Best brute force dictionary. Brute Forcing Passwords and Word List Resources 2019-03-11
Best brute force password cracking software? : hacking

Find out the dangers of malicious file uploads and learn six steps to stop file-upload attacks. Download L0phtCrack from this link: Ophcrack Ophcrack is another brute-forcing tool specially used for cracking Windows passwords. It also has a distributed mode that lets you perform attacks from multiple computers to attack on the same password hash. It was demanded, as a condition to restoring normal relations, that Japan sign an agreement with various other nations who had never before been party to the negotiations, including Thailand and Soviet Russia pp. I'm pretty picky about what goes into this list 3.
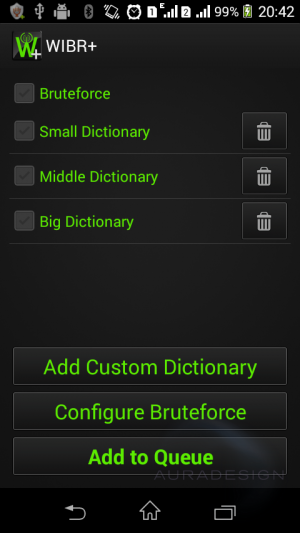
6+ Best Brute Force Software Free Download for Windows, Mac, Android

Japan agreed, repudiating the Tri-Partitite Pact pp. Besides, extracted data is going to be available in the form that would be compatible with the L0phtcrack. And of course there's also WordNet. There are two types of passwords. Download link: Brutus Category: Tools for Password cracking Cost: Free Released back in the year 2000, Brutus is known to be a fast and flexible software that is being used for remote password cracking.
Brute

Brute force attacks involves repeated login attempts using every possible letter, number, and character combination to guess a password. Essentially, this is a utility tool for the recovery of the password, and this is done with great ease. It is used to get a password for unauthorized access or to recover a forgotten password. © 2018 Mobile Spy Free - SpyAdvice. Compatible with all Operating Systems? However, for offline software, things are not as easy to secure. Download link: Bonus tip — How hackers crack the passwords Undoubtedly, nowadays we have to stop relying on traditional passwords — especially the companies. Where do you get them? Success depends on the set of predefined values.
Dictionary Brute Force

Japan gave the Americans permission to publish the text of the repudiation p. The pre-computed dictionary need be generated only once, and when it is completed, password hashes can be looked up almost instantly at any time to find the corresponding password. A more refined approach involves the use of , which reduce storage requirements at the cost of slightly longer lookup-times. Stolen Password When an attacker desires to target an individual, he, first of all, checks if the target user uses credentials that were stolen from any other site already. It is available for both Windows and Linux and supports all latest versions of these platforms. Brutus One of the widely used remote online tools used for password-cracking is Brutus. Mean, it can perform simultaneous attacks where you can crack passwords of multiple email accounts for example at a time rather than just one.
Brute
A pro version of the tool is also available, which offers better features and native packages for target operating systems. It analyses wireless encrypted packets also then tries to crack the passwords with cracking its algorithm. Download John the Ripper from this link: Rainbow Crack Rainbow Crack is also a popular brute-forcing tool used for password cracking. The most notable thing is that the tool is only available for Windows platforms. Com Professional from Christ University, Bangalore. You can crack a password within a couple of minutes with it; thanks to its strong incremental and dictionary attacks.
Brute force

A heart attack occurs when blood flow to a part of the heart isblocked, usually by a blood clot. After computation, results are stored in the rainbow table. He likes to find vulnerabilities in websites and playing computer games in his free time. The good thing is that there are various organizations, which already published the pre-computer rainbow tables for all Internet users. L0phtCrack download link: ophcrack Category: Tools for Password cracking Cost: Free Ophcrack is one of the top rainbow-tables based password cracker. Is can handle varying tasks. It supports various attacking methods including Mask attack, Dictionary attack, Hybrid attack and Attack with Rainbow tables.
What are the differences between Dictionary Attack Brute Force Attack and Hybrid Attack
It claims to crack around 10 million passwords per second on a good computer. Roosevelt wished to import rubber, tin, etc from the South Pacific, supplying the British in the Near East with meat, wheat, corn, troops, and military supplies pp. Credential recycling is another type of brute force attack that reuses usernames and passwords from other data breaches to try to break into other systems. Not if an attacker knows what they're doing. Have a combination of small characters, capital letters, and special characters. This method of password cracking is very fast for short length passwords but for long length passwords technique is normally used. The oil embargo meant the destruction of Japan's independence and perhaps survival as a nation.
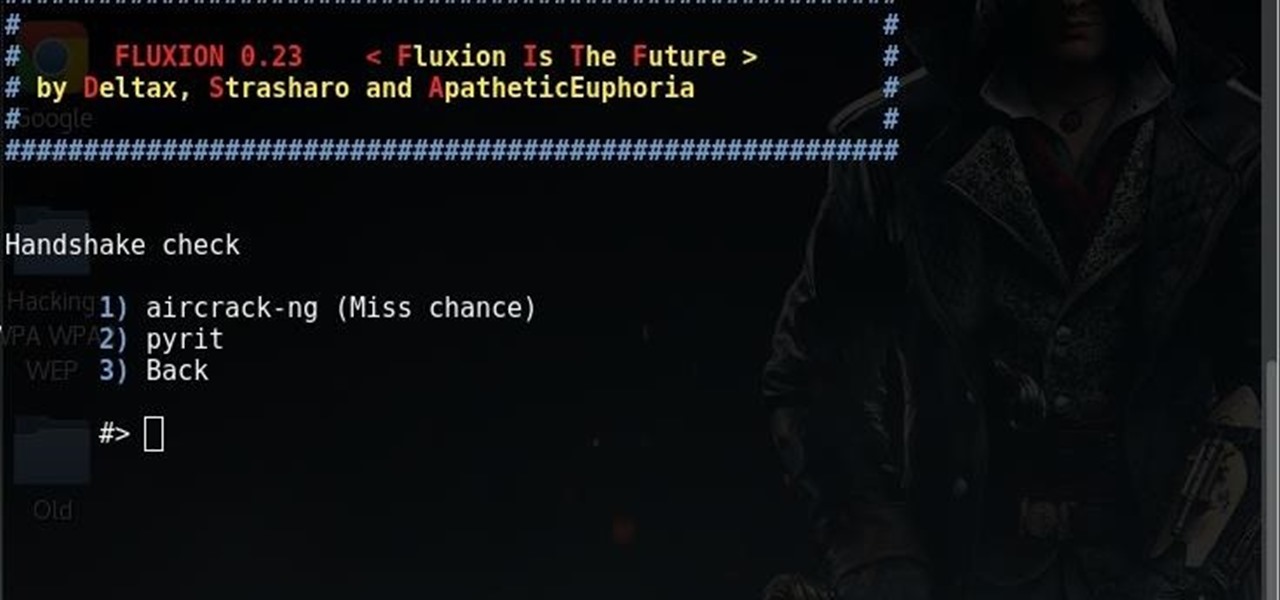
Popular Tools for Brute

Please note that you will need to learn commands before using it since Medusa is the command line tool. Secondly, if you are using the service for its intended purpose it is not wrong and you've probably got little to no idea if it's bad. That is assuming the drive is not encrypted. Moreover, it handles fake access points, de-authentication, and replies to attacks using the packet injection. When a hacker's objective lies beyond their reach thanks to good cybersecurity practices such as password rules and encryption, they might turn to another method: Brute force. No, you will need to pay for it — but it has a free trial though.
Difference Between Brute Force & Dictionary Attack

Ophcrack is completely free to download, Windows based password cracker that uses rainbow tables to crack Windows user passwords. Pre-computed dictionary attacks are particularly effective when a large number of passwords are to be cracked. Brute-force attack when an attacker uses a set of predefined values to attack a target and analyze the response until he succeeds. Anomalies can be a login from a new machine, location, multiple failures when login from another device. The American embargo applied to foodstuffs, including rice, tea, soy beans, wheat flour, fertilizer, fodder, edible fats and seeds pp. I tried to list only a few of the best and most popular tools. Brute force is a technique that is used in predicting the password combination.
10 Most Popular Password Cracking Tools [Updated for 2018]

Ready to get ahead of brute force attacks? If the password changes during that time frame, the attacker will need to start over. It can help in cracking various kind of passwords by performing brute-forcing attacks, dictionary attacks, and cryptanalysis attacks. Ethical Hacking Boot Camp — Exam Pass Guarantee Conclusion Brute-forcing is the best password cracking methods. Both anxiety and panic attacks are treatable with medications and Cognitive Therapy learning tools to control your negative thought patterns. RainbowCrack It falls in the hash cracker tool category that utilizes a large-scale time-memory trade off process for faster password cracking compared to traditional brute force tools.