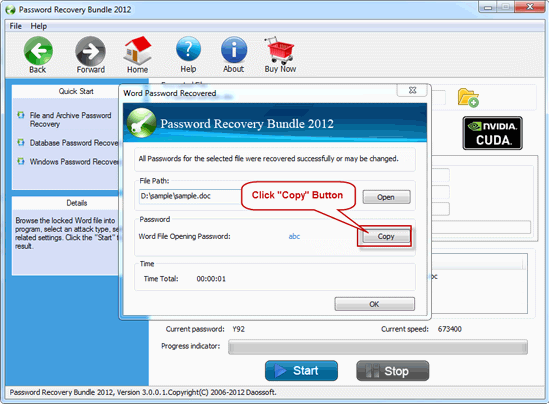
All trademarks, registered trademarks, product names and company names or logos mentioned herein are the property of their respective owners. The rate of this password search varies according to the archive version. Brute-force attack can be used if your password is less than say 5 characters, otherwise, password recovery can take months! You should use Dictionary attack. All this power comes with a surprisingly simple interface. You may define the charset, minimal and maximal lenght of the generated passwords. This option is recommended if you are sure that the password is the simple work. Under the Dictionary attack all provided passwords are checked.
Atomic Zip Password Recovery 2.70

The free dictionaries are available on our site. The actual developer of the software is AtomPark Software. Step 4: Dictionary or Bruteforce attack if Dictionary attack. The program is able to save a current state you can interrupt the program at any time, and restart from the same state later. The program allows for a current state of attack to be saved and resumed at a later time.
Atomic RAR Password Recovery (free version) download for PC

It's slow method, but only it can guarantee the password recovery. Tetapi tentunya semakin banyak karakter dari sebuah password, maka software ini juga akan semakin lama untuk menemukan password dari file rar tersebut. The program lies within Security Tools, more precisely Privacy. The program's installer files are commonly found as AtomicRarPasswordRecovery. If your password is a known word not name or so then there is a way out. Thus, it comes in particularly handy when you forgot the password you used to secure a given file.
RAR Password Cracker

It uses a wizard to let you configure the cracking process. All programs and games not hosted on our site. In fact, the longer your password is, the longer it takes exponentially! It can also be used to view web pages and download videos. Reports are provided by an industry leading antivirus aggregator. However, once it happens, Extra An additional dictionary worth trying ready-to-use unzipped plain-text, 133 MiB : Copyright © 2019 dnSoft Research Group. The method to find the password is the brute-force attack.
Download Atomic RAR Password Recovery 17.1

Our antivirus check shows that this download is safe. According to our tests, the program found these combinations: passwords with all small letters, all capital letters, all numbers, and all symbols up to five characters. The tool is quite easy to use even if you do not have any previous experience. This application features brute-force attack, brute-force with mask attack, etc. The automatic mode enables Atomic Zip Password Recovery to use standard settings to find a password, but these can be configured in manual mode.
Atomic RAR Password Recovery (free version) download for PC

A Must For All Jewelry Professionals, Consumers, Pawnbrokers, Jewelers, Refineries, Investers, Laylmen. Both of them have varying degrees of success depending on a few factors. This site is not directly affiliated with. It crack rar password with three powerful attack types: Brute-Force Attack, Dictionary Attack and Brute-force with Mask Attack. This method is best to be tried out when the password is a common name or object since it's a big possibility the password will be in the dictionary wordlist. Mungkin anda pernah mendownload file rar dari internet, tetapi ternyata setelah anda selesai mendownloadnya dan ingin mengekstraknya, file rar tersebut diberi password.
Fsx gold edition rar password trend: Atomic RAR Password Recovery, RAR Password Recovery, RAR Password Recovery Magic
Then Sir Tristram reposed him there till that he was amended of his sickness; and when he was big and strong they took their leave, and every knight took their horses, and so departed and rode together till they came to a cross way. You may pause or terminate the search here. It's in fact a password cracker that lets you choose to use one of the three available methods to retrieve the passwords. We can only assume it automatically used a dictionary for the found keys, and that it cannot handle more powerful encryption combinations. How he passed the doctor was a mystery to us, he must have bluffed his way through, because he certainly was independent. It also found one password with small caps and letters i.
Atomic RAR Password Recovery Download
Preparations were already making to execute the sentence, when the soldier, who gave himself up for lost, formed the desperate resolution of not dying without revenge. Apalgi jika file yang kita download tersebut adalah file yang berukuran besar. Dictionary Attack enables you to add dictionaries and specific words that it can test for and select case transformations as is, lower and upper, all combinations. The speed of the password search depends on the archive version. Estimated time calculator allows you to configure the program more carefully.
Atomic IE Password Recovery 1.20 Free Download
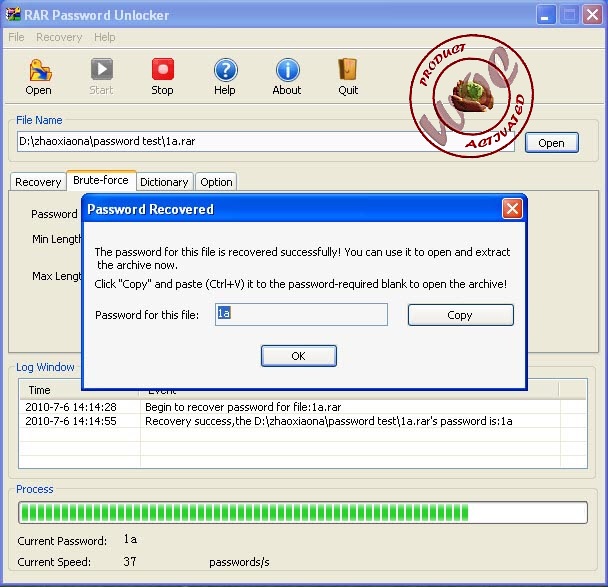
She hoped so, for atomic rar password recovery crack download was getting rather tired and hungry, and until she reached the gypsies there was no definite prospect of bread and butter. The second way of decripting the password is using a dictionary wordlist attack. The software took only several minutes to find those passwords in default settings, and default + user defined settings for the password with special symbols , while using minimum system memory, and it did not pop up any errors. There are no special requirements for memory capacity, but the processor performance should be as high as possible. It has a wizard which helps you to discover the password in the way in which that is fastest. The duration of password decryption depends on the length of the password and usually takes longer if the password exceeds 5 characters and is not a common name, object or place.