Help_decrypt.html trend micro. Restore Encrypted Files 2019-04-08
Trend Micro
This is a pretty standard approach in the software world if you think about when you need to install new versions of Office, etc. Malwarebytes Antimalware for Business and AdBlock Plus addon for Mozilla Firefox. Trend Micro released a for victims of earlier Cerber infections but it has limitations. Restart the computer normally to reset the registry. Please check this for more information. Products available for online renewal are for 100 users or less, and up to 6 months after the product expiration date.
Get Trend Micro Security
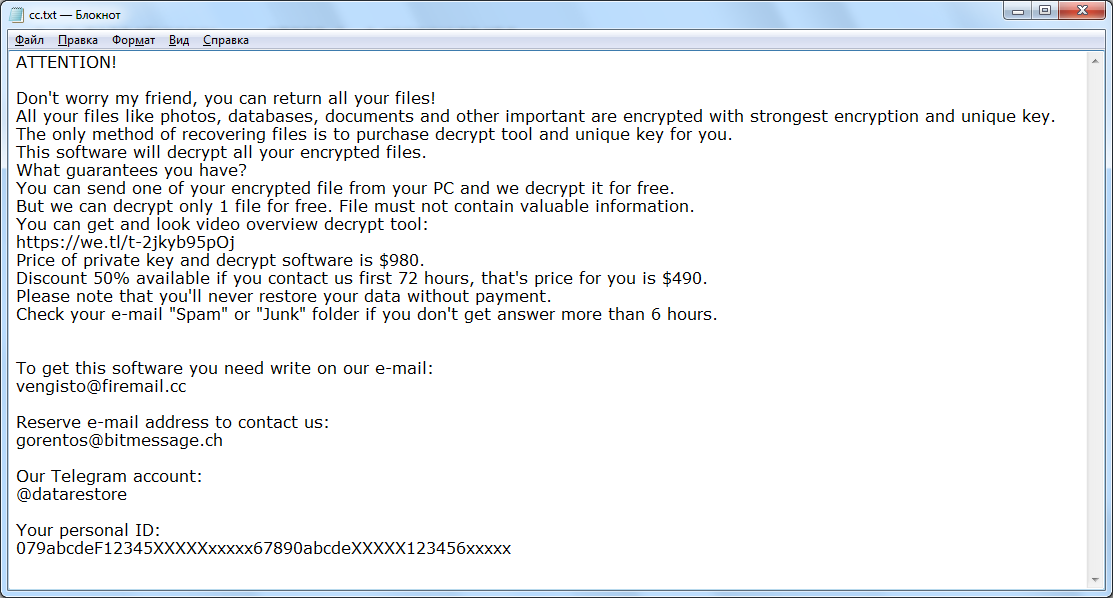
You may also check out this first before modifying your computer's registry. At the moment, there are no free decryptors available, but there are certain manual methods we explained in this article to help you decrypt files. It has absolutely nothing to do with malware. To do that, restart your computer, before your system starts hit F8 several times. To remove malware, you have to purchase the full version of Spyhunter. Hi LegoMan, that's quite clever. Please do this step only if you know how or you can ask assistance from your system administrator.
Trend Micro Ransomware File Decryptor Updated

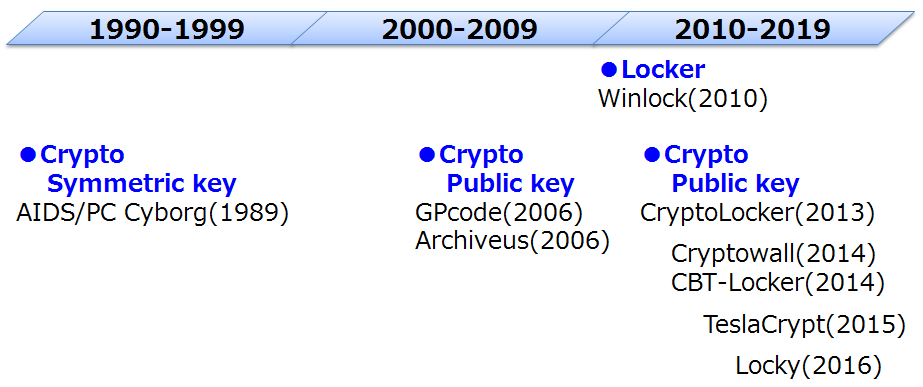
She even told me that if i recovered her files i will have money so please tell me how to recover it :D Any files that are encrypted with Cerber Ransomware will be renamed with 10 random characters plus the. » For Windows 8, Windows 8. You may also check out this first before modifying your computer's registry. As mentioned previously, the filename and other metadata is usually irrelevant. Please do this step only if you know how or you can ask assistance from your system administrator. In summary the technologies have matured to the point it's not an overhead in most environments to administer. » For Windows 8, Windows 8.
How to remove Cerber3 Ransomware and decrypt .cerber3 files

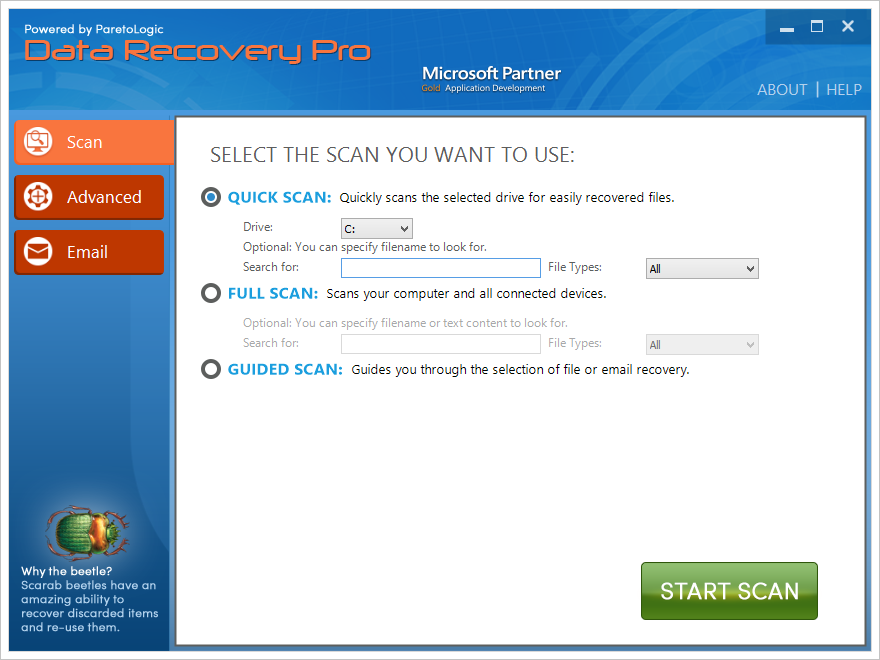
Detailed instructions are included for each of them. Now you can try to use manual methods to restore and decrypt. It is very important that users do not try and reboot their system before trying the tool. If the Windows Advanced Options menu does not appear, try restarting again and pressing F8 several times afterward. When you decrypt or encrypt a file, OfficeScan creates the decrypted or encrypted file in the same folder. Search for files or folders named or All or part of the file name.
Help_decrypt in Outlook 2010
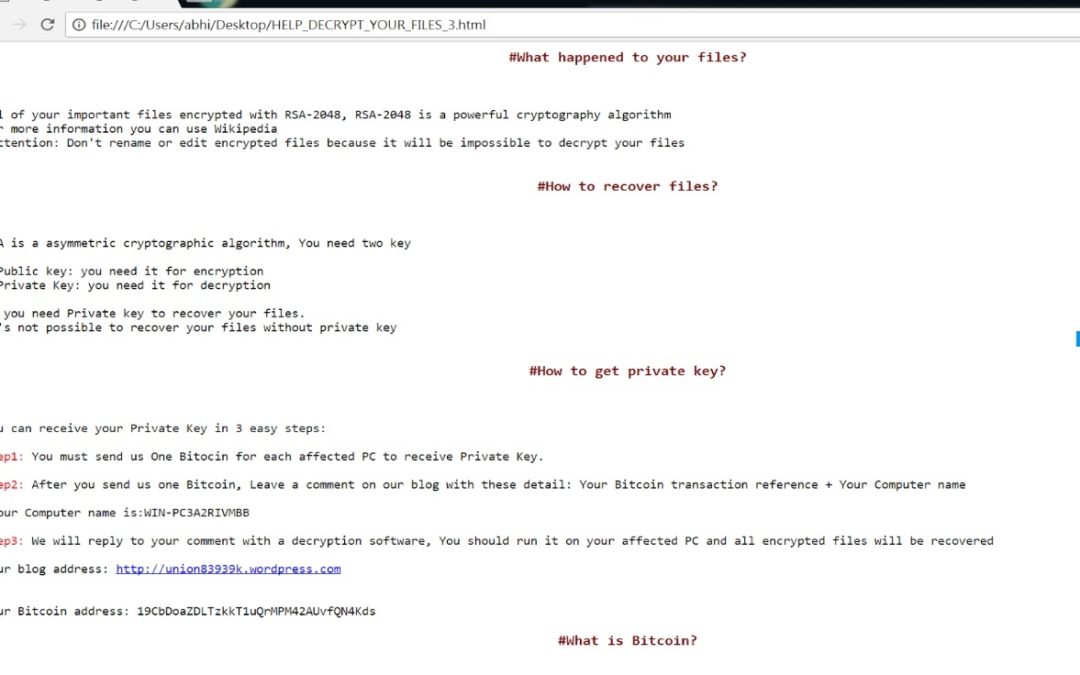
If the infected machine is rebooted, the ransomware process is somehow stopped after the initial infection, or any other situation occurs that would affect the process memory of the infection machine the decryption will fail. Apparently numerous other companies were effected as well. If you find an infected document and you need to retrieve the information from it, you will need to decrypt it first. As the CryptoWall attacks your local AppData folder and the mappped drives, would the script be better if it detached the mapped drives immediately once it detects it? Start your computer in Safe Mode with networking. Make sure you have completely removed the threat before decrypting the files.
.cerber3 ransomware attack my files please help me with out paying to
Choose Safe mode with networking option from the options list using up and down arrows on your keyboard and hit Enter. Antiviruses have a small chance to catch Cerber3 virus as it is constantly modified. Keys can produce the same hashes sometimes. After 30 days trial or paid version expired, only Ad blocking will still continue to function. Need to decrypt your files? It is currently unknown how long the prime numbers related to the private key will be stored in the memory address space before being reused or overwritten. Else, check this first before modifying your computer's registry.
[SOLVED] The Shame of CryptoWall 3.0
Save your Hard Drive keep it in a safe place and wait until they find a way. Else, check this first before modifying your computer's registry. If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. Select the encrypted file or folder The tool can either attempt to decrypt a single file or all files in a folder and its sub-folders by using recursive mode. They will wait for the victim to pay for the ransom.
Trend Micro Ransomware File Decryptor Updated
Trend Micro Security also blocks annoying, intrusive ads for faster site loading and a better web browsing experience. You may already know HitmanPro as famous cloud-based anti-malware scanner. This Petya family is different from EternalPetya family discovered in 2017. » For Windows 8, Windows 8. There is an ongoing discussion in this topic where you can ask questions and seek further assistance. If you had an approved executable, which was then modified maliciously, because the hash would calculate differently for that file going forward, it would no longer be approved and would be blocked.