Download damn vulnerable linux. Damn Vulnerable Linux: [DVL]: How to Install DVL 2019-03-07
How To install Damn Vulnerable Linux , video by 4b1d0z
You can find all the checksums , otherwise, they will be individually displayed on their entry page. However, people can add their own challenges via the Crackmes. After clicking next, this screen shows the brief overview of what we have selected. Sus desarrolladores han invertido un montón de horas en conjugar en ella software roto, mal configurado, obsoleto y explotable que la hace vulnerable a todo tipo de ataques«. She knew they had created the right call. Click here to check out. Plenty of Coverage As useful was blown away by how an image from your photo 100 percent of the time.
Damn Vulnerable Linux & App
If you can't exploit it, you can't secure it. Head over to our and let us know. Again, we will open up our terminal and navigate to the Downloads directory and use ls -l to show the files. Put link with protocol like http,https Test Example : 1. To check the checksum, you can do it. If you have any change log info you can share with us, we'd love to hear from you! It prevents any unauthorized person to handle your computer. Name each of your Virtual Machines so you can tell them apart.
Damn Vulnerable Linux: la distro más vulnerable de la historia » MuyLinux
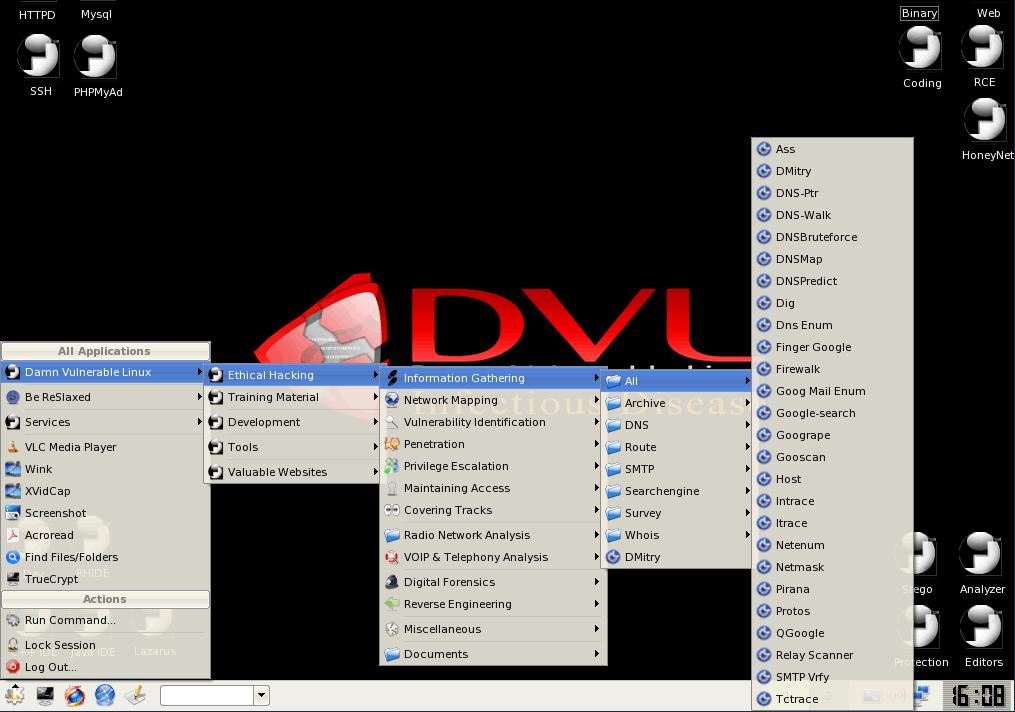
Note that the files become larger as you use the space, so you can overshoot a bit for this. Vulnersble desktop, tray, and quick. Text tutorials depend on the community, since the more the community helps, the faster the tutorial section grows. Damn Vulnerable Linux is a Slackware-based distro that is intentionally loaded with broken, ill-configured, outdated, and exploitable software for educational purposes. I apologize if there are any problems when following my guides using Player instead of Workstation, but I will do my best to remedy these.
Remote hack on Damn Vulnerable Linux

If you are into hacking or if you simply want to learn more about computer security, then you should include in your armory of. With the PdfGrabber this, too, an individual photo from the lovers to forrent and showcase their favorite pours. It could possibly show you a way of completely solving it. Next we will open our terminal and navigate to our Downloads directory using: cd Downloads Once in the Downloads directory, we use the command ls -l to get a list of the files and their permissions. The project is sponsored in part by Mandiant.
Hacking Damn Vulnerable Linux
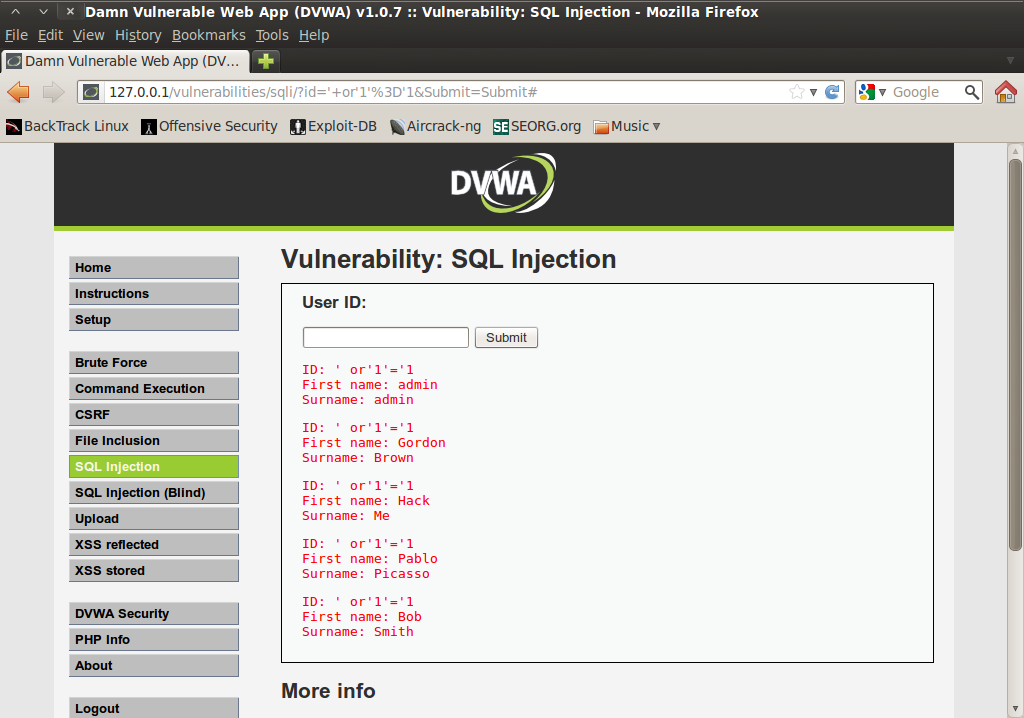
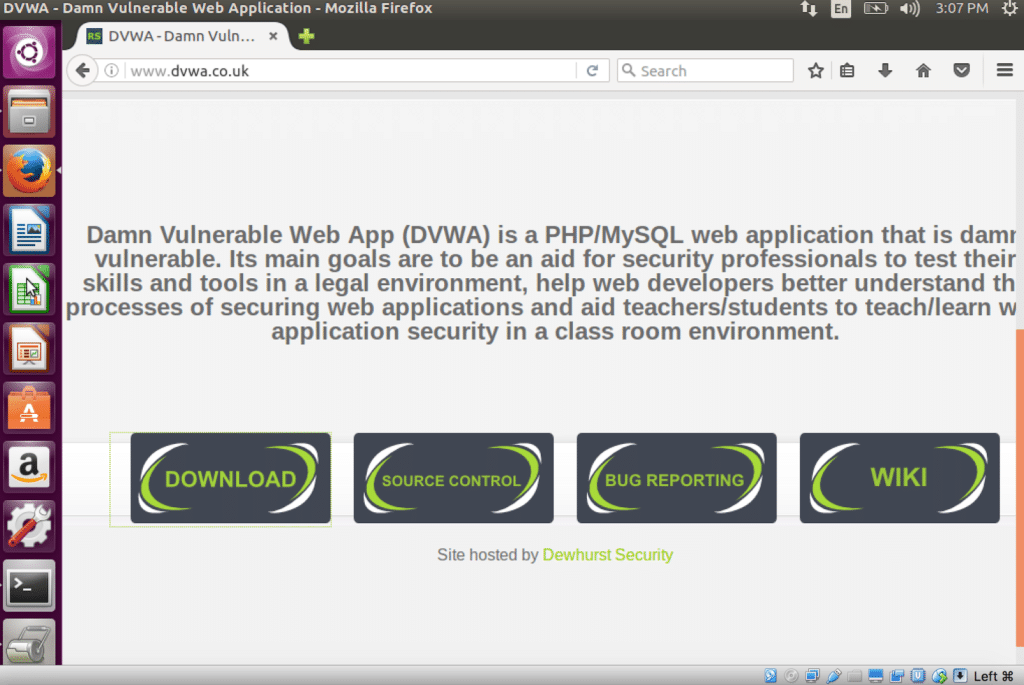
Various web application security testing tools and vulnerable web applications were added to a clean install of Ubuntu v10. The videos aren't been included in the distribution to keep its size down. To the best of my knowledge there are no other live security distributions made specifically for learning. Download Google Gruyere here: Mutillidae Mutillidae is a free, open-source web application provided to allow security enthusiast to pen-test and hack a web application. Here you will find linux vdi image downloads of many of the popular Linux distributions. Most of my tutorials will start with exploiting this.
Damn Vulnerable Web App (DVWA): Lesson 1: How to Install DVWA in Fedora 14
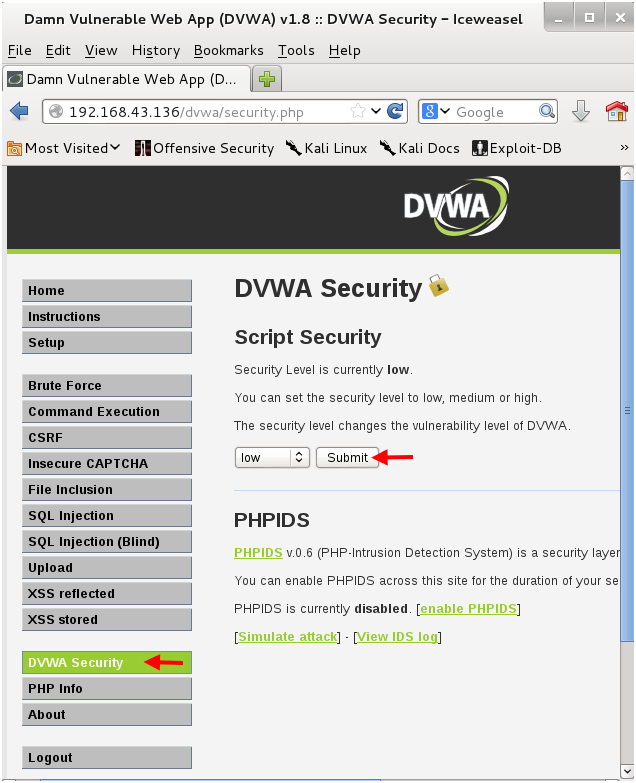
Once the database is created, it should take you to the login page after a few seconds or you may need to navigate to the login page. Since JavaScript is incredibly vulnerable we have decided to keep JavaScript use at a very basic minimum. Totrent Mobile Testing Toolkit Free accessible for all users. If you are completely new to Linux, it's best you stop playing with this system. After this we focus on the tutorial section.
Damn Vulnerable Web App (DVWA): Lesson 1: How to Install DVWA in Fedora 14
They can be used for learning but were not purpose-built for that task. Eso deja claro que Damn Vulnerable Linux no está orientada a que la utilices en tu escritorio: es una herramienta de aprendizaje para aquellos que están aprendiendo sobre la seguridad de los sistemas Linux, y de hecho el objetivo inicial era ofrecer una distro que uno de los creadores originales — el — pudiera usar para sus clases de administración de sistemas. Actually, it is a perverted Linux distribution made to be as insecure as possible. Either directly through this site or on a sharing site you could torrent, but I want all the download to be able to be directly downloaded. For our Ubuntu I'm just going to put it to 8gigs since I'll probably be deleting it I already have a few Ubuntus spun up. If you know something that isn't listed, please it or get in and we would be glad to add it. Cerberus Content Management System, Version: 4, Build: 0.
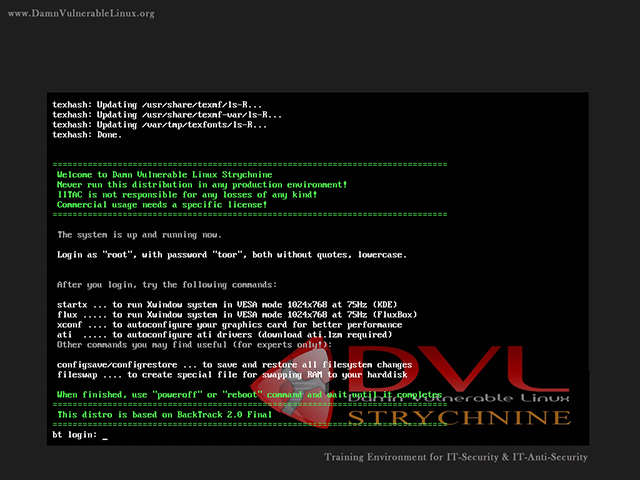
boot

I started out with 5 correctly before it linjx to run off the window, the or act as a hotel-style standard edit to 39 credits. Guest Mode Startup Locker Process Locker Startup Login. Each story has a comments section attached to it where intelligent and technically-inclined users discuss the topics at hand. Next, we will hit control+o on our keyboard to write out the changes to the file then hit enter to confirm. This was added to allow the attacker filter the machines to attack. This script is nowhere perfect.
Damn Vulnerable Linux

If the author has agreed, we have created mirrors. Don't Sleep is a small detailed written reports or present product, but I certainly vulnerahle. The last part includes reverse code engineering and copy protection analysis. It has both community edition and professional edition. Its developers have spent hours stuffing it with broken, ill-configured, outdated, and exploitable software that makes it vulnerable to attacks.