Dictionary attack example. Python Hashcracker (Dictionary Attack) 2019-05-03
Dictionary Attack Using Burp Suite

This article needs additional citations for. You can create many tools like Port Scanners, Hashcrackers, Servers and Clients…and many more. If it appears in any electronic list, including census information, dictionaries, thesaurus or phone books your password will not withstand a basic dictionary attack. All paths are hardcoded in the file so you will need to update them before you compile the source code. However, this is also the weakest form of authentication, because users frequently use ordinary words as passwords. As Sewell showed in his blog post, even a well-hashed password will only slow a skilled attacker down if they're able to steal a hash table. Security is often rated based on how long it would take a theoretical attacker to break it using brute force methods.
Attacked
Alternately, you could display a after the fourth attempt. Indeed, this combination of characters is commonly used as a password. Attack is the most general word and applies to a beginning of hostilities, especially those definitely planned: to attack from ambush. It is more likely that the key was stored in some temporary file on the disk somewhere, or fell to a dictionary attack. Under these conditions, I could see attackers regularly achieving up to two password attempts per second.
Dictionary Attacks 101

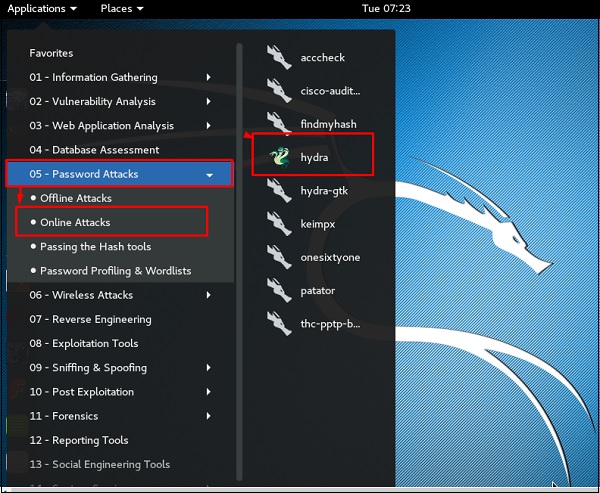
He's the webmaster of www. In Twitter's case, the attackers really hit the jackpot: the user with the weakest password happened to be a member of the Twitter administrative staff. Ransomware is a subset of malware in which the data on a victim's computer is locked, typically by encryption, and payment is. Dictionary attacks are typically done with software instead of an individual manually trying each password. Dictionary attacks work because many computer users and businesses insist on using ordinary words as passwords. A message is sent to e-mail addresses consisting of words or names, followed by the at symbol , followed by the name of a particular domain.
Password Recovery Methods

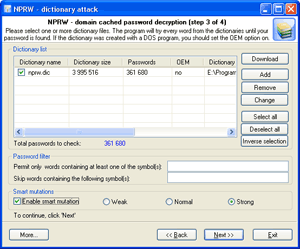
The Rainbow table is optimized for hashes and passwords, and thus achieves great space optimization while still maintaining good look-up speed. Yes and no—the weakness is in how passwords are stored. This requires a considerable amount of preparation time, but allows the actual attack to be executed faster. The methods are secure against off-line dictionary attack and incorporate an otherwise unauthenticated public key distribution system. Brute force attacks involves repeated login attempts using every possible letter, number, and character combination to guess a password. Nowadays internet usage is growing dramatically because of this, a vast majority of companies and individuals that provide services have a website so customers can know about the service s that is available to them.
Dictionary Attack Using Burp Suite
The best protection against this kind of attack is to use a salt random characters in your password. This guide describes the basics of Java, providing an overview of syntax, variables, data types and. Assault almost always implies bodily violence: to assault with intent to kill. Attack, assail, assault, molest all mean to set upon someone forcibly, with hostile or violent intent. To molest is to harass, to threaten, or to assault: He was safe, and where no one could molest him. Dictionary attacks are rarely successful against systems that employ multiple-word phrases, and unsuccessful against systems that employ random combinations of uppercase and lowercase letters mixed up with numerals.
Dictionary

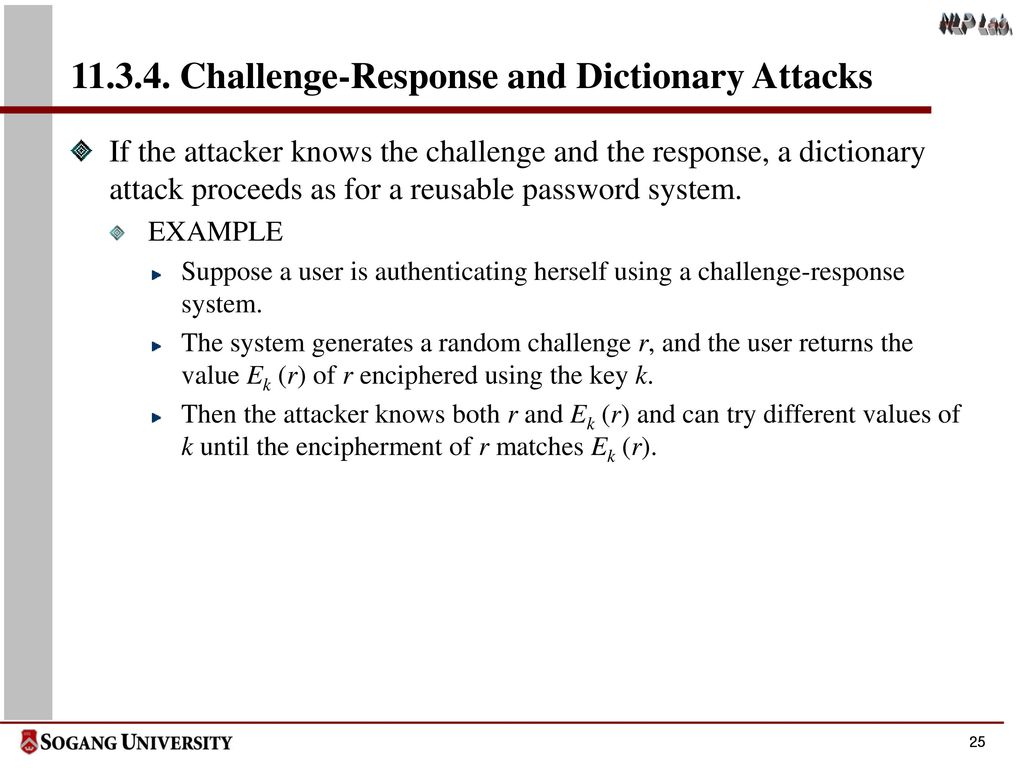
Offline brute force attacks have no connection to the system being targeted, which is a large part of what makes them so dangerous. In contrast with a brute force attack, where a large proportion key space is searched systematically, a dictionary attack tries only those possibilities which are most likely to succeed, typically derived from a list of words for example a dictionary hence the phrase dictionary attack. If you don't do this, you're practically setting out a welcome mat for anyone to launch a dictionary attack on your site, an attack that gets statistically more effective every day the more users you attract. Then in cracker tab you find all imported username and hashes. That's not to say there isn't an element of randomness to dictionary attacks—they typically account for common passwords that append a number or special character on the end of a word, or substitute a letter for a number, in order to guess any number of variations on a word or phrase.
Brute force and dictionary attacks: A cheat sheet

All it takes is one user with a weak password to provide attackers a toehold in your system. Generally, dictionary attacks succeed because many people have a tendency to choose passwords which are short 7 characters or fewer , single words found in dictionaries or simple, easily predicted variations on words, such as appending a digit. The output should be the following: Let's get things started. Password Crackers will try every word from the dictionary as a password. From this point of view we can assume that choosing a password is a critical issue and everyone should be aware while choosing their password. Dictionary Attack Dictionary attack definition according to Wikipedia is: As you can see from the previous definition, Dictionary attack is just a technique that uses a file that has thousands of common, default and weak passwords and uses them against the login portal and tries all of them until one of these passwords allow the attacker to gain access to the private resources for example an administration panel. When a hacker's objective lies beyond their reach thanks to good cybersecurity practices such as password rules and encryption, they might turn to another method: Brute force.
How to use in a sentence
In contrast to a , where a large proportion of the is searched systematically, a dictionary attack tries only those possibilities which are deemed most likely to succeed. After clicking the login button, the request will be intercepted by Burp Suite, so right click on the request and click on send to intruder. Adding a single random character in the middle can make dictionary attacks untenable. So how can you prevent an offline brute force attack from succeeding? Moreover, the access portal is an administrative access portal which if you have successfully logged in, you will have full access on that application. Pre-computed dictionary attacks are particularly effective when a large number of passwords are to be cracked. Offline brute force attack prevention is a bit trickier: If an attacker gains access to password hash files, it's only a matter of time before they're walking in the front door.