Download brute force file. Brute Force Tutorial + Download for free [ HOW TO HACK ACCOUNTS ] 2019-03-02
Brute Force Tutorial + Download for free [ HOW TO HACK ACCOUNTS ]
It does not make brute-force impossible but it makes brute-force difficult. Example: If testing a bank in denver I might use the words: cash mile high broncs broncos elway cashier. Brute Force Attack Method tries all probable combinations of passwords to find back lost excel password. Brute-force attacks can also be used to discover hidden pages and content in a web application. It supports various attacking methods including Mask attack, Dictionary attack, Hybrid attack and Attack with Rainbow tables. Your question may have been asked already, or is in the sidebar.
Popular Tools for Brute

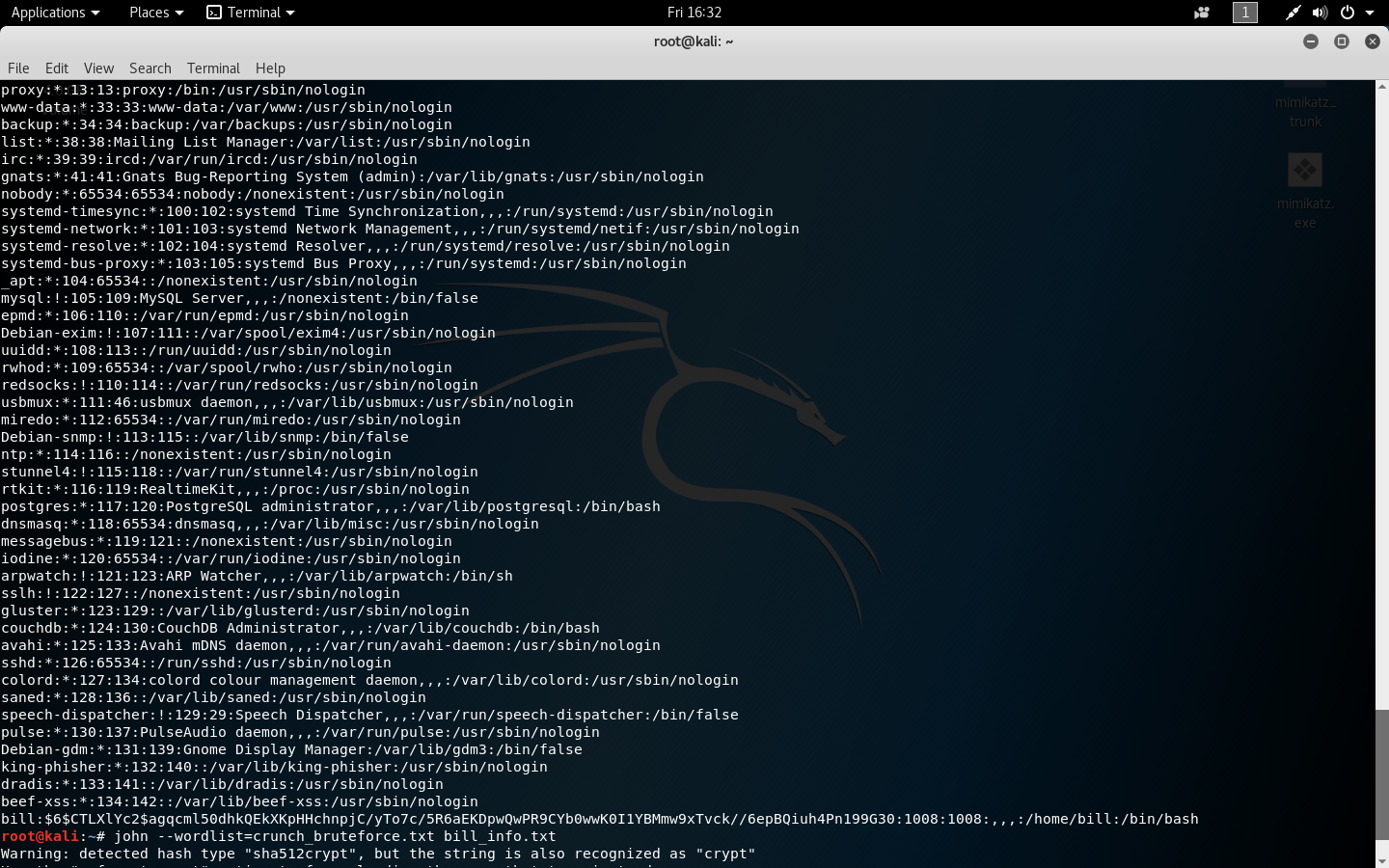
Download Aircrack-ng from this link: John the Ripper John the Ripper is another awesome tool that does not need any introduction. Registered users can also use our to download files directly from all file hosts where it was found on. Proxy a Online proxy grabber b Auto Clicker with proxy. It manages network flow and keeps attack traffic out. Brute Force Software are very useful especially in the cases where one has forgotten their password, and there are no means of accessing it back. Anthony Scans software to find whether it is harmful for computer and also checks for updates of security.
Router Brute Force v2.7.1 APK Free Download (Latest Version) for Android
A place to share resources, ask questions, and help other students learn Network Security specialties of all kinds. With this tool, you will have access to a wide range of target system as well as the ability to conduct scheduled scans. Mortinus I had difficulties with the pdf documents which needed to be edited before presentation, then I. We do not yet have a description of Bruteforce Save Data itself, but we do know which types of files our users open with it. Brute force is a technique that is used in predicting the password combination. You have to enter the possible characters with a space between each character, like this: 0 1 2 3 4 5 6 7 8 9 a b c d e f g h i j k. Do they have to change their password often? In this case, you can try the same password and guess the different user names until you find the working combination.
DirBuster Download

Some software may not have details explanation or their price, program version updated. Think if you know a password but do not have any idea of the usernames. Therefore, it will take a longer time to reach to the password by brute-forcing. This program is distributed as freeware. You may customize the extended settings for brute- force or dictionary break to search the entire password. Reverse brute-force attack A reverse brute-force attack is another term that is associated with password cracking.
Download Brute force dependencies files

However, for offline software, things are not as easy to secure. So, if you to provide your own passwords and want the app to check them to match the router password, you should be careful. It can automatically detect the type of hashing used in a password. With this software, the different aspects of a wireless network will be taken care of and thus let you gain easy access. Proactive Password Auditor helps secure networks by executing an audit of account passwords, and exposing insecure account passwords.
brute force attack Software
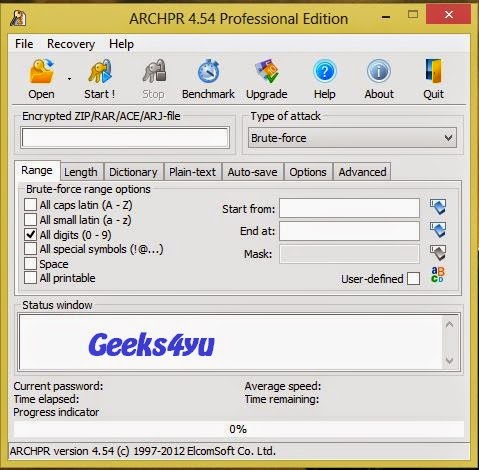
The user simply adds the required files or an entire folder before choosing the method. And if the password matches, the application shows directly to you. This is an easiest way to send files to someone who cannot accept them live. Now, you know that Brute-forcing attack is mainly used for password cracking. What nicknames does the company have. The software comes loaded with powerful features that let the users achieve a lot.
Download Facebook brute force v3 0 rar files
It can perform different attacks including brute-forcing attacks. Mask Attack Technique searches password from that one character which. Dictionary Attack method tries to search password from by default given word list and Mask Attack executable when an excel user who lost password. Using warez version, crack, warez passwords, patches, serial numbers, registration codes, key generator, pirate key, keymaker or keygen for brute force attack license key is illegal. This attack is best when you have offline access to data. Cyber criminals know you use Remote Desktops. Is there a naming schema for employ usernames? In this, attacker uses a password dictionary that contains millions of words that can be used as a password.
Popular Tools for Brute

Try a few programs and see which one works best for you. In this way, attack can only hit and try passwords only for limited times. Characters -A All Characters, Numbers, and Letters -min Minimum Size -max Maximum Size -o outputfile. If it is possible to recover the password within a reasonable time, the password is considered insecure. With our powerful recovery methods: brute- force, dictionary-based and user-defined mask attacks, it can help you to recover your lost password with ease! What DirBuster will not do for you — Exploit anything it finds. I am sure; the application can explore the key of the network. He is currently a researcher with InfoSec Institute.