Download rockyou wordlist for kali linux. Password dictionary 2019-01-28
Password dictionary
It should not be used for illegal activity. If you have multiple wordlists, you can also combine them into one large file. To do this, it enables the cracking of a specific password in multiple ways, combined with versatility and speed. It takes forever or so it seems. What nicknames does the company have. I have also included Wordlist that come pre-installed with Backtrack and Kali called darkc0de. It is designed to break even the most complex passwords.
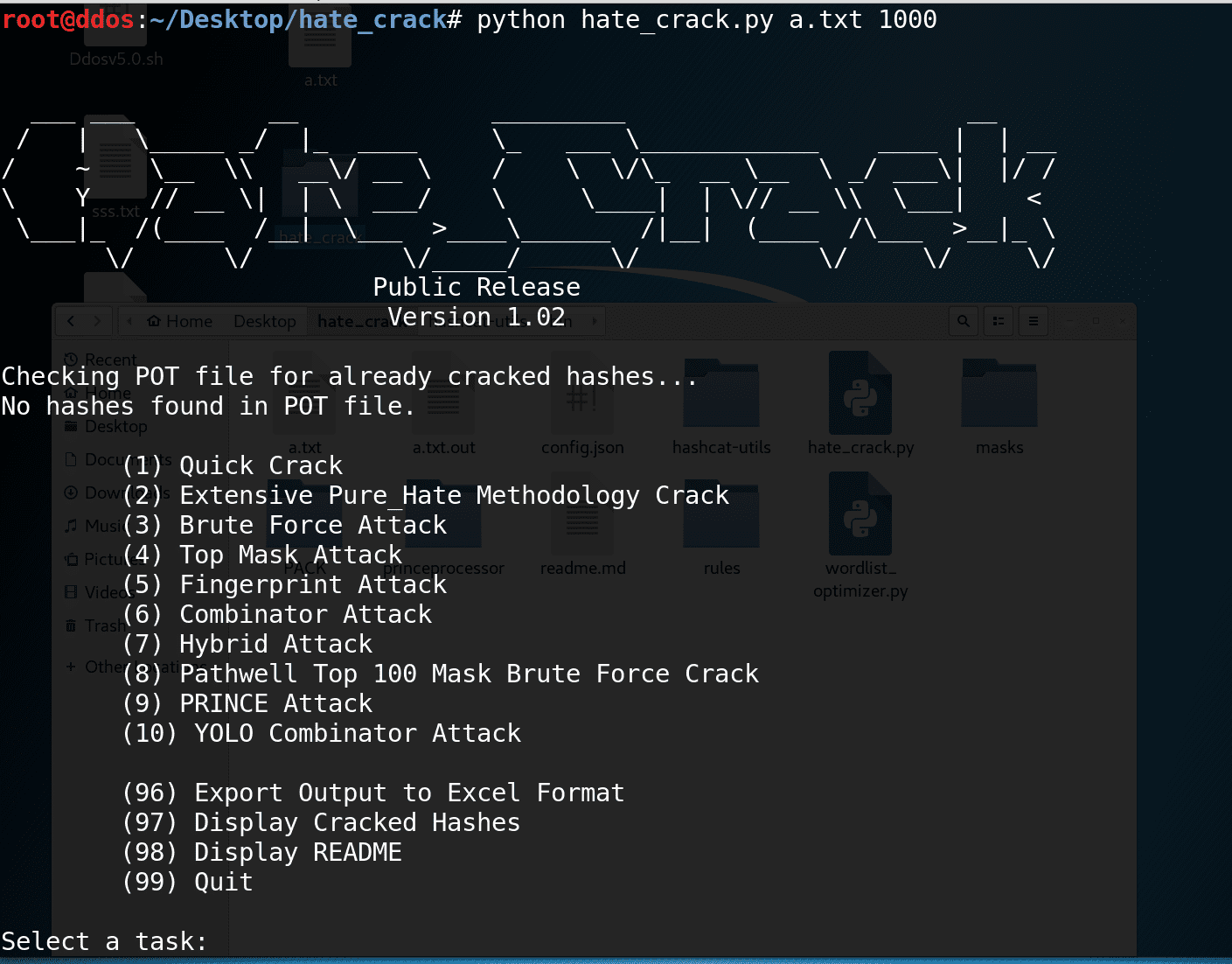
How To Crack WPA/WPA2 Hash Using HashCat

Example: If testing a bank in denver I might use the words: cash mile high broncs broncos elway cashier. I dug them up using advanced Google search operators. Gets through almost every time. How the hell are you guys able to write any commands? They are similar to lookup tables, except that they sacrifice hash cracking speed to make the lookup tables smaller. Hybrid Attack :- It works like a dictionary attack, but adds some numbers and symbols to the words from the dictionary and tries to crack the password. Spoonfeeding is only for babies.
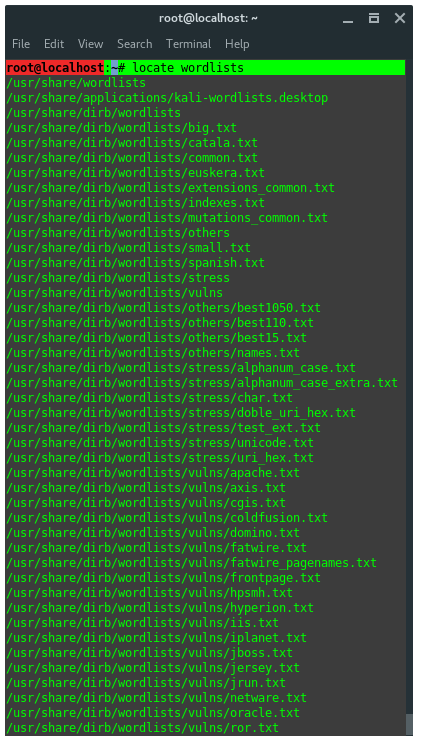
Word List / Dictionaries built into Kali

Finally, Hashcat provides numerous options for password hashes that can be cracked. Approaching final keyspace - workload adjusted. And I partially remember the password. I am executing the command. The can also be extracted in linux using the unrar command.
Word List / Dictionaries built into Kali
Below are some dictionaries that can be used with. I'm still learning linux but I was wondering, is it possible to compile the txt and lst files together and write it out as a txt file? Then learn about partition and partition tables, and how they are related to booting. Hashcat turns readable data into a garbled state this is a random string of fixed length size. Wordlist RockYou : Awesome Wearable Gadgets You Must Have Steps: Enter These Commands In the terminal 1. A wordlist or a password dictionary is a collection of passwords stored in plain text. Long story short, my world lists are in lst and txt formats.
Best Wordlist for brute force attacks? : netsecstudents

A place to share resources, ask questions, and help other students learn Network Security specialties of all kinds. By the way you may also check this post, this Website also has an awsome post on it. You could do a in such cases but even that could take millions of years depending on your computer. Its not like a movie. The majority I found from websites that share leaked passwords. Dictionary and brute-force attacks are the most common ways of guessing passwords. How do I use the Ultimate2016 if there is no.
How To Crack WPA/WPA2 Hash Using HashCat
Hashes do not allow someone to decrypt data with a specific key, as standard encryption protocols allow. This article provides an introductory tutorial for cracking passwords using the Hashcat software package. The author is not responsible for its use or the users action. How do I use this? These techniques make use of a file that contains words, phrases, common passwords, and other strings that are likely to be used as a viable password. Extracting them in Windows, copying them to a flash drive and than into Beini may be the easiest way. These are dictionaries that have been floating around for some time now and are here for you to practice with. Rule-Based Attack :- This attack is used when the attacker gets some information about the password.
Download A Collection of Passwords & Wordlists for Kali Linux (2018)

The weakest Password just became strong and off your list. It can be used on. There is this wonderful web page called Google and I can see you are trying to use it…. Now my question for you is… how would i remove character symbols from the example below? You can create your own wordlist or use existing ones that's been compiled by others. Last updated: Nov 20 2018 Today you'll be able to download a collection of passwords and wordlist dictionaries for cracking in Kali Linux. I am extracted it on my desktop but when i use aircrack-ng -w wordllist.
How to Hack a Wifi Using Kali Linux 2.0
How to Crack Hashes The simplest way to crack a hash is to try first to guess the password. It's basically a text file with a bunch of passwords in it. Youtube Channel : Follow Me On Twitter : Like My Awesome Computer And Hacking Tricks Facebook Page : Thanks. How to Create Wordlist with crunch in Kali Linux. From experience alot of people commenting are right. Dictionary attack :- A dictionary attack uses a targeted technique of successively trying all the words in an exhaustive list called a dictionary from a pre-arranged list of values. Bottom line of what I am trying to say.