Eset endpoint security 6.4 download. ESET Endpoint Security Crack With Lifetime Keys Free Download 2019-05-10
ESET Endpoint Security 6.4.2014.0 [Latest]

It detects any entry by any toxic agent and relates to it as quickly because it can along. New functionality Anti-Phishing — protects you from efforts to acquire passwords in addition to other information that is painful and access that is sensitive is limiting malicious websites that impersonate good ones. Includes risk assessment and forensic investigation. When triggered, the threat is blocked immediately on the machine. Therefore, we are in need of each one of these tools in one software that is single can monitor all the sources of harmful agents and protect our devices against them.
ESET Endpoint Security 6 Crack, License Key Free Download
So make sure you read the readme file first. You should at least once utilize in your Computer to be safe. A botnet that is— that is learning that is new through analyzing its system communication patterns and protocols. Eset Endpoint Security 2016 6. In the conclusion of the magician, we could get into program consoles and start the procedure for placing each configuration and the coverage settings. Administrators protect and can secure Microsoft Windows endpoints through anti-virus capacity web filtering and device management, in addition to the network from spyware and viruses.
Download ESET Endpoint Security 6.4 for free

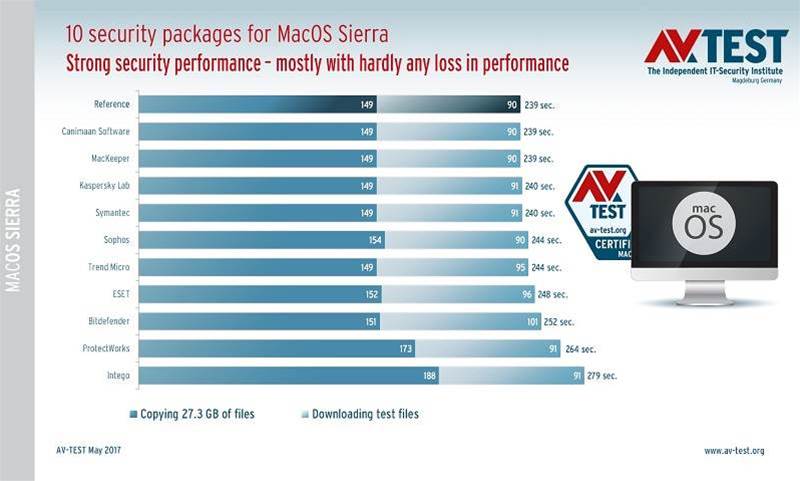
Hello, Please excuse me if there's an answer of this, but I have the following problem. Please note, that this functionality will be available for Windows Endpoints only. You might realize about the slowdown a trade for high-quality protection and advanced security features. This is authorized software that is majorly used in the operating systems broadly nowadays and is very famed. Keep out distractions like pop-ups during presentations or slideshows. The application includes a firewall that can help block traffic that prevents that is malicious against inadvertent spyware that is distributing.
Eset Endpoint 6.4

The spyware originates from a variety of sources which include videos, songs, publications and especially kids internet sites. The danger is blocked on the device when triggered. They can also be modified in your installation package during. Guard company network against breaches with two-way firewall with learning mode, and control illegal media and devices in the network. Contemporary technologies dependent on the use of artificial intelligence may stop viruses, spyware, viruses, trojans, spyware, viruses, viruses, rootkits, and other strikes without affecting the operation of the computer and interruptions from being attacked. Make sure that under Package contents, the option Security product + Agent is selected.
Eset Endpoint Security 6 Crack + License Key FREE Full Download

When I add the remote computer to the All Computers group manually it adds, but I cannot see no details of it and even if I try to create task to deploy agent even that with the custom made installer it is already installed it fails. Crack for Eset Endpoint Antivirus 2016 Final. Enlist a range of customization and reporting features to tweak the system security as you need. It not only protects a device from viruses but additionally shields it against spyware, trojans, worms, adware, etc. You can select another language optional. Please note, that this functionality will be available for Windows Endpoints only.
ESET Endpoint Security 6.4.2014.0 [Latest]
It creates it easier for users to safeguard themselves. New Graphical Interface: a touch that is very is the high-resolution program that is well-matched access to its all features and tools used many. It constitutes another important layer of protection against spreading malware, network-conducted attacks, and exploitation of vulnerabilities, for which a patch has not yet been released or deployed. Silent installation To run the installation with no user interaction, see below. Modern technology dependent on the use of intelligence can prevent rootkits, spyware, trojans, spyware, viruses, viruses and other attacks without impacting the functioning of the pc and interruptions from the work from being assaulted. You could protect your inbox from spam and files that are corrupted.
ESET Endpoint Security 7.0.2073.1 with Activation Code [Updated]
Complete protection for company endpoints combining proven antivirus technology with a built-in firewall, web control, device control and remote administration. A problem tackled by many people while linking to a Wi-Fi that is the general spot that is the public possibility of entrance by someone through the Wi-Fi. It constitutes another important layer of protection against spreading malware, network-conducted attacks, and exploitation of vulnerabilities for which a patch has not yet been released or deployed. You can install Antivirus on this one on almost any type of windows server. For illustrated instructions for the setup wizard, see the Online Help topic.
ESET Endpoint Security 6.6.2086.1 Crack+License Key Full Free

They can also be modified in your installation package during. Help for touch-screens and quality that is detection that is removal that is a lot of protection solutions. If you decide later to change this setting, you are able to do so using Advanced setup. It empowers defining networks which makes the connections, for example to, limited by default, and supplies protection, information vulnerability prevention. It represents another layer of security against malware strikes and manipulation of weaknesses. .
Deploy an install package to client workstations (6.4 and later)—ESET Knowledgebase

Server Hostname and Port are automatically selected for you. All the images are collected from Google. Select the check box next to I accept the terms of the application End User License Agreement and acknowledge the Privacy Policy. I like it very nice and great working. Take advantage of advanced monitoring and reporting tools for complete oversight and to take immediate action. We discovered supporting the customers to be as straightforward.