Encryption password with salt. Storing passwords in a secure way in a SQL Server database 2019-05-13
What is a Salt and How Does It Make Password Hashing More Secure?

Let's alter our table and the stored procedure to use a salt in the password encryption. What's the difference between the two methods? This page will explain why it's done the way it is. I have a question about storing encrypted passwords in your database to help secure them. You should calculate the iteration count based on your computational resources and the expected maximum authentication request rate. User account databases are hacked frequently, so you absolutely must do something to protect your users' passwords if your website is ever breached. Perform 20,000 iterations or more.
Storing passwords in a secure way in a SQL Server database
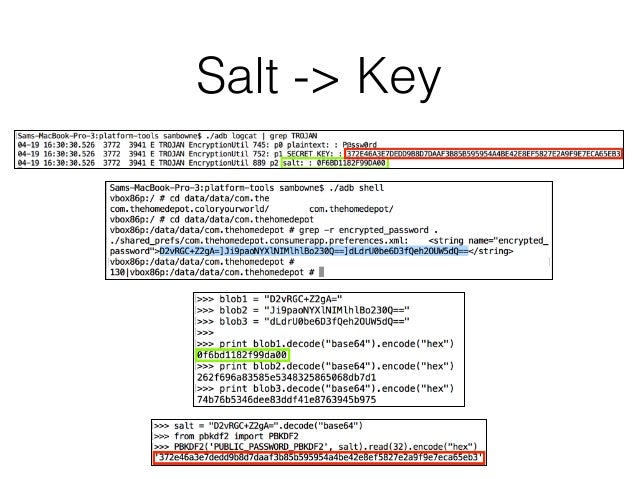
So for maximum compatibility, your app should detect whether or not the browser supports JavaScript and emulate the client-side hash on the server if it doesn't. From the database side of things, the random-ish salts do provide the added layer of defense that makes hash comparisons more difficult. If you are reading this guide, I am going to assume that you are not a security expert and looking for ways to create a more secure system. Store the iteration count, the salt and the final hash in your password database. The salt should also be secret and calculated.
SaltStack: Keeping Salt Pillar data encrypted using GPG

The only way to decrypt a hash is to know the input data. If the browser produces the same hash value then it knows that both the signature and the file are authentic—they have not been altered. Salts are in place to prevent someone from cracking passwords at large and can be stored in cleartext in our database next to the hashes. In particular, letting users reset their passwords can be risky; it's preferable to do so via email by sending users a link to click. A longer salt effectively increases the computational complexity of attacking passwords which in turn increases the candidate set exponentially. You may use the following links to jump to the different sections of this page. LinkedIn subsequently proceeded to invalidate passwords for all accounts created prior to 2012.
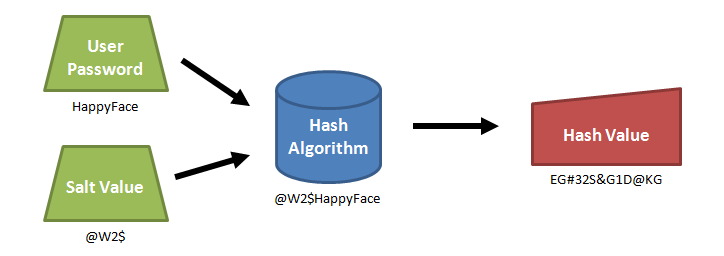
Decrypt password using machine key and password salt

Consequently, the unique hash produced by adding the salt can protect us against different attack vectors, such as rainbow table attacks, while slowing down dictionary and brute-force attacks. If the hash verification fails, the user is prevented from logging into the website. Should we just stick to enforcing a password change with a fixed frequency instead? As a rule of thumb, make your salt is at least as long as the hash function's output. Hashed passwords are not unique to themselves due to the deterministic nature of hash function: when given the same input, the same output is always produced. It's too easy to screw up. If found, one will have to remove the salt from the password before it can be used.
Password Encryption, Hashing, Salting Explained
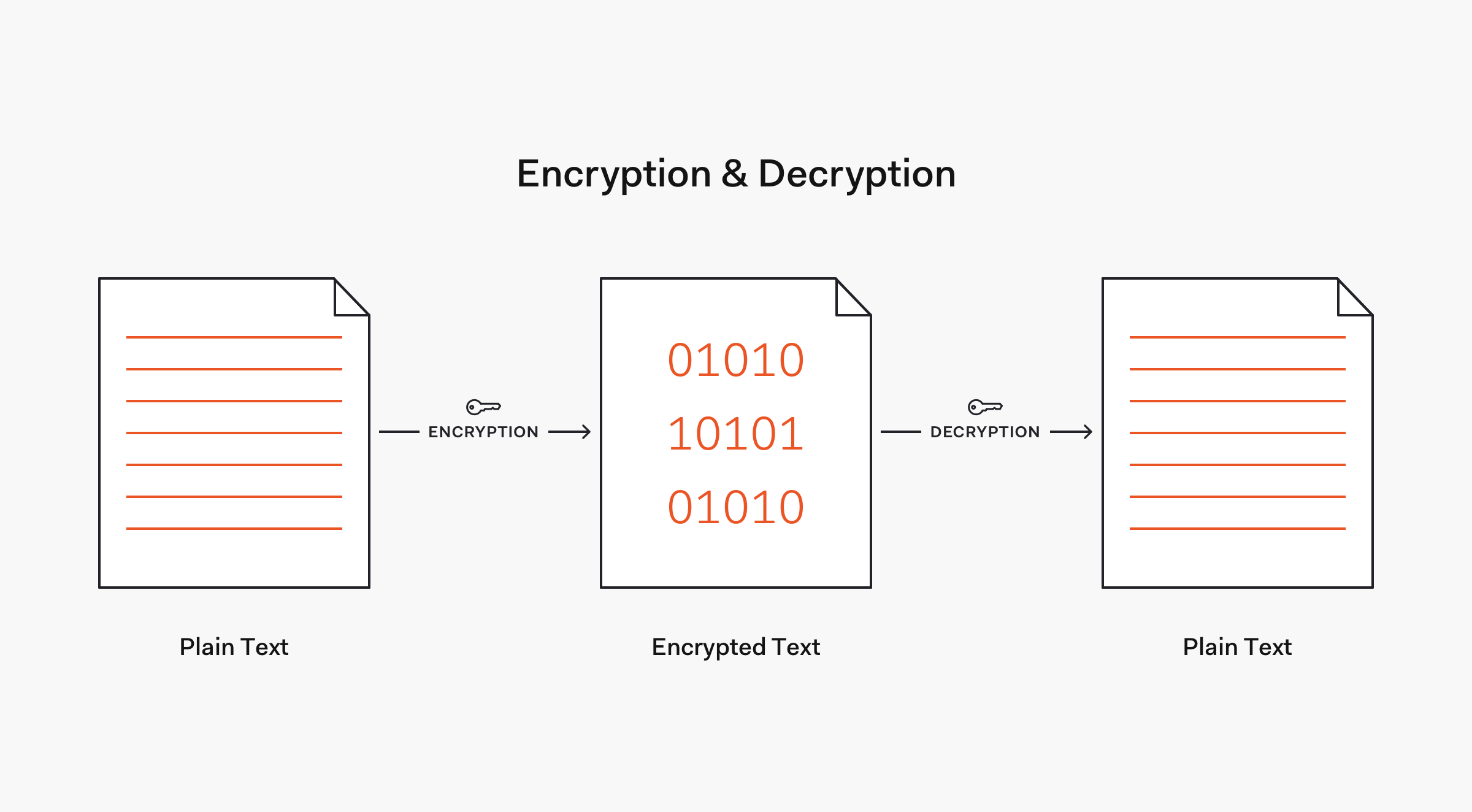
It is likely, even with salted slow hashes, that an attacker will be able to crack some of the weak passwords very quickly. Encryption was entirely contingent upon a private key, which had to be physically exchanged in order for decryption to take place. Note that if you are using to verify a password, you will need to take care to prevent timing attacks by using a constant time string comparison. Whereas encryption is a two-way function, hashing is a one-way function. If you want a better idea of how fast lookup tables can be, try cracking the following sha256 hashes with CrackStation's. They should be an unpredictable random binary blob used only to identify a record in a database table. So store the hashed password including the individual salt and the number of iterations which allows you to increase the number of iterations later if you need to in the database.
Salt Hash passwords using NodeJS crypto

It is easy to think that all you have to do is run the password through a cryptographic hash function and your users' passwords will be secure. An attacker won't know in advance what the salt will be, so they can't pre-compute a lookup table or rainbow table. If I get time I will work up a solution to show you. Everyone has analyzed them to death. The hash value would be made up from both of these together rockyi.
The difference between Encryption, Hashing and Salting
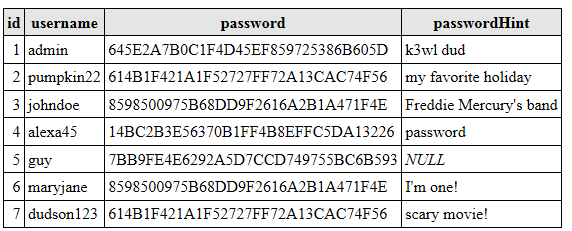
Currently, there exists many varied ways to crack password hashes — namely, dictionary attacks, brute force attacks, lookup tables, reverse lookup tables, and rainbow tables. All an attacker can do to grab the password is run some sort of dictionary attack and hope. Please note that keyed hashes do not remove the need for salt. This page will explain why it's done the way it is. SetAuthCookie username, false ; If you use FormsAuthentication. A great resource for learning about web application vulnerabilities is.
PHP: Password Hashing
Have you ever experienced the Password Recovery Control sending a blank for the password in the email? It's clearly best to use a standard and well-tested algorithm. Create a new class that derives from MembershipProvider. My guess is that the implementation would stand up against an audit still today. In this case, they pick up passwords from a known dictionary of common passwords or generate them iteratively up to a given size and alphabet , hash the passwords, and make an attempt against your membership system. Note that setting a minimal number of unsuccessful attempts might help stop or slow these attacks -- but not if hackers exploiting other holes in your system can gain direct access to your database and possibly copy it.
The difference between Encryption, Hashing and Salting
Natively, the notions of salt and cost are applicable. Additionally, are mitigated to a degree as an attacker cannot practically. Don't re-use the one that was used to hash their old password. Always use a state of the art password hashing algorithm. While it is certainly possible to pass these plaintext credentials directly in the state, this is not best practice. A popular hacking technique known as lookup tables entails the use of ad hoc tables of pre-computed hashes for known passwords. It implies the need to parse and concatenate strings.