Computer networks protocols examples. Top 5 Network Routing Protocols Explained 2019-05-12
Computer Network
See your article appearing on the GeeksforGeeks main page and help other Geeks. It is used for managing the files on the internet. In other words, a protocol is a standard procedure and format that two data communication devices must understand, accept and use to be able to talk to each other. A protocol may belong to one or multiple protocol suites, depending on how you categorize it. This tutorial is the first part of the article.
Protocol
In the , both the data and the control planes are described. What is a Network Protocol Rules of Network Protocol include guidelines that regulate the following characteristics of a network: access method, allowed physical topologies, types of cabling, and speed of data transfer. They offer the libraries with ready-to-use vector design elements, professional-looking examples, samples and templates. This decreases the probability of collisions. So, the changes in the topology are reflected to all routers. One serious drawback here is that, we are not sure about whether the data has been received properly at the receiver end. Local Talk adapters and special twisted pair cable can be used to connect a series of computers through the serial port.
Examples and types of networks

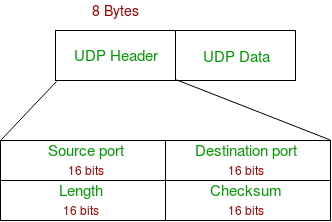
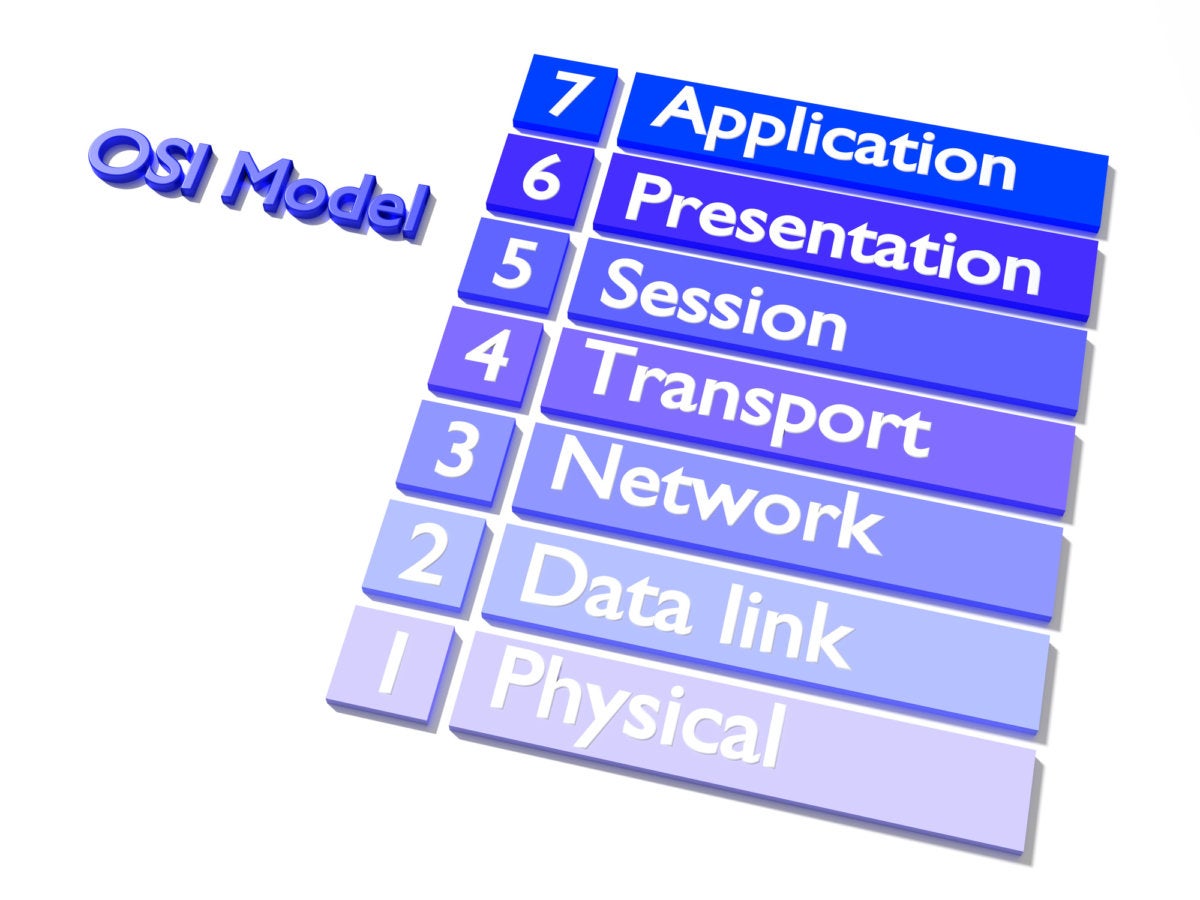
Convert, compress and encrypt are the main functions which presentation layer performs in sending computer while in receiving computer there are reconvert, decompress and decrypt. This way a data packet is always delivered to the same network layer protocol from which it was sent. It is designed for printer sharing. Now it is actually the industrial standard, it is supported by many devices. All these devices are capable efficiently interact each other and so give wide possibilities for automation the execution of repetitious tasks, increasing a home security, improvement quality of life inside a home, enhancement a personal productivity, and also make easier an access to entertainment. Some protocols also add a footer at the end.
Medium Access Control Sublayer Tutorial in Computer Network with Examples
By following these standards, they can build the networking components and software applications which work in dissimilar environments. If the devices are within the range of network then we can share files and data between them. Data transportation This layer establishes a logical connection between sending system and receiving system and uses that connection to provide end-to-end data transportation. Network protocols include mechanisms for devices to identify and make connections with each other, as well as formatting rules that specify how data is packaged into sent and received messages. In client server protocols, the application layer protocol can be split into two sub-protocols, one for the client side and another for the server side, with each sub-protocol running on different computers. The risk of a security problem arising is slim for those who don't have sites with a lot of critical information, but the risk of that information being accepted will increase when it comes to information that can be valuable in the hands of a competitor or a hacker wanting to use the data in nefarious ways. There are many kinds of computer networks that differ in the transmission medium, in communications protocols, in size, topology, organizational intent, and also in territorial basis.
Computer Network
You managed to hit the nail upon the highest and defined out the entire thing with no need side-effects , other folks can take a signal. In addition, category 5 twisted pair or fiber optic cable is necessary. It is based on the functional modeling language Structured Analysis and Design Technique abbr. To successfully send and receive information, devices on both sides of a communication exchange must accept and follow protocol conventions. Not only do these network security protocols create a safe connection but they also greatly reduce the costs associated with creating an alternate solution, such as building or leasing lines to create a private network.
Protocols in Application Layer
Your favorite reason appeared to be at the internet the simplest factor to take into accout of. An application program is considered as network-aware when it can make any sort of network request. Classification based on relationship with peer application layer Another method of classification of application layer protocols is based on whether it is a client-server protocol or a peer to peer protocol. It is responsible for setting up, managing, and dismantling sessions between presentation layer entities and providing dialogs between computers. If the sequence number is lower than the highest one , it is rejected.
Role and Types of Application Layer Protocols
Wi-Fi 6 is a standard for wireless internet that replaces the 802. In Token Ring, the computers are connected so that the signal travels around the network from one computer to another in a logical ring. Because of this, the protocols which define the network communication are highly inter-related. The Token Ring protocol requires a star-wired ring using twisted pair or fiber optic cable. Network diagram is effective tool for representing and description the network knots and connections between them in comprehensible graphic view, for studying and analysis them. It also provides physical addressing.
Medium Access Control Sublayer Tutorial in Computer Network with Examples

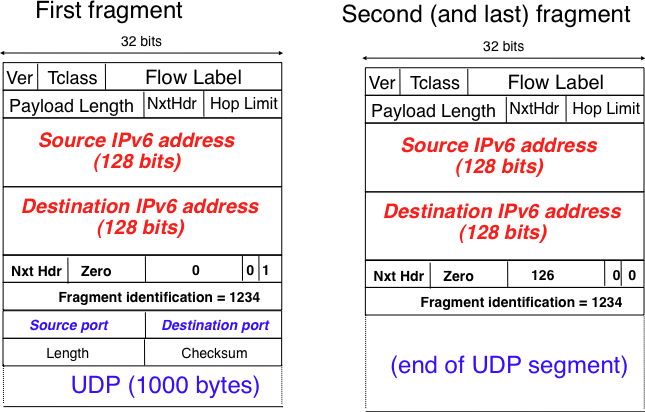
As a result, except for specialty networks built around a specific architecture, few networks would be able to function, and the internet as we know it wouldn't exist. I say to you, I definitely get annoyed while other folks think about issues that they plainly do not understand about. The delivery of packet source to final destination can be achieved by two methods: 1. More than one route is possible in every network, however the shortest route should be selected. Main functionalities of transport layer are segmentation, data transportation and connection multiplexing. Routing is a process of forwarding data packet to its destination.