Cepstral voice activation key. Key Chain Spy Voice Recorder 2019-01-17
Cepstral License Keygen

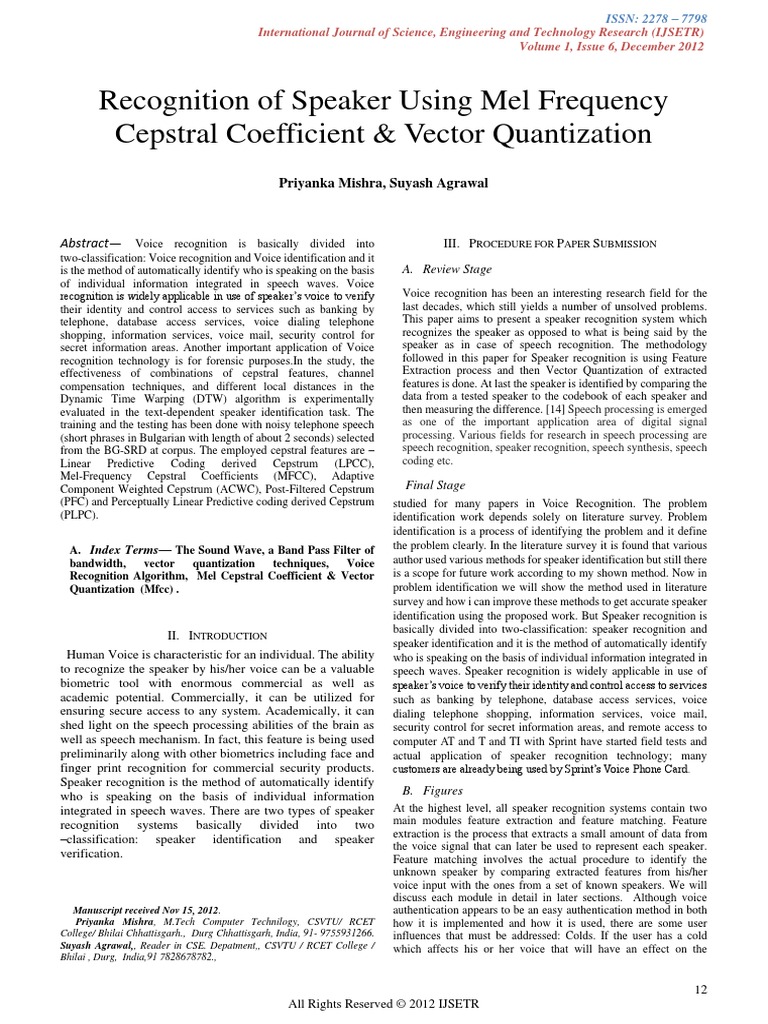
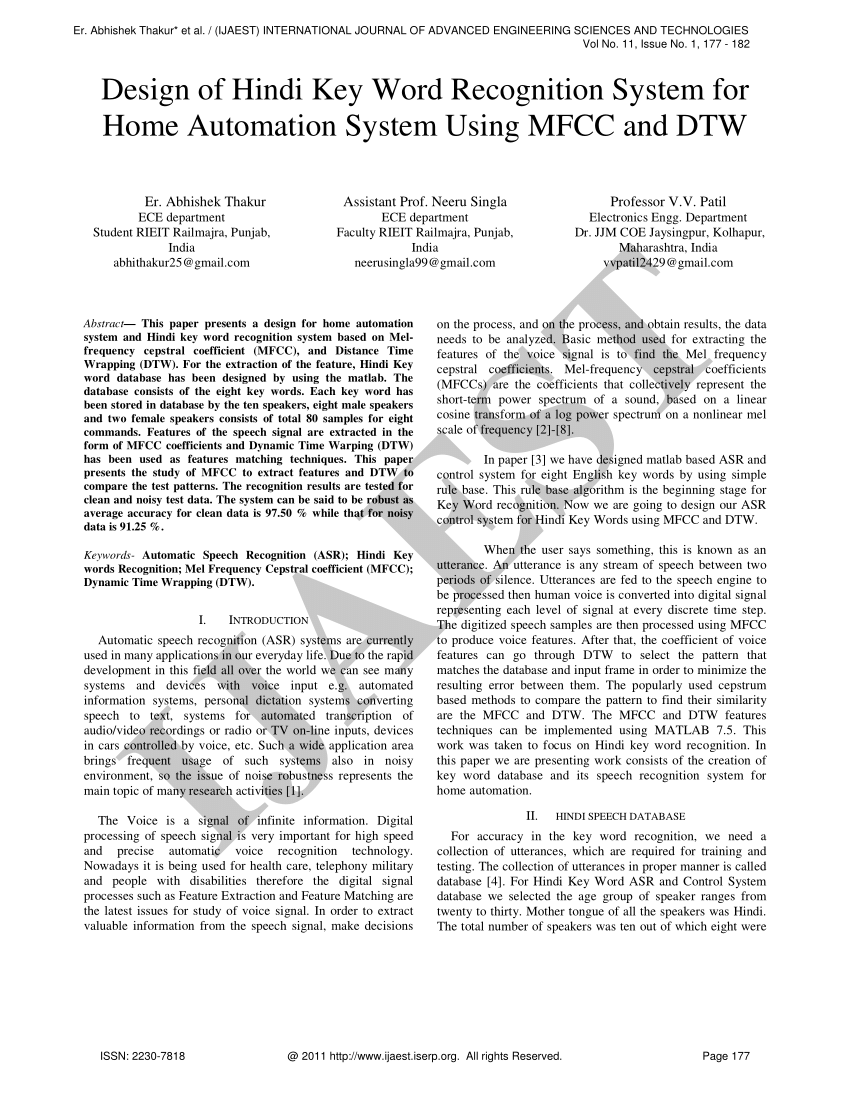
At Cepstral, Text- to- Speech is our only focus. The access to our data base is fast and free, enjoy. You will be prompted to enter your name, your company name, the number of ports you wish to register, and then the activation key. Can protect the content of the ebook and can add trial limitations. We highly recommend the Typical installation.
Key Chain Spy Voice Recorder
Audio is processed in a unique way for voice activation training. The data file is static. Now go to to pay the piper. If you've made it this far with no hiccups, it's probably time to cough up your 30 bucks and make the nag messages disappear. Timestamps on captured buffers remain true. Through this output you will hear the transformed voice if Voicemod app is opened, but not the rest of the sounds comming from games or other applications.
Cepstral 6 keygen

You will be prompted to enter your name, your company name, and then the activation key. We have the largest serial numbers data base. You may not modify the Product in any manner. Our members download database is updated on a daily basis. Q: Can recordings be listened to off the device itself? This ensures that the voice works properly with your telephony system. Q: Does this unit have voice activation? For today, we're going to walk you through installing Cepstral with the Cepstral Allison voice. The term Keyword Detection, describes the detection of the keyword by either hardware or software.
Cepstral Support

If you're an application designer, you probably need to keep this in mind. While waiting for the driver to service the interrupt, the hardware continues to capture audio into the buffer, ensuring no data after the keyword is lost, within buffering limits. How to Setup your Communication app or Game To make your life easier we have created a virtual microphone through which you can send your transformed voice to wherever you want. You can check all of them out on the. Cortana End User Experience To understand the voice interaction experience available in Windows, review these topics.
Allison’s Text
With over 25 years of experience, Spy Centre Security is your premier spy gear store and security camera equipment provider. It provides multiple high-quality skins that bring a fresh and elegant look to your computer screen. The Spy Gear Superstore® Welcome to Spy Centre Surveillance Equipment online store! You can create time-limited, demo and non-expiring keys, create multiple keys in one click, quickly encrypt strings using your own private key and lock a license key to a particular machine. This property is set by the operating system to configure the keywords to be detected. The structure includes an array of 0 or more structures describing constraints specific to any signal processing modes.
Cepstral 6 keygen

Performance counter timestamps Several of the driver routines return Windows performance counter timestamps reflecting the time at which samples are captured or presented by the device. So i have solve it. Here you have a video to show you how to change the Sample Rate of your microphone. Don't hesitate to pick up the phone and talk to one of our helpful technicians. Keychain and Recorder in one Stylish Design This great looking key chain is a voice activated recorder that is built right into a sturdy metal housing. Our reference system is the manufactured by Everex.
Cepstral License Keygen
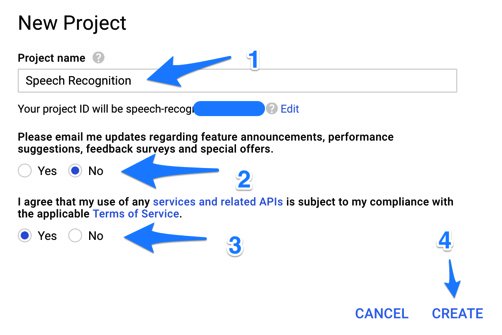
The event that is fired when a keyword is detected is a event. This software package is necessary for the correct operation of Voicemod and has to be installed in your Windows Operative System. When you double click on the program it will open a window that will display the time and date that the computer is set to. You can also right click on any of the displayed product license key to quickly copy it. Users often want to be able to instantly access an experience without having to physically interact touch a device. If you've longed for a text-to-speech Asterisk® toolkit that sounds just like the default Allison prompts that ship with Asterisk 1.
Cepstral License Keygen
The driver also returns the performance counter value that corresponds to the sampling instant of the first sample in the packet. If there is more unread buffered data available the driver either: i. All retail software uses a serial number or key of some form, and the installation often requires the user to enter a valid serial number to proceed. It doesn't tie up your Cepstral voice very long to read a sentence. Don't ask how I know.