Download crackstation wordlist free. Free Wordlist For Wpa Crack For Mac 2019-04-26
www.littleboyblu.com « SupraFortix Blog

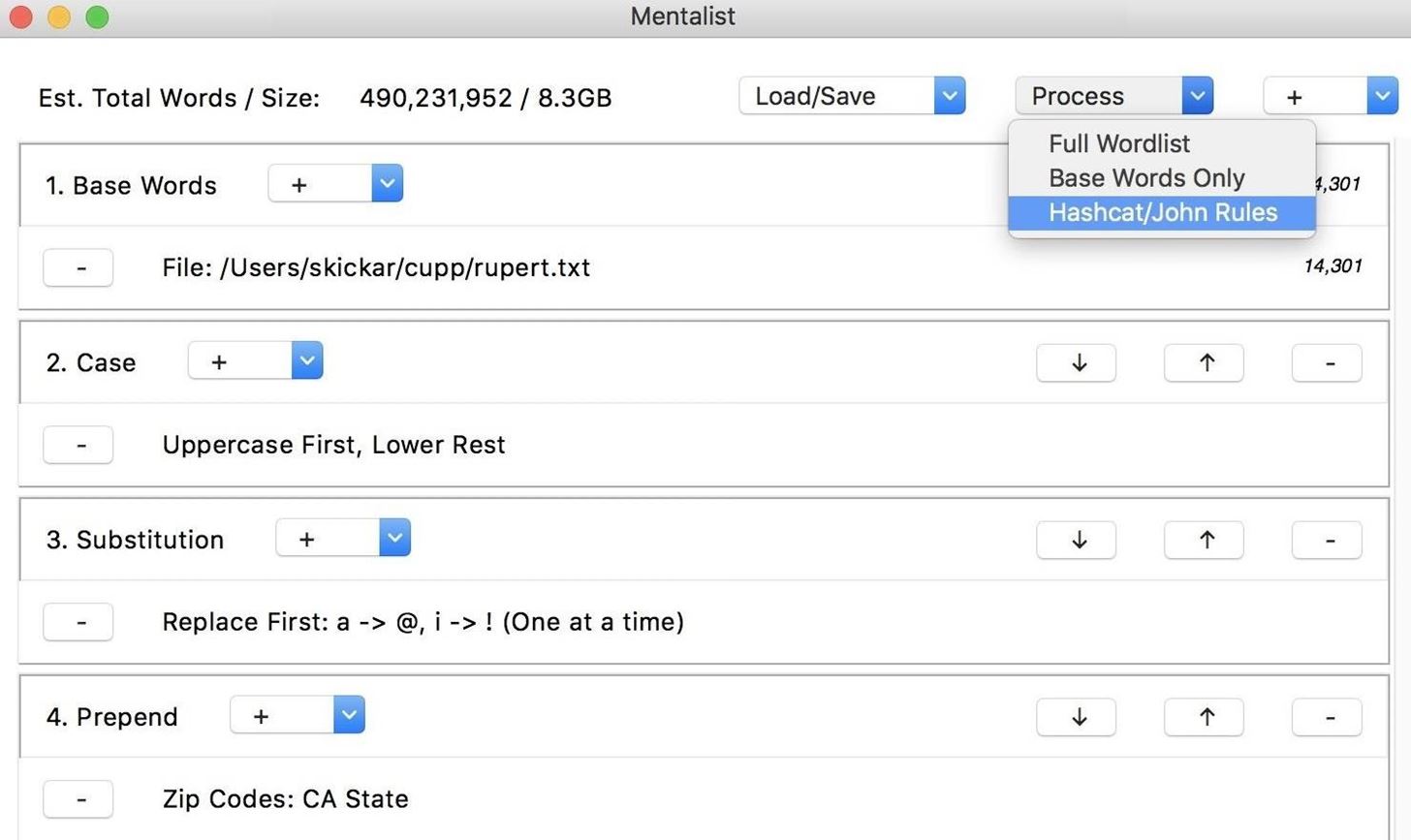
I like base words and then rules to modify them in a particular way. It's basically a text file with a bunch of passwords in it. Here are the results of cracking LinkedIn's and eHarmony's password hash leaks with the list. The science behind rule sets is very simple, however the correct application is very difficult. Hack wpa2 wifi passwords free download. If you have an idea of what the password parameters are for example, has to be 8-10 chars with only letters and numbers, no symbols , you can pipe crunch to most bruteforce programs with the tailored parameters. True mastery is everything in the middle, where analysis of passwords, patterns, behaviors, and policies affords the ability to recover that last 20%.
WPA / WPA2 Word List Dictionaries Downloads

Here's a tool for computing hashes easily. There are a lot of rules that can be added to a particular rule set to maximise the potential of a successful password crack. It also contains every word in the Wikipedia databases pages-articles, retrieved 2010, all languages as well as lots of books from Project Gutenberg. Also, this might be obvious to most, but I had a few people email me telling me none of the wordlists worked for them. How do I use the Ultimate2016 if there is no.
Large Password Lists: Password Cracking Dictionary's Download For Free
This manual will not be covering the installation of these tools, but will include references to their proper installation, and if all else fails, Google. Not the answer you're looking for? Wow thanks for sharing that! This is the only one free and dedicated tool for doing. What a boot manager is, and what it does. Did you know there is a manual to almost any program? One click and your in. But you still need a wordlist to perform a combinator attack.
Create a dictionary wpa + wordlists download
It will be useful to save these results for future reference. Nothing about a magnet link can be blocked once the link itself has reached the user without breaking the majority of Bittorrent altogether. Bottom line of what I am trying to say. The format of the list is a standard text file sorted in non-case-sensitive alphabetical order. The first step is information. If you use a different version then some of the command options may have to be changed.
CrackStation's Password Cracking Dictionary (Pay what you want!) [1.493 Billion Words @ 15GB] : netsec

Now my question for you is… how would i remove character symbols from the example below?. The included languages are: Afrikaans, Croatian, Czech, Danish, Dutch, English, Finnish, French, German, Hungarian, Italian, Japanese, Latin, Norwegian, Polish, Russian, Spanish, Swahili, Swedish, Turkish, and Yiddish. He uses lists as they are and rules to change them. Unlike madwifi- ng, the monitor interface has no Access Point field at all. Here are the results of cracking LinkedIn's and eHarmony's password hash leaks with the list. Because both interfaces share a common radio, they must always be tuned to the same channel - changing the channel on one interface also changes channel on the other one.
Wordlist Brute Force Attack,Word List Downloads,WordList password
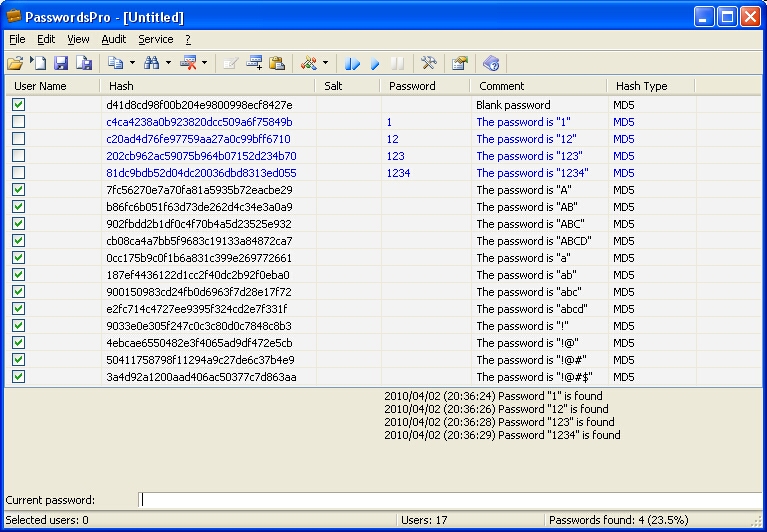
Included only in the full version and not available in the freely downloadable version of the collection is a huge list of all the common passwords and words from all the languages with word mangling rules applied to form other likely passwords, such as by adding capitalization or digits to words and any duplicates purged. Without limiting the rights under the copyright reserved above, no part of this publication may be reproduced, stored in, or introduced into a retrieval system, or transmitted in any form or by any means electronic, mechanical, photocopying, recording, or otherwise without prior written permission. Straight Cracking on its own compares hashes to words as they appear in wordlists. Dust Attack Exploit featured Framework free wifi generate key google. This is the sort of thing that scares me, I never really know whats going on. Good luck and the dictionarys above are a must have.
Large Password Lists: Password Cracking Dictionary's Download For Free
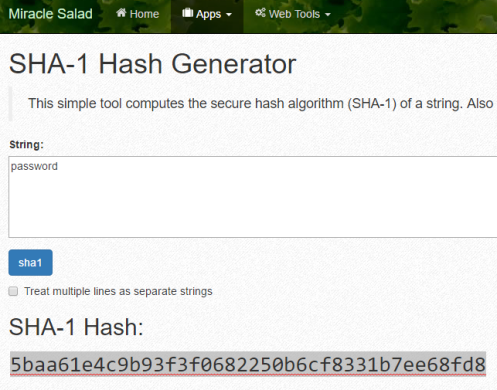
For instance, if you need to remove all blank lines from a file, a one-liner will do the trick. This diagram illustrates hash cracking process that utilises a simple rule set. The practical demonstration utilises pre-made rule sets, included in Hashcat directory by default. Pass this to your tool of choice as a straight dictionary attack. Its common to log thousands of attempts every day for an internet connected host.
Word List Downloads
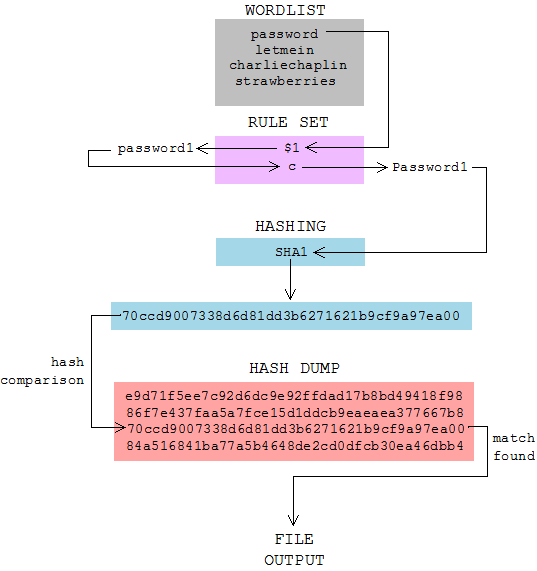
This demonstration utilises three different wordlists:. Because it has attracted low-quality or spam answers that had to be removed, posting an answer now requires 10 on this site the. It also contains every word in the Wikipedia databases pages-articles, retrieved 2010, all languages as well as lots of books from Project Gutenberg. It describes various Hashcat rule sets, which can maximise the potential amount of cracked passwords utilising basic wordlists. The format of the list is a standard text file sorted in non-case-sensitive alphabetical order. Mbit are 'b', 6, 9, 1. I also prefer custom, small, language specific targeted wordlists.