Crysis ransomware decryption tool. How to decrypt Crysis ransomware and delete it manually 2019-02-06
New decryption tool for Crysis ransomware

Kindly apply the methods outlined below as they have been carefully developed to provide a recovery help for the most severe cases of encrypting assaults. To do that, restart your computer, before your system starts hit F8 several times. CryptoMix Offline CryptoMix also known as CryptFile2 or Zeta is a ransomware strain that was first spotted in March 2016. The originals have been deleted. Why the keys were released is also unknown, but it may be due to the increasing pressure by law enforcement on ransomware infections and the developers behind them. For example, the most recent variants would have a file named test.
New decryption tool for Crysis ransomware

The crooks who masterminded the CrySiS ransomware campaign are proficient in what they are doing. The tool was developed using the master decryption keys recently published. Another, easier, way is to load into Safe Mode and do all file recovery measures from there. The crooks display no traces of any moral code. That is why, in this guide we will try to recover deleted files as you remember, ransomware creates an encrypted copy of a file and deletes the original file without installing anything on a disk.
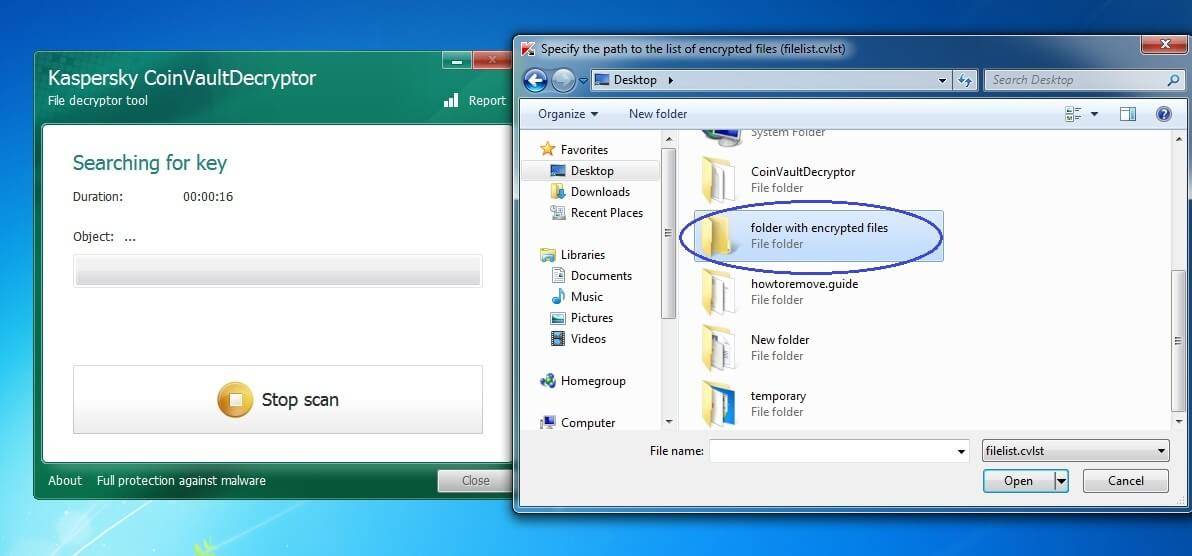
CrySiS ransomware decryptor

Type msconfig in the search field and select the System Configuration option in the results. Select the detected entries and click Fix Threats to get the troubleshooting completed. This feature is available in Windows 7 and later versions. You can use this feature to restore files and folders that you accidentally modified or deleted, or that were damaged in our case — CrySis Ransomware by CrySis Ransomware. If you were using Dr.
New decryption tool for Crysis ransomware
Use special removal tool to remove core files of CrySis Ransomware and free decryptor to decrypt. Then, go to the Previous Versions tab as illustrated below. Update: Use following service to identify the version and type of ransomware you were attacked by:. The one in question definitely subscribes to that routine. If you need additional information on how to use the tool, please refer to. These techniques are certainly not a cure-all, but they will add an extra layer of ransomware protection to your security setup. This family of malware gained popularity after , another ransomware that also spread widely while it was active it ceased its operations early this year upon the to revert it.
Free Ransomware Decryption Tools
It seems this incursion is perfectly orchestrated no matter how you slice it. Update 2017-07-21: The decryptor was updated to also work with Mole variant. It offers Export feature for much faster retrieval of the latest readable copies. However, the more you use the computer, especially if you do something that writes new data on the hard drive, the more chance that your deleted file gets overwritten and will be gone for good. Please also note the recovery returns files as saved before the time associated with the restore point addressed.
New decryption tool for Crysis ransomware
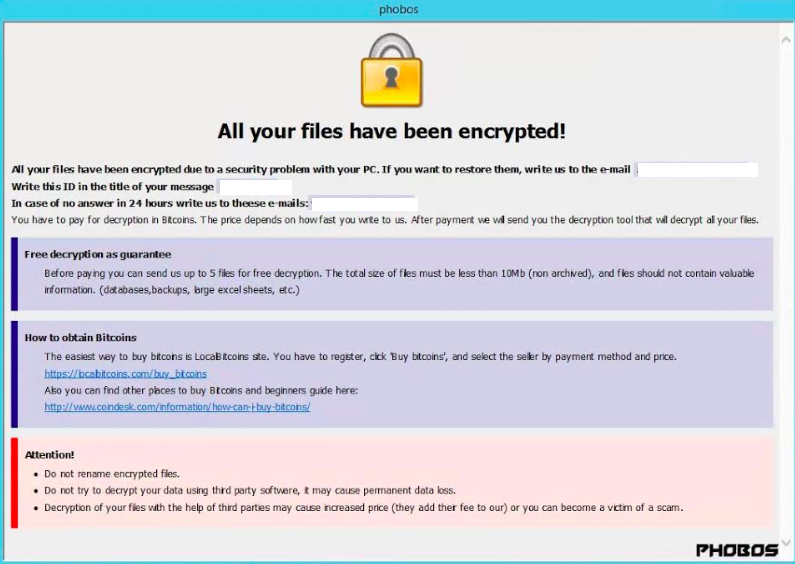
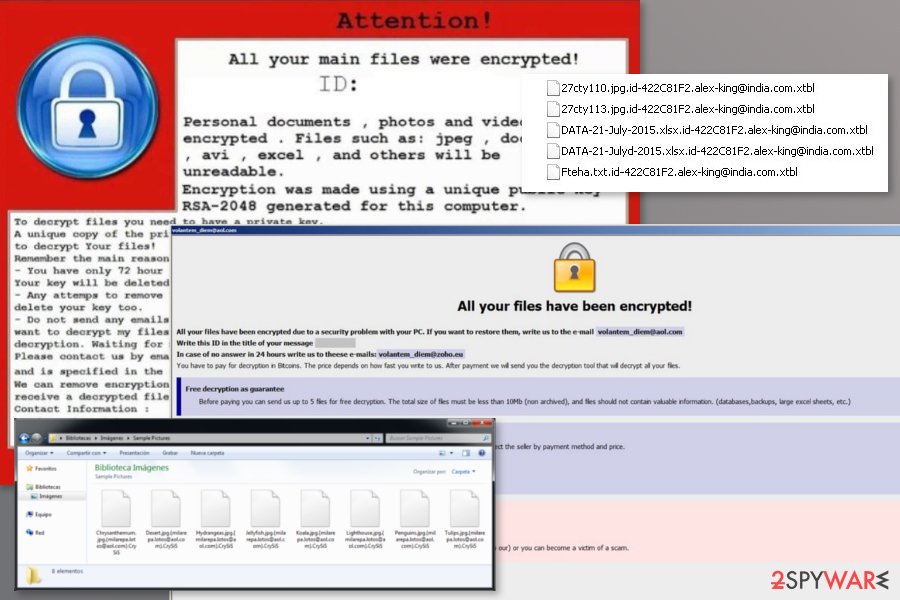
To make use of the feature, right-click an affected file and choose Properties in the drop-down list. Lawrence Abrams is a co-author of the Winternals Defragmentation, Recovery, and Administration Field Guide and the technical editor for Rootkits for Dummies. Crysis is a Filecoder-type malicious code whose purpose, as its name suggests, is to encrypt information and request the payment of a ransom in exchange for the return of said information. What is Java ransomware If your files have been encrypted, and. Backups and removing remaining traces of Crysis ransomware Prevention is the best cure. In the second folder, the ransomware prevents the user from noticing its presence by hiding itself in a native folder, essential for Windows.
CrySiS ransomware decryptor

Rest assured the scan report will list all items that may harm your operating system. This method is more cumbersome that the use of ShadowExplorer, but it can help restore the most important individual files on condition that the ransomware failed to disable the Volume Snapshot Service on the computer. Those messages instruct the victims to contact the crooks by email for further advice. The tool was prepared using the master decryption keys, recently released via a forum at. The current update of now can help victims of six variants of Crysis ransomware family with following extensions:. Unfortunately, a lot of users neglect password strength or use default credentials for this type of connection, which explains how come the felons behind the CrySiS virus have been so successful for months on end.
ESET releases free Crysis ransomware decryptor tool

Then, files containing the steps to follow to recover files shall be created, which will vary depending on the ransomware; however, Crysis will use text files or images to guide the user. Use arrow keys to highlight the Safe Mode with Command Prompt entry. Select the Restart option and wait for the system to load into Safe Mode. The trojan that has installed Crysis ransomware, unless removed, is to trigger its installation campaign as soon as a new strain of ransomware is available. Restore the encrypted files Crysis ransomware encryption is a sophisticated data modification.