Define software crackers. Hackers vs Crackers: Easy to Understand Exclusive Difference 2019-03-29
Crackers
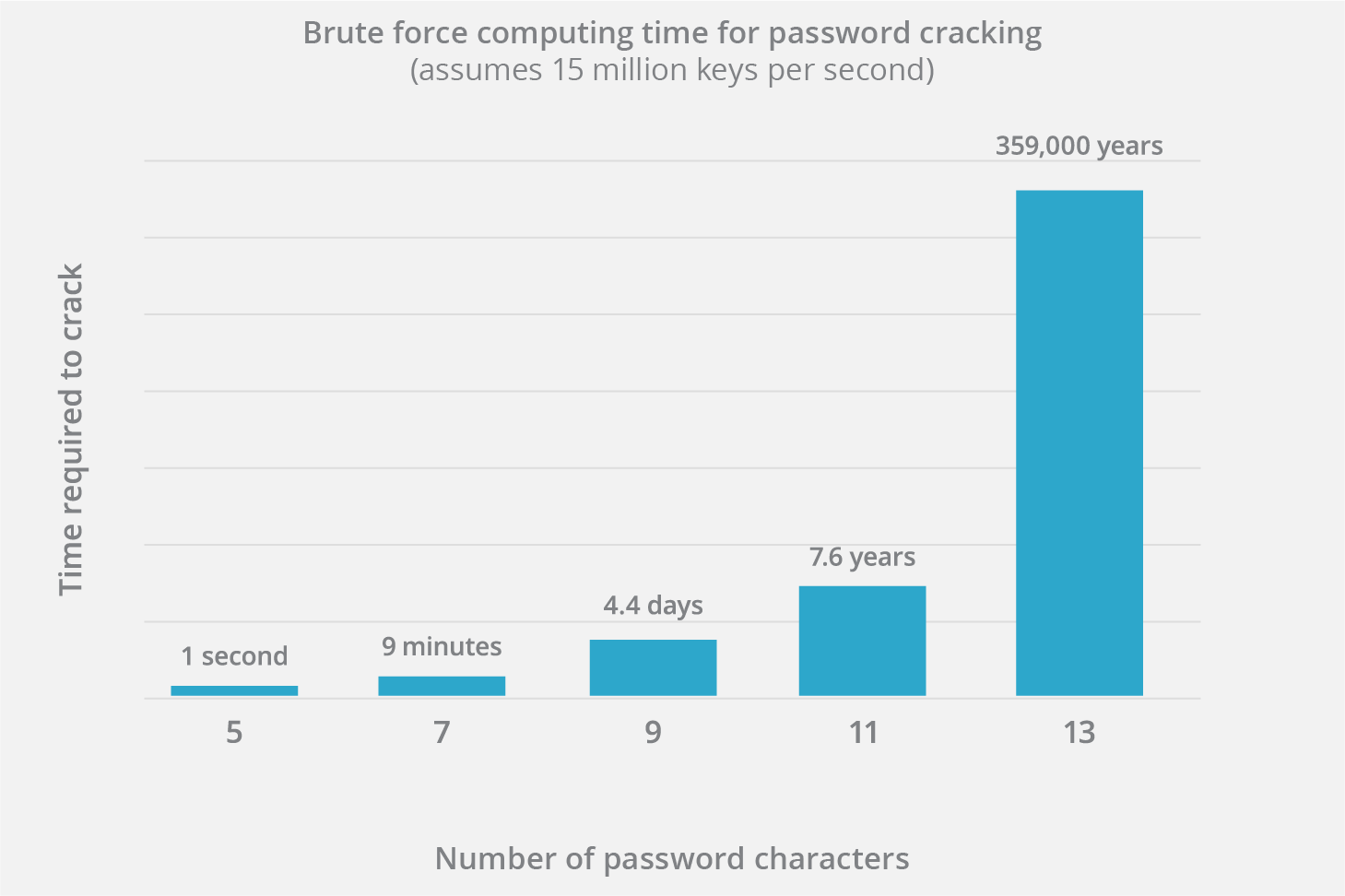
But having a password combination of a-z, A-Z, 0-9 and other special characters with a good length will make it harder to crack. His defacement of the Web pages included an activist statement, as well as instructions for other hacktivists. They usually have a deep interest in computers and programming. Often applies to game software. This can be helpful where users have been advised to include a number in their password. Although that community does indeed use reconnaissance, so does the cracker community. So therefore, it is just how they work which makes them entirely different from each other.
Crackers dictionary definition

They do so to violate the security of the systems. They can steal credit card information, they can destroy important files, disclose crucial data and information or personal details and sell them for personal gains. They break into systems to see if they can, then log off. Generally there was little to no defense available to the copy protection system, since all its secrets are made visible through the simulation. Most samurai hackers claim to be loyal to their employers and to engage only in ethical cracking.
Urban Dictionary: Cracker

Crackers can easily be identified because theiractions are malicious. And this is because most of the times people confuse the term hacking with cracking. The Hackers being the good guys are called white hats while who violate computer security for personal gains. It also uses dictionary and brute force attacking for generating and guessing passwords. A crack refers to the means of achieving, for example a stolen or a tool that performs that act of cracking.
cracker Definition from PC Magazine Encyclopedia

A gray hat is a name given to an otherwise ethical hacker who walks a fine line between legal and illegal hacking. A has shown that the protection may not kick in at any point for it to be a valid crack. It attempts to crack Windows password from hashes. For purposes of clarity when communicating with others about security issues, I recommend you do the same. As such, hackers obtain advanced knowledge of operating systems andprogramming languages.
10 Most Popular Password Cracking Tools [Updated for 2018]
As a result, modern phreaks intent on cracking the telecommunications systems often rely on criminal acts such as stealing phone cards and cloning cell phones. While a hacker works totally in the interest of a company or an individual, the cracker works totally in an opposite manner. They often use these tools without any real understanding of what the actual program does. For a portrait of the typical teenage cracker, see warez d00dz. In this post, we are covering a few of the most popular password cracking tools. Often these crackers create tools that enable less-skilled criminals to subvert security and exploit weaknesses in computer systems. These type of hackers protect the cyberworld from every possible threat and fix potential future security loop holes.
What is cracker?

Thieves tend to be linked to electronic sabotage and espionage. These upgraded drives allowed the user to make exact copies of the original program with copy protections in place on the new disk. Still, it can be useful for you. The holes allow steam to escape during baking. Now it is up to you. Download Rainbow crack here: 3. But it is totally not to be confused with crackers.
Crackers dictionary definition

Variety in passwords: One important thing you must always take care. Popular commercial copy protection applications which may be scanned for include and StarForce. These tools are totally dependent on the dictionary, so success rate is lower. That is what makes the two so different. Never use same password everywhere. This tool is available for free. Another theory asserts that it was applied due to Georgia and Florida settlers Florida crackers who cracked loud whips to drive herds of cattle, or, alternatively, from the whip cracking of plantation slave drivers.
Cracker

They discover the weak points in the network securities and work tirelessly and put in their best efforts to seek solutions to these network issues. This tool supports various network protocols. There may be a theft from the accounts of credit card holders, important data may be lost and secure information may be divulged. Hacktivists The hacktivist is a gray hat or cracker who defaces Web pages to bring attention to a political agenda or social cause. White hats may be security professionals, hired by companies to audit network security or test software. So, you can pause the attack process any time and then resume whenever you want to resume. The most dangerous crackers Although the majority of crackers are relatively unskilled, not all are inept.