Enterprise key management policy. Enterprise key management plan and policy 2019-02-21
Enterprise Key Management: Create both an enterprise key management plan and policy for a company.

And if a key is lost, the data it protects becomes impossible to retrieve. This policy applies to any institutions that implement encryption technology in compliance with controls of various industry and the government regulations. This email address is already registered. Next, identify data at rest, data in use, and data in motion as it could apply to your company. Encryption concepts and policy impacts From a business perspective, encryption can be summed up with the following sentence — Encryption locks data, only people with the correct key can unlock it.
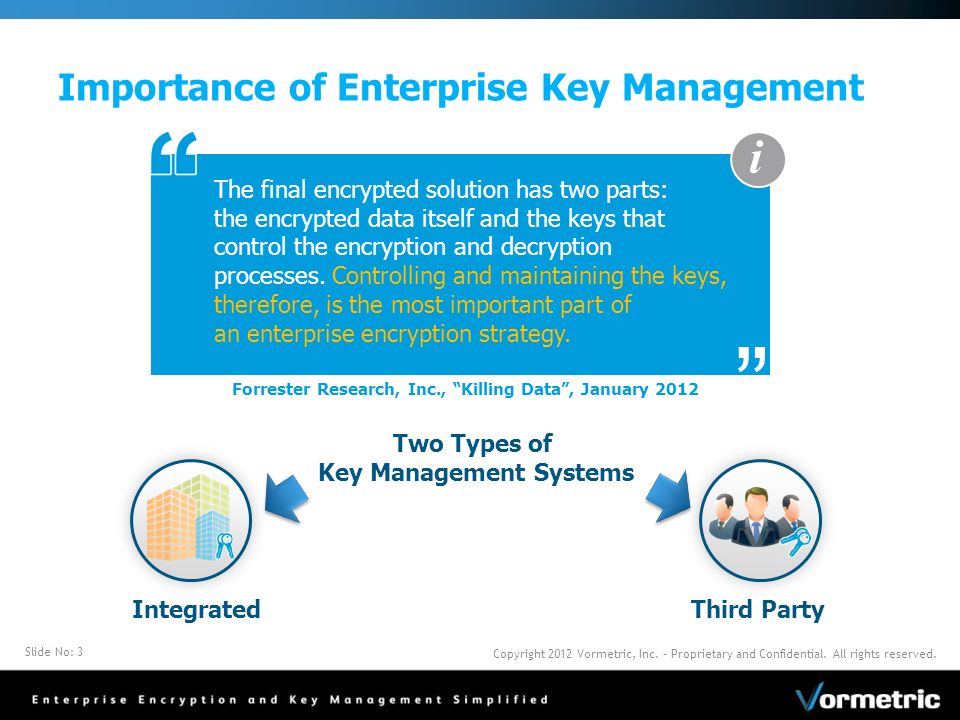
Enterprise Encryption Key Management
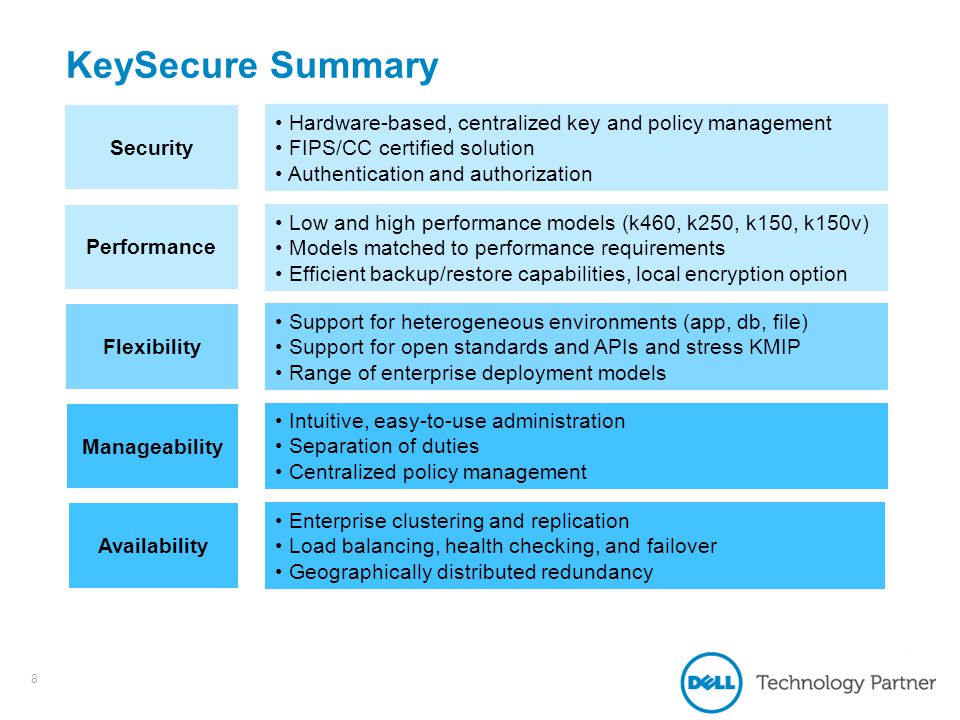
Unless the creation, secure storage, handling and deletion of encryption keys is carefully monitored, unauthorised parties can gain access to them and render them worthless. The spoke component can easily be deployed onto different nodes and can be integrated with any encryption application. Required Performance: Meets Performance Requirements 7. In addition, it is important to make strategic plans for how to deal with encrypted data in case of merger, acquisition or divestment, not least because organisations are likely to employ a range of technologies, which can make merging corporate information tricky. Address these as separate sections in the plan. Another is that employees must receive initial and annual security training.
Enterprise Key Management: Create both an enterprise key management plan and policy for a company.
If they select the wrong option, fail to protect their key, or do not encrypt sensitive data, all of the organizations efforts on data protection can be wasted. Next, propose solutions that the companies could have used to address these gaps. This eliminates scope for abuse on the part of that person, who should be the one who ensures there is no abuse of keys by approved holders. You will use and submit this information in your implementation plan. With the correct key Description: This key works with the cipher to descramble the data. Before you submit your assignment, review the competencies below, which your instructor will use to evaluate your work. Required Performance: Meets Performance Requirements 7.
Encryption key management is vital to securing enterprise data storage
These responsibilities have to officially documented and periodic review to ensure clarity in everyone roles. First, conduct independent research to identify the gaps in key management that are in existing corporations. Required Performance: Meets Performance Requirements 2. Use this information in your implementation plan. The length of this policy should be two to three pages double-spaced. The new web-based system needs to be running in a month.
Enterprise Key Management: Create both an enterprise key management plan and policy for a company.
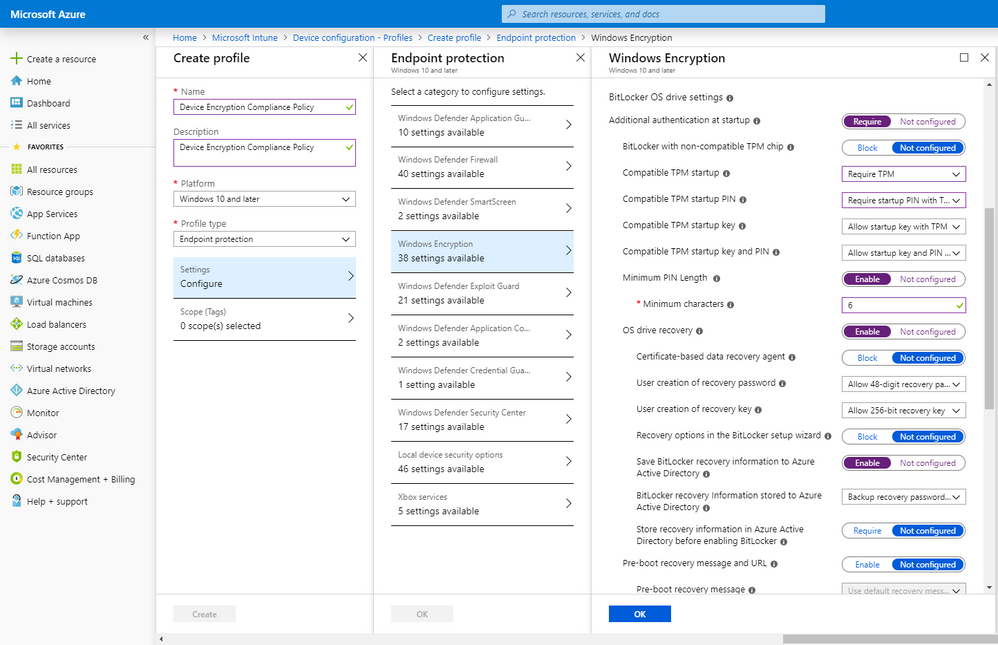
Data Description: The information the organization is protecting. But this has changed as compliance issues such as the and high-profile data loss incidents have become prominent news. Required Performance: Meets Performance Requirements 1. Using the learning and materials produced in those steps, develop your enterprise key management plan for implementation, operation, and maintenance of the new system. This email address is already registered. Although considered generally secure, the downside is that there is only one key, which has to be shared with others to perform its function. Although the first the version of the policy may not be perfect, it still enables the organization to prepare for the usage of encryption.
Enterprise key management plan and policy

Step 2: Identify Key Management Gaps, Risks, Solutions, and ChallengesIn the previous step, you identified the key components of an enterprise key management system. Part 2 provides guidance on policy and security planning requirements for U. Given the magnitude of sensitivity, all data must be backed up on a daily basis. Include a reference list with the report. If the corporation does not develop this new skilled community, what are other means for obtaining results of cryptanalysis? Assessment Method: Score on Criteria - 1. The following overview describes eight best practices in encryption key management and data security. Before you submit your assignment, review the competencies below, which your instructor will use to evaluate your work.
SOLUTION: enterprise key management plan and policy for a company, writing homework help

Assessment Method: Score on Criteria - 7. Finally, review these resources on insecure handling, and identify areas where insecure handling may be a concern for your organization. The page count does not include figures or tables. Furthermore, they must be archived under time-based management so that they are available to retrieve historic data. As a security architect, you know that key management is often considered the most difficult part of designing a cryptosystem. Next, if encryption is being used, verify it meets the standards set within the organizational policy. Its research is produced independently by its research organization without input or influence from any third party.
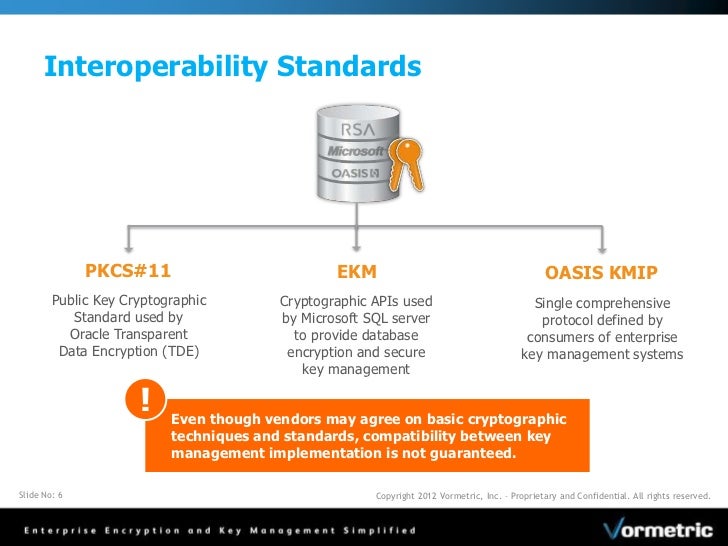
Encryption key management is vital to securing enterprise data storage
Step 3: Identify Key Management Gaps, Risks, Solutions, and Challenges In the previous step, you identified the key components of an enterprise key management system. Asymmetric encryption comprises two elements: a public key to encrypt data and a private key to decrypt data. Submit your plan to the Assignment folder. You can use the list below to self-check your work before submission. You can use the list below to self-check your work before submission. In this step, you will conduct independent research on key management issues in existing corporations. Your access and use of this publication are governed by.
Enterprise Encryption Key Management
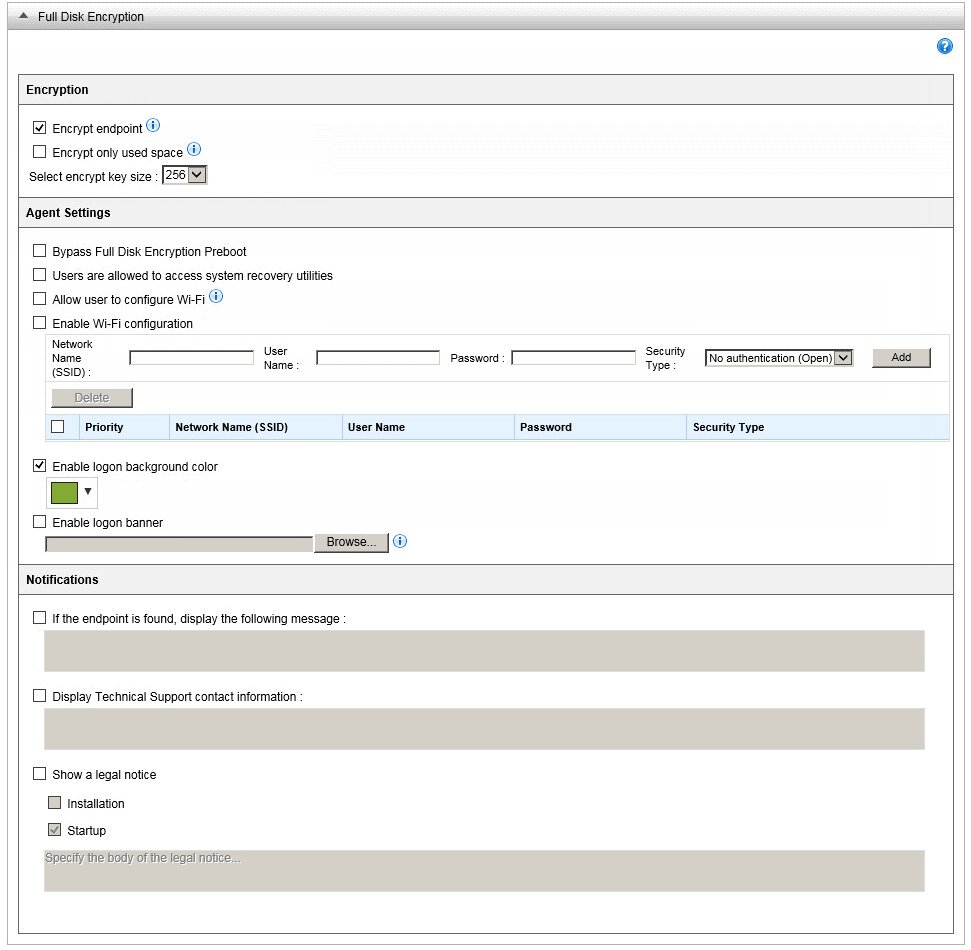
Next, identify data at rest, data in use, and data in motion as it could apply to your company. A good practice would be to use each competency as a self-check to confirm you have incorporated all of them in your work. The attacker then simply downloads this data and can read this without even a password. Using the guidance previously discussed, create a baseline enterprise encryption policy that sets the technical standards, operating procedures and monitoring activities required to implement encryption organization wide. Then, provide a high-level, top-layer network view diagram of the systems in Superior Health Care.
Enterprise Key Management: Create both an enterprise key management plan and policy for a company.

Describe the cryptographic system, its effectiveness and efficiencies. Cryptanalysts are a very technical and specialized workforce. Likewise, in the case of smartphone keyless access platforms, they keep all identifying door information off mobile phones and servers and encrypt all data, where just like low-tech keys, users give codes only to those they trust. Keywords assurances; authentication; authorization; availability; backup; compromise; confidentiality; cryptanalysis; cryptographic key; cryptographic module; digital signature; hash function; key agreement; key management; key management policy; key recovery; key transport; originator usage period; private key; public key; recipient usage period; secret key; split knowledge; trust anchor Control Families None selected. To complete these tasks, review the resources provided to you. Spoke key-management components are easily deployed to these nodes and integrated with the local encryption applications.