Avast secureline vpn.avast vpn. Avast Secureline VPN Review [UPDATED May. 2019] 2019-05-08
VPN AVAST SECURELINE

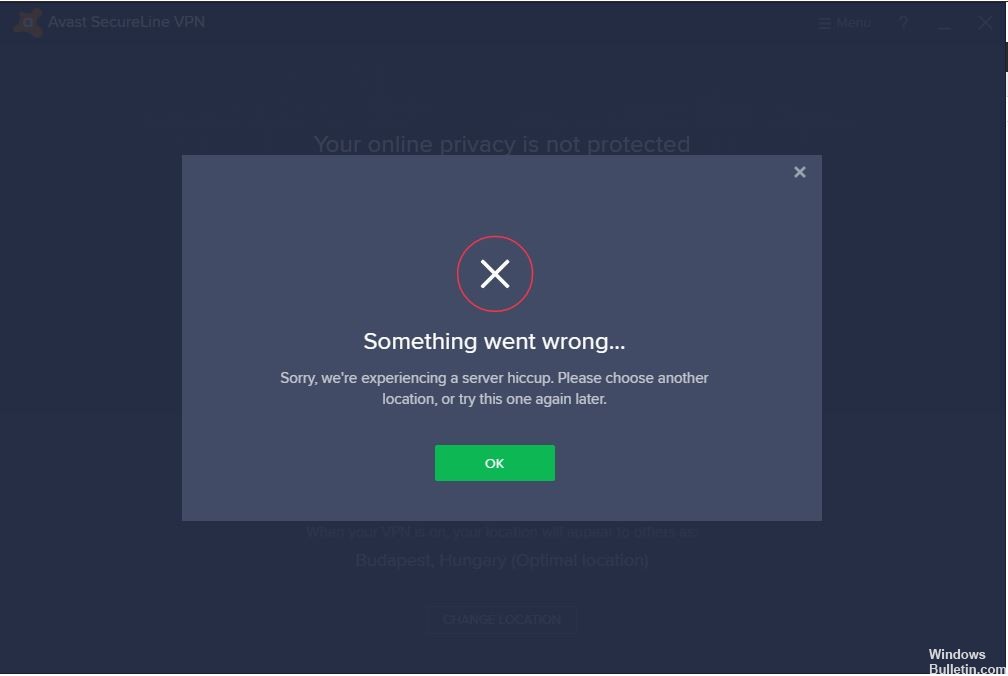
I just signed up for one month to test it. The cutting edge Symantec network stops you from unknown visiting dangerous and false websites. Additional Notes Although we have used Avast Free Antivirus 2019 screenshots in this article, these steps are also applicable for all Avast Antivirus solutions i. The one thing that bothers me now is that they may give out information and that they store our information. As it is now, it is strongly recommended to look for other cheaper and better alternatives to SecureLine.
Avast! Secureline VPN Review

This excellent tool is very simple and easy to access support. Perhaps sometime in the near future when it is revamped and improved, we might consider the tool. It also enhances your security as the whole connection is encrypted, so no one can steal your personal information or see what you are doing. The privacy policy reveals that use of the service is covered under California law, which is less than ideal. I wish i would stay connected so you would not have to log into every time. Bitcoin is an option for users looking to protect their payment information, as they can use the cryptocurrency to pay for their subscription.
avast secureline vpn license key till 2021 + Cracked {Latest}

A secure connection without leakage established. This growing technology prevents the phishing scams or stops the keyloggers from stopping your information. This permits you to browse openly, even from nations with web restriction. Unfortunately, the company does not offer the possibility of paying with cryptocurrencies such as BitCoin. It Is Cracked Without any serial key, license file or crack.
Download Avast SecureLine VPN 5.2.429.0 for PC Windows
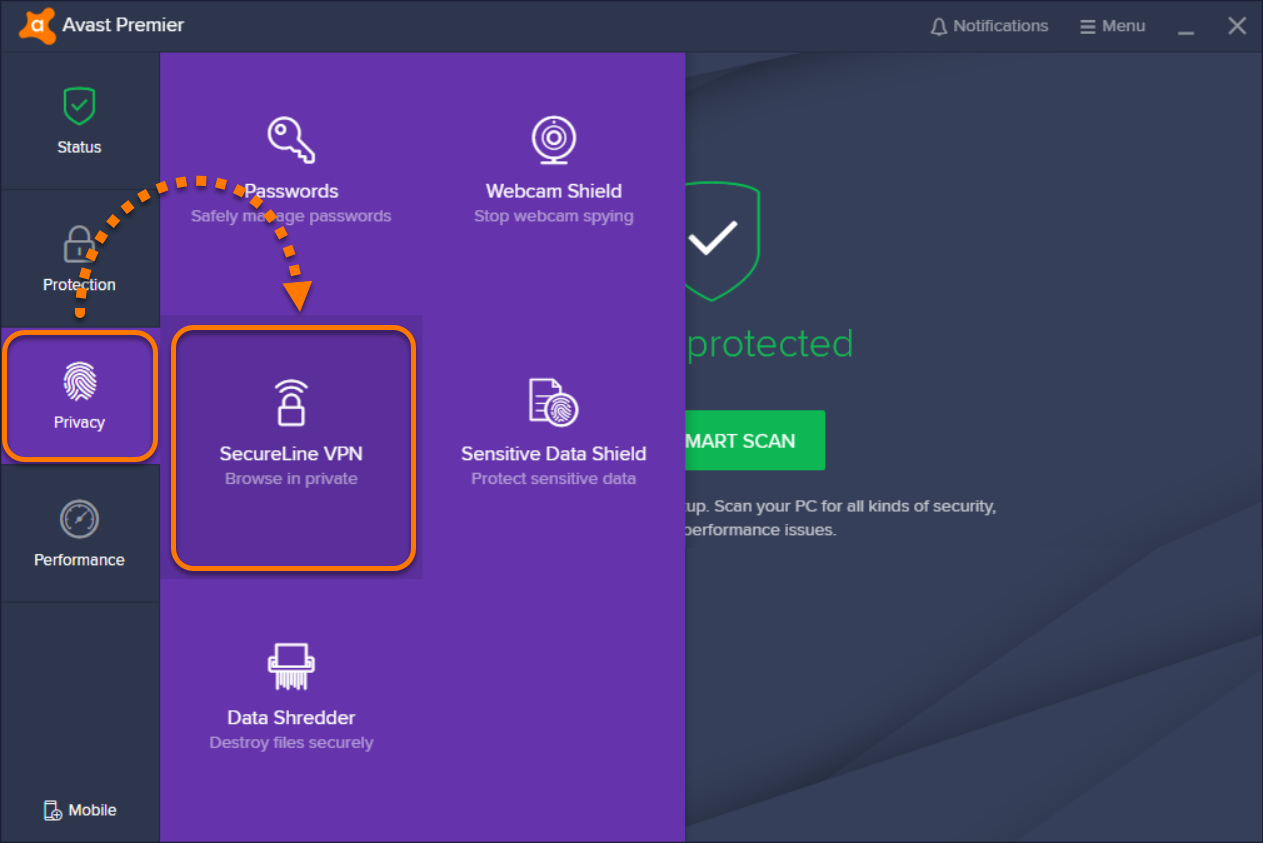
See the pricing listed above. You basically only select the server country, city to which you want to connect and click on connect or switch. On the other hand, it does pack everything necessary and brings you extreme ease of use. So there is no need to actually use Avast antivirus, you can either use both or one of them. A kill switch really is a critical safeguard because if Avast SecureLine detects your network connection will terminate, the app automatically kills your current session as well. That means you have to pay for the calls, and we all know technical troubleshooting by phone can take a while.
Avast SecureLine VPN 5.2.429 License File Till 2021 Full Crack

Most typically the one when you are connecting to the unsecured public WiFi network. Before publishing each review, our team checks whether it was submitted by an actual user in an effort to prevent false or spammy reviews. The number has been updated just in December 2017, when to its server list. Browse 100% anonymously, or make websites think you're someplace else to get around pesky region locks. I recently started using this service.
Avast Secureline VPN Review [UPDATED May. 2019]
See our review, if that is what you need. The client takes up a lot of space on your screen, considering how little information it contains. Sometimes you may need to dig deep for answers, but the search field makes it easier to find what you need. On the other hand, it doesn't offer many server locations or advanced features. It is a hurdle through which users must pass through first before users can connect to their company database away from their homes. Its clean, minimalist interface makes it easy to use and simple to operate. Grateful with a kind response from you.
Avast SecureLine VPN 2019 for Windows — Review & Test

In particular, make sure to check out if you are concerned about online privacy. It secures the operating system. It really is an excellent product. It scans for Internet-enabled apps and performs access that rules based on a database managed by Symantec during installation. This is encrypted, which means that it is inaccessible to others who might intercept or listen on the connection.
Free Download of Avast SecureLine VPN License File & Key

Bringing you the , , , , , and much more. You can send an email to their billing support or technical support via the ticketing system and get an instant confirmation. A single license allows you to use it on 5 devices of the same kind simultaneously. Nowadays you use it entirely for free for 30 days. It is capable of recovering the data from missed partitions and damaged volumes.
Avast SecureLine VPN 5.2.429 License Key Full 100% Working {2019}

For purchases made via these links, we earn commissions that allow us to keep producing helpful content. This information is routinely deleted within 30 days. However, these connections are not immune to other electronic threats such as Virus, Malware and Network Attacks. See our , for one example. We constantly update the content on our website, keeping it fresh and relevant to our readers at all times.