Bittorrent protocol wiki. SampleCaptures 2019-03-13
BitTorrent protocol encryption : Wikis (The Full Wiki)
That's it for handshaking, next comes an alternating stream of length prefixes and messages. This is usually done in the form of a hyperlink from the website of the content owner or through indexing websites like or. After the file is successfully and completely downloaded by a given peer, the peer is able to shift roles and become an additional seed, helping the remaining peers to receive the entire file. The first byte of the bitfield corresponds to indices 0 - 7 from high bit to low bit, respectively. Thanks Does anybody out there have pcap files with the following? Before announcing or scraping, you need a connection-id must be valid for at least two minutes.
Company
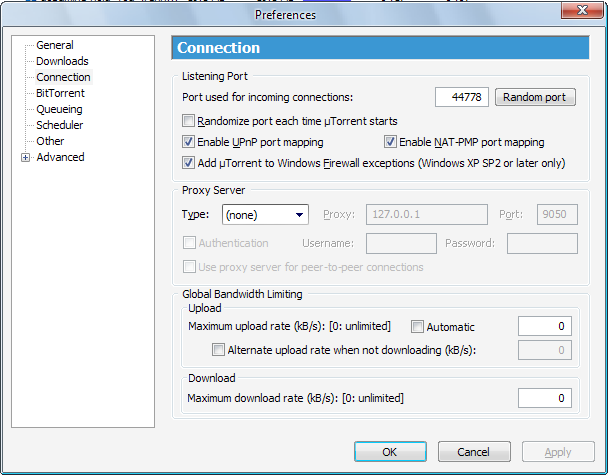
To work with people, industries and nations to create better ways to move information. Note that the examples uses port number 24209, which must be configured in the protocol page. However, this protection, theoretically, comes at a cost: downloads can take time to rise to full speed because it may take time for enough peer connections to be established, and it may take time for a node to receive sufficient data to become an effective uploader. In general, although encryption can make it difficult to determine what is being shared, BitTorrent is vulnerable to. Current versions of the official BitTorrent client, µTorrent, BitComet, Transmission and BitSpirit all share compatibility with. This potentially allows the Azureus client to reach a bigger swarm.
Implementing Bittorrent Protocol
Specifically, and formerly known as Democracy Player support automatic processing of. Overview The BitTorrent Protocol shares files through a P2P network that allows for higher download speeds at lower bandwidth. A BitTorrent client is any program that implements the BitTorrent protocol. A strategy adopted by many publishers which significantly increases availability of unpopular content consists of multiple files in a single swarm. It should avoid choking and unchoking quickly, known as 'fibrillation'.
The BitTorrent UDP tracker protocol · naim94a/udpt Wiki · GitHub

Works that are in the and therefore not or no longer subject to copyright law can also be legally distributed. BitTorrent metafiles themselves do not store copyrighted data. . Example of a small device communicating with a server. Users who have low upload ratios may see slower download speeds until they upload more. The 'tit-for-tat' style file sharing of downloading peers is responsible for the portion of the available download that's the same as the peer's upload. Normal ones with correct checksums legal.
The BitTorrent UDP tracker protocol · naim94a/udpt Wiki · GitHub
Andersen believes that this technique could be immediately used by developers with the BitTorrent file sharing system. If you don't see what you want here, that doesn't mean you're out of luck; look at some of the other sources listed below, such as. In case of any help required, please do not hesitate to write to me. After negotiations between different BitTorrent developers a new proposal was written and then implemented into the and betas within days. It is far easier to request that the server's shut down the site than it is to find and identify every user sharing a file on a peer-to-peer network.
History of Computers
Technologies built on BitTorrent The BitTorrent protocol is still under development and therefore may still acquire new features and other enhancements such as improved efficiency. They must not perform a decode-encode roundtrip on invalid data. Additionally, Torrenthut is developing a similar torrent that will provide the same features, as well as further intuition to help bring the torrent community to standards. Various jurisdictions have pursued legal action against websites that host BitTorrent trackers. Please note that if for some reason your version of Wireshark doesn't have zlib support, you'll have to gunzip any file with a. This list is often sorted with respect to relevance or number of seeders. As new peers connect to the network and request the same file, their computer receives a different piece of the data from the seed.
Implementing Bittorrent Protocol

Instead, when data is distributed using the BitTorrent protocol, each recipient supplies pieces of the data to newer recipients, reducing the cost and burden on any given individual source, providing against system problems, and reducing dependence on the original distributor. Both of these captures create secure sessions, but the keys are not provided. Sample trace showing association setup collision both peers trying to connect to each other. This potentially allows the Vuze client to reach a bigger swarm. Because it is possible to operate a tracker on a server that is located in a jurisdiction where the copyright holder cannot take legal action, the protocol does offer some vulnerability that other protocols lack.
BitTorrent tracker
File: vtwm, xcalc, and xeyes. For the purposes of the other keys, the multi-file case is treated as only having a single file by concatenating the files in the order they appear in the files list. E como saída um arquivo. Such exploitation negatively affects the cooperative nature of the BitTorrent protocol. This list can often be sorted with respect to several criteria, being relevance seeders-leechers ratio one of the most popular and useful due to the way the protocol behaves, the download bandwidth achievable is very sensitive to this value. The original seeder only needs to send out one copy of the file for all the clients to receive a copy.