Ftk password recovery toolkit download. Product Downloads 2019-01-24
What is AccessData Password Recovery www.littleboyblu.com and How to Fix It? Virus or Safe?
Drives that show otherwise, without a plausible explanation, would be suspect. Search torrent: access data password recovery toolkit. AccessData recommends that the certification be taken in conjunction with their AccessData Boot Camp and Windows Forensics courses, but it is not required. When the client software was downloaded, there was a GoogleDriveSync. That means we must be prepared to deal with encrypted data. Can you talk a little about how that works and why it's important? Delaying the start of this service is possible through the service manager. Take your time to get familiar with the program's design and wealth of functions available.
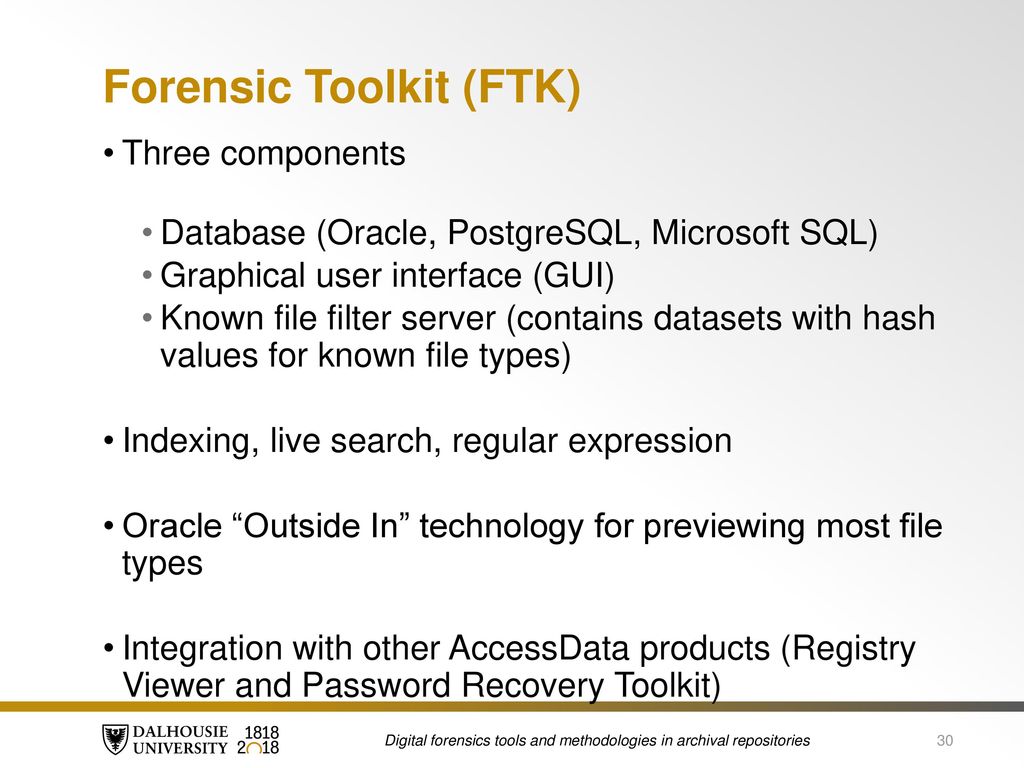
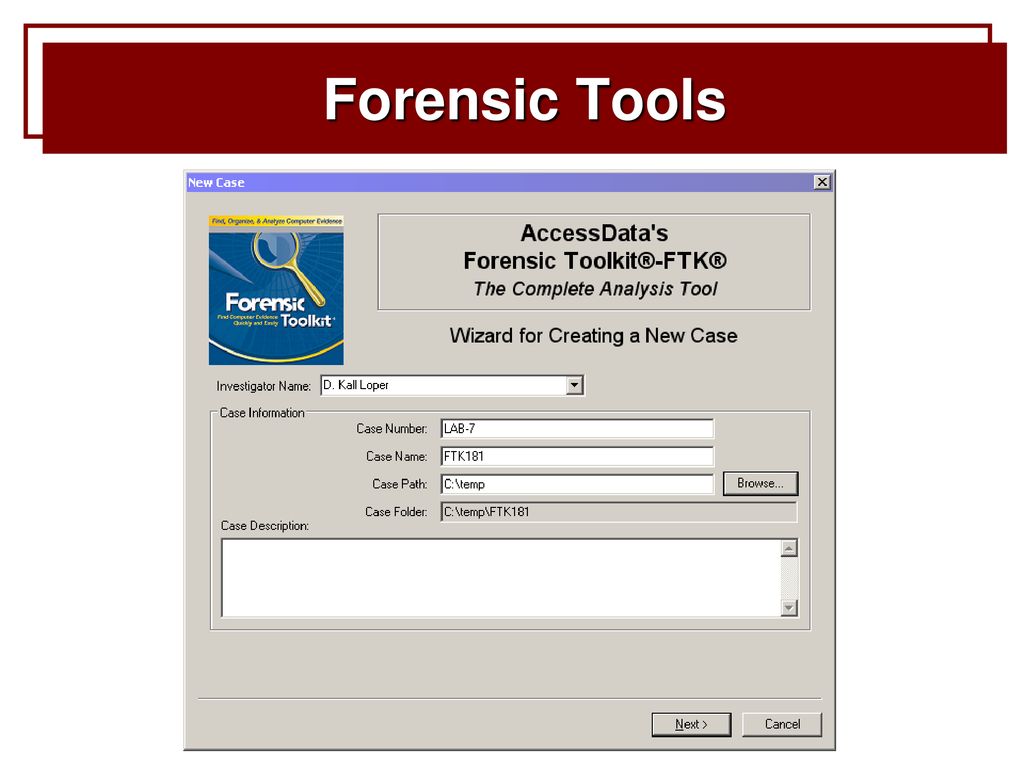
Forensic Toolkit 5
Dictionary attacks are generally the chosen method over brute-force attacks. Passwords are commonly used in a variety of locations, and when conducting analysis to determine a password to view encrypted files, one practice is to build an index of data to use with password analysis tools such as AccessData Password Recovery Toolkit, Passware, or Elcomsoft password analysis tools. Of these methods, none is guaranteed to work all the time, or even some of the time depending on the encrypted file properties. Please Note: If AccessData Password Recovery Toolkit. Written by a Certified Information Systems Security Professional, Computer Forensics: InfoSec Pro Guide is filled with real-world case studies that demonstrate the concepts covered in the book. From an evidentiary or investigative perspective, the presence or use of these applications can serve as the next best thing to the original evidence.
AccessData Password Recovery Toolkit
If the password is not located in memory, or if memory capture is not possible, it is still possible to access a Google Drive account using the forensic image of a hard drive where the Google Drive client software has been used to access an account. If you are not currently backing up your data, you need to do so immediately to protect yourself from permanent data loss. Part I covers the technology all digital forensics investigators need to understand, specifically data, storage media, file systems, and registry files. This procedure involves moving data from one location on the drive to another. Confirm the removal by clicking Uninstall.
AccessData Group Forensic Toolkit (FTK) Version 5.1 in Data Forensics

Activate the Uninstall Programs button 5. Unfortunately, these same utilities can be used for other, less honorable purposes. We are sorry for the inconvenience. There are a few different ways you can attempt to determine whether a drive has been recently defragmented. Sometimes, users want to remove this program. This can be made even more complex by substituting an exclamation point for the letter I and substituting the number 3 for the letter e, so that the password becomes! This enables team members to collaborate more efficiently, saving valuable resources. In full, this and the other four books provide preparation to identify evidence in computer related crime and abuse cases as well as track the intrusive hacker's path through a client system.
AccessData Password Recovery Toolkit version 7.9.0.777 by AccessData
Analysis to determine the method of access, whether the client software was used, a browser used to upload, access, or download, or a combination of both, is possible. There are also specialized tools that can bypass or recover passwords of various files. However, if the password is not located in memory or if memory capture is not possible, it is still possible to access a SkyDrive account using the forensic image of a hard drive where the SkyDrive client software has been used to access an account. Even if encryption or steganography cannot be bypassed, documenting which files are concealing data can help an investigator, attorney, or trier-of-fact determine the intent of the defendant. The defragmentation process can occur in three ways; it can be user scheduled, manually initiated by the user, or done automatically by the operating system Casey, 2009. Activate the Uninstall Programs button 5.
AccessData Password Recovery Toolkit version 7.9.0.777 by AccessData
This can be easier said than done because uninstalling this manually takes some knowledge related to removing Windows programs manually. Every program or application or other system that uses passwords does it differently. All the items that belong AccessData Password Recovery Toolkit which have been left behind will be found and you will be asked if you want to delete them. These troubleshooting steps get progressively more difficult and time consuming, so we strongly recommend attempting them in ascending order to avoid unnecessary time and effort. They can target specific files and folders as well as potentially incriminating system values like those found in the Windows Registry. Even when full disk encryption is not used or can be circumvented, additional effort is required to salvage data from password protected or encrypted files Casey, 2002.
FTK Forensic Toolkit Overview
If you would like to learn more about manual registry editing, please see the links below. Success depends largely on the quality of the tool and the skills of the user. Students are introduced to the technology involved in computer forensic investigations and the technical and legal difficulties involved in searching, extracting, maintaining, and storing electronic evidence, while simultaneously looking at the legal implications of such investigations and the rules of legal procedure relevant to electronic evidence. Because of this risk, we highly recommend using a trusted registry cleaner such as Developed by Microsoft Gold Certified Partner to scan and repair any AccessData Password Recovery Toolkit. Once forensic analysis has determined, a Google Drive account has potential evidence of relevance to an investigation, and the practitioner can communicate this to relevant persons to enable them to respond to secure evidence in a timely manner. The text was written to fulfill a need for a book that introduces forensic methodology and sound forensic thinking, combined with hands-on examples for common tasks in a computer forensic examination. Mallery, in , 2013 Use Robust Passwords With the increased processing power of our computers and password-cracking software such as the Passware products 47 and AccessData's Password Recovery Toolkit, 48 cracking passwords is fairly simple and straightforward.
torrent Access Data Password Recovery Toolkit Crack

A confirmation page will show up. Click Next to start the cleanup. Hash values for the client software can be calculated and searched across forensic image files, memory, and network captures. Which Tools Does It Contain? It's not exactly a new insight, but people are becoming more and more aware that passwords as a security device are often inadequate. Available as a perpetual or subscription license.
AccessData Password Recovery Toolkit version 3.6.1 by AccessData

This forces the password-guessing tool to also hash the password 10,000 times per password guessed, which leads to many fewer passwords per second. Keeping track of when and where your AccessData Password Recovery Toolkit. While creating copies of original disk drives, a critical aspect is to check file integrity. Here is how to do this: 1. Guide to Digital Forensics: A Concise and Practical Introduction is intended for students that are looking for an introduction to computer forensics and can also be used as a collection of instructions for practitioners.
torrent Access Data Password Recovery Toolkit Crack

For example, this could reveal relevant evidence that resided in a document at some point in the past but was intentionally changed and would not be recoverable any other way — a major stumbling block in digital investigations. Considering that a password may not even be in a recognizable word format, a dictionary attack will be ineffective in some instances. What are those based on and how does that work? In such cases, it may be possible to locate unencrypted versions of data in unallocated space, swap files, and other areas of the system. Take a look for more info on AccessData. AccessData Password Recovery Toolkit is a software program developed by AccessData. In addition, registry entries may indicate the use of the setup software or the client software, as will link files. Using a automates the process of finding invalid registry entries, missing file references like the one causing your AccessData Password Recovery Toolkit.