Malwarebytes anti malware vs superantispyware. Malwarebytes or Superantispyware? Compare www.littleboyblu.com and www.littleboyblu.com 2019-03-26
Compare SUPERAntiSpyware vs Malwarebytes 2019

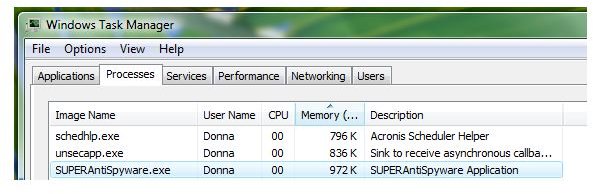
Each one scans for different things. The result was a constant race to keep up with the evolving landscape of threats as new viruses were created and released into the wild. GuiltySpark: Thank you for the reply. On badly infected computers, I tend to start with Malwarebytes, then run SuperAntispyware, then restart into Safe Mode, then run Malwarebytes and SuperAntispyware again. You encounter threats even when you are just browsing casually. You also have an option for making an account to rate how good or safe the website you are on is on WebSecurityGuard.
SuperAntiSpyware FREE And Malwarebytes FREE?
Who knows what other malware it might've downloaded that's new to signatures or whatnot. Not to validate or the opposite their test ing procedures but there aren't that much comparative reviews for the tested programs. However, services used by Hitman Pro like G Data and Emsisoft have scored well in laboratory tests. Final notes: There is no doubt that both programs are powerful and useful, however, there are some aspects that you should evaluate before installing one or another program. It works as a primary anti-malware suite which eliminates the need for a secondary software. Malwarebytes based on my experience has updated at least once usually more every day.
SUPERantispyware or Malwarebytes?
Your protection should be a top priority. However, between the two, which one is better? Keep an eye out for that. It is now generally rated as the lowest of these listed programs. Hi - This often depends on how good your settings are for Tracking Cookies and Hosts file settings. Anti-exploit measures were developed as a shield against this method of attack, protecting against Flash exploits and browser weaknesses, including new exploits that have not been identified or vulnerabilities for which patches have not yet been created. Further, most people don't understand how to use Spybot's and that feature can cause more problems than it's worth.
Compare SUPERAntiSpyware vs Spybot

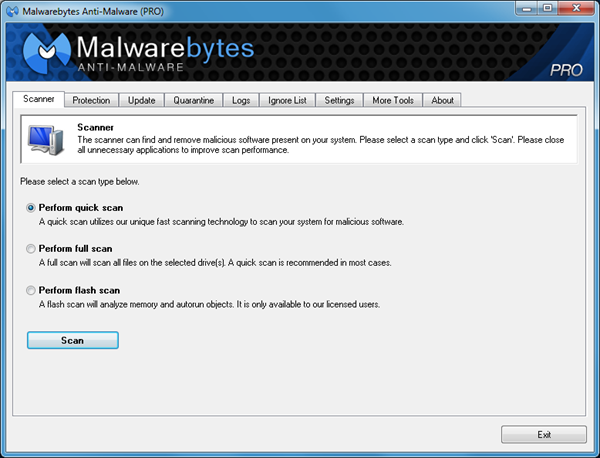
Additionally, TeaTimer may conflict with other security tools which do a much better job of protecting your computer and in some cases it will even prevent disinfection of malware by those tools. Additionally, TeaTimer may conflict with other security tools which do a much better job of protecting your computer and in some cases it will even prevent disinfection of malware by those tools. According to on the avast! Today, we are going to compare two products — Plumbytes Anti-malware and probably more known program — MalwareBytes AntiMalware. Do these basically do the same thing? The research team investigates new rogue applications and malicious files so the database is usually updated several times a day in an aggressive effort to keep it current. It does anti Ransomware and I think even an antivirus to an extent. I do not have an understanding of the registry so I will not use that. What this shows is that a single solution is not enough.
SUPERANTISpyware vs. Malwarebytes Anti malware
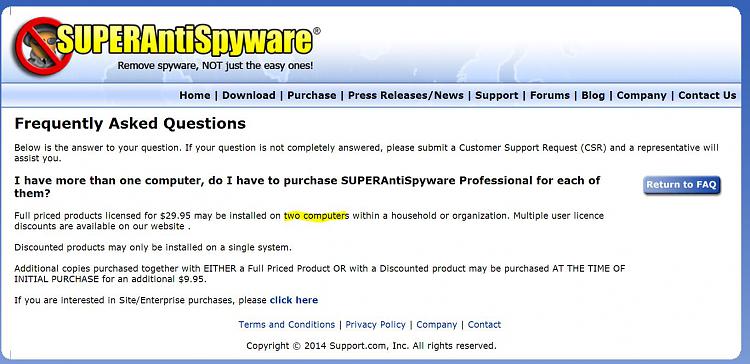
My guess: So they can sell a seperate product for more revenue. B One application may scan archives and one may not. Give the details a look, and select the best plan for your business. You will need to purchase the standalone HitmanPro. However, I am thoroughly impressed with how often the developer team at Malwarebytes releases updates definition files and how effective those updates definition files are.
Compare SUPERAntiSpyware vs Spybot

It is good to note that there are no unnecessary applications bundled during installation. If you need me to submit anything else just let me know -bradja The tracking Cookies are worthless - really are. Comparing Malwarebytes vs Superantispyware may also be of use if you are interested in such closely related search terms as superantispyware vs malwarebytes 2015, superantispyware vs malwarebytes, superantispyware vs malwarebytes 2012, superantispyware vs malwarebytes 2013 and superantispyware vs malwarebytes 2011. As they say, prevention is better than cure. I also run Spyware Blaster which is supposed to stop spyware from gettin gin your computer in the first place. If you don't have understanding how a particular security tool works, then you probably should not be using it. Traditional antivirus alone is not up to the task, as evidenced by the regular stream of newspaper headlines reporting yet another successful cyberattack.
Antivirus & Anti

In brief, signature-based antivirus is like a bouncer at the nightclub door, carrying a thick book of mug shots and booting anyone that matches. SuperAntiSpyware currently only supports 32-bit operating systems. Funny thing -2 months ago, with all this protection running I got a viruse -computer locked up and I had to reinstall windows from zip. See - scroll down and read under Freeware Antispyware Products. Alert for more real-time features. These are one hit only tools, and not vague Cleaners that have no idea of what You want to keep or remove.
SUPERANTISpyware vs. Malwarebytes Anti malware

These are one hit only tools, and not vague Cleaners that have no idea of what You want to keep or remove. Viruses are just one kind of malware. Are there some things that Malwarebytes finds that SuperAntiSpyware can't, and vice versa? It should also protect you while browsing before threats can even reach your machine. Scanning is performed quickly while other tools can take hours. Also, keep Windows, all your programs, web browsers, and web browser plug-ins updated. Spyware Terminator also has a file deleter to delete locked files.
SuperAntiSpyware FREE And Malwarebytes FREE?

However, I will not fake, lie, or create falsities to make things turn out the way I want. That means you have the option to use the mobile version without installing it. The anti-malware, along with other security suites, was tested against several samples of ransomware and malware types. You might think that the more popular program is better than the less-known one, but we suggest you not to judge hastily. Bottom line, you need more than one product to provide any sort of protection these days. It'll completely restore the server, and is more opportune for a server; at least in my opinion.
malwarebytes vs superantispyware

It has made a name for itself in the arena of free removal anti-virus tools and has even earned a reputation as a solid backup for companies that develop their own anti-virus tools. During active scanning, Malwarebytes shows you which part of your computer it is scanning for threats. Call it good to go. Give the details a look, and select the best plan for your business. In future I know what to do now to submit a sample. Both these technologies are a perfect fit for cybersecurity, especially since the number and variety of threats coming in every day are too overwhelming for signature-based methods or other manual measures.