Cyber capture. NGA Capture the Flag Cyber Challenge 2019-02-23
CyberLink
The Symposium provides a national forum for industry and government to work together to help solve the challenges of cybersecurity, community cyber readiness, and national defense. Please see to learn more about our global network of member firms. We seek to spark interest in the cybersecurity field by hosting hands-on trainings and interactive competitions that challenge and encourage individuals of all ages to explore new security techniques and concepts in a safe, open environment. Change takes effect immediately, there is no need to restart your computer. So what we did is we built an entirely new system that … they've never seen before, and doesn't work like they expect it to work. Why result do not come back? You also grant to Cisco a worldwide, perpetual, irrevocable, royalty-free and fully-paid, transferable including rights to sublicense right to exercise all copyright, publicity, and moral rights with respect to any original content you provide. As Avast is not very forthcoming with their.
CyberCapture

The break-in went undetected until last September. A group of Virginia Tech students took their skills to the bank this spring. McGee, deputy commanding general for operations at Army Cyber Command, told reporters Feb. A loud, celebratory whoop went up from Team Trogdor as the event resumed after lunch. The club turned out in force, bringing 70 students to compete and vie for first place! We serve all branches of the military, agencies of the Department of Defense, and the intelligence community, as well as the Departments of Homeland Security and Justice.
Parsons Cyber
There were no requirements, but finding the right combination of leaders and doers was one of the challenges of the game. No, we are not deadbeats. This competition is used as a learning tool for everyone that is interested in cyber security and it can help sharpen the tools they have learned during their training. Where some might get mad, I like to get even. The content is provided for informational purposes only and is not meant to be an endorsement or representation by Cisco or any other party.
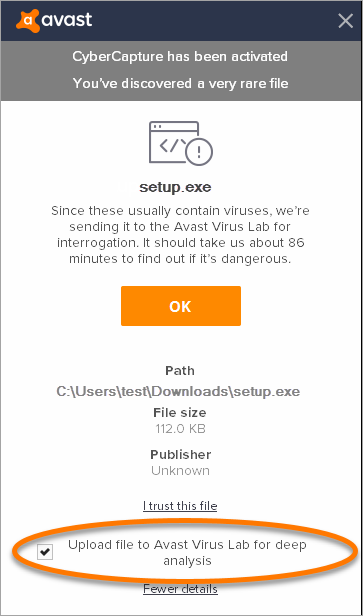
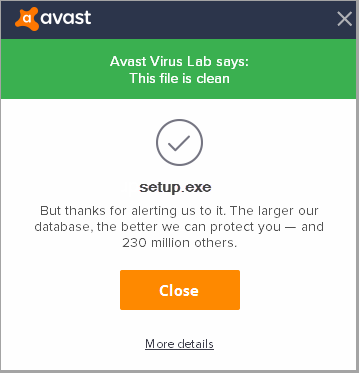
Avast Antivirus CyberCapture, great feature or privacy concern?
Hello, files downloaded from web and executed and low prevalent. All content is focused on the latest 2019 version. Opinions expressed here and in any corresponding comments are the personal opinions of the original authors, not of Cisco. Money Morning gives you access to a team of ten market experts with more than 250 years of combined investing experience — for free. But's there's definitely some unanswered privacy questions out there as of the time of the writing of this blog.
Build Those Cyber Skills: Here’s How to Host a Successful Capture the Flag Event

From there, it does some additional scanning and testing and determines whether it thinks it's harmful or not. Craig Seiler, member of Team Kobayashi Maru. You can can capture an image s from a movie and save it to file, your desktop as a wallpaper , or to the clipboard. The team with the most points at the end wins. See, when we spoke back on Oct. CyberCapture is basically an inverted Secure Virtual Machine. If you want bold and lasting results—Deloitte can help.
CyberCapture

My group consisted of three people from my cohort, including myself. Their own real-life stories and insights can prove to be valuable to the participants. Comprehensive fansite about Avast Antivirus 2019 — the World's most popular antivirus. Experience matters when it comes to stopping contemporary cybercriminals. Seriously, this is frustrating, you hear something positive and you're excited about it and then when more details emerge, it's the same old Avast. What conditions lead to a file being locked and uploaded by CyberCapture? His team managed to fix their communication issues and did better as the game progressed, though ultimately Team Trogdor won the day.
CyberCapture

Alternative solution and recommended is to add the specific program to , so CyberCapture is not triggered when the file is launched. They are not allowed to disable any network connections or turn off the machines. If the file is identified as malware it is automatically moved to Virus Chest and full system scan is recommended. How does Avast protect my privacy if my file is uploaded by CyberCapture? Thing is, I left out an embarrassing anecdote. If there is any rule violation, the team will incur a penalty or be disqualified. This game of cyber capture the flag, hosted by the 780th Military Intelligence Brigade, was an unclassified force-on-force network exercise that enforced practical lessons on how to operate as part of a joint environment in the cyber domain.
Annual Capture the Flag Cyber Challenge

There can be more than two teams as the teams are not trying to attack each other. It's almost hard to be enthusiastic anymore about new technology in avast! Milos I don't understand logic behind their design at all. He's a Pulitzer Prize-nominated writer and reporter, lauded by the Columbia Journalism Review for his aggressive style. It doesn't look like Avast provides a list of all your files that they upload to their cloud. At these events, participants faced questions from reverse engineering a program, to steganography, network forensics, and more! There are flags text files, folders, images, etc. But the situation got me thinking a lot about our brute-force protection system when reading about the latest big cyber intrusion.
CyberCapture

No wonder the bad guys compromised 500 million accounts. You shouldn't allow an application on your computer to upload any file personal, medical, financial etc. Seiler and members of the 780th enjoy hosting events like this one. This type of hands-on experience is not part of most traditional computer science programs. Hames, Soldiers, Defense Media Activity See more at httpsoldiers. Could Avast give some information on this? Hi Two days ago, i downloaded SecureMyBit.