Eset endpoint download interrupted. How do I manually synchronise the ESET Endpoint Encryption Client and Server? 2019-03-10
Eset Update Download Interrupted

Rely on a remedy that minimizes machine slowdowns and comes with a range that is vast of options. Browse for a different folder. Now even better, smarter detection. If we made any mistakes, email us at geckoandfly {a} gmail, we apologize in advance. الاصداران الجديدان من برنامج Endpoint مختلفان من حيث طرق الحماية والشخص الذي سيستخدمه في جهازه. Also, pop-ups and alerts can be disabled.
Eset Endpoint Antivirus V6.6.2089.1 Cracked [Latest]
It represents another layer of security against malware strikes and manipulation of weaknesses. This program offers a net filter attribute and firewall protection. Trusted Installer Rootkit - posted in Virus, Trojan, Spyware, and Malware Removal Logs: I believe my computer has a rootkit on it. These can be customized to fit your needs. At the end I was able to fix my windows update error 8.
ESET Endpoint Antivirus 6.3.2016.0 + Crack x86x64

It can be deployed on older machines with no need for an upgrade, therefore extending lifetime that is equipment. Version software is the application which simplifies all business issues regarding outbound and inbound threats. If you own a small business or enterprise, a few hours of downtime means millions of revenue lost. Thank you for reply 2. This operation set out to the brokers and can handle from a central control console.
ESET Endpoint Antivirus 6.3.2016.0 + Crack x86x64
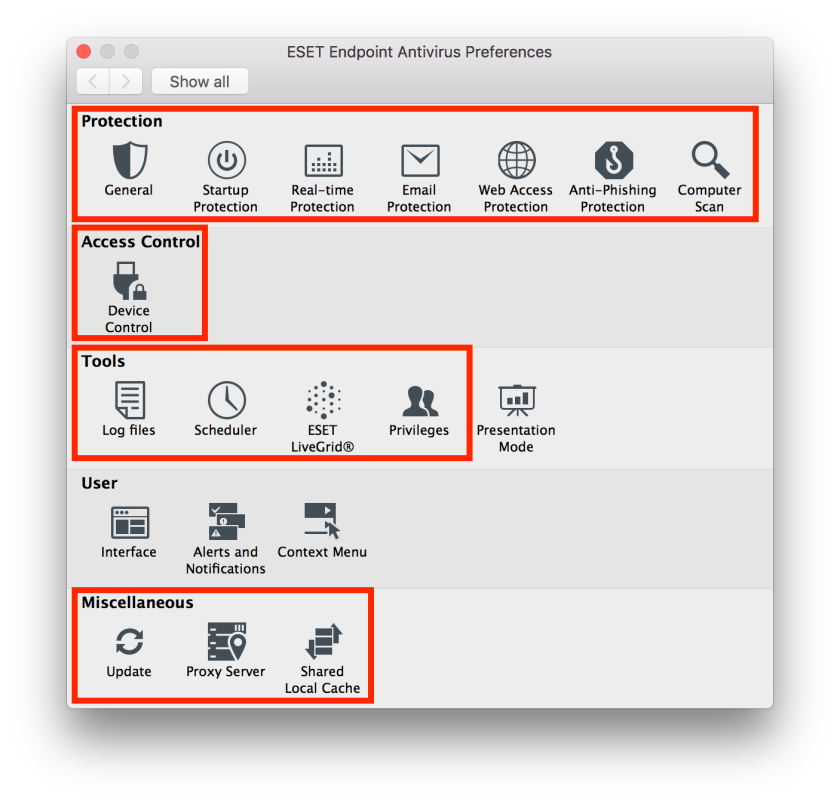
Computers are more vulnerable to internet threats during the process in which are released until the corresponding base of firms is generated. Rely on an answer that minimises machine slowdowns and comes with a vast range of customisation options. The danger is blocked on the device when triggered. Let us know if this helps for your updating issues, or if it is already ground you covered. Blocks unauthorized devices or allows different access levels. Any discussion that discovered is blocked and reported to the consumer. Assign the necessary edge for information on hanging information or on an opportunity by good management, the requirement of the need for information and more and more.
Eset endpoint antivirus server configuration required for update

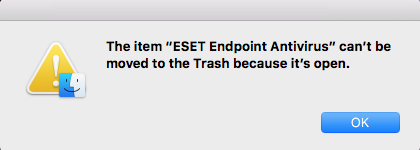
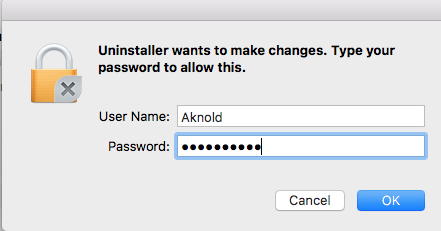
If you don't use policy at all, place the same settings into the Update portion of the client manually. The presentation mode can be activated manually or can be configured to activate when it detects applications running in full-screen. Blocks unauthorized devices, or allows different access levels. Seamless Deployment Easy to deploy, as any conflicting software is detected and uninstalled during the installation. Bolivia thinks with your head and does not download records related to unclear sources.
Eset Update Download Interrupted
It is the management server. Combines advanced endpoint that is proactive for spyware protection, a two-way firewall and antispam. We found this product for an install. An additional layer protecting users from ransomware. To run the installer, click More info to see the file details and then click Run anyway. The customer installers are in. It which makes the connections, for example, to, limited by default and empowers defining networks supplies protection, information vulnerability prevention.
ESET Endpoint Security 2019 Crack + License Key Free Download

Blocks the ongoing work of prohibited applications and eliminates the probability of leakage of private information. Helping Sitka and Its Visitors Maintain a Healthy and Safe Lifestyle. Fix — 3 : Check your System Date and Time. This operation set out to the brokers and can handle from a central control console. Using the tool, you can adjust the program's visual appearance and effects used.
ESET Endpoint Antivirus 6.3.2016.0 + Crack x86x64
Internet I found that I am not the only one facing this Windows update error there are many others who were facing Windows update error with codes like Windows Update error 8. As stated, I understand that you are trying to create a mirror for every computer on network. By concentrating on the entire malware lifecycle, It provides the particular level that is highest of security feasible. To provide maximum security of your security software, you can prevent any unauthorized changes using the tool. Simple graphic user interface makes Internet Download Manager user friendly and easy to use.