Elcomsoft distributed password recovery registration code. Elcomsoft Distributed Password Recovery 2019-04-04
Digital Forensic, Data Decryption and Password Recovery Solutions for Law Enforcement, Forensic and Corporate Customers

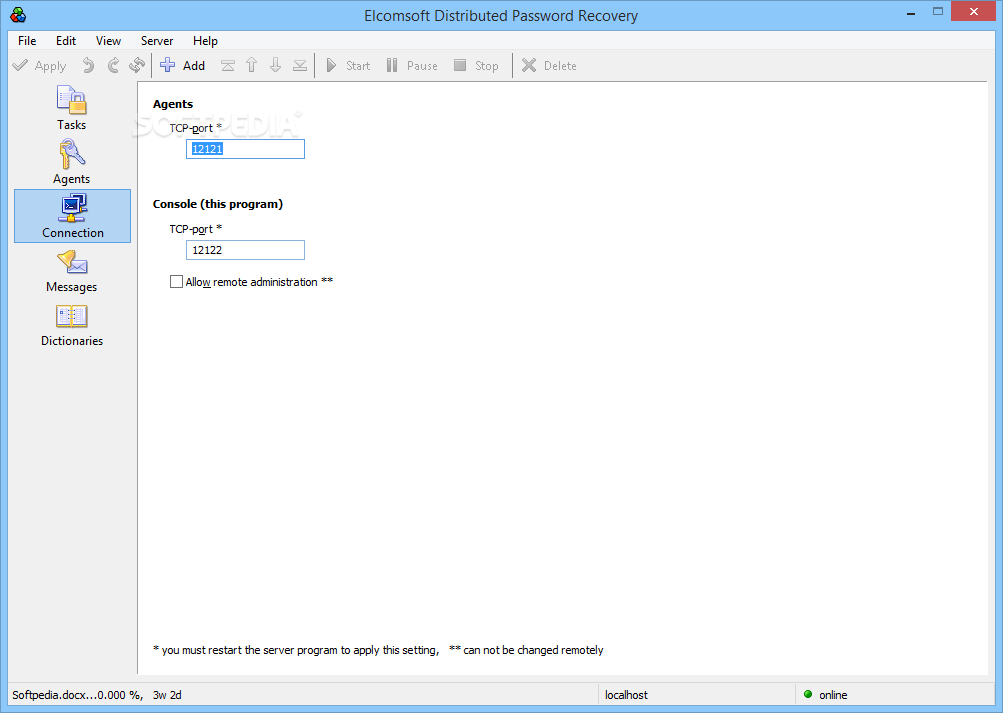
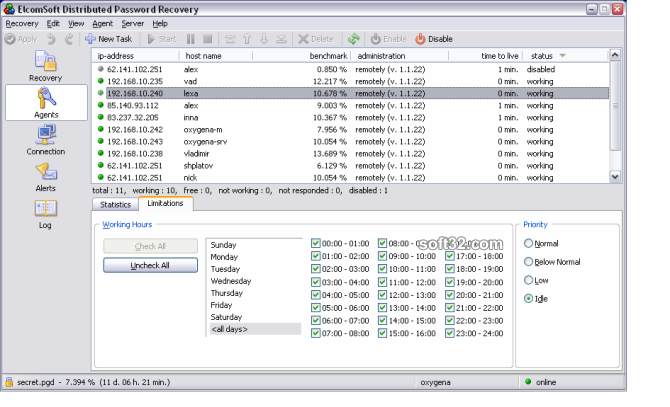
Elcomsoft Distributed Password Recovery manages to put up a strong performance and through an innovative approach it allows anyone to profit from an advanced technology, even if could do with a more refined look and some extra customization features. Based on in-house tests as well as feedback from ElcomSoft valuable customers, these password recovery tools are the fastest on the market, the easiest to use and the least expensive. By only transferring the bare minimum of information over the network, Elcomsoft Distributed Password Recovery allows for massively parallel operation, and scales linearly to as many as 10,000 workstations with no scalability overhead. Various forensic techniques exist allowing experts overcoming BitLocker protection. End users are mostly familiar with one particular feature of the keychain: the ability to store all kinds of passwords.
ElcomSoft Distributed Password Recovery v2.99.481 » Developer Team :: Best choice for developers!
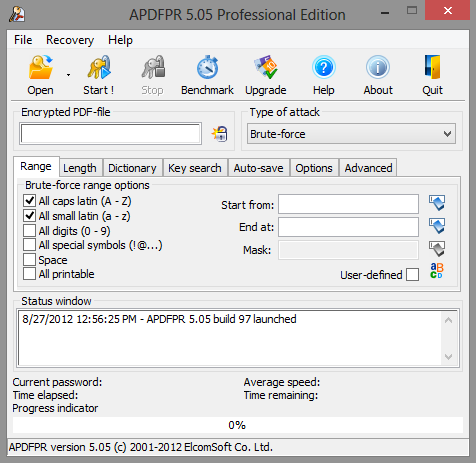
Recover passwords using dictionary and brute force There are, nonetheless, some solutions that can circumvent such constraints and decrease he waiting time dramatically. With hundreds of thousands passwords lost every year, protected information becomes unavailable to the rightful owner. If you have software or keygens to share, feel free to submit it to us here. Considering how consistent the numbers are between multiple researches carried out over the course of four years, we can safely assume that around 60% of consumers reuse their passwords. Also you may contact us if you have software that needs to be removed from our website. Capturing a memory dump of a computer while the encrypted volume is mounted is one of the most frequently used venues of attack. Compared with office documents and archives that are relatively infrequent, every second case involves an encrypted container.
Elcomsoft 1.84 serial torrent trend: CrystalOCR (build 184)
Zero Footprint Operation ElcomSoft offers a forensically sound solution. Combining these methods, experts can collect a greater set of evidence compared to using any single method alone. Some formats are more resistant to brute-force attacks than others. Password Recovery With Crack Advanced Office Password Recovery With Keygen Advanced Office Password Recovery With. Break complex passwords, recover strong encryption keys and unlock documents in a production environment. How to recover your forgotten password or your files? One of the disadvantages of programs designed to restore lost or forgotten passcodes is the rather slow-moving pace at which they work, especially when it comes to complex passwords.
Distributed Password Recovery Serial Number, key, crack, keygen
Expert-level support, concise maintenance and update policies make our products a solid investment. On rare occasions where we must manually verify your order, the license will be available in 48 hours or less. BitLocker protection is extremely robust, becoming a real roadblock for digital forensics. Consistent password recovery tool Elcomsoft Distributed Password Recovery manages to put up a strong performance and through an innovative approach it allows anyone to profit from an advanced technology, even if could do with a more refined look and some extra customization features. . ElcomSoft products help regain control over encrypted data, recover lost and forgotten passwords and access locked-out accounts in popular operating systems, applications and services.
Elcomsoft 1.84 serial torrent trend: CrystalOCR (build 184)
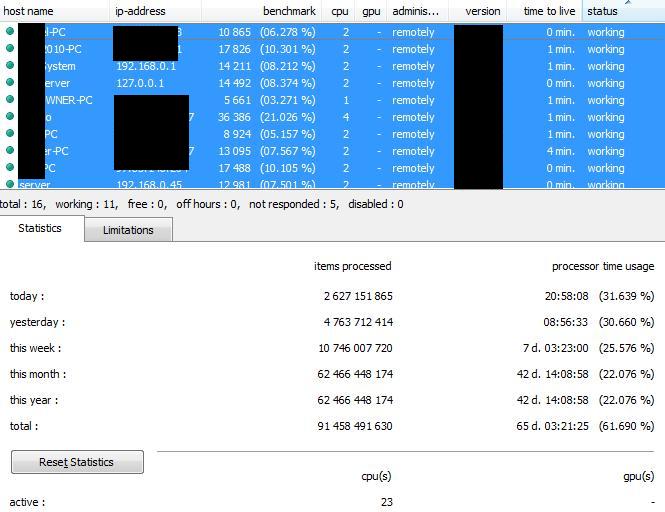
Elcomsoft Distributed Password Recovery v. The latest development revolutionizes the speed of password recovery without requiring expensive hardware. Heterogeneous acceleration allows using multiple video cards of different makes and models, effectively utilizing existing hardware and squeezing the last bit of performance out of every supported component. Elcomsoft Distributed Password Recovery v. Your search for Distributed Password Recovery may return better results if you avoid searching for words like: crack, serial, keygen, activation, code, hack, cracked, etc. The limitations may not be on the software side only, but also because hardware resources are in turn at a smaller scale.
Download Elcomsoft Distributed Password Recovery 4.10 Build 1245
Besides downloading torrent files, this program also lets you watch movies while they are being downloaded and you have the possibility to organize all of your downloaded files into categories. The supported methods for decrypting and getting back the needed data consist of dictionary, mask and length attacks. Manufacturers followed the trend, continuing the performance race. The supported methods for decrypting and getting back the needed data consist of dictionary, mask and length attacks. If the volume is dismounted before hibernation, the encryption keys may not be derived from the hibernation file. ElcomSoft Distributed Password Recovery 2. Date Name Success Rate 2009-10-17 06:22:15 83% 2009-10-22 23:47:41 93% 2012-12-12 10:25:46 0% 2009-10-17 06:22:15 40% 2009-10-17 06:22:15 25% 2009-10-17 06:22:15 13% 2009-10-17 06:22:15 77% 2009-10-22 23:47:41 0% 2009-10-22 23:47:41 0% 2009-10-22 23:47:41 20% 2009-10-22 23:47:41 0% 2009-10-22 23:47:41 0% 2011-09-08 10:48:57 0% 2011-09-08 10:48:57 0% 2011-09-08 10:48:57 0% 2012-12-12 10:25:06 0% 2012-12-12 10:25:34 0% 2009-10-17 06:22:15 25% 2009-10-17 06:22:15 52% 2009-10-22 23:47:41 0% 2009-10-22 23:47:41 84% 2009-10-22 23:47:41 64% 2009-10-22 23:47:41 0% 2009-10-22 23:47:41 74% 2009-10-22 23:47:41 40% 2011-09-08 10:48:57 0% 2011-09-08 10:48:57 0% 2011-09-08 10:48:57 56% 2011-09-08 10:48:57 0% 2011-09-08 10:48:57 22% 2011-09-08 10:48:57 0% 2012-12-12 10:24:49 47% 2012-12-12 10:25:24 53% 2012-12-12 10:25:28 70% 2012-12-12 10:25:59 53% 2009-10-17 06:22:15 16% 2009-10-17 06:22:15 11% 2009-10-17 06:22:15 70% 2009-10-17 06:22:15 20% 2009-10-17 06:22:15 26% 2009-10-22 23:47:41 57% 2009-10-22 23:47:41 0% 2009-10-22 23:47:41 0% 2011-09-08 10:48:57 0% 2011-09-08 10:48:57 40% 2012-12-12 10:24:57 60% 2012-12-12 10:25:20 69% 2009-10-17 06:22:15 42% 2009-10-22 23:47:41 0% 2009-10-22 23:47:41 0% 2009-10-22 23:47:41 0% 2009-10-17 06:22:15 17% 2009-10-17 06:22:15 16% 2009-10-17 06:22:15 41% 2009-10-22 23:47:41 40% 2012-12-12 10:25:02 61% 2009-10-17 06:22:15 62% 2009-10-22 23:47:41 77% 2012-12-12 10:25:48 36% 2012-12-12 10:25:54 0% 2011-09-08 10:48:57 0% 2012-12-12 10:25:50 58% 2009-10-17 06:22:15 23% 2009-10-22 23:47:41 53% 2012-12-12 10:25:14 20% 2012-12-13 00:42:43 75% 2011-09-08 12:54:48 79% 2012-12-13 13:08:27 56% 2012-12-13 00:42:46 63% 2012-12-13 00:42:49 71% 2011-09-08 12:54:48 0% 2011-09-08 12:54:48 0% 2011-09-08 12:54:50 0% 2011-09-08 12:54:50 0% 2009-10-17 06:18:48 20% 2009-10-17 06:18:48 39% 2009-10-22 23:27:16 0% 2009-10-22 23:27:20 0% 2009-10-22 23:48:52 42% 2009-10-22 23:49:20 82% 2009-10-22 23:49:20 0% 2009-10-22 23:49:20 18% 2009-10-22 23:49:20 56% 2009-10-22 23:49:21 0% 2009-10-22 23:49:41 59% 2009-10-22 23:50:57 81% 2011-09-08 12:28:40 60% 2011-09-08 12:28:40 0% 2011-09-08 12:28:40 0% 2011-09-08 12:28:40 0% 2011-09-08 12:28:40 56% 2011-09-08 12:28:40 30% 2011-09-08 12:28:40 0% 2011-09-08 12:28:40 0% 2011-09-08 12:28:40 0% 2011-09-08 12:28:40 0% 2011-09-08 12:28:40 0% 2011-09-08 12:28:40 0% 2011-09-08 12:28:40 0% 2011-09-08 12:28:40 0% 2011-09-08 12:28:40 0% 2011-09-08 12:28:40 0% 2011-09-08 12:28:40 0% 2011-09-08 12:28:40 14% 2011-09-08 12:28:40 0% 2011-09-08 12:28:42 0% 2011-09-08 12:28:42 0% 2011-09-08 12:28:42 0% 2011-09-08 12:28:42 40% 2011-09-08 12:28:42 0% 2011-09-08 12:29:28 0% 2011-09-08 12:29:28 0% 2011-09-08 12:36:51 65% 2011-09-08 12:40:30 95% 2012-12-12 01:48:59 0% 2011-09-08 12:54:48 0% 2011-09-08 12:54:48 0% 2011-09-08 12:54:50 55% 2009-10-17 06:18:14 53% 2009-10-17 06:18:22 57% 2009-10-17 06:18:26 24% 2009-10-17 06:18:26 76% 2009-10-17 06:18:26 39% 2009-10-17 06:18:27 80% 2009-10-17 06:18:27 52% 2009-10-17 06:22:11 41% 2009-10-17 06:22:11 52% 2009-10-17 06:23:06 39% 2009-10-17 06:23:06 14% 2009-10-17 06:26:28 61% 2009-10-17 06:28:08 0% 2009-10-17 06:28:08 42% 2009-10-17 06:28:08 40% 2009-10-17 06:28:08 0% 2009-10-17 06:28:08 100% 2009-10-17 06:36:26 74% 2009-10-22 23:27:10 55% 2009-10-22 23:27:13 100% 2009-10-22 23:27:13 0% 2009-10-22 23:27:14 0% 2009-10-22 23:27:14 0% 2009-10-22 23:27:14 100% 2009-10-22 23:27:14 0% 2009-10-22 23:27:14 0% 2009-10-22 23:27:14 0% 2009-10-22 23:27:14 0% 2009-10-22 23:27:14 0% 2009-10-22 23:27:14 0% 2009-10-22 23:27:14 0% 2009-10-22 23:27:14 100% 2009-10-22 23:27:14 0% 2009-10-22 23:27:14 0% 2009-10-22 23:27:14 0% 2009-10-22 23:27:14 0% 2009-10-22 23:27:14 0% 2009-10-22 23:27:14 0% 2009-10-22 23:27:14 59% 2009-10-22 23:27:14 20% 2009-10-22 23:27:14 20% 2009-10-22 23:27:14 62% 2009-10-22 23:27:14 0% 2009-10-22 23:27:15 0% 2009-10-22 23:27:15 0% 2009-10-22 23:27:15 0% 2009-10-22 23:27:15 53% 2009-10-22 23:27:15 0% 2009-10-22 23:27:15 69% 2009-10-22 23:27:15 0% 2009-10-22 23:27:15 65% 2009-10-22 23:27:15 66% 2009-10-22 23:27:15 0% 2009-10-22 23:27:15 0% 2009-10-22 23:27:15 63% 2009-10-22 23:27:15 0% 2009-10-22 23:27:15 0% 2009-10-22 23:27:15 0% 2009-10-22 23:27:15 0% 2009-10-22 23:27:15 100% 2009-10-22 23:47:40 0% 2009-10-22 23:47:40 0% 2009-10-22 23:47:51 90% 2009-10-22 23:47:54 0% 2009-10-22 23:48:00 68% 2009-10-22 23:48:01 82% 2009-10-22 23:48:17 0% 2009-10-22 23:48:17 0% 2009-10-22 23:48:17 0% 2009-10-22 23:48:17 0% 2009-10-22 23:48:37 0% 2009-10-22 23:48:37 0% 2009-10-22 23:48:52 0% 2009-10-22 23:48:52 0% 2009-10-22 23:48:52 0% 2009-10-22 23:48:52 62% 2009-10-22 23:48:52 0% 2009-10-22 23:48:52 0% 2009-10-22 23:48:52 0% 2009-10-22 23:48:52 94% 2009-10-22 23:49:19 68% 2009-10-22 23:49:19 0%.
Elcomsoft Distributed Password Recovery 2.99 Build 445 + Key : 41.99 MB
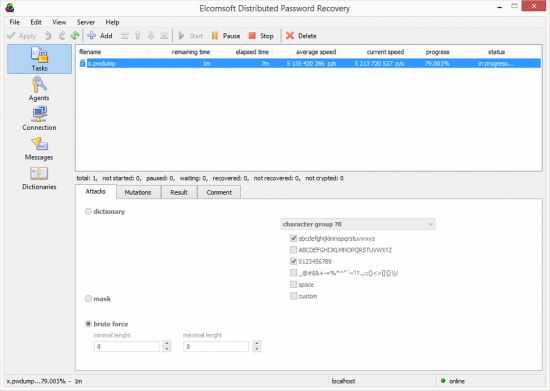
The need for this arises more and more every day, as applications are increasingly used to keep data safe. Broad Compatibility Recover passwords to a variety of office documents, archives, encrypting file systems, Windows and email accounts, and remove many more types of password protection. The same passwords are very likely to be chosen to protect access to offline resources such as encrypted archives and documents. If you still have trouble finding Distributed Password Recovery after simplifying your search term then we recommend using the alternative full download sites linked above. ElcomSoft Distributed Password Recovery is a complex program that lets you recover data hidden behind a password in the easiest way possible.
ElcomSoft Distributed Password Recovery
All trademarks, registered trademarks, product names and company names or logos mentioned herein are the property of their respective owners. While the tool can reset Microsoft Account passwords to allow instant logins to otherwise locked accounts, this is not the point. The point is that we have finally laid our hands on something that can help us break into a major online authentication service, the Microsoft Account. Learn how rootless jailbreaks are different to classic jailbreaks, why they are better for forensic extractions and what traces they leave behind. With cutting-edge hardware acceleration technologies, our tools are the fastest on the market when using consumer-grade gaming video cards for accelerating the recovery. Information read from mounted disks and volumes is decrypted on-the-fly in real time. WikiExt monitors and provides timely updates for its database in order to have up-to-date information and the latest programs for opening any file types at all times.
Elcomsoft 1.84 serial torrent trend: CrystalOCR (build 184)

But it was about as fast as the new Macbook. Our unique technologies and deep knowledge in information security implemented in our products allow investigators recovering the most complex passwords faster or even instantly. The program provides audio-visual online broadcast, without the need for maintenance of the park servers and expenditures for payment of the network traffic. Get Forensic Access to Protected Data ElcomSoft offers a comprehensive range of tools for unlocking access to many types of data, recovering passwords and decrypting encrypted files and volumes. A passcode or system password from any trusted device can be used to decrypt iCloud Keychain and access Health data and iCloud Messages.
Elcomsoft Distributed Password Recovery + Crack Keygen Serial Download

Why Download ElcomSoft Distributed Password Recovery using YepDownload? Brute-force attacks are inefficient for modern formats e. Charlie, May 14, 2016 awesome! Electronic licenses are generally available instantly after the credit card charge is approved. Elcomsoft Distributed Password Recovery 3. What does it mean for us? You can also subscribe to our. Credit card orders are processed immediately. Tags: , , , Posted in , , , Comments Off on How to Break 30 Per Cent of Passwords in Seconds Not all passwords provide equal protection. Please bear with us for up-to-date information and detailed technical discussion.