Decode password md5. Online Password Cracker 2019-05-13
MD5 Password Hashes Cracker: Recover Password Using MD5 Hash
The answerer above probably used one of these. Thus, to complicate the search by the rainbow tables databases , it is recommended to add salt a prefix or a suffix to the password. The success rate is over 95%, and many complex ciphertexts can only be queried by this site. I then sorted them, and enlarge the final wordlist by creating a script that multiplicated the list to finally lend to a unique and pertinent wordlist. Good hash functions, however, have the property that finding such pairs is extremely difficult, even though they are guaranteed to exist.
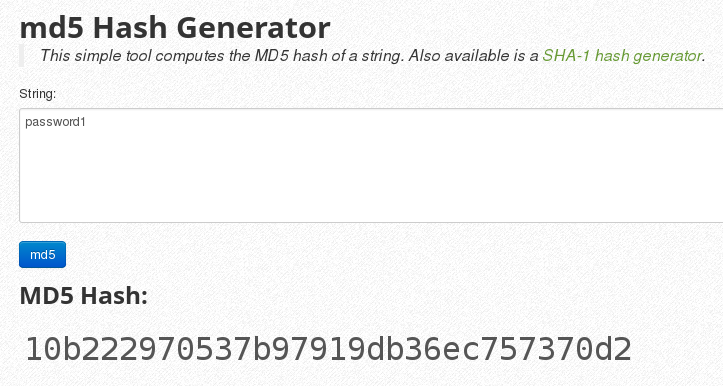
MD5 Cracker Page

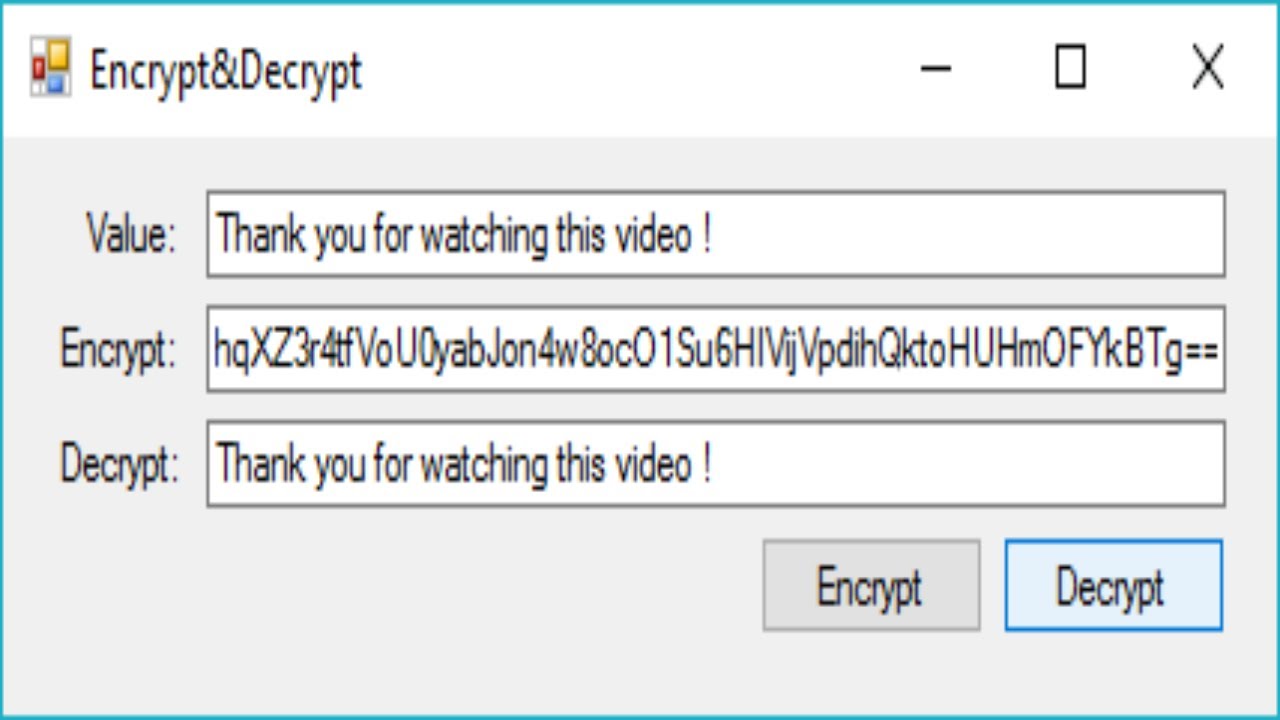
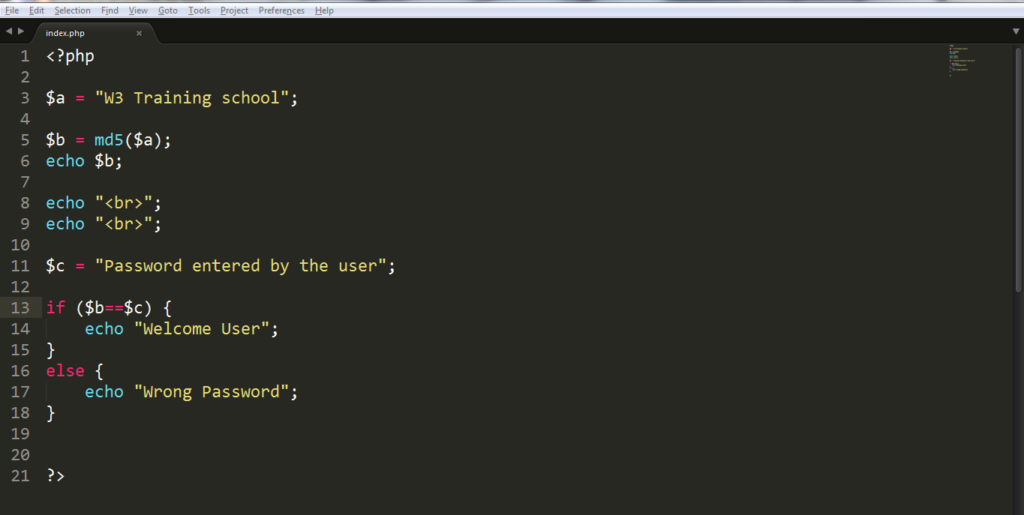
Other than that, less security minded people will probably use the same password for all online services and this will potentially allow the hacker to gain access to all other services belonging to the user. Mark Hi There Cheers for the response and information. The form allows up to 5 hash values at a time and the result is shown instantly at the bottom of the form. The idea is that you generate a hash from the password, and then when provided with the password you can confirm that it hashes to the same value. It is still useful because the results are shown in real time without the need to refresh the webpage. It has been operating stably for more than ten years and enjoys a good reputation.
mysql
Here we have a huge md5 hash database to help you with decryption. Natively, the notions of salt and cost are applicable. But there are several attacks possible that could identify the origin message with certain probability. They have a public forum which is very helpful because anyone can sign up for a free account and post a hash cracking request as long as it is below 25 hashes. Ask a new question Source code dCode retains ownership of the source code of the script Hash Function online.
MD5 hash decrypter / decoder: Decode MD5 online with this tool

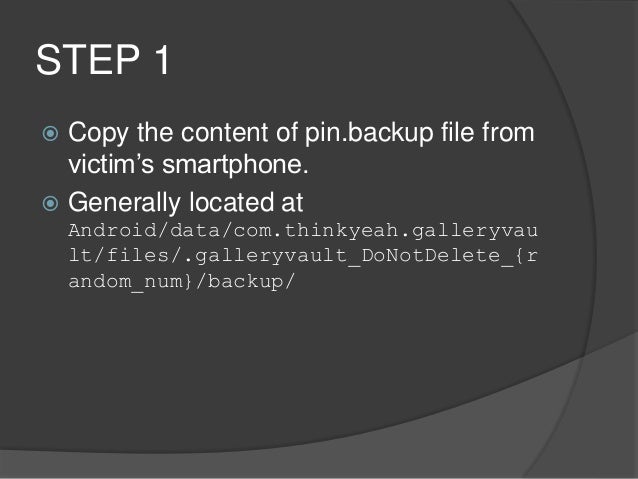
This is obviously unsafe because a hacker that manages to hack into the server will instantly have access to thousands of passwords. But as I mentioned above, I believe this is purely only used in the case where a routers configuration has to be restored from a backup. . It can still be used as a checksum to verify data integrity, but only against unintentional corruption. We also applied intelligent word mangling brute force hybrid to our wordlists to make them much more effective. Great work, as usual Raymond. It seems that sha256 is becoming more and more used in order to replace the old md5 hash function.
Hash Functions (+Salt) Decrypter
The recovery engine is fully configurable, so you can adjust the recovery options as needed. If the word is not in the dictionary, then there will be no result. Try to configure the command when no one is looking around :- Narayan I realized this was answered but I wanted to add to this another solution. This can be compared to a fingerprint as a purportedly unique, short and convenient representation of a human being. Hash functions are used in computers and cryptography.
Is this possible to decrypt MD5?

Say that you are paranoid about the password being seen by someone looking over your shoulder while you enter it into the router. One of the properties of the hash function is that they are non-invertible one way functions. The hash functions apply millions of non-reversible operations so that the input data can not be retrieved. I looked for days to find any wordlist online. We have been building our hash database since August 2007. Example: dCode has for hash e9837d47b610ee29399831f917791a44 Example: dCode has for hash 15fc6eed5ed024bfb86c4130f998dde437f528ee Example: dCode has for hash 254cd63ece8595b5c503783d596803f1552e0733d02fe4080b217eadb17711dd See the dCode pages for each hash function to know how it works in detail: , , , etc.
MD5 Password Hashes Cracker: Recover Password Using MD5 Hash

Also Standard version does not support. Although not directly, it is possible to perform a reverse lookup. It remains suitable for other non-cryptographic purposes, for example for determining the partition for a particular key in a partitioned database. This is not possible except by trying all possible. However thinking a little more about this and it now makes sense. The fingerprint is usually returned as characters.
Hash Functions (+Salt) Decrypter
A salt is a string that you add to the user's password to make it longer, and add special characters. The lookup is based on several online databases as well as engines using rainbow tables. Unfortunately, because of the fixed length of the hash, there must exist pairs of different inputs that yield the same hash value. Even if it is more secure though, you should still consider using a salt to improve security. Answers to Questions The hash functions use computer data format and apply nonlinear and non-reversible functions with a strong avalanche effect the result is very different even if the input data is very similar. Currently it stores over 500 billion not million entries, and will explode to at least 2 trillion within the year.
MD5 Online
The only way to decrypt a hash is to know the input data. We have also implemented Password Recovery Engine for Cell processor used in Sony PlayStation 3 ; more information is available on request. The principle of hashing is not to be reversible, there is no decryption algorithm, that's why it is used for storing passwords: it is stored encrypted and not decryptable. One of such attack is Rainbow Table Attack with chaining. Our decrypter database is coming from all the wordlist I was able to find on the internet. Crackstation's lookup tables were created by extracting every word from the Wikipedia databases and adding with every password list we could find. It is therefore possible to test all the possible words in a dictionary to check if their fingerprint is the one sought.