Logmein mac control alt delete. Sending Ctrl Alt Del command to a remote computer 2019-05-05
How to Perform

When scanning with default recommended settings these applications are evaluated as clean. Copy, Cut, and Paste Ctrl + C, X, or V Copying and pasting is a way of life for most people. It is an ongoing project and very interesting. Once you've done that, write a message to the lab that includes all of the information asked for in the knowledgebase article, along with any other additional information you feel might be helpful or useful for them to know. I do not see a need for a product in which most end users will not take the time to study and learn all of Eset antivirus's intricacies and unexplained phrases just to help save themselves from the occasional malware infestation. Before connecting to computer you have an option to launch Logmein as a service Restart customer applet as windows system service.
How to send ctrl alt del to a remote desktop session
I understand this classification may sound general, but it has to be that way because there are so many different ways in which the performance, speed, reliability or behavior of computer can be affected. That valuable feedback helped us re-think our roadmap in order to further improve the program. We don't see much in the way of, say, spyware delivered through drive-by downloads. I do not see a need for a product in which most end users will not take the time to study and learn all of Eset antivirus's intricacies and unexplained phrases just to help save themselves from the occasional malware infestation. Just substitute the Command key where you see Ctrl.
Solved: Send Ctrl Alt Delete??

Instead, they are called potentially unwanted applications, and it is up to the user to decide if they want to detect those types of programs. One prefers more conservative detection with no notification about neutral stuff, another prefers scanner which is more strict and to have higher control regarding applications entering his system. Even this diatribe is not enough. Home users are typically not keen enough about security to learn all of the many, many settings in Eset antivirus much less Eset Smart Security. Let them who have eyes to see then. Many applications on Mac allow you to undo a command by pressing Command + Z. Each user choose what is best from his own individual perspective and he may change his decision any time later in the Advanced setup.
Solved: Send Ctrl Alt Delete??
This setting gives the user the possibility to scan for the applications with potential for misuse. If anyone has a solution or suggestions it will be greatly appreciated. Click the headings to sort processes. Remote access software, some monitoring applications, bitcoin miners, etc. You can download LogMeIn Free on as many computers as you would like. Eset, in its wish to be the best in the industry I am sure, is making the product more of a problem than a reliable, simple solution.
How to send Ctrl+Alt+Del in Remote Desktop

Users can turn it on if they want to or turn it back off at any time afterward in the program's settings. People will stop using Eset if using it requires taking a class or watching 2 or 3 hours of YouTube videos to make sure all of the settings are correct. However, there might not be a reason for such software to be used by a mail room clerk. How to Ctrl Alt Delete on Mac Turns out they are there—three magic buttons just like Windows. Or maybe they do other things like monitor your behavior on the Internet or inject advertisements into your search results or other web pages that you view. Like when you go to launch a program and you get a never-ending loading bar. But they are programs which customers have asked us to detect, which we do, but, again not as malware.
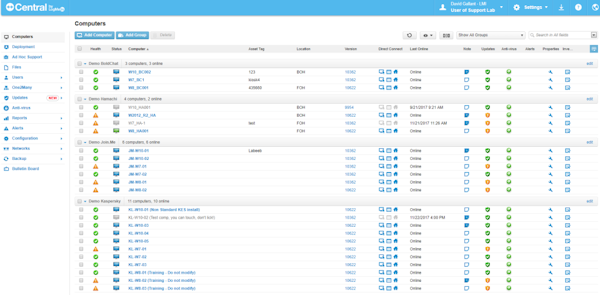
Remote Computer Access: Control Your PC or Mac from Anywhere
That different companies have different policies in how they handle things shouldn't be a surprise. Each user choose what is best from his own individual perspective and he may change his decision any time later in the Advanced setup. The bottom of the window even provides a visual representation of the numbers. On site 2 days ago at client and installed Eset Antivirus. One way is to use your mouse and click on Start Button and then click on Windows Security. And small businesses have much more to deal with than to become an expert in any specific software. Only non-approved applications are reason to be worried.
LogMeIn Remote Access
This is a different classification and is used for different reasons which I outlined above. Opinions about grey zone software differs from user to user. One prefers more conservative detection with no notification about neutral stuff, another prefers scanner which is more strict and to have higher control regarding applications entering his system. Home users are typically not keen enough about security to learn all of the many, many settings in Eset antivirus much less Eset Smart Security. I don't think there's any further reason to continue this conversation. Things get eve worse when you open the app and take a look at the options for Antivirus detection.
How do I remotely unlock my host computer?
Even touch devices like the have been able to implement an equivalent with holding the Windows key and pressing the Power button. Now press 'Cancel' button, and then press 'Switch User' button. I have also seen this problem reported by some who do not use Eset; however, the majority of people feel it is related to Eset. Instead, they are called potentially unwanted applications, and it is up to the user to decide if they want to detect those types of programs. Or there might be more specialized programs out there intended for use by specific groups of people in specific situations to do things like crack passwords, monitor network traffic or perhaps even access a computer remotely. I do not wish to take any more of your time with this thread, as I am certain that you have any other people to attend to with similar questions. Remote access software, some monitoring applications, bitcoin miners, etc.
Remote Computer Access: Control Your PC or Mac from Anywhere
A related behavior are software wrappers also known as download wrappers used on some software download sites. But, perhaps that is the problem. Regarding the optional classification categories: Suspicious applications detection turned on by default It detects run-time packers and protectors which are often used by malware. If people had the knowledge that you seem to be asking us to acquire just to use your product, there would be less need for Eset antivirus as they would probably be much more careful in where they went on the internet, what they downloaded and would probably run most things in sandboxes virtually eliminating the need for Eset altogether. I couldn't get it to work.