Dictionary attack john the ripper. Cracking Encrypted PDF Password Using Dictionary Attack 2019-02-18
Dictionary attack
Simultaneous invocations John can handle several simultaneous jobs, each writing to the same john. All the same applies to wordlist mode rules as well. The more experienced users and software developers may , along with revision history information for each source file. More generally, the -i:charset option refers to the charset. How Do Password Crackers essentially work? Incremental mode In incremental mode john does not use a word list, but just tries all possible passwords. You simply have to select Kali linux iso image for making bootable disk. In this way, it can find hidden pages on any website.
Free Download John the Ripper password cracker

Now, that we understood what features are offered by John the Ripper, let us now also get exposed to the tools that could enable us to visualize such features on a practical level. . Among the operating systems supported by John the Ripper, there is a plenty. However, for offline software, things are not as easy to secure. These attacks can take several minutes to several hours or several years depending on the system used and length of password.
Popular Tools for Brute
The password dictionary file used is the standard password. Different systems store password hashes in different ways depending on the encryption used. Very strong passwords are but one method to that end. It is similar to the Ophcrack and Lophtcrack tools. More the passwords to try, more the time required.
Cracking password in Kali Linux using John the Ripper

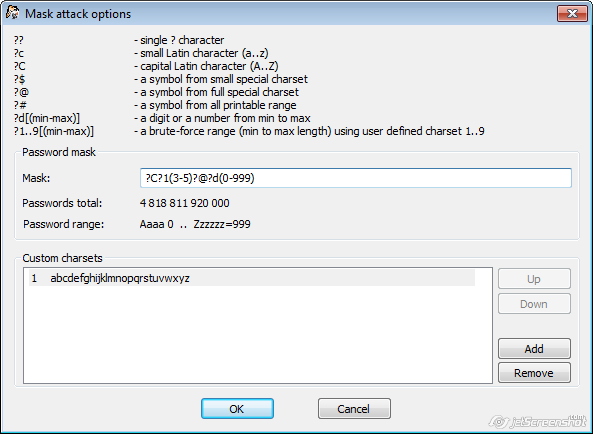
This is not always a good idea, though, since lots of people do not check their e-mail or ignore such messages, and the messages can be a hint for crackers. Dictionary attacks often succeed because many people have a tendency to choose short that are ordinary words or common passwords, or simple variants obtained, for example, by appending a digit or punctuation character. It supports various attacks including Brute-Force attack, Combinator attack, Dictionary attack, Fingerprint attack, Hybrid attack, Mask attack, Permutation attack, Rule-based attack, Table-Lookup attack and Toggle-Case attack. Reverse brute-force attack A reverse brute-force attack is another term that is associated with password cracking. See for an example of an authentication system compromised by such an attack. Other rainbow tables are also available to download. In fact, it is recommended that you do not truncate candidate passwords in your wordlist file since the rest of the characters beyond the length limit of your target hash type are likely still needed and make a difference if you enable word mangling rules.
Free Download John the Ripper password cracker
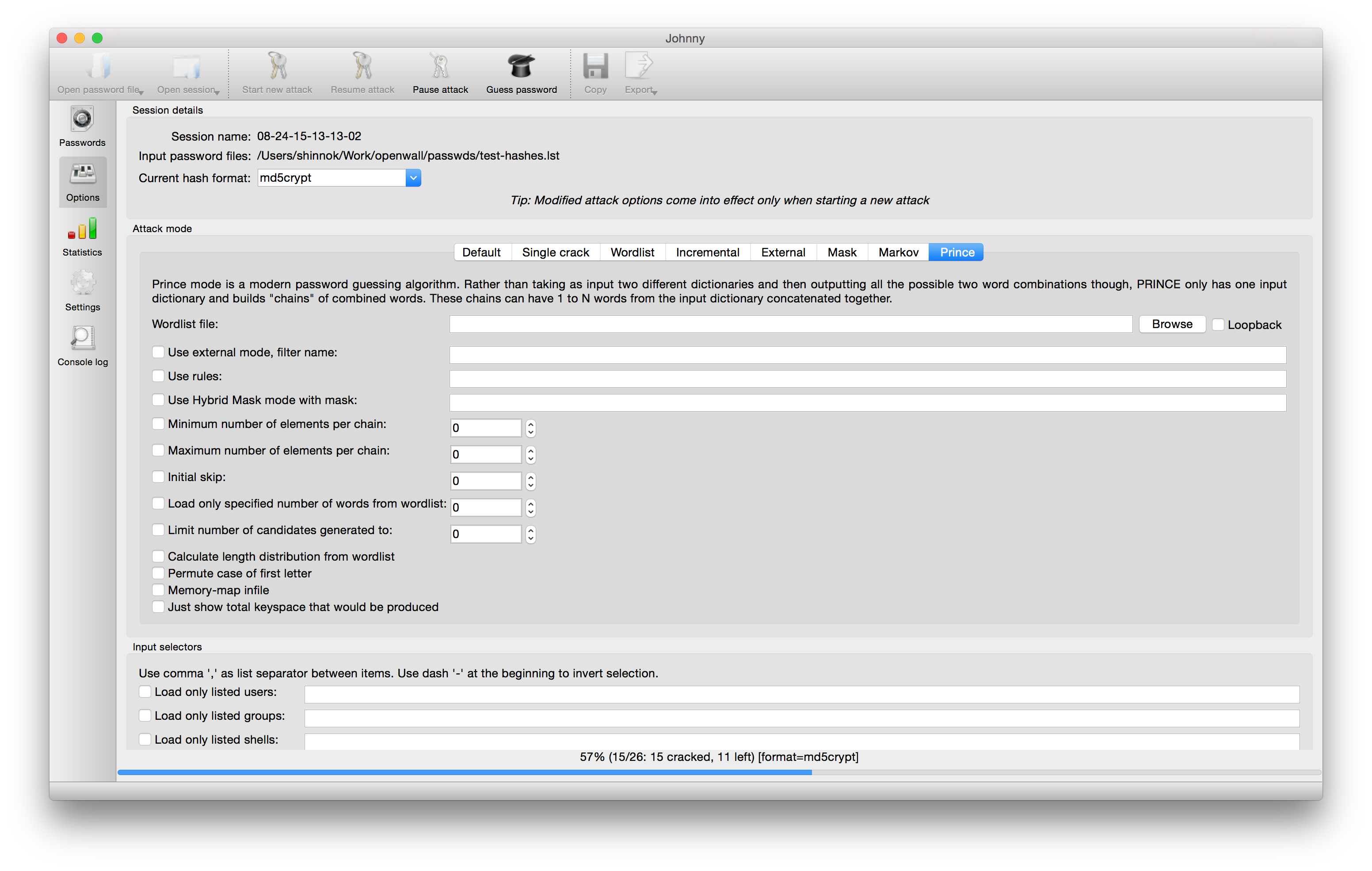
Password crackers are primarily after root or administrative account passwords which grant the administrator full access and privileges to the operating system. John the Ripper is free and Open Source software, distributed primarily in source code form. Especially that it has the capability to include and deal with many more hash types on which encrypted passwords are based in the first place. The storage requirements for the pre-computed tables were once a major cost, but are less of an issue today because of the low cost of disk storage. This method is useful for cracking passwords which do not appear in dictionary wordlists, but it takes a long time to run. This attack is best when you have offline access to data. Popular tools for brute-force attacks Aircrack-ng I am sure you already know about Aircrack-ng tool.
Dictionary attack
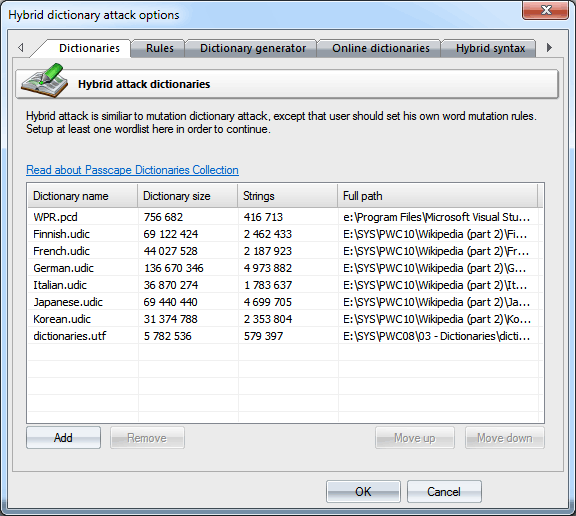
Rainbow tables basically store common words and their hashes in a large database. One of the best security tools which can be used to crack passwords is John the Ripper. I'm taking a security class in school, and we have to implement a custom cipher and crack some supplied ciphertext using a dictionary attack. This will modify dictionary words in many ways, so that you also gives You, you1, 2you, 4you, youyou, you? This tool supports both dictionary attacks and incremental attacks. If an organization used a single dictionary word as a password, it may only take hackers a few minutes to break the codes.
Free Download John the Ripper password cracker
Then run: mailer mypasswd Configuration file. So we can now use john —show option to list cracked passwords. Password policies designed by well-meaning system administrators dictate the required number of characters and the complexity of passwords, but is that dictated complexity enough to protect user accounts from hackers? It takes text string samples usually from a file, called a wordlist, containing words found in a dictionary or real passwords cracked before , encrypting it in the same format as the password being examined including both the encryption algorithm and key , and comparing the output to the encrypted string. There are many such tools available for free or paid. On ubuntu it can be installed from synaptic package manager. Usually an external utility is more convenient.
Free Download John the Ripper password cracker
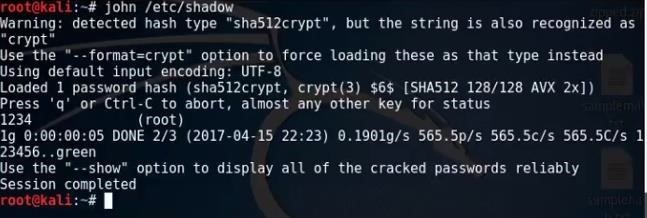
Want to get started with password cracking and not sure where to begin? Invocation Basic invocation: % john passwdfile Here passwdfile is a file with one line per hashed password. Speed One is mostly interested in the number of passwords tried per second. John is a free tool from. Please refer to for information on the programming language used. On the there are pages entitled. Now a days hashes are more easily crackable using free rainbow tables available online. It helps in reducing the time in performing the attack.