Avast wannacry warning. WannaCry: Everything you need to know about the global ransomware attack 2019-01-29
Warning: Massive Ransomware campaign launched

The Chinese version contains content not in any of the others, though no other notes contain content not in the Chinese. At this point in time, nobody really knows for sure. Other experts also used the publicity around the attack as a chance to reiterate the value and importance of having good, regular and , good including isolating critical systems, using appropriate software, and having the latest security patches installed. A Broad Scope The software mainly targeted business networks, although there were many instances of personal computers falling victim. I'm nasdaq and will be helping you.
COMPUTER HACKED? IT MAKES YOU WannaCry, DOESN’T IT?
Lastly, remember that computer security is a layered approach, so it is a combination of Antivirus, A good Network Firewall, and most importantly user training. On top of that, we are flagging it at multiple layers, even on day one! As it turns out, a majority of anti-virus and security products made for Windows users also forgo these useful security protections. If I missed the post with the solution, please provide a link. Visit our for more information! Last week saw what has been described as the single worst ransomware attack in history. How can I protect myself from WannaCry? Avast helped protect hundreds of thousands of users from the threat, and have committed to preventing similar attacks in the future.
Petya ransomware

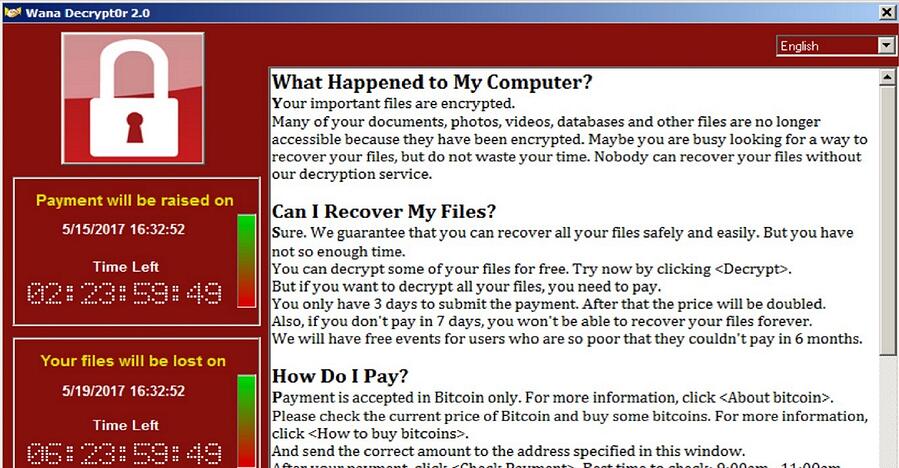
Registering a for a stopped the attack spreading as a worm, because the ransomware only encrypted the computer's files if it was unable to connect to that domain, which all computers infected with WannaCry before the website's registration had been unable to do. Programs that have never been seen before are nearly always given more scrutiny, but they also are a frequent source of false positives. Hopefully affected users have backups of their data available, because the only other option right now that is known to work is to follow the instructions offered in the software to pay the ransom. If you were unlucky enough to fall victim to the attack, WannaCry will most likely demand a certain amount of money in exchange for your files. Make sure you use an antivirus, as this will help detect any suspicious activity on your computer. Avast will protect you with or without a patch.
Today Avast detected Wannacry in my Laptop, what now? : antivirus

The first time the tool is run, it makes also another log Addition. Posting about Sales, Beta's, that sort of thing is Allowed, but don't spam it. In an interview with KrebsOnSecurity, Sharov said Dr. Chinni somberly read aloud a few of the entries in the event viewer marked with yellow exclamation points, saying they were signs that my computer could have a problem. This is by far the biggest outbreak we have seen to date. Within four days of the initial outbreak, new infections had slowed to a trickle due to these responses. Avast Commit to Defending Against Ransomware Following Huge Attack The software represents a worrying development in the world of ransomware, in the fact that it operates as a worm.
AVAST! — Krebs on Security
Avast, however, have suggested that this is a mostly empty threat, and WannaCry is unlikely to delete any files. Could you please check what your system says about that? Where does Petya come from? Design by and This web site is designed for general information only. It is based on evidence. Starting from 21 April 2017, security researchers reported that computers with the DoublePulsar backdoor installed were in the tens of thousands. The makers of Avast antivirus software are warning users about a new scam involving phone calls from people posing as customer service reps for the company and requesting remote access to user systems. I recently highlighted a study which showed that most of the top software applications built into Microsoft Windows that can help block attacks from hackers and viruses. Several organizations released detailed technical writeups of the malware, including Microsoft, , , and.
download : Avast Premier 2017 Crack + License Key Full Version Till 2050

My post was concerning Barkly. In particular, there have been reports that victims of WannaCry who paid the ransom are not getting their data back. It affected a range of countries, mainly Russia where more than half of the reported cases took place , Taiwan, and Ukraine. There were no exploit kits or the other more usual delivery methods. It remains unclear exactly how this ransomware strain is being disseminated and why it appears to have spread so quickly, but there are indications the malware may be spreading to vulnerable systems through a security hole in Windows that was recently patched by Microsoft. Trend Micro Worry-Free Business Security Services and Trend Micro Worry-Free Business Security Services Advanced both cloud-managed vs. The WannaCry code can take advantage of any existing DoublePulsar infection, or installs it itself.
Updating Windows to fix the EternalBlue vulnerability and prevent the DoublePulsar attack

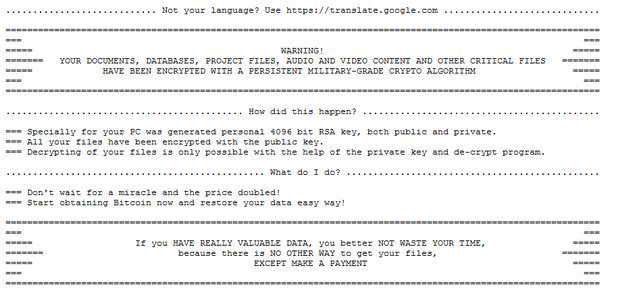
The move comes just one day after by KrebsOnSecurity. The key is to reduce your chances of getting hacked to begin with. Even if they are patched. Pardon if I missed an earlier discussion on this particular aspect of Wannacry. The ransom note left behind on computers infected with the Wanna Decryptor ransomware strain. Avast antivirus technology detects and removes Petya ransomware, as well as other kinds of malware. Then on Friday, we increased the protection level for this specific threat via updates to our detection engine.
WannaCry ransomware attack

Bossert said that Canada, New Zealand and Japan agree with the United States' assessment of the evidence that links the attack to North Korea, while the United Kingdom's says it also stands behind the United States' assertion. I think most of us would prefer a single product that covers all forms of malware without the need to purchase additional modules. You should disable the file sharing on your computer and block the incoming traffic on port 445. Your best hope is recovering your files from a backup, if possible, but first you have to clean and update your computer. After that, the price doubles. The most affected country in that attack was Ukraine, with the Kiev metro, the Ukrainian National Bank and several airports as some of its highest profile targets. In December 2017, the , and formally asserted that was behind the attack.
Updating Windows to fix the EternalBlue vulnerability and prevent the DoublePulsar attack

I installed all the important ones and several of the optionals and, after several reboots, I installed and ran Avast Free. This unprecedented malware attack began sweeping the globe late last week, and security researchers estimated that nearly 57,000 computers in more than 150 countries were infected by the end of the day on Friday. One of the largest agencies struck by the attack was the hospitals in England and Scotland, and up to 70,000 devices — including computers, , blood-storage refrigerators and theatre equipment — may have been affected. I wanted to see whether I, too, would receive follow-up sales pitches. If you are too small of an operation to have 10 devices, look for the home grade products and you will be just fine. On 19 May, it was reported that hackers were trying to use a botnet variant to effect a on WannaCry's kill-switch domain with the intention of knocking it offline. Archived from on 27 May 2017.
COMPUTER HACKED? IT MAKES YOU WannaCry, DOESN’T IT?

If it was, then t2tech is misinformed because we have Small Business products like Worry Free Services that offer tools to help protect from ransomware and can be purchases for a few as 1 device. I just bought Trend Micro Worry-Free Business Security Services Advanced for a new client and connected its Cloud App Security to Office 365. An equivalent scenario with conventional weapons would be the U. Security experts believed from preliminary evaluation of the worm that the attack originated from North Korea or agencies working for the country. This approach was iterated upon by a second tool known as Wanakiwi, which was tested to work on Windows 7 and Server 2008 R2 as well. On 22 May, Hutchins protected the domain by switching to a cached version of the site, capable of dealing with much higher traffic loads than the live site. I'd have to imagine the above is true for most security software vendors.