Havij sql injection pro. ITSecTeam Havij Pro 1.17 Crack + Registration Keygen 2019-01-19
Download Havij Latest Version 1.17 2019 Pro Full Version [CRACKED]

The basic purpose of this software is to take advantage of defenseless and weak web applications. The program can capitalize on a defenseless web application. It will start scanning and give you results after some time. Then password hashes, dump tables and columns. This step reveals all the columns in selected table. If a person intends to use it for harm, the program makes it much easier for them t be successful in their task. Havij pro is the software that can deal with this language.
Havij 1.17 Pro + Crack

Enter your email address to subscribe to onhax and receive notifications of new cracks via email. It can get the benefit of susceptible web software. So, Automated tools have also great importance you can also check your own website for the vulnerability. You can use google dorks for this purpose, I have already told in many tutorials that what google dork is, Most common dorks for sql injection vulnerable site are:- inurl:index. There is a free version available and also a more fully-featured commercial edition available. The characteristic authority of Havij that differentiate it from alike tackle lies in its sole method of injection.
Havij Pro 1.17 SQL Injection Full Version Cracked Download

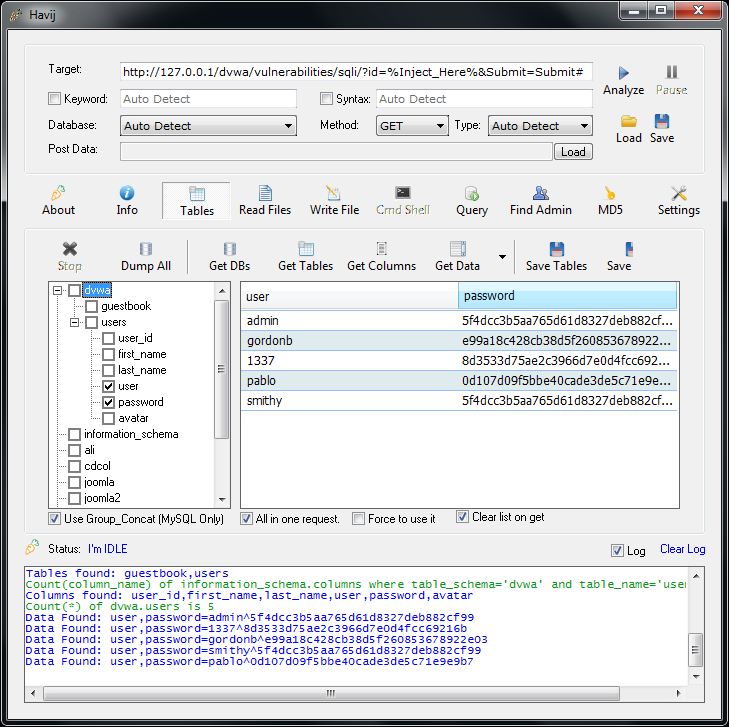
It can also be used for educational purposes. Such ease of use may be the reason behind the transition from attacks deployed by code-writing hackers to those by non-technical users. How to Crack Havij Pro 1. The accomplishments price of this software is a lot more compared to 93%, and that tends to make it distinctive from some other resources of similar genre. The accomplishment rate when using this program is over 95% at susceptible injection targets. It can make the most of an insecure net program. In my case, admin table has columns — id, nome name , email, senha password , and nivel level.
Havij Pro 1.17 Cracked SQL Injection Tool Free Download
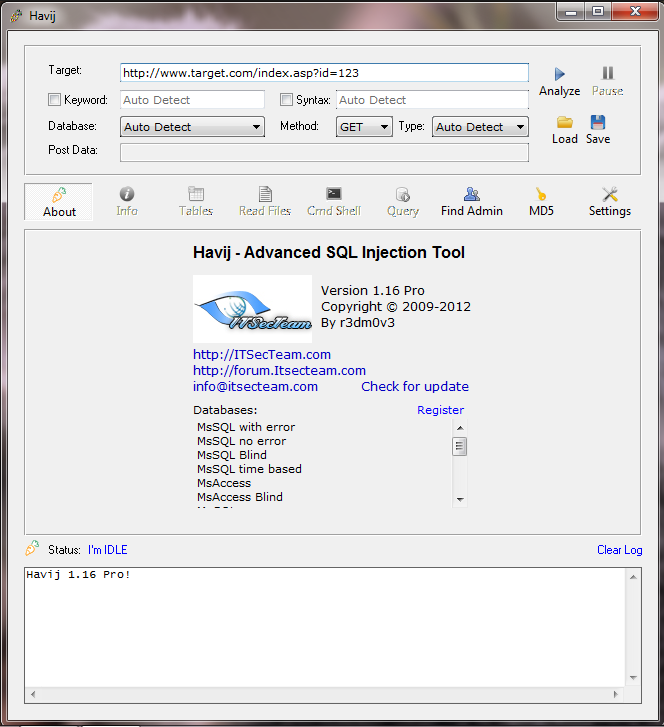
You do not have to be a specialized user. Download Havij Here How to Install and Use? It can take advantage of a web application. Havij Crack Full Version Download Havij 1. Warning — This article is only for education purposes, By reading this article you agree that Hacky Shacky is not responsible in any way for any kind of damage caused by the information provided in this article. The power of Havij that makes it different from similar tools is its injection methods. The success rate is more than 95% at injectiong vulnerable targets using Havij. It can take advantage of a vulnerable web application.
Havij 1.17 Pro Cracked Full Version Download

Havij download can make the most of a vulnerable web program. Illegalcrew welcomes hearing from our readers and members. By using the advanced version of Havij, you can perform all the functions at the back-end of a vulnerable website. However, some evil minds use this application to hack different websites. However, you may still download older releases of the software which came with an evaluation edition. It allows for users to hack into a site in just a matter of seconds. The distinctive power of Havij that differentiates it from similar tools lies in its unique methods of injection.
havij
It can likewise make the most of a vulnerable web program with several security loopholes. Users will also get to work on the back-end database fingerprints and execute commands on the operating system. You have successfully cracked your version of Havij. As a result of these integrated configurations, Havji Pro could utilize by anybody. Put it in Google search bar and hit enter. Verdict Tools like Havij must only be used for the positive and beneficial purposes. Due to these built-in settings, Havji Pro can be used by anyone.
Download Havij Latest Version 1.17 2019 Pro Full Version [CRACKED]
We cannot, nevertheless, guarantee the quality of the old evaluation editions as many bugfixes and features have been effected since then. The distinctive power of Havij that differentiates it from similar tools lies in its unique methods of injection. This may also mean that not all attacks will necessarily carry information disclosure or damage — they sometimes only serve to pass a boring afternoon for a high-school kid, playing with a cool tool they found online. Make sure, the database is selected in the respective screen. The distinctive power of Havij that differentiates it from similar tools lies in its unique methods of.
Analysis of the Havij SQL Injection tool

It can take advantage of a vulnerable web application. Step5: Now select the Tables with sensitive information and click Get Columns button. The newest variant of Havij Pro 1. Havij pro is the software that can deal with this language. Users can dump tables and columns, fetch data from the data base, run Structured Query Language statements and access underlying file system. Easily execute operating system shell commands.