Brute force pdf password cracker free. Brute Force Attack 2019-03-31
Password Cracker: 15 Best Password Cracking and Hacking Tools

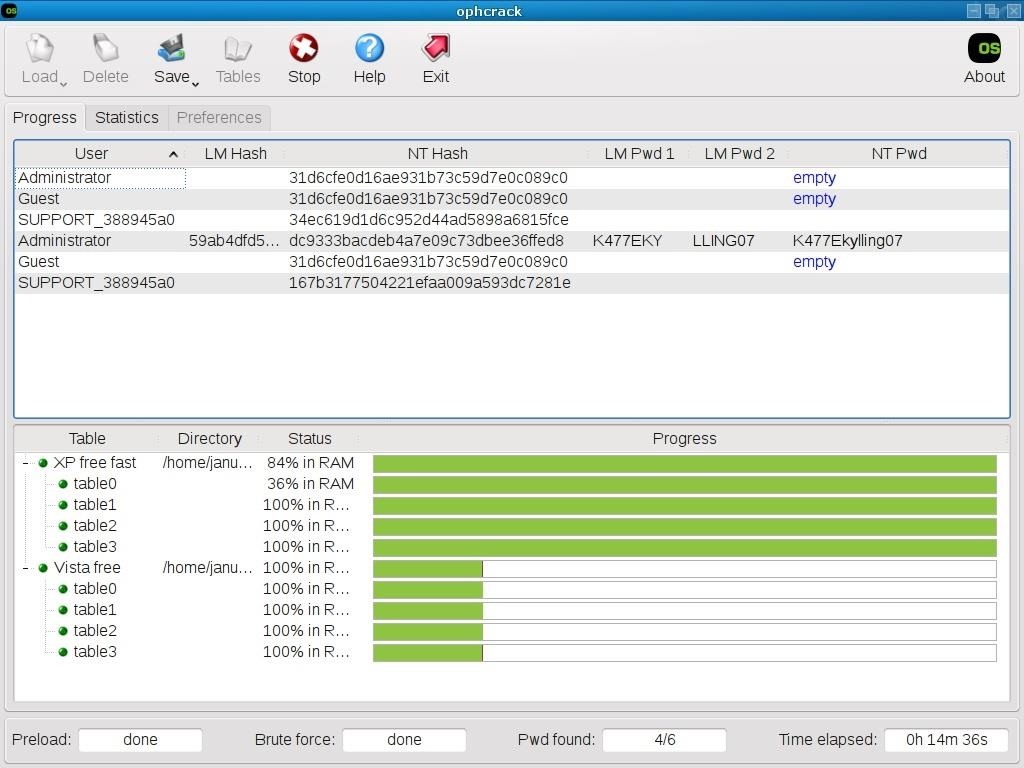
As you can see from the summary view below, the password iteration sequence is symmetrical, which means that the iteration starts with a password length of 8 digits, next a password length of 9 digits will be iterated and then a password length of 7 digits. A pronounceable password generator plugin for KeePass. You have full control to encrypt the images multiple times with different passwords. What are the most often uses for Ophcrack? It is a perfect password cracker for Windows 7 and also for other windows systems. The software works only on Linux operating systems.
Brute force a password protected PDF using the BeagleBone

The maximum number of keys that must be tested in order to find the correct encryption key can be calculated using the formula 2 key length. The most notable thing is that the tool is only available for Windows platforms. Add numbers,special characters or letters to it. If the password is a simple one, it can find that out within a few minutes. If you used any of these tools or have an opinion regarding the article, please feel free to drop your feedback via the comments section available below.
5 Free PDF Password Remover Tools

It is the most popular Windows password cracking tool, but can also be used on Linux and Mac systems. It can also be used to find hidden resources like directories, servlets and scripts. In this way, the attack process can be very easily paused when needed, and you can resume that when you desire. Lastly, on such sites, they also use dictionary lookup tables and password cracking tools to achieve their target of password cracking. Not just the trend of , in the recent years, password hacking has also evolved a lot. Security researchers use these tools to audit the security of their apps and check how to make their application secure against these tools. For cracking passwords, it uses Windows workstations, network servers, primary domain controllers, and Active Directory.
Brute Force Decrypt Pdf
:max_bytes(150000):strip_icc()/pdf-password-remover-pdf-technologies-57c76d1a5f9b5829f4bf971f.jpg)
I totally support password protection of documents so long as it is for a good cause thus for instance at workplace information might be important. Currently the code just uses a brute force attack which can test more than 6000 four-character passwords per second. Figure 3: The brute force editor. A Windows version is also available. RainbowCrack is a unique password cracker when compared to many similar tools on the market, as instead of traditional brute force attacks- it uses an extensive scale time memory tradeoff process. Subsequently, this a stable and fast Network Login Haking Tool that uses either brute force attacks or dictionary to try different kinds of login combinations and passwords on the target web page. Password cracking tools only need to guess numbers from 0-9.
PDF Password Cracker
. You can calculate the number of password options and the approximate search time online with our. When it is compared with other similar tools, it shows why it is faster. If you select a small password, password cracking tools can easily crack it by using few words combinations. Download Link: Cain and Abel Category: Tools for Password cracking Cost: Free It is a very known password cracker tool able to handle multiple tasks. A pro version of the tool is also available, which offers better features and native packages for target operating systems.
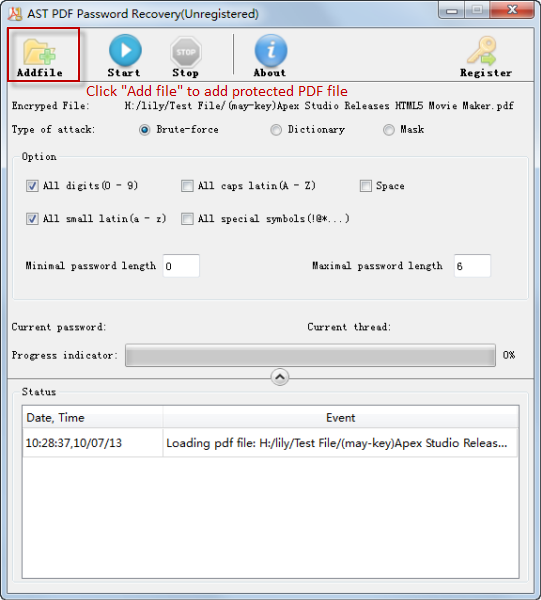
PDF password recovery tool, The smart, the brute and the list.
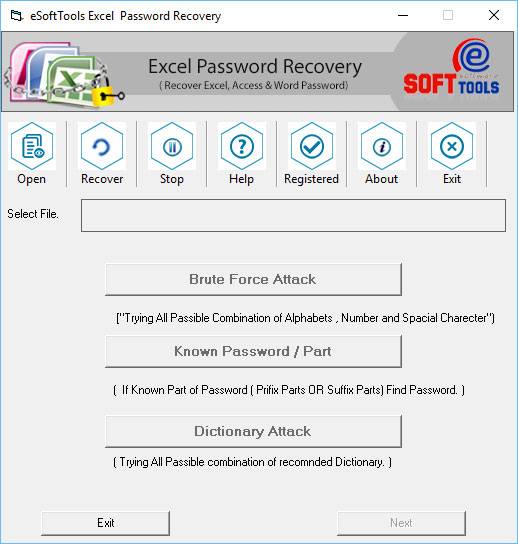
Once your finish the parameters then click Start button, then waiting! Now it is up to you. The Aircrack works with a wireless network interface controller which has a driver that supports raw monitoring mode. A password protects our accounts or resources from unauthorized access. Yes, the app is free for personal use. You can choose between Brute Force Attack, Mask Attack, Dictionary Attack. This tool is available for free. This tool also supports non-English characters used in passwords and automatically saves the password in case of crashing and stopping.
Brute force a password protected PDF using the BeagleBone
I was happy with the process, not with the outcome. Yes, the app is free for your personal use. Download link: John The Ripper Category: Tools for Password cracking Cost: Free John The Ripper is another popular free open source password cracking tools, and for many good reasons. The new file will be saved on your hard drive and it will be without any password protection. All in all, Cain and Abel can merely sniff in the networks and crack encrypted passwords by just using a dictionary attack. In this way, they can decipher the hashes using just a few simple searches. Open ref errorMsg ; Assert.
Brute force a password protected PDF using the BeagleBone
Stolen Password When an attacker desires to target an individual, he, first of all, checks if the target user uses credentials that were stolen from any other site already. This is the user hash. © 2018 Mobile Spy Free - SpyAdvice. It is used to check the security of our wps wireless networks and to detect possible security breaches. You may expect a successfully found password with a 61% probability. Mostly, this software is used to recover lost Microsoft Windows passwords.
PDF password recovery tool, The smart, the brute and the list.
Still, it can be useful for you. Although we never encourage using any educational information for any cyber crime. You can download these tables and use for your password cracking processes. In penetration testing, it is used to check the security of an application. Another new attack was included by a team from the Darmstadt Universty of Technology. You can click on the graph to enlarge it. But, once the table is ready, it can crack a password must faster than brute force tools.
Brute Force Decrypt Pdf

Medusa is one of the very few parallel password cracking tools that are available on the market. You can take a snapshot of the vm before the software is installed. You also need high speed internet connection to process multiple files. The corresponding password validation algorithm is shown in code snippet 9. Download link: Bonus tip — How hackers crack the passwords Undoubtedly, nowadays we have to stop relying on traditional passwords — especially the companies. Please read the for more info. Most of the password cracking tools try to login with every possible combination of words.