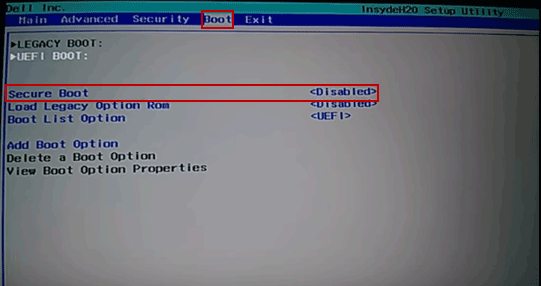
Clear secure boot keys. Windows Secure Boot Key Creation and Management Guidance 2019-03-10
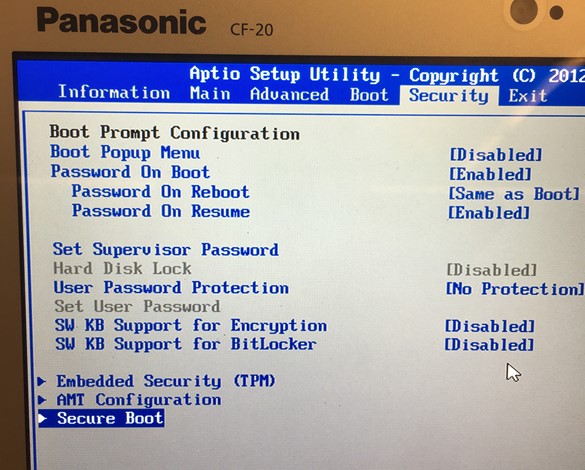
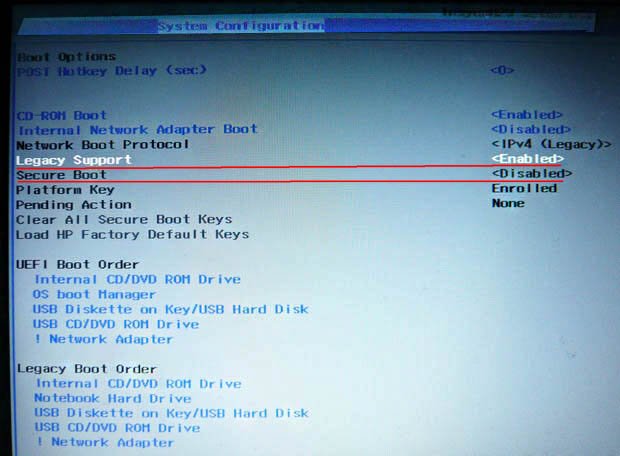
HP Bios Settings for TPM 2.0 and Win10 : SCCM
This page provides an overview of what Secure Boot is and how the Linux community is responding to it. Smarter people than me have been telling this to you for so long, it seems you have your fingers in your ears. It is not intended as prescriptive guidance and does not include any new requirements. Crypto processors can speed up key creation and access. Secure Boot is on its deathbed. You will be presented with an open command window.
Windows Secure Boot Key Creation and Management Guidance
The costs of these products can be in tens of thousands of dollars based on the extra services they offer. Signing the certificate with a private key and placing the signature in the certificate ties the private key to the public key. Should major technology companies create backdoors in their services? Note that here, we are using the -a option to append rather than replace , and a slightly different format for the input file since it is a X. I think that is correct - please correct if not. Then, re-connect to the machine via ssh. This appears to be a known issue, but there is no fix in efi-updatevar as yet. One of the primary functions of this level is to provide data integrity to the information being signed.
intel

If the bootloader is signed by any certificate present in this database, or its hash is present here, it will be denied from execution. Issue: Tip At your option, you can instead sign the EfiTool executable with your db key, and use that version. This is not meant for use in a production environment. After binaries reaches the Microsoft they are checked against malwares and malicious code. For more info, see Sections 1. Golden backdoors will never stay hidden.
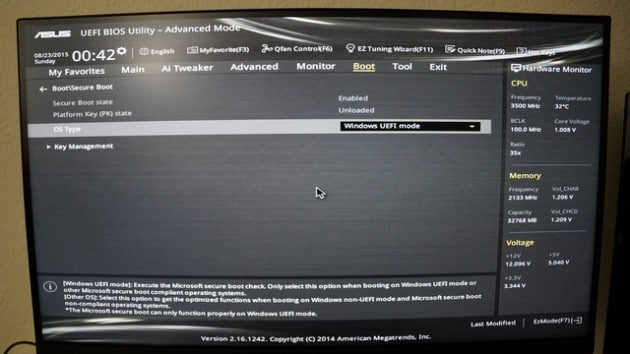
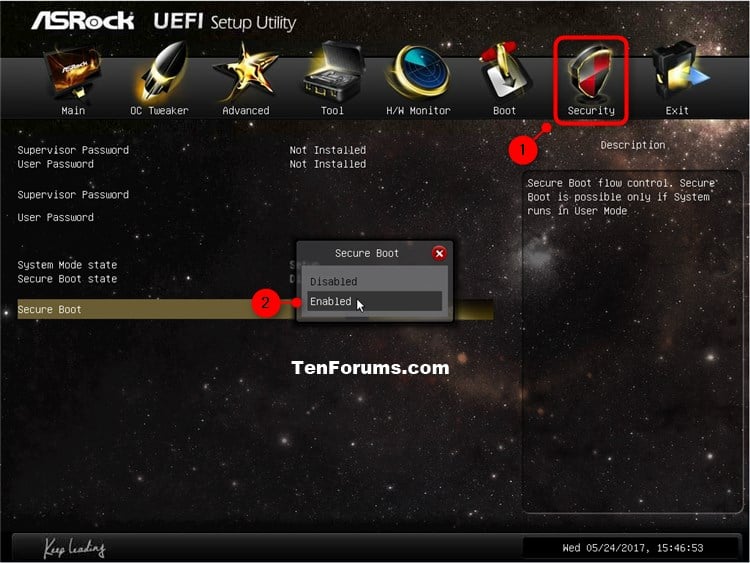
How to Disable or Enable Secure Boot for ASUS Motherboard
I was still having some trouble but I figured out that anytime you go into the bios it disables legacy support. Hi Markus, Modifying the Secure Boot settings requires the firmware on your Surface to be updated. It is not too expensive and can be a valuable addition to your toolkit. Pen stopped working since the install media did not contain the drivers. For more information see section 27. Think of them, like the certificate store in a web browser. If you find this Web page useful, please consider making a small donation to help keep this site up and running.
How to Disable or Enable Secure Boot for ASUS Motherboard

If so, log in directly at the target machine's keyboard, use ifconfig to find out the new address, then issue the above ssh command citing that address. Close out the command window by clicking on the 'x' in its title bar. Level 2 Security Level 2 requires, at a minimum, role-based authentication in which a cryptographic module authenticates the authorization of an operator to assume a specific role and perform a corresponding set of services. I regret the boot problem you are experiencing. A 'Date and time' dialog appears. If asked whether you wish to proceed, click 'Yes'.
Surface Pro 3

Every time the system booted clean boot, shutdown, restart, etc. I think there is just something wrong with this bios. I think the clear keys is used if you want to load your own keys. If you experience errors when running the preceding commands the most likely being a message of Cannot write to. So attacker which has access to our machine could temper with these components and replace bootloader with malicious one.
intel

Although Secure Boot is developing less rapidly than it was in late 2012, when I first wrote this page, it's still a dynamic area. This variable holds a signature database containing one or more X. Yet another road block for Linux advocates to work around… sigh. Having one unique key for each device. I mean, there will be some enterprising individuals who take the time test this, but for the majority of individuals, this will simply be another security blip that passed them by.
Surface Pro Bricked after re
Please consider based on resource availability what method would work for you. Any non-trusted components will not be loaded and instead will trigger Secure Boot remediation. The secure boot protocol checks, when software is loaded, to ensure that it has been signed by one of the keys that are installed. Unfortunately my main backup drive failed yesterday and although the data is secure it's been causing me problems so I may not be able to reload now until next weekend so I just wanted you to know that I hadn't forgotten. Windows boot components verify the signature on each component.
intel
As such, my advice would be to run through the process in this chapter with 2048-bit keys initially; then, once you have everything working and only if you wish so to do — it is entirely optional , you can repeat the process, but with 4096-bit keys. Saving Current Keystore Values, and Creating New Keys We begin by re-establishing an ssh connection, as before as it will make the work of entering commands etc. This may involve storing a key in a key container on an encrypted hard drive and possible for additional sandboxing and security use a Virtual machine. Other keys are used by Secure Boot to protect access to databases that store keys to allow or disallow execution of firmware. I have tried all the suggestions on boot sequencing with the backspace key, delete key, the F8 key Shift key you name it and nothing. There are more details under section 2. This may include very high value transactions or high levels of fraud risk.
Windows Secure Boot Key Creation and Management Guidance
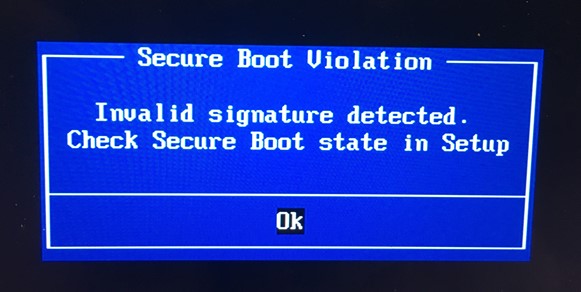
These warnings may safely be ignored. On upcoming Windows 10 devices, manufacturers may remove the option to turn off Secure Boot. For that, I needed to disable the secure boot on the machine. More details can be found in the efi-updatevar manpage. But for the meantime, Secure Boot can be unlocked. Not sure if this was the original requesters issue, but the symptoms line up and could be a solution for other folks.