Cyberghost vpn mac os x. CyberGhost VPN Basic for Mac OS X 5.0.14.12 2019-02-21
CyberGhost VPN for Mac

This signifies that they are buying of your stuff and they're selling to you, that also implies that they can 'fix' the price tag on the currency pair if they may be crooks. So, when you are on your MacBook in a café, shopping online or doing some work, you can rest assured that your online activity will be protected. Mac users can use the original BlueStacks for this purpose. Server based remote session services enable numerous users to connect with a single server all on the same time. By using this software it is chance to no third person can steal your personal data, your personal conversations, browsing history or online transactions, even on public WiFi. Just follow the downloading and installation steps bellow: 1.
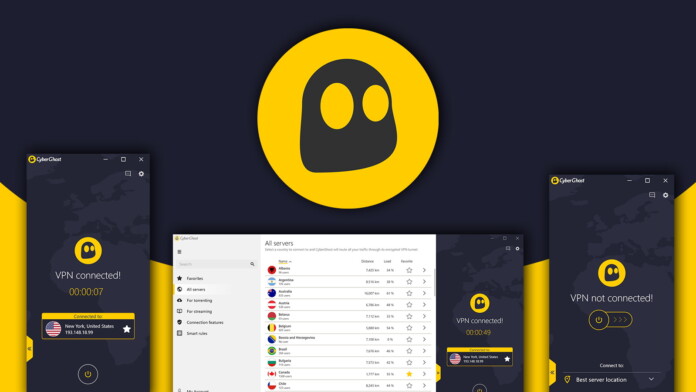
CyberGhost VPN Basic for Mac OS X

A rule of thumb would be to see in the event the pips are 'fixed pips. But, with the program being implemented, I can no more allow this. Unprotected WiFi connections often give the Network Administrators a chance to snoop into your personal data. Host based authentication runs on the public host key for authentication that is highly vulnerable to hacking. The use of this application is that you can view your desired sites and pages on a bigger screen of your computer.
CyberGhost VPN for Mac

You are logged in as. Censorship and monitoring from the governments and corporate entities is becoming rampant. This is not a major problem unless you are used to using it on Windows and need that feature, but something to keep in mind if switching over. Anonymous Browsing Another function of this service is privacy. To unblock a website or an application, you must run it within your Android emulator.
CyberGhost VPN for PC
You can get cyberghost vpn review. This is why lots of people choose the iPhone simply because it really is arguably among the safest smartphones around however, you will still need to take a few things into account to make sure that your phone will be safe. It keeps you anonymous online to protect your online privacy. Two main issues to become discussed here: 1. These steps are login your personal account, you will connected after accept your credentials and third is secure. Summary: optional Count: 0 of 1,500 characters The posting of advertisements, profanity, or personal attacks is prohibited.
@1 Anyconnect Vpn Windows Mac Os X Linux Ssl Vpn Compare Trusted VPN Worldwide

If you do not receive the confirmation email within the next hour, please make sure that you used correct email address, and that the message is not filtered by your spam filter. Therefore, data transfer, user operations, and location addresses are hidden, allowing you to surf anonymously. Privacy Isn't A Guarantee - Not Anymore It's not merely the hackers anymore. Malicious programs could ruin or steal information that is critical and irreplaceable. They are scanned with a router or firewall and also the packets that seem suspicious are with held. If none is found about the routing table, it really is assumed the packet has been spoofed as well as the router drops the packet immediately.
CyberGhost VPN Basic for Mac OS X

The first method which you can use is to reduce host based network authentications. Though the auto-lock feature isn't really a burglar alone, it's certainly a great feature when added using a password. Compatible Macintosh computer with an Intel x86 processor. Apple has become able to really be in addition to the smartphone industry and I believe how the phones by them self are already very safe nevertheless, you must be mindful and thus listed here are four things you should do to fully protect your iPhone. This is the best vpn. If the problem continues, please use a different email address. To prevent spammers from being abused, the email program should not be hidden this does not apply to webmail, the mail application accessed by the browser.
@1 Anyconnect Vpn Windows Mac Os X Linux Ssl Vpn Compare Trusted VPN Worldwide

Also Available: With over 3,000 fast servers in 60+ countries and over 30 million users. By connecting to a secure Cyber Ghost server, you can access content from around the world. Cute little icon if that's anything to you. Be sure to be smart about your phone also to follow these simple tips in order that you have the ability to avoid any future problems. It keeps you anonymous and protects your data when connected to public Wi-fis providing you at the same time, absolute freedom to access censored or blocked content.
CyberGhost VPN for Mac
In summary, I've been very pleased with my experience and anticipate to utilize service for quite a while to come. I mean, the kids that experiment the house don't desire to go entirely home just to get yourself a song that they were looking to let their friends have a look at. Thus, you will enjoy a secure experience even on public, unprotected WiFis. However, some brokers allow their trader clients to do business with each other. Too often does a person lose their phone and can end up with books problems. Some from the reasons might be for criminal activities or to visit websites that have morally unacceptable content.