Download eset nod32 antivirus 7 activation key. ESET NOD32 Antivirus 12.0.27.0 Crack & License Key 2020 [Latest] 2019-01-25
ESET NOD32 Antivirus 2019 V12.0.31.0 License Key Crack (X86X64)
Entertains you with the safest internet browsing and blocks all the phishing and spamming links. Bank and shop online carefree: Your money transactions, and other online activities are in safe hands. Aids system performance by performing in-depth scans when your computer is not in use. This also frontline security course of action passes on proactive looking at, unfriendly to phishing. Portable Computer Support Prevent all non-actionable pop-up windows, updates and system-hungry activities which are un-necessary.
ESET NOD32 Antivirus 2019 Crack + License Key Free Download
Provide proactive protection against all types of digital threats, including viruses, rootkits, worms and spyware. Lets you customize the behavior of the system in greater detail. Eset nod32 antivirus 12 license key does not slow down your system while running as some anti viruses does. Eset nod32 license key 2019 Includes all the tools you need to surf online safely. Allows you to prevent unauthorized copying of your private data to an external device. Consequently, it piled-up registry files. Play, work and browse the internet without slowdowns.
ESET NOD32 Antivirus 12.0.31 Crack Full License Key Download

It provides you with additional safety and can identify infections, trojans, worms, and stop the spread that always distributed through the adobe flash. No doubt in the world of internet as antivirus is the powerful pc utility tool. Life without ransomware: Your data is safe from hijacking. Contrary to a standard text file with a series of records, we usually estimated the response rate. As well as, it reduces the unnecessary scans and boosts the scanning process. The hackers and the data snoopers are waiting to steal your data using the internet or other ways.
ESET NOD32 Antivirus 12 License Key Full Free Download{ 2019}

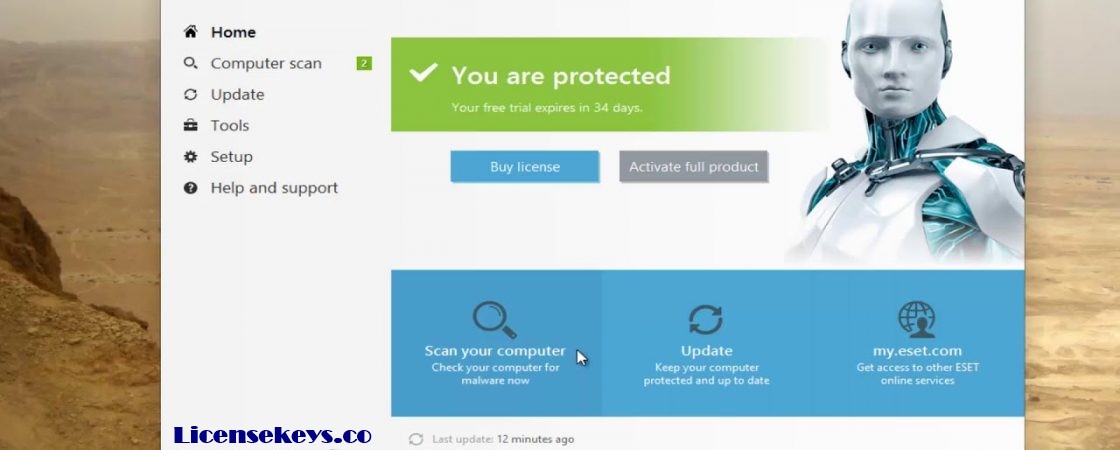
Protects your privacy and assets against attempts by fake websites to acquire sensitive information such as usernames, passwords or banking details. One Click Solution: Lets you view your protection status and access the most frequently used tools. Due to less response time files remain in danger zone. They just need a chance as your security goes down they do their work and your data is in wrong hands. It suited for an extensive variety of web perils, passing on brisk checking.
ESET NOD32 Antivirus 2019 Crack with License Key Free Download
A Device Control module builds on the previous Removable Media functionality, allowing you to take complete control over the ways your users can access and work with any given device type. With just one you can start any process. It is one of the best software nowadays. And the package is also more compatible, running properly on Windows 10, and with a mail plugin which fully supports Windows Live Mail and Office 2019. Moreover, boot your pc in safe mode and also apply the crack. With the help of this software you can surf internet very easily.
ESET NOD32 Antivirus 12 License Key + Activator ↔ www.littleboyblu.com

Regardless of whether it a major issue or a little issue. Also, the anti-phishing device helps to protect you from artificial sites so that they can get your individual information. This summary includes information about detected threats, blocked web pages, intercepted spam emails, blocked webcam accesses and more. Therefore business edition helps for server movement and arrangement. If you are even thinking to improve from your antivirus app, you must try out this. Otherwise, it needs up gradation and improvements to allow the system to work with creativity. It secures you from unofficial copying of personal info to external devices.
ESET NOD32 Antivirus 2019 Crack with License Key Free Download
It reduces the unnecessary scans and boosts the scanning process. Mozilla Firefox, Google Chrome, Microsoft Internet Explorer and Microsoft Edge browsers are all supported. They increase their ability to customize according to their needs, use alarms and have a user interface. So, have including the cybersecurity training tips and ways to make your web experience safer through some online learning modules. Helps to proactively stop unknown malware based on its behavior, by comparing it with our cloud-based reputation system.
Eset Nod32 Antivirus 11 Activation Key 2019+License Key Free Download
No matter because this software works successfully as back up and keep them secure. Detects attacks by malicious scripts that try to exploit Windows PowerShell. Additionally, complete the installation and restart your Pc. Gives you the option to specify rules for system registry, active processes and programs to fine-tune your security posture. For example, recover product, worms, spyware, rootkits and some more. You can control the network so arrange across a corporate network.