Mac list keychains. How to Reset Keychain Password after Mac Password Change 2019-03-26
How To manage passwords using iCloud Keychain access (mac and iOS)

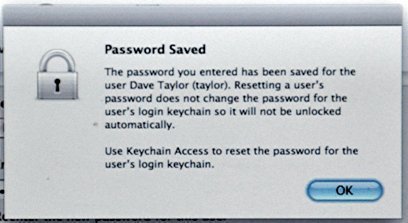
When the password used to log into the machine does not match the current keychain password, the login keychain does not unlock, resulting in persistant popup messages. When the user logs out or the Mac is turned off, the Keychain is encrypted to protect its contents. This means keychain passwords will not be remembered from one session to the next, even if the login password has not been changed. Restart Mac and hold on Command + S to enter single user mode. Sometimes when users change their Lehigh password they do not receive a prompt to enter the new one for a particular site or service.
mac

Enter that and click Allow, and the password will be revealed in the Password field. Hackers would still need to implant malicious software on your computer. Method 2: Reset Keychain password with command line in single user mode If you cannot work with Keychain Access because of something like Messages Agent constantly asking for the forgotten login keychain password, you can use command line to reset Keychain password in single user mode. So what is this all about? This can occur if a keychain has become corrupt or has permission errors. Below this is the Category pane. Fortunately, we no longer need to scribble down each and every password on a hunk of binder paper that we tape to our desks in plain sight. According to various sources, approximately 4.
How to manage passwords with Keychain Access
Still, the results would be very useful for any hacker who succeeded. When you are, enter the password and the keychain will be unlocked. Archived from on May 31, 2012. When Users cannot change their keychain password In some specific situations, the above instructions may not be sufficient to unlock or recreate the keychain. Just mount the disk image and use your favorite file manager to copy the required files to your Windows computer. It is , software released under the terms of the. The Keychain Access icon looks like three metal keys on a keychain.
Keychain (software)

Additionally, it can store secure notes, private keys, and certificates. Click it and enter the new login password in Password field to create new keychain. In what may seem like a step backward, we now juggle dozens of passwords. Because it has attracted low-quality or spam answers that had to be removed, posting an answer now requires 10 on this site the. Instead of maintaining an unauthorized presence on your computer with malware, they could simply get all of your login credentials and then delete the malicious program.
Macintosh Support
Wardle echoed that position, saying the best way for Apple to ensure that the highly sensitive keychain is secure would be to encourage security researchers to find flaws by paying them. Among its many features, PowerTalk used that allowed mail to be retrieved from a wide variety of mail servers and online services. When you connect to a network server, open an email account, or access any password-protected item that is keychain-aware, your keychain can provide the password so you don't have to type it. Log out of your account and then back into it. The keychain cannot be read by other tools because it is encrypted. Tap Saved Credit Cards, and you will be able to add or delete your stored credit card information.
Remove a Saved Password from Mac Keychain

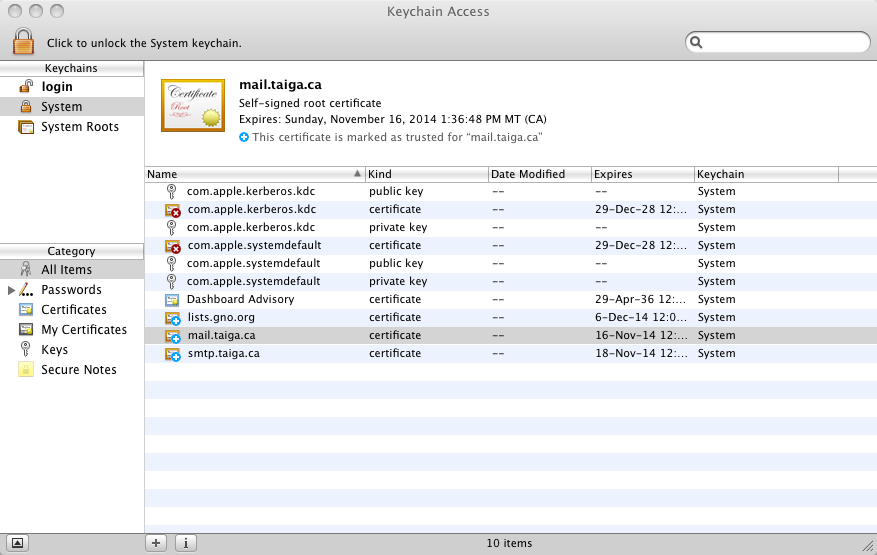
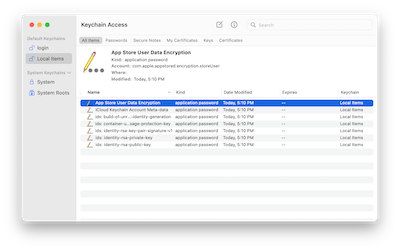
Here you can choose to view specific kinds of things stored in the keychain—passwords, secure notes, certificates associated with your account, encryption keys, and certificates used broadly by your Mac. We'll use Lehigh wireless as an example here, but you can use the same instructions to remove a saved password from any site or service in your Keychain. So you can simply enter the password you use with your account to uncover a keychain item's secrets. In the next screen, you will be able to add and delete new cards. It's a command line tool Apple made called 'security'… In Terminal there is a way to search for a specific item… this searches for a generic password for the service 'test-test. Enter the same password in the Verify field. Regardless of which happens, would help you access Keychain again.
KeySteal exploit attacks MacOS keychain to take all your passwords

The first time you try to record you must setup Accessibility to allow access for Automator the dialogs step you through it. If you know your old password, use that password to update your existing login keychain: Open the Keychain Access app, which is in the the Utilities folder of your Applications folder. What are my options besides making back-up copies of the keychain files which, obviously, will become obsolete next time I add a password? Now launch Keychain Access and select the login item that appears in the Keychains pane. From the column on the left, click the All Items list. This information will help building a custom template or mask when performing a brute-force attack. Double-click a keychain item to locate the Show Password option. Previous answers didn't work for me.
Keychain (software)
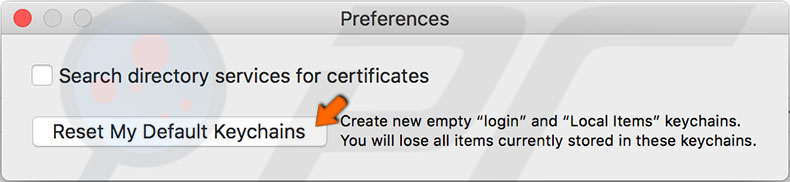
Share your login keychain If you have multiple Macs, each one has its own login keychain with its own set of passwords. Log out and log back in. As already mentioned, nearly every password the user ever types ends up in the keychain. In the sheet that appears, click Delete References. An expert speechwriter, Milano has drafted speeches that have been delivered to audiences ranging from 30 to 1,700. Another potential issue is attempting to decrypt a user keychain with a missing password. If you don't know your old password, the solution is to create a new login keychain.
mac

He has worked with a wide variety of clients, ranging from small one-man shops to major corporations and universities. Now tweak the playback speed in automator to 10x, Save the workflow, drag the actual workflow file back into Automator so that it calls itself. The top-left pane lists keychains accessible to you. Not the answer you're looking for? The export list item on the menu is greyed out. I logged out and logged back in and I had to re-enter many account passwords-- so it looks like it may have worked. The wikiHow Tech Team also followed the article's instructions and validated that they work.
Mac OS X security keychain command
If the disk image is in EnCase. Like so: Make a copy of the login. Archived from on June 13, 2011. To do this, click the magnifying glass icon in the upper-right corner of your screen, and type Keychain Access. And even though Henze has discussed the flaw publicly, he hasn't told potential hackers all the steps they'd need to take to re-create his malicious app. For example, even if you use a high-end hardware accelerator, you can only try about 25,000 password combinations per second when attacking documents encrypted with Microsoft Office 2013.