Crack mssql password hash. Cracking MD5, phpBB, MySQL and SHA1 passwords with Hashcat on Kali Linux 2019-02-26
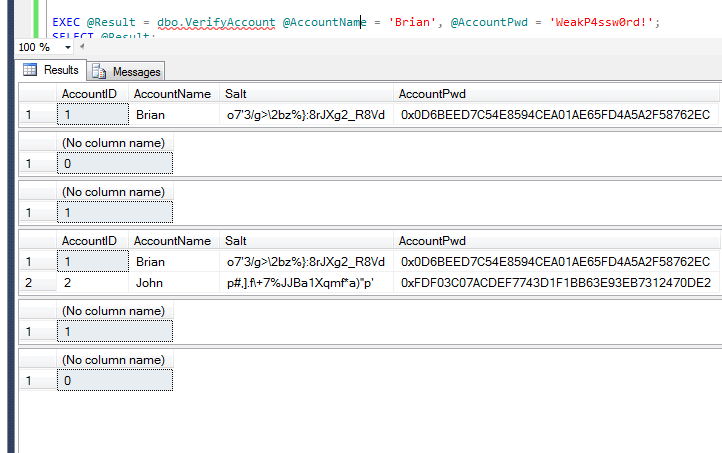
Decrypt the hashed password in SQL Server 2008

Suggested reading - : identify your unknown hash: we support over 250 hash types. An Explorer property page tab offers a handy and familiar access to program controls without context switching, but the small physical window size places constraints on application features. They can be vulnerable to some attacks dictionary, rainbow tables, etc. Lastly, if you are a developer of one of the tools or online resources covered in the manual reach out to me on twitter and I'll mail you a free copy. This is because hashing does not encrypt the original value at all.
Decrypt the hashed password in SQL Server 2008
What should you do when you forgot the password to login to Windows or Windows Server system? Doesn't look like it supports hash comparison. Because I will stick with attack mode 0 Straight Attack Mode , I just need to adjust the value for -m where you specify which type of hash is that. Can be used to create a database of computed hashes and revalidate against it. Sqlmap is the most popular tool for carrying out automated sql injections against vulnerable systems. Match highlights are in very pale colors that may be difficult to see on some monitors. After digging through forums and blog posts looking for tool usage, password analysis, and examples you apply some new trick only to forget it by the next pentest. Pankaj Kumar Yadav- It is not possible to decrypt a hash.
Crack Password Hashed on MySQL

But all these considerations are not enough if passwords are stored in an unsecure way. Because I will stick with attack mode 0 Straight Attack Mode , I just need to adjust the value for -m where you specify which type of hash is that. You collect some hashes, fire up John The Ripper or Hashcat, and use default settings with rules and some lame dictionary you pulled off the internet and hit. Updates and additions to the manual are planned for future chapters and sections based on customer feedback and geared towards assisting the network security professional. You might ask why I showed the same command over and over again! Finally -- and perhaps most importantly -- make sure you follow up on your findings.
CrackStation

Second method would be to query the database for both the salt and the encrypted password and do all the comparisons in the app with that single database call. The commercial product can also crack Oracle password hashes. A console application, for example, allows for scripting and ad- hoc programming that is not possible with graphical applications, but its user interface is somewhat limited. If not, what other options are there? Can minimize to the system tray. Changes in supported hashes or hash formats since then may not be reflected on this page. These tables store a mapping between the hash of a password, and the correct password for that hash. Question: Would changing the salt anytime they change their password be a good idea? He probably doesn't understand the point of hashing and so he tries to reverse it to make the comparison work.
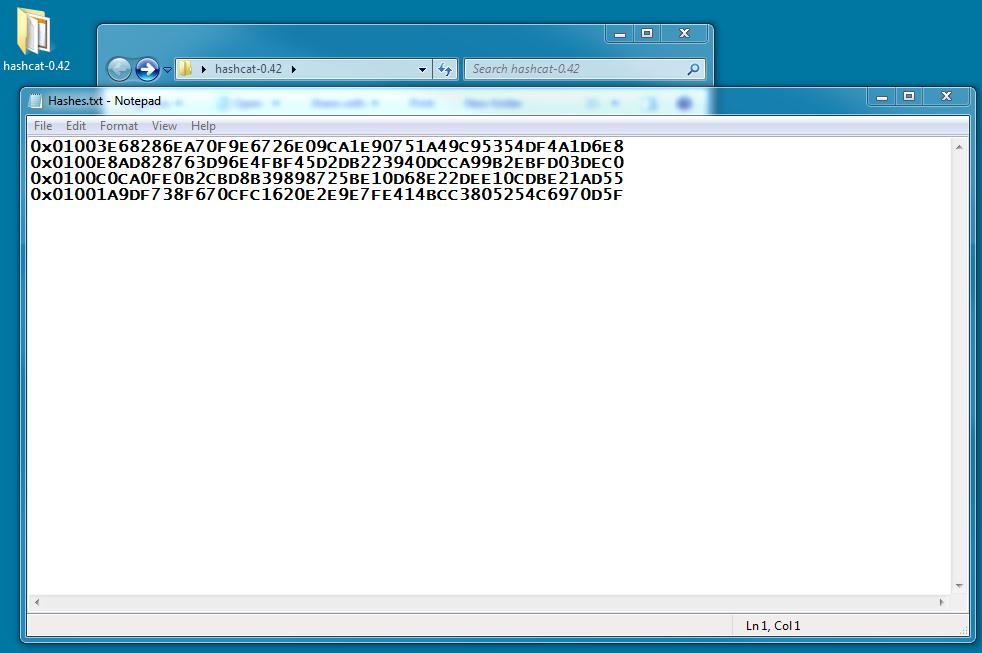
HASH CRACK

First, query the database for the salt for a specific user, use the application to encrypt the password, then query the database a second time to compare the hashed passwords. This is probably pretty unlikely that both logins 1234 and 1243 will have the same password. You recover a fair amount of the passwords but fail to make any real breakthroughs. Salt should be unique for each user, otherwise if two different users have the same password, their password hashes also will be the same and if their salts are the same, it means that the hashed password string for these users will be the same, which is risky because after cracking one of the passwords the attacker will know the other password too. The program can calculate the hash for files, directories, subdirectories, and text strings. In this case, the hash value saved in the database must be the same as the hash value of the password being passed in. I have queried and found the data stored and return both are different.
Decrypt the hashed password in SQL Server 2008

This sheet was originally based on. It can also be a. This is the precise reason why salt and hash should not be kept together. I will try to cover and explain as much I can. Mule hashes of one or more disk files. It means that it's impossible to revert to the original value using encrypted output. In cases where posts contain code examples these may be used as long as a suitable header is appended consisting of at least a simple link to the original content.
John The Ripper Hash Formats
As always, read the manual and help file before you ask for help. Something simple like hashing the plaintext 100 times with a new additional salt each time would be barely perceptible if at all to a user logging in to your site, but it would increase the time it takes to brute-force a password by the same 100 times. However, I'm not a security expert and there may be reasons not to do it one of these ways. In this manner, while you can't decrypt, you can determine whether the user knows the password or not without storing the password. There is plenty of about its command line options.
Microsoft SQL Server Passwords (Cracking the password hashes)
It can save generated hashes to. I thought it might be helpful to compile a cheat sheet to reduce the amount of time I spend grepping and googling. The weaker the password is simple, small, etc. Easy Hash is a portable application and Explorer context menu that computes over 1. . However, passwords were not case sensitive at that time.
HASH CRACK Password Cracking Manual

You can do the hashing in your application and save the resulting message string to the database. But, how is this value actually calculated? For storing passwords you need a slow one way crypting algorithm like bcrypt. In this case you can encrypt questions using symmetric keys, and decrypt them when needed. From the database side of things, the random-ish salts do provide the added layer of defense that makes hash comparisons more difficult. It appears however that this approach leaves a glaring security hole; i. You can type in hashcat --help or cudahashcat --help and read through it.
Password Hashes Cracker: MD5 LM NTLM SHA1 MYSQL OSX and more

While you may know your environment like the back of your hand, it doesn't hurt to ferret out servers that may have been forgotten or that someone else connected to the network without your knowledge. Below is the adapted version of the code to calculate the hash value. These problems can all be sorted with a bit of googling or grepping through the john source code. There is plenty of documentation about its command line options. You might ask why I showed the same command over and over again! Not the best way to enable a password, but a workaround for sure.