Cyberghost mac address. #1 Cyberghost Strongvpn 5 5 Number Of Ip Addresses 59 500 Reviews + Discount Codes 2019-04-12
Top 10 Best Free MAC Address Changer Tools for Windows

In this technique, all packets originating coming from a source outside of the network are filtered on the gateway in the network using a source address from the network to make sure that that they can originate from a real source. Go to your account and log in with the created account credentials. Some consumers have fears about offering up personal financial information to strangers on the web. Anyone who has usage of your personal computer can install one, so make sure that you've got your personal machine password protected and that you limit use of it. But how exactly the heise. I hope that clears it up for you. You can take a look at the all the changes made in the log window.
#1 Cyberghost Strongvpn 5 5 Number Of Ip Addresses 59 500 Reviews + Discount Codes

If you find yourself in a very predicament and want immediate relief, applications can be purchased and processed twenty four hours a day. It belongs to the company, instead of you. That means, all your traffic will go via Amazon rather than directly to the pages you want to access, which of course raises some privacy alarms: all your habits, history, basically all you data will transit Amazon. High Anonimity Proxy: This is quite similar for the distorting proxy, other than it is more honest. Different people have different reasons why they'd wish to spoof the network. You can either enter the address manually or simply generate an address automatically.
How to Track any MAC address Geographical Location

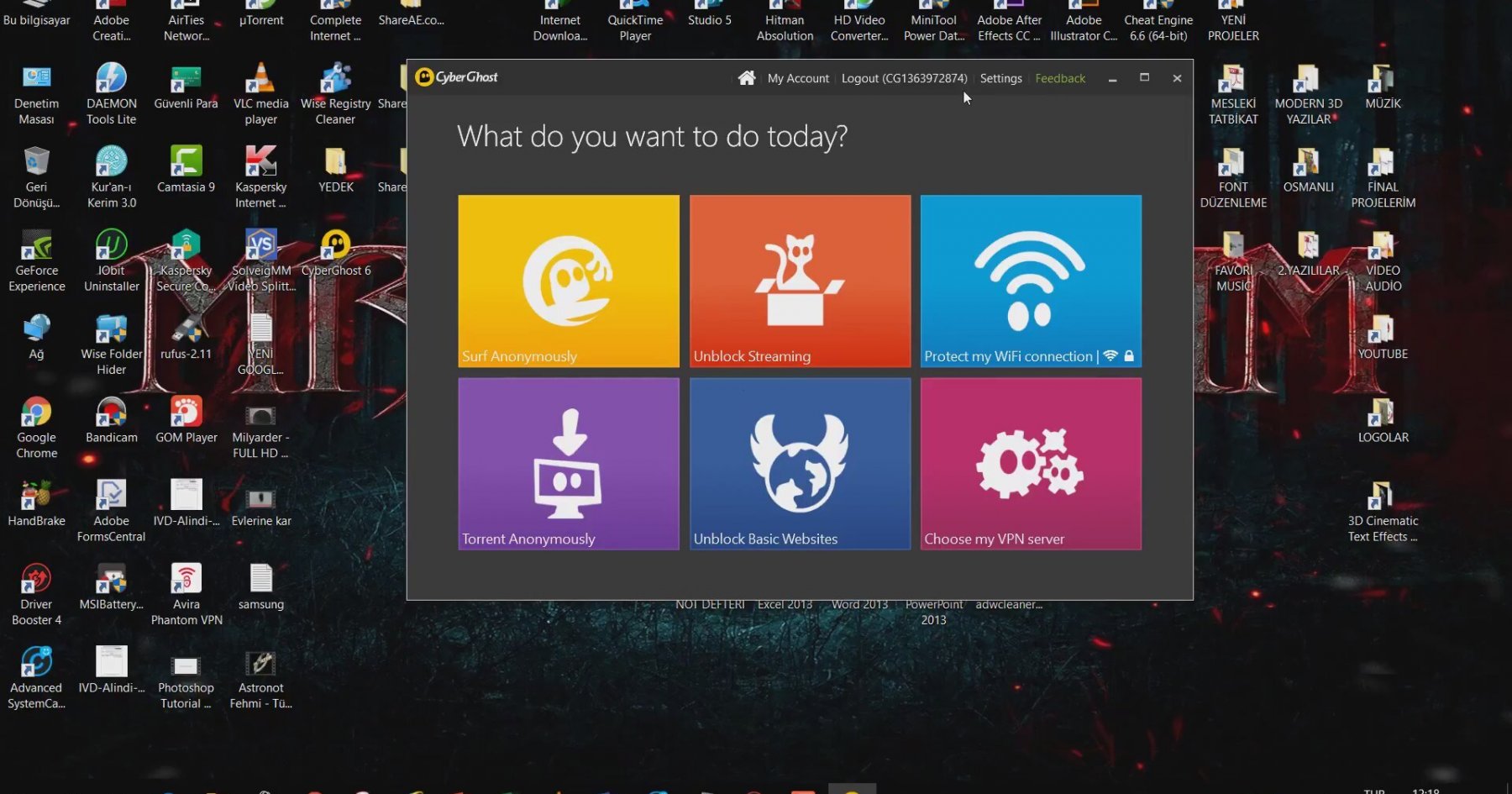
Alternatively, We can run the below command to retrieve the mac addresses of a remote computer. The wikiHow Tech Team also followed the article's instructions, and validated that they work. Also Available: With over 3,000 fast servers in 60+ countries and over 30 million users. While FreeGate, Tor and UltraSurf works extremely well on any computer, FoxyProxy are only able to provide on computers which have Mozilla Firefox installed and is used being a default web browser. Software keystroke recorders operate behind the scenes within your systems sub-processes, as well as the heightened keystroke recording software can email everything you've typed on the person who installed it. Active programs remain active even when there can be a change of wireless connection.
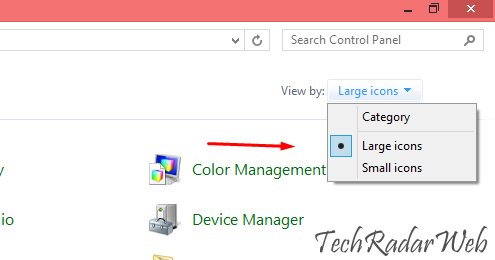
How to Spoof MAC Address in Windows 10 / 8.1 / 8 / 7 OS
If it needs to make a request then it gives the server a unique key. It may look like a small graphic see above image , or like a tiny computer monitor. But with the hackers, it might often be alarming to work without necessary protection. The results of the process, which will requires a couple minutes, will let you know the rate at which you are eligible, too. Most of this of course depends on the devices being in use.
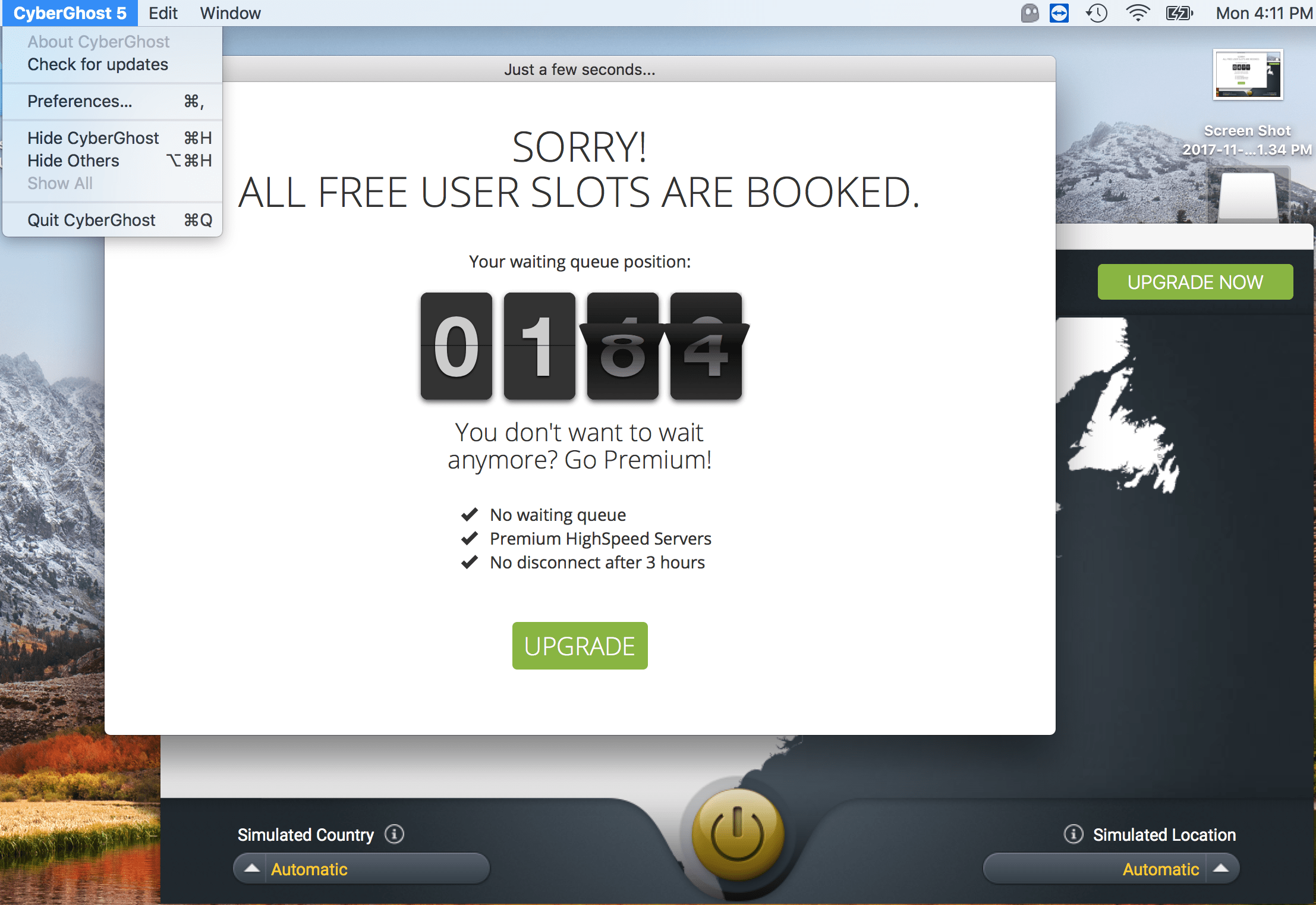
How to install CyberGhost VPN on Mac

There is arping, but we need rarping. Your personal account will also be protected, as well as any information obtained is held secure, even after you no longer make use of the services. CyberGhost is a multi-platform, truly complete and constantly updated privacy solution. So instead you should utilize network encryption for authentication. Internet security professionals oftentimes should obscure the address that they are working from to test their own security systems. How To Hide Your Internet Usage. The Government is trying to create a new set of laws that would permit the authorities to access private information of any Canadian, whenever, no warrant needed.
Technitium MAC Address Changer

With mobile virtual private network, users are allowed gain access to their company's resources while traveling. Modern hardware keystroke recording products are shaped just like your keyboard cord, and never look out of place, so be cautious or you might overlook them. Source: Also, David Cameron, Prime Minister of the United Kingdom, announced new measures, that would restrict Twitter or other social networks. Paid services likewise have the benefit of there becoming an accountable party when something fails. The tool was swift enough to start working in a matter of seconds. Register online in the site and download the program to your system within the office network. No need to download anything.
#1 Cyberghost Strongvpn 5 5 Number Of Ip Addresses 59 500 Reviews + Discount Codes
This is great because there is something for everyone. Host based authentication works on the public host key for authentication that's highly vulnerable to hacking. Now, that you simply have checked your computer for the key logger it is time to provide you with a few choice for Secure Browsing At Work - Strategies for Secure Browsing At Work. Secure Browsing At Work - Strategies for Secure Browsing At Work. Using this tool you can even find those addresses that are hidden for privacy or change them especially when they are used for internet access authentication.
Get mac address from command line (CMD)
You will get the details of your selection below. You can watch whatever programs you desire, in almost any country, without notice sufficient reason for complete privacy. We pass hundreds of surveillance cameras everyday without even knowing. The free version is the most basic one called Evaluation Edition which offers some of the essential functionalities. To mention a number of, Tor, UltraSurf, FoxyProxy and FreeGate. However, it misses a few enhanced features that are available in the paid versions.