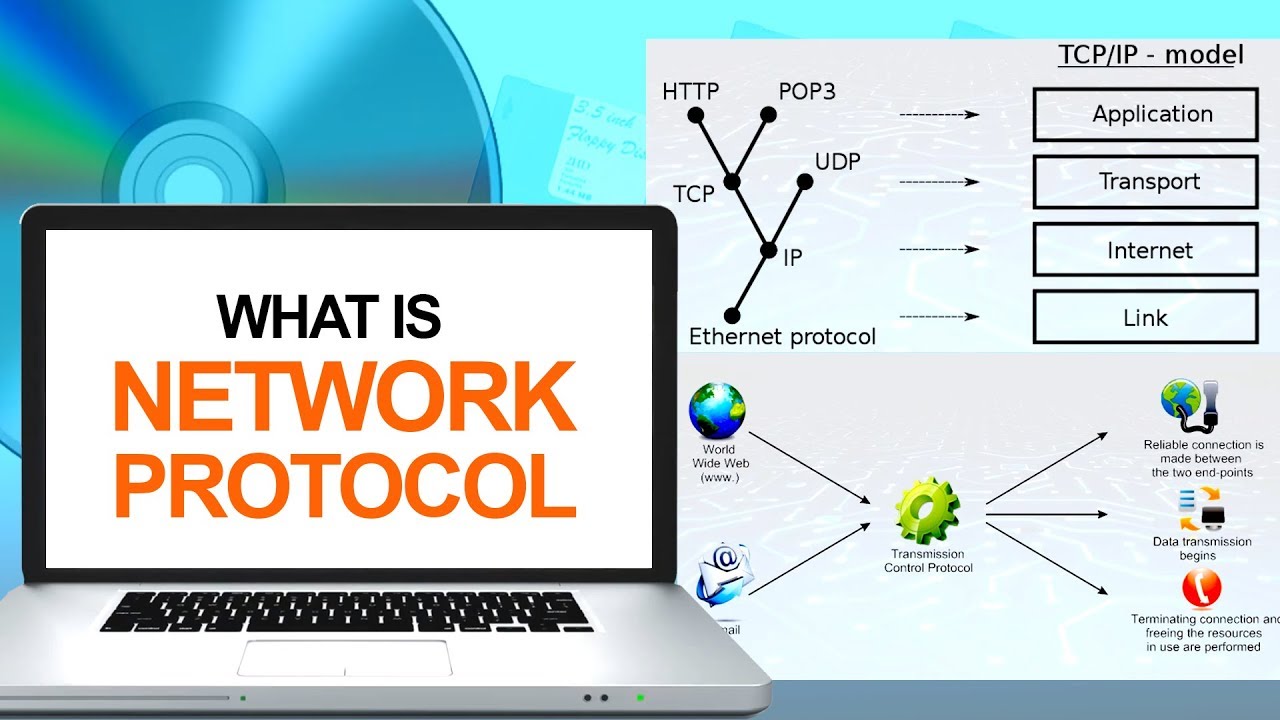
Computer network protocol diagram. What is UDP (User Datagram Protocol)? 2019-02-11
The TCP/IP Model and Protocol Suite Explained for Beginners
Host-to-Network Layer: It translates data and addresses information into format appropriate for an Network or Network. Switch is used to join multiple computers together at a low-level network protocol layer. With the stream-mode, the service provider supplies a byte stream that links the two communicating users. This will connect all the devices to a central hub. It operates over fiber optic cable at 100 Mbps.
The TCP/IP Model and Protocol Suite Explained for Beginners
It is possible for computers to talk to each other using just Ethernet, and with no networking protocol, but it is not practical You can liken a link to a street. It is also frequently used by Internet Service Providers to utilize high-speed access to the Internet for their clients. . Fast Ethernet To allow for an increased speed of transmission, the Ethernet protocol has developed a new standard that supports 100 Mbps. The interface of the software feels like Microsoft Word 2003 interface, with no ribbon menu as some of the other software we have reviewed.
OSI model
The application layer per se has no means to determine the availability of resources in the network. When identifying communication partners, the application layer determines the identity and availability of communication partners for an application with data to transmit. Hubs do not create a separate collision domain they just repeat packets. It also defines the protocol for between them. Hubs vs Switches Hubs operate at the physical level, and were once the primary mechanism for connecting computers together.
A basic overview of the HTTP Protocol
They occupy a larger area and can be large enough to be world-wide. Network interface cards provide a dedicated, full-time connection to the network. The dashed line between the two primitives indicates that the Data. A protocol is a set of rules that govern how systems communicate. You can also exclude certain as needed through the Wizard. It provides to help distinguish different user requests and, optionally, a capability to verify that the data arrived intact.
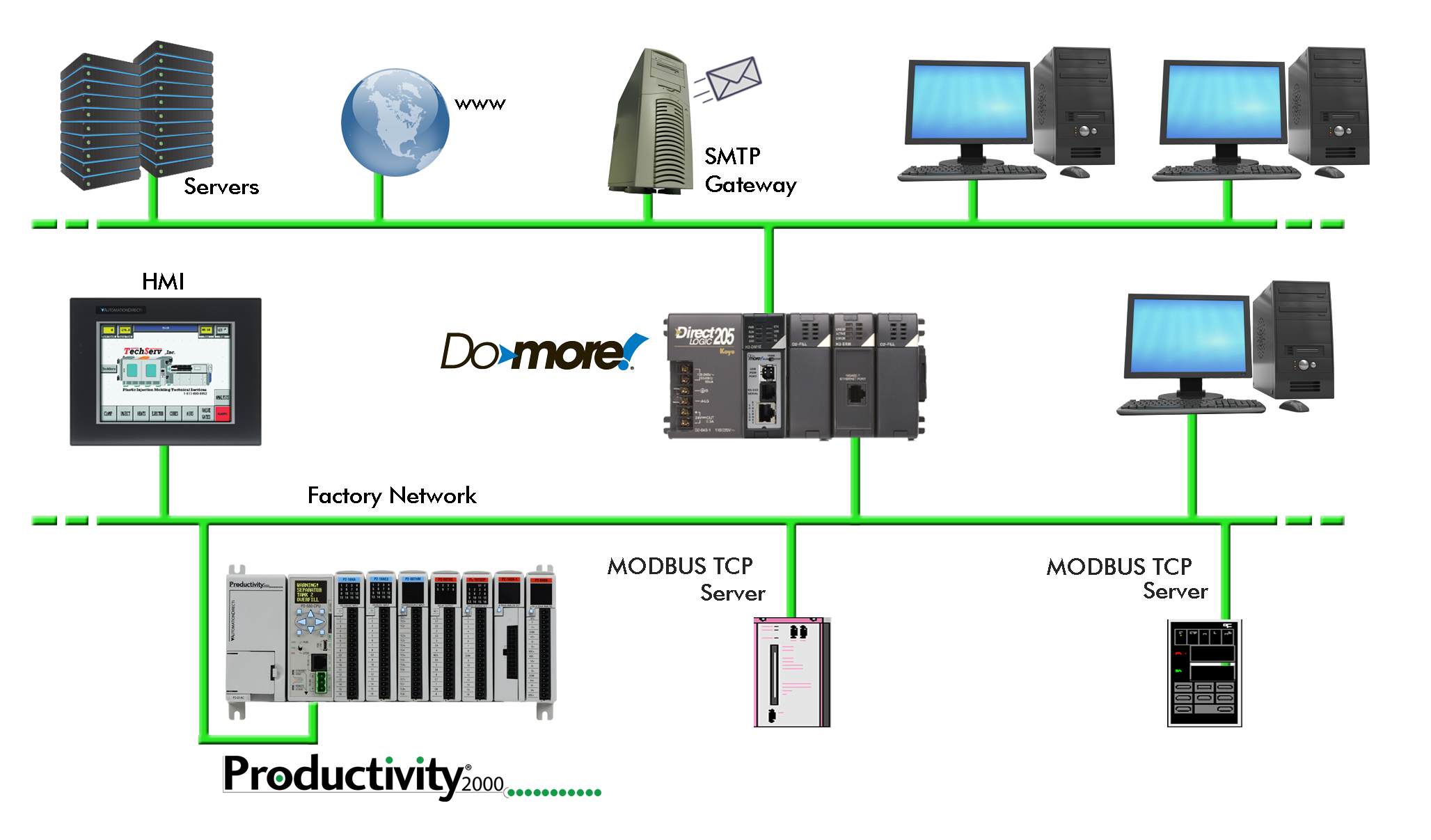
Computer Network
Segmentation is the process of dividing a long message into smaller messages. The letter will then be collected and delivered to its final recipient. This layer is also responsible for session checkpointing and recovery, which is not usually used in the Internet Protocol Suite. An example of this kind of network is the Internet. These protocols were defined by many different standard organizations throughout the world and by technology vendors over years of technology evolution and development.
The TCP/IP Model and Protocol Suite Explained for Beginners
This means that the transport layer can keep track of the segments and re-transmit those that fail delivery. The third phase is the termination of the connection. You have very clear and consise explanations. You can also access data of another computer in the network. What is a Network Protocol Rules of Network Protocol include guidelines that regulate the following characteristics of a network: access method, allowed physical topologies, types of cabling, and speed of data transfer.
Computer Network
It conceptually divides architecture into 7 layers in a logical progression. To be able to deliver these messages, the service provider must be able to unambiguously identify each user. It is highly recommended that you practice them. You will also see the default gateway address 192. This is a system where each computer listens to the cable before sending anything through the network. Mainframe is a big computer.
The TCP/IP Model and Protocol Suite Explained for Beginners

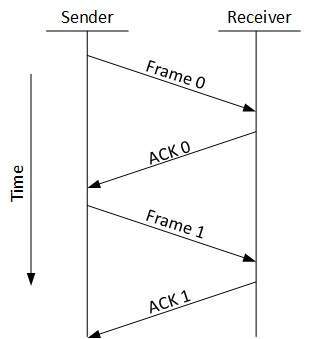
Diagnostic devices are used in diagnosing and troubleshooting the network problems. They have a wide array of pre-built templates that are ready for you to plug in your data and quickly modify to your needs. The token then proceeds around the ring until it comes to the computer for which the data is meant. The term frame is used for data units at the data link level and the the term packet for data units and the networking level. This model has the ability to connect multiple networks together in a way so that data transferred from a program in one computer are delivered safely to a similar program on another computer. This is illustrated by the time-sequence diagram below.