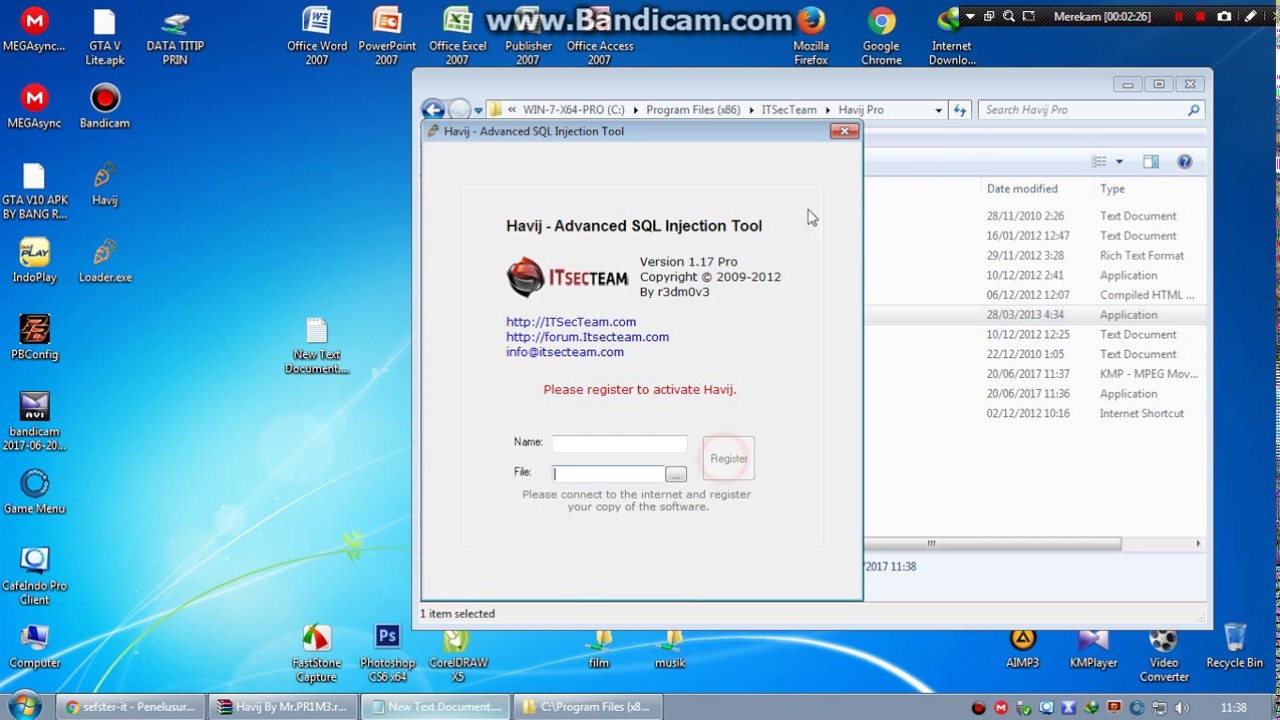
Download havij 1.17 pro cracked. Havij Adv. SQL Injection Tool 1.17 Crack [Latest] 2019-04-19
Havij pro cracked 1.17 SQL injection Full Version Free Download

It can take advantage of a vulnerable web application. By using the advanced version of Havij, you can perform all the functions at the back-end of a vulnerable website. Due to these built-in settings, Havji Pro can be used by anyone. You can google around for it or use the free version offered on the official website. So that you can use it freely : Download Havij Pro 1. Owners can get rid of columns and tables, fetch details in the data source, operate Structured Query Language claims as well as gain access to underlying file feature.
Havij 1.17 pro full crack (100% working)

Havij pro is the software that can deal with this language. So i have uploaded a crack for Havij Pro 1. Havij Crack Full Version Download Havij 1. The power of Havij that makes it different from similar tools is its injection methods. Grab yourself a copy of Havij and set it up.
ITSecTeam Havij PRO 1.17 Crack With Keygen Free Download
It can take advantage of a vulnerable web application. The success rate of attack on vulnerable targets using Havij is above 95%. You can also from here with all features and tools fully free. Nevertheless, Havij remains active and widely used by both penetration testers as well as low-level hackers. The success rate of the application is more than 93%, which makes it different from other tools of the same genre.
UPDATE !! Download Havij 1.17 Pro Cracked REPACK
We are trying to provide you the new way to look and use the blogger templates. Also,give us a link to a download that doesn't need a password! Let's try to look for some clueson the download page to see if we could find the password. It can get the benefit of a vulnerable web application. And even access the underlying file system and execute operating system shell commands. It's stupid that they have a password on the mediafire rar folder! For one, it has a simple to use user interface. The fundamental reason for this particular program is taking benefit of sensitive net apps and defenseless.
Havij 1.17 Pro + Crack
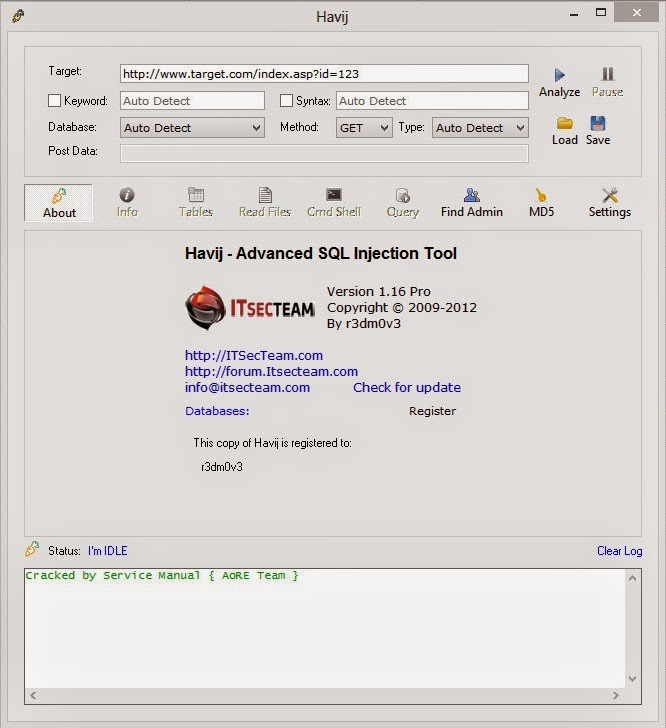
It can take advantage of a vulnerable web application. Owners can get rid of columns and tables, fetch details in the data source, operate Structured Query Language claims as well as gain access to underlying file feature. Havij download latest version has the most user-friendly Graphical User Interface and automatic settings. It can take advantage of a web application. However, some evil minds use this application to hack different websites.
Download Havij 1.17 free full version cracked

The accomplishments price of this software is a lot more compared to 93%, and that tends to make it distinctive from some other resources of similar genre. Additionally it have success rate of attack on vulnerable targets using Havij is above 95%. You will not have to waste your time on setting up the application, rather you can begin the work right after the installation. Verdict Tools like Havij must only be used for the positive and beneficial purposes. The software is available free of cost on their website so just download the software and get working to improve the web research and web positioning of the websites. It can get the benefit of vulnerable web software. The potency of the application that makes it diverse from comparable tools is its injection system.
Download Havij 1.17 Pro Full Version 2017
It can get the benefit of vulnerable web software. We now have a full list of dangerously exploitable data. Havij download can make the most of a vulnerable web program. The basic purpose of this software is to take advantage of defenseless and weak web applications. The distinctive power of Havij that differentiates it from similar tools lies in its unique methods of injection. The distinctive power of Havij that differentiates it from similar tools lies in its unique methods of.
Havij Latest SQL Injection Tool 1.17 Crack Download

Copy the link of the site which you want to test for vulnerability. Now paste on scan bar and click on analyze. As a result of these integrated configurations, Havji Pro could be used by anybody. Most Common Users: Havij is commonly used by low-level hackers and penetration testers, who wish to test the security strength of particular applications being put on the market. Many of you guys are looking for Latest Havij Pro 1.
Havij 1.17 pro full crack (100% working)

The latest version of Havji Pro 1. Illegalcrew welcomes hearing from our readers and members. Customers shall not in any manner reproduce, distribute, modify, decompile, disassemble, decrypt, extract, reverse engineer, lease, assign, or sublicense the said software, unless such restrictions are prohibited by applicable laws or such actions are approved by respective copyright holders under licenses. Our designers are working hard and pushing the boundaries of possibilities to widen the horizon of the regular templates and provide high quality blogger templates to all hardworking bloggers! Moreover it provide login names and password hashes, dump tables and columns. It is still, however, a useful tool that many hackers keep in their arsenal for quick attacks.