Does superantispyware remove viruses. How to remove malware from your Windows PC 2019-03-02
SUPERAntiSpyware

If your antivirus program allows it, run the scan in Safe Mode. Keylogger: A piece of software designed to record every key pressed on your keyboard, mostly used to steal your usernames and passwords. The current versions of the popular web browsers and no longer support these operating systems forcing many users to use outdated versions or extremely old versions of Internet Explorer which is rife with security flaws. Emotet itself does not attempt to do much harm; instead, it opens the door for other malware who pay the doorman on the way in. Garrison Keillor While not limited to invoices or Christmas cards, these emails attempt to get the user to click the download link and then to open the document. Neither the beta AntiSpyware nor the shipping CounterSpy version 1.
What is spyware? And how to remove it
Spyware is oftenpackaged with some freeware application you may have downloaded. Recording network traffic is generally only done by businesses, which helps TrickBot evade detection on personal computers. Many malicious apps pretend to be antivirus programs or tools. However, if you download software that installs spyware, using Firefox, Internet Explorer or any other browser won't matter, you'll get infected. Keeping your system up to date with software patches is also something we recommend to help protect yourself.
McAfee Virus Removal Service
Sadly, there might be none because the virus disguises its processes well. It can easily infect your device and it can be hard to identify. Tests of Spyware Doctor proved time consuming. This is designed to encrypt your files quickly to avoid detection. In this picture, you can see an example of such web browser and also an example of fake Chrome Update ad.
How to Remove a Virus (with Pictures)
It fully encrypts files that are less than 1 Megabyte, and encrypts only a single Megabyte of files larger than that. However, the app is closely related to adware - ad-supported software that displays misleading pop-ups and redirects to dubious websites. Resetting Microsoft Edge browser Method 2 : If Method 1 failed to help you, you need to use an advanced Edge reset method. Thus, they should be more cautious. Once installed, thespyware monitors user activity on the Internet and transmits thatinformation in the background to someone else. How it works Anatova is distributed through peer-to-peer P2P file sharing networks.
How to remove a Trojan, Virus, Worm, or other Malware

Even trading software or documents with friends may result in the stealthy delivery of a spyware program hidden within. Hijackers - A program that attempts to hijack certain Internet functions like redirecting your start page to the hijacker's own start page, redirecting search queries to a undesired search engine, or replace search results from popular search engines with their own information. If you're using AntiVir, run the installer, and then reboot. This kind of malicious software disguises itself as legitimate software. What is an easier method of accessing a system is to get the user to do it for you. To use the Disk Cleanup utility included with Windows 10 just type Disk Cleanup in the search bar or after pressing the Start button and select the tool that appears named Disk Cleanup.
SUPERAntiSpyware Blog
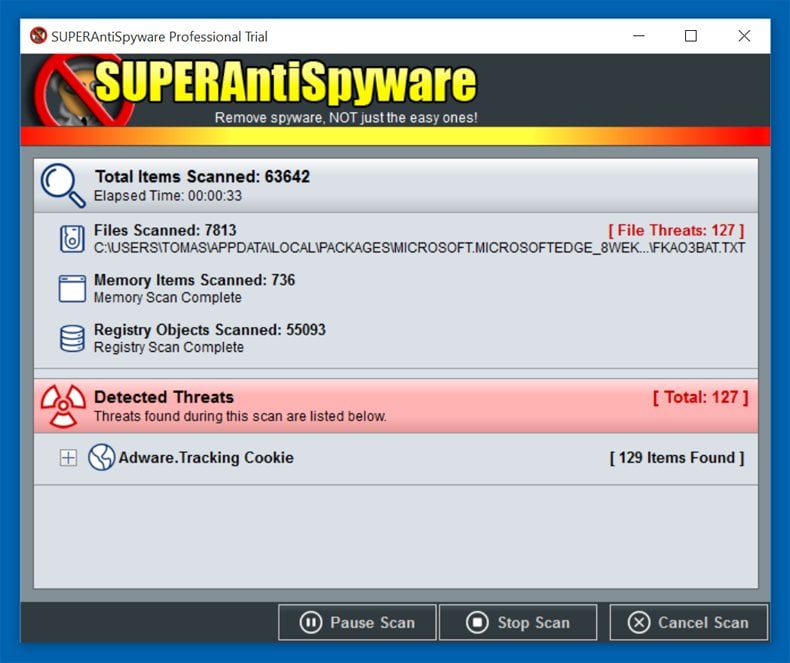
Run a complete scan with free curing utility Dr. We also have a self-help section that contains detailed fixes on some of the more common infections that may be able to help. Being able to restore your important documents from a cloud or local backup is the best way to thwart a attack. If prompted, allow the scanner to as appropriate. Our instructions call out these danger spots, but if you don't feel confident about performing them, ask for help from a knowledgeable friend or from the experts on a spyware-removal Web forum such as , , or.
Does spyware doctor just scan or does it also remove virus

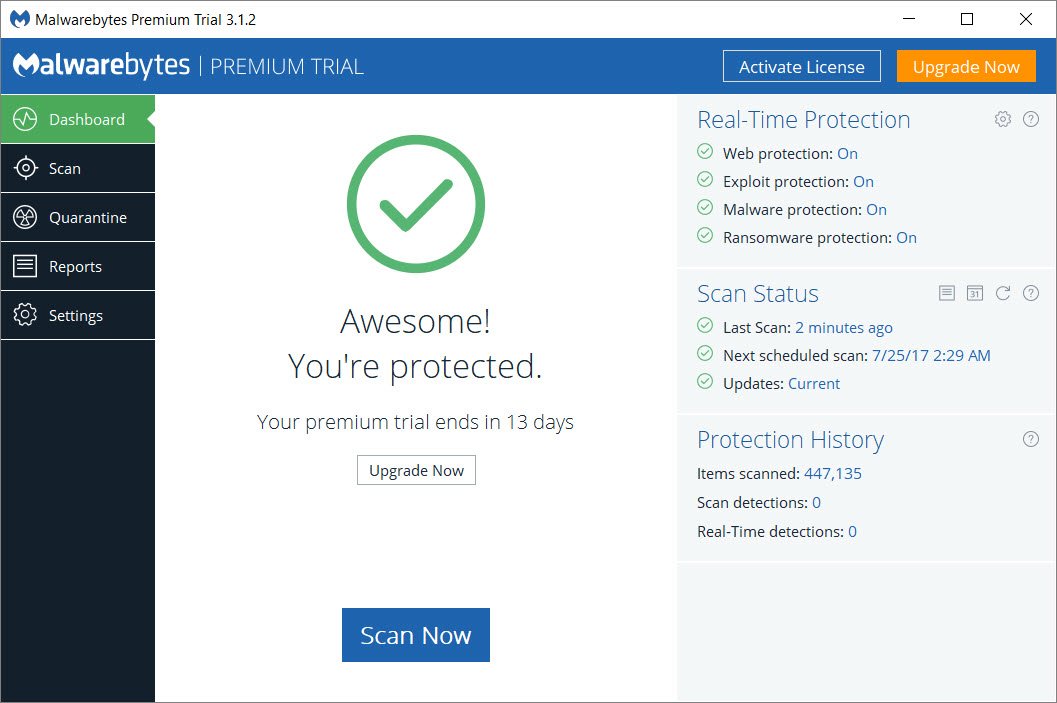
Some malware get into your computer and appear to do nothing at all. If the software gives your system a clean bill of health but you still think that your system has acquired some malware, consider running a custom scan with Malwarebytes and trying the other scanners mentioned earlier. Even after the primaryapplication is removed, the spyware will still be in there. There are two types of antivirus programs. HijackThis will scan your registry and various other files for entries that are similar to what a Spyware or Hijacker program would leave behind. Before finishing, the script launches the command cmd.
How to Remove a Virus (with Pictures)
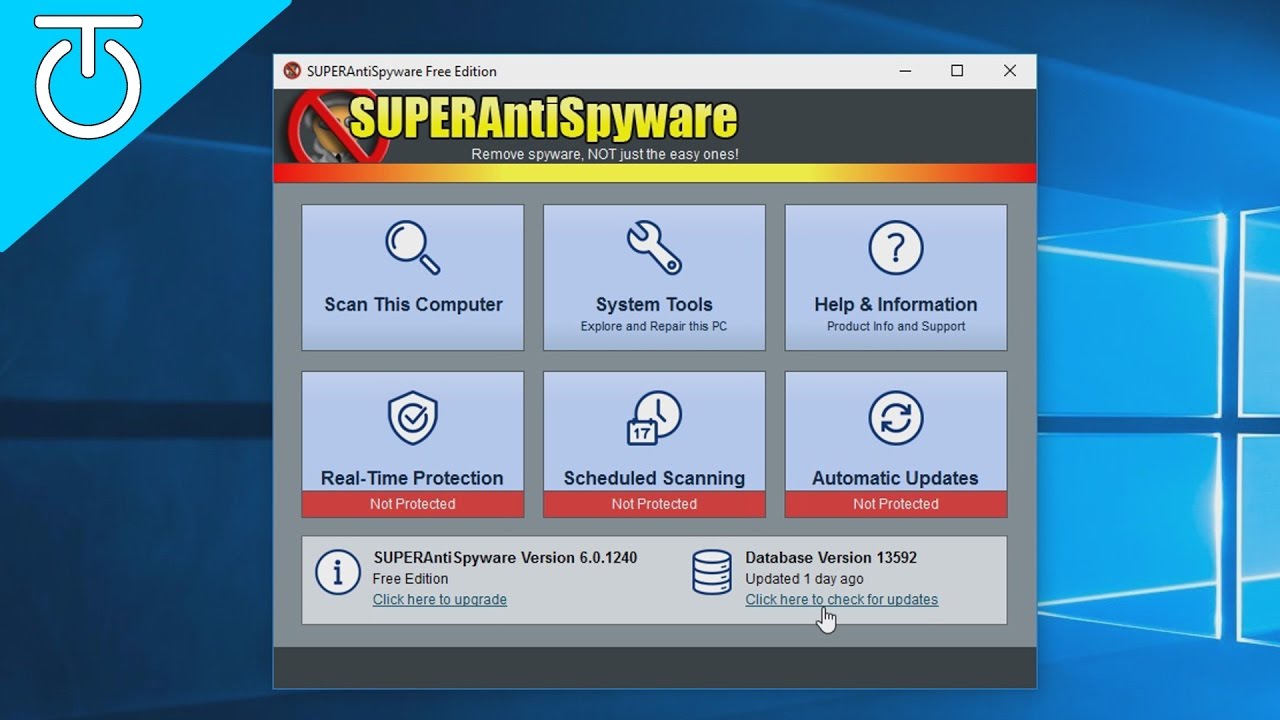
Both Mac and Android devices become infected when you install an app with malicious code. The quickest way to catch all of its components is to run a security software like. Once you do this, select Preferences. The Android robot is reproduced or modified from work created and shared by Google and used according to terms described in the Creative Commons 3. While it is highly likely that Ytmp3 users themselves enabled the site to allow notifications, the ads might be caused by adware hidden inside the computer. Spyware is often programmed to change the users homepageand may insert bookmarks.
What is Malware? How Malware Works & How to Remove It

Unfortunately there are a lot of malware that makes it very difficult to remove and these steps will not help you with those particular infections. Even though the larger files are not completely encrypted, enough damage has been done that they are, most likely, no longer usable. This malware checks your system language and refuses to run in several countries such as Iraq, India, and the Commonwealth of Independent States. This version of Chromium virus was developed by Epom Ltd. It is important to note that not all adware programs are necessarily considered malware.
How to Remove a Virus (with Pictures)
:max_bytes(150000):strip_icc()/superantispyware-5c5d8481c9e77c00010a483c.png)
Select 'Troubleshooting Information' Reset Mozilla Firefox Click on 'Reset Firefox' button for a couple of times Remove ytmp3. Click 'Remove' to get rid of each of them Reset Mozilla Firefox Click on menu icon and then on '? Once Quick Access Menu shows up, select Control Panel and Uninstall a Program. How does ServHelper works ServHelper is downloaded through Microsoft Word documents with macros. Try the following programs; they will stop all unwanted stuff from getting onto your computer. We use cookies and similar technologies to recognize your repeat visits and preferences, to measure the effectiveness of campaigns, and improve our websites.