Crack rar file password kali linux. Howto Crack Zip Files Password in Linux 2019-02-16
How to Hack or Crack Zip/RAR File Password in Seconds with Kali Linux[Hindi/Urdu] #Kali Linux
If you have a complex password it will take a lot longer than simple passwords, and with the free tables your password may never be cracked. In this image I want to specify only one character so I used :. Now we are going to crack this zip password by using dictionary attack. For example, if a file has a password: 12345 and another file has a password: abc123 then the file with the only numerical password will be very easily cracked compared to the other file. More the passwords to try, more the time required. .
Howto Crack Zip Files Password in Linux
For the wordlist we shall be using the password list that comes with john on kali linux. Usage only allowed for legal purposes. Here we know our password is numeric e. In addition to that, it also adds multi-core support. This tries all possible combinations of the letters you specify. Using Wordlists To Crack Passwords Lets begin.
Cracking ZIP/RAR Password With John The Ripper
I am going to show you these : 1. Hacking someone's account or password without taking legal permission is a crime and i do not support such activities. Scan to a depth of 2 -d 2 and use a minimum word length of 5 -m 5 , save the words to a file -w docswords. It allows for rapid, yet reliable large-scale auditing of multiple hosts. If you know your password has numeric ex- 123.
Crack Windows Passwords in 5 minutes using Kali linux

It is a very efficient implementation of rainbow tables done by the inventors of the method. On Ubuntu it can be installed from the synaptic package manager. Now that our new user is already created its time to crack his password. Use for security: check passwords, if 0 is returned, reject password choice. John is in the top 10 security tools in Kali linux. Luckily, the JtR community has done most of the hard work for us.
Cracking ZIP/RAR Password With John The Ripper

Remember that you need john the ripper to do this. Install fcrackzip in Ubuntu sudo aptitude install fcrackzip This will complete the installation. For the rar file it did not take nearly as long since the password was relatively common. Burp gives you full control, letting you combine advanced manual techniques with state-of-the-art automation, to make your work faster, more effective, and more fun. Steps To Use Pyrit To Crack Password 1.
Howto Crack Zip Files Password in Linux
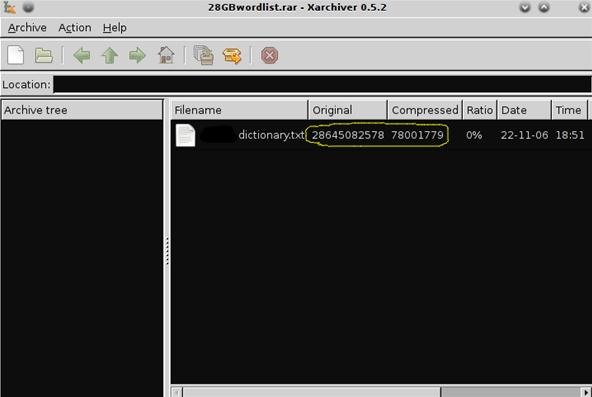
A rule of thumb for passwords is the longer, the better. If your password has small alphabets characters and length of password is 8 digits. The name can also be the number of the method to use. Other password lists are available online, simply Google it. This process is very time consuming. For that, you have to follow the complete guide discussed below.
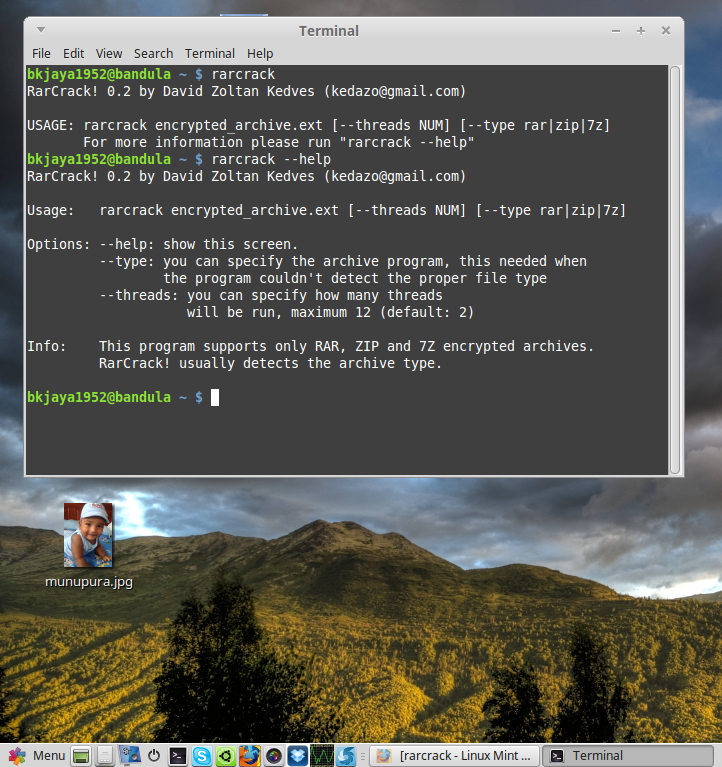
How To Crack Ziprar File Password

A Windows version is also available. Hope you like my post. I will crack a hash that is inside a text file. See the for more information on modes. So What Do I Need To Do? Ncrack was designed using a modular approach, a command-line syntax similar to Nmap and a dynamic engine that can adapt its behaviour based on network feedback. For years, experts have warned about the risks of relying on weak passwords to restrict access to data, and this is still a problem. Because after a whole night, this has got to this point… rarcrack testfile.
Kali Linux How to crack password protected zip files
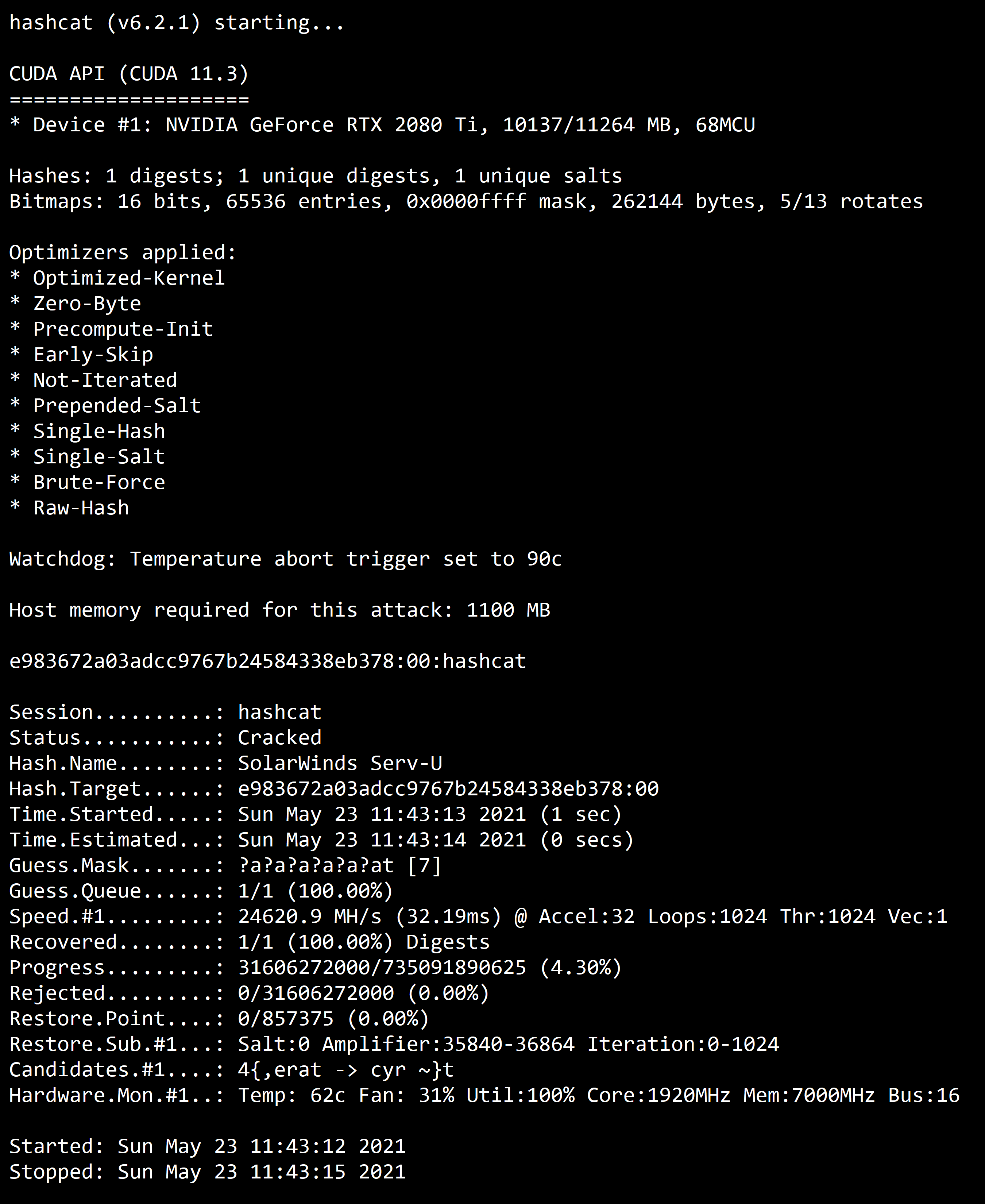
In this case its admin. This tool makes it possible for researchers and security consultants to show how easy it would be to gain unauthorized access to a system remotely. Or first create a new user with a simple password. You can specify wich characters will be used in password generations. Hi Friends, in this video, we will be looking at Linux and encrypted password cracking with John the Ripper.