Elcomsoft ios forensic toolkit. ElcomSoft iOS Forensic Toolkit 5.0 Crack Here [2019] 2019-04-10
Elcomsoft iOS Forensic Toolkit

Legacy devices do not require a jailbreak to be physically acquired. Access to most information is provided instantly. While logical acquisition returns less information than physical, experts are recommended to create a logical backup of the device before attempting more invasive acquisition techniques. Please note that some models require jailbreaking. In the worst case, a passcode may contain all printable characters, and may have any length.
[ASP] Elcomsoft iOS Forensic Toolkit cracked version download
Thanks for your efficient service and clear communication throughout. With physical acquisition, is it possible to recover the data that have been deleted from the device such as photos? Is it possible to perform data carving through unallocated space, or restore deleted files? The original passcode will be instantly recovered and displayed. It is the password of the user 'root'. I've got a problem when my problem goes to sleep during Toolkit operation. Real-Time Access to Encrypted Information Unlike previously employed methods relying on lengthy dictionary attacks or brute force password recovery, the new toolkit can extract most encryption keys out of the physical device. With encryption keys handily available, access to most information is provided in real-time.
ElcomSoft iOS Forensic Toolkit 5.0 Crack + Serial Key 2019

Of course, if you know the existing password, there is no need to change it. If a jailbreak can be installed, experts can image the file system of 64-bit iPhones and iPads, extract protected application data and working databases. In many cases, physical acquisition returns more data than logical acquisition, as many files are locked by the operating system and not accessible during the process of logical acquisition. Passcodes of the second type also only contain digits, but are not limited to 4 digits. The extraction requires an unlocked device or a non-expired lockdown record.
ElcomSoft iOS Forensic Toolkit v5.0 Crack [Latest] ~ APKGOD

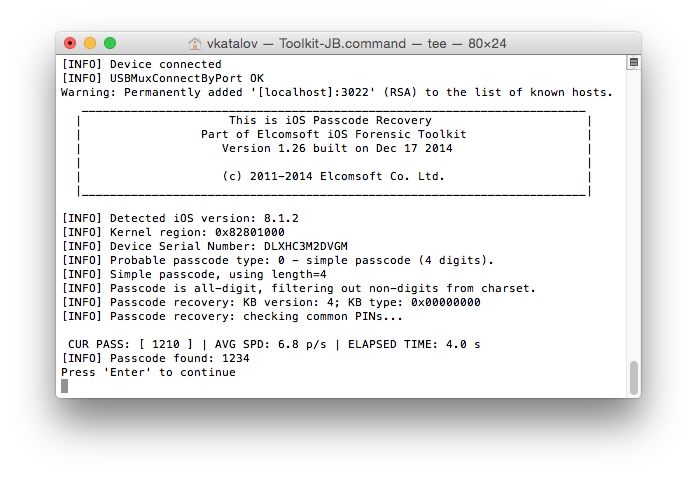
The Manual mode also allows cracking complex passcodes that are longer than 4 characters or contain alphanumerical characters using brute-force and dictionary attacks. The device will never be locked. Instead, the Toolkit makes use of a rootless jailbreak with significantly smaller footprint compared to traditional jailbreaks. However, we would recommend you to use a special third-party tool such as. The extraction requires an unlocking. The only way around this problem is using physical acquisition.
Elcomsoft iOS Forensic Toolkit FAQ, part 1

Access to most information is provided instantly. Read the original jailbreak documentation before installing the code. Image device file system, extract device secrets passwords, encryption keys and protected data and decrypt the file system image. This would be compatible with 64bit and 32bit windows. Much more information is available with physical acquisition compared to backup analysis, creating a bit-precise image of the device in real time.
Elcomsoft iOS Forensic Toolkit 4.10

Please make sure you understand the procedure and follow it carefully. In this mode, you get a text-based menu listing the operations you can perform. A typical acquisition of an iPhone device takes from 20 to 40 minutes depending on model and memory size ; more time is required to process 64-Gb versions of Apple iPad. What is the difference between Guided and Manual modes? Also, logical acquisition comes handy if you don't have access to third-party forensic tools that work with disk images. In brief, what is the typical usage of the Toolkit, and where should I start from? Hold down the Home catch base focus and rest catch regularly the upper right corner in the meantime for 10 seconds.
How To Crack iOS Passwords : Step

Sorry, they are not supported. A typical acquisition of an iPhone device takes from 20 to 40 minutes depending on model and memory size ; more time is required to process 64-Gb versions of Apple iPad. The process is divided into steps that include physical acquisition, logical acquisition, media and archives. The software is useful for quickly extracting multimedia files, such as the camera roll, books, voice recordings and the iTunes multimedia library. The same passcode on iPhone 5 will take about 10 minutes. How easy is it to break the passcode? All information will be accessible. While you can still extract raw data, decrypting the data will not be possible, so anything obtained from the device will be completely useless for an investigation.
ElcomSoft iOS Forensic Toolkit 5.0 Crack + Serial Key Full Download 2019

For the time being as Apple has at long last begun to truly secure the working framework. What about iPad 4, iPad Mini and iPod Touch 5th gen? Physical acquisition for 64-bit devices is fully compatible with jailbroken iPhones and iPads equipped with 64-bit SoC, returning the complete file system of the device as opposed to bit-precise image extracted with the 32-bit process. If a BlackBerry device is locked with an unknown password, it is not possible to perform a physical acquisition at all. Is the Mac version better than the Windows one? Image device file system, extract device secrets passwords, encryption keys and protected data and decrypt the file system image. If the device is configured to produce password-protected backups, experts must use to recover the password and remove encryption.
Enhanced Forensic Access to iPhone/iPad/iPod Devices running Apple iOS
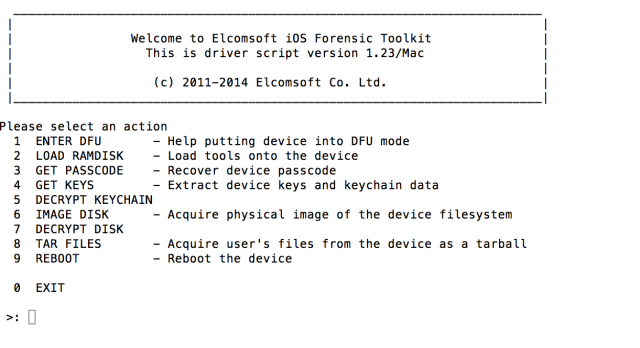
Are there any limitations supporting these last-generation devices? The original passcode will be instantly recovered and displayed. You can still image system and user partitions, and decrypt the user partition. In a ballpark, physical acquisition may take from 15 minutes to about an hour. So we can perform physical acquisition if a device is already jailbroken or if you can install the jailbreak yourself. This would be compatible with compatible version of windows. If a lockdown record is used, some files may not be accessible unless the lock screen passcode is removed.