Learn kali linux pdf. Learn Ethical Hacking Using Kali Linux From A to Z Course 2019-02-28
Tutorial on Hacking With Kali Linux
Ransomeware: It is a code program by Hacker which encrypts mean make them so nobody can open that data your whole Hard disk data then ask for some Money if you want to remover your data. This book has the most advanced tools and techniques to reproduce the methods used by sophisticated hackers to make you an expert in Kali Linux penetration testing. When you open the link and 2-3 another tab, then your facebook tab page Url will be replaced by another page. My installation guides are outdated mine are for Kali 1. Now, I've been dealing with beginners since a long time and myself was one for a long time too. As far as Facebook hacking is concerned, it's a difficult task. In the final chapter you will acquire the skill of exploiting remote Windows and Linux systems and you will learn how to own a target completely.
Kali Linux Wireless Penetration Testing Beginner's Guide, 3rd Edition

You will find commonly used security testing methods at the start followed by exploitation and post-exploitation methods in the middle and you will also learn to bypass physical security, social engineering, web services and attacking network direct end user. You will also learn a critical concepts called social engineering used by hackers to steal sensitive information. Other Youtube Channels for Learning: Also read: Well in 2016 and onwards, obviously its good to cover getting started with Kali and by proxy, Linux. Buy from Amazon Mastering Kali Linux for advanced penetration: As evident from this book name, it is for masters. In this lesson, I am talking about basic commands in Kali Linux, not all only that you needed in starting a + free source of learning all Linux commands. Also Read: 4 The Internet is used all around the world at a very large scale. Wi-Fi is the most popular internet connection.
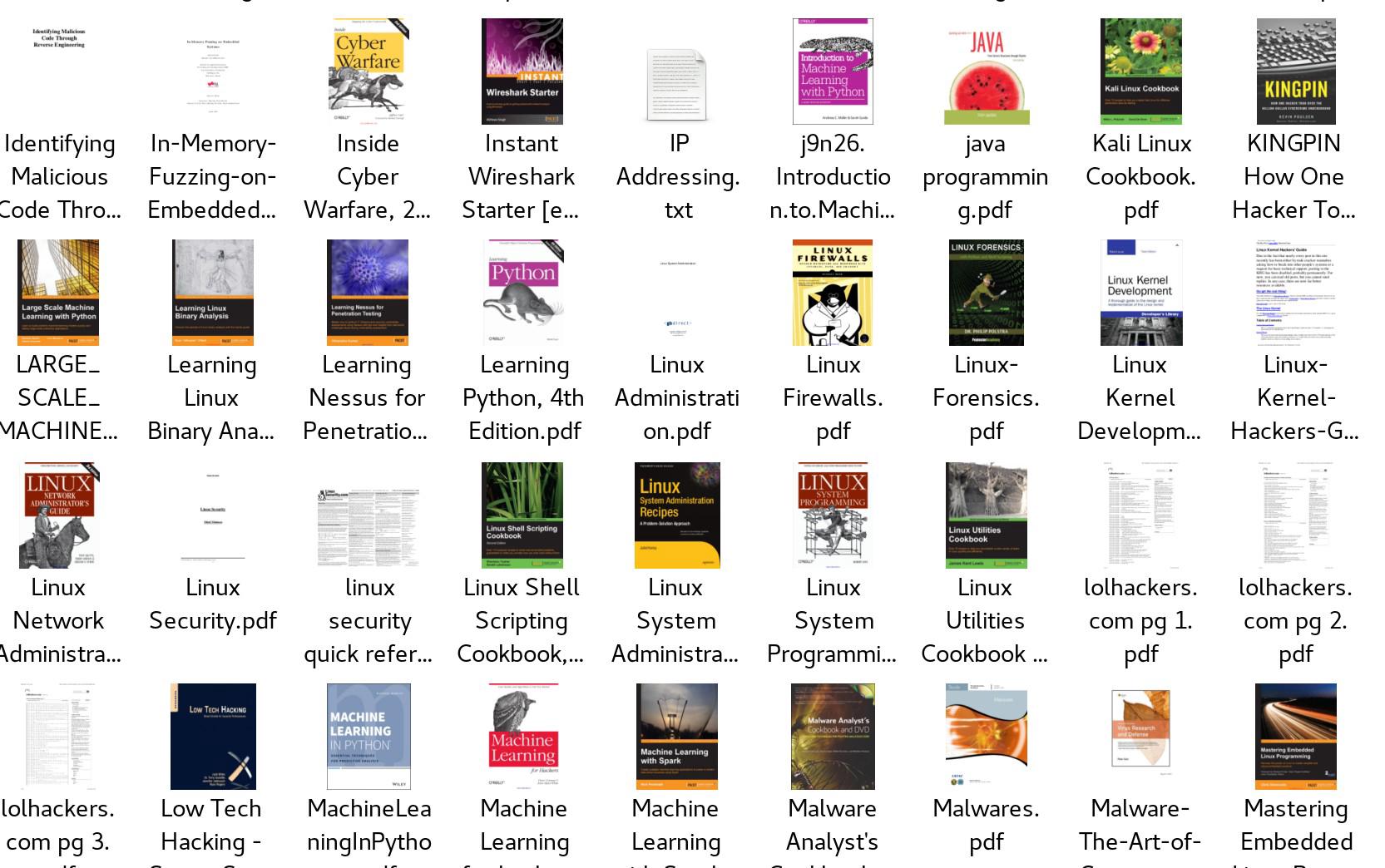
Which are some good books in PDF format to learn Kali Linux?

Static: by default it is static. Your feedbacks are always welcome. Now you know your path to become a Pen tester. But, to use these tools, you first need to know these tools and what they can do for you. When data exceeds the limit of bandwidth, server crushes.
Top 10 Kali LinuxTutorials : Guide to Start Learning to Hack using Kali

No more words let come to point How to dual boot with Kali Posted: March 25, 2017 Hope you have installed Kali Linux in virtual box or using any other way. Importantly, you will receive monthly virtual machines as a hacking challenge, to test your progress. In Short Hacks: In the world of technology, you will hardly find anyone reading books to acquire knowledge. You will then dive into classic and modern encryption techniques where you will learn the conventional cryptosystem. Learn from these Kali Linux Tutorials that are free.
Learn Ethical Hacking Using Kali Linux From A to Z Course
Maybe something wrong with VmWare. This is one of the best books which you can have for learning testing the security. It provides with extensive knowledge of what all you can do in wireless technologies. It will teach you from starting like kali overview, Metasploit Tutorials, Information Gathering, Exploiting Windows and Linux, wireless attack, password hacking techniques and security tips for your network, etc. Paytm use 128-bit encryption mean if it will increase your password length which has 2 128 combinations for applying brute force attack. The advance version of phishing: Desktop Phishing Tabnapping Desktop Phishing: This is the advanced type of phishing.
Kali Linux Hacking eBook Download in PDF 2019

I would have said that the iso may be broken, but since you downloaded it twice, that quite improbable. It can be changed by Vpn or using the proxy. In particular, it's ideal for system administrators and system architects who want to ensure that the infrastructure and systems they are creating and managing are secure. But the problem is in virtual machine my network is not detected, rather if i type 'airmon-ng' on terminal, no networks are detected, probably there could not be network driver pre-installed in any virtual machine, but still there would be some way to connect host's network driver to guest's. With more than 600 protection resources in its collection, the Kali A linux systemunix submission can be frustrating. It's an ideal reference guide if you're looking for a solution to a specific problem or learning how to use a tool.
Top 10 Kali LinuxTutorials : Guide to Start Learning to Hack using Kali

You'll have to basically divide your disk in two parts and then install Kali Linux in one part and the other part already contains your Windows. I don't think a book pdf or an actual book is a great idea looking at the current scenario. While you can use an old installation guide and make a few changes and have it work for you, it's better, especially if it's your first time installing an operating system alongside another, that you follow a guide tailored for your situation eg. Besides learning these tools, you will see how to use OpenVas, Nikto, Vega, and Burp Suite. The terminal is software as commands prompt available is window operating system. The training in this course involves using a testing lab for practicing various types of attacks. It is operating system used by hackers because it has all software that needed in Hacking.
250+ A

If you want an authorized certification for hacking with Kali Linux, visit the above link to go to Udemy. Beside Hacking, Python also helps in data science. Kali Linux is very independent in terms of installation. After that software combination all these factors and create so many words and try to apply as every word as a password. Encryption: Generally it is used for encrypting the password in the database. Fake traffic is sent to the web server.
Learning Kali Linux
My recommendation would be to start by hacking a wifi, then do some penetration testing, and maybe read something on Denial of Service when you have free time. The book covers network sniffers and analysis tools to uncover the Windows protocols in use on the network. Host: I like your site. In this article, I will explain everything from scratch. Maybe ill talk my dad into it or get a job this summer or something. The Pen test site look rather fun to test, quite honestly. .