Malwarebytes identified threats. Identified Threats not being quarantined 2019-02-16
Antivirus & Anti

C from the computer and get rid of relevant virus and trojan, please execute the procedures as stated on this page. Collected data will be sent to remote attacker for analysis. Malwarebytes finished scanning in a little over four minutes; While Hitman Pro took 11 minutes and 29 seconds. This is normal and indicates the tool ran successfully. Some security programs deemed this threat as a Ransomware with that causes high potential damage. However, the bugs also affect the company's premium product. Our mission is to ensure that everyone has the right to a malware-free existence.
Cyberthreats, viruses, and malware
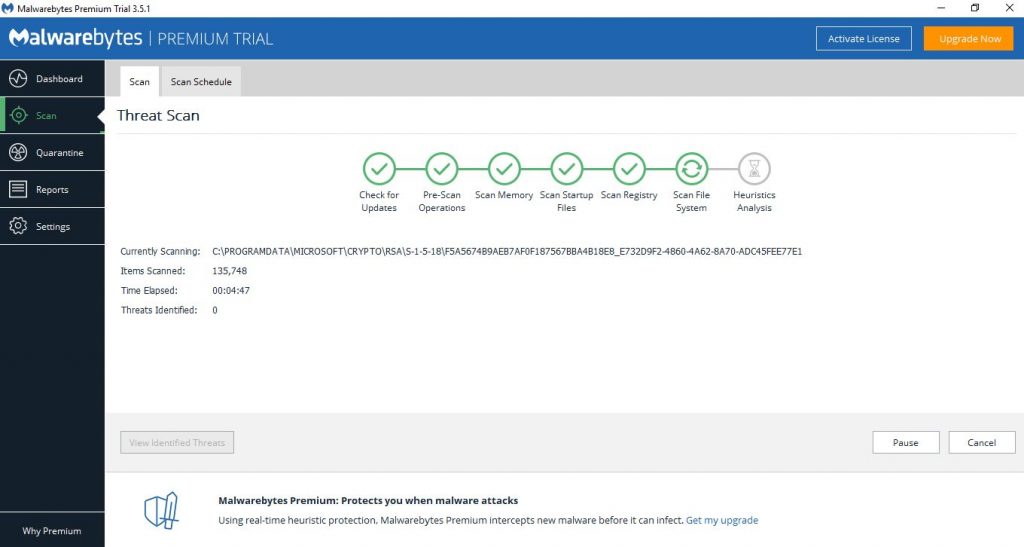
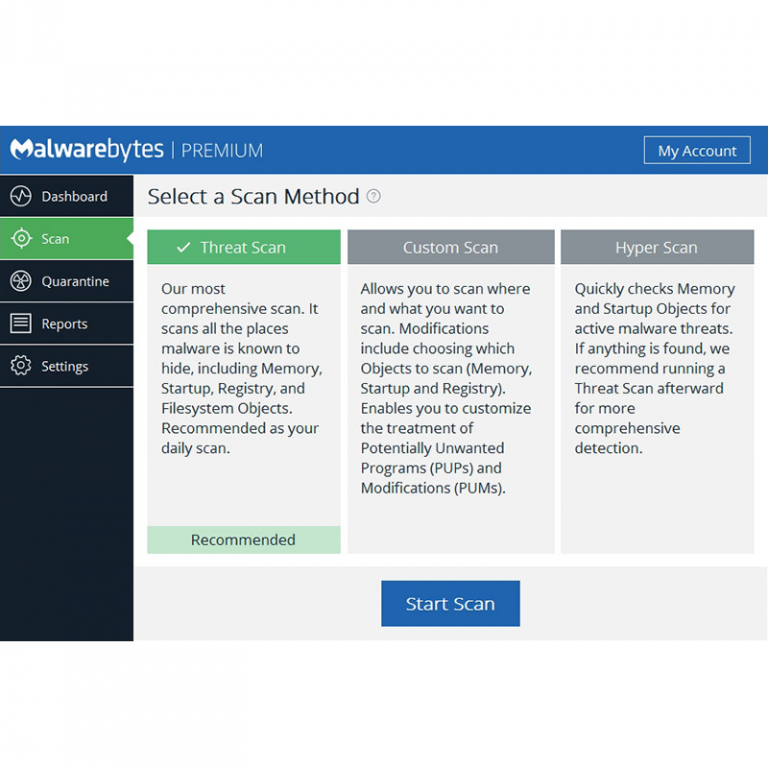
If you attempt to install Malwarebytes' and the setup program automatically closes then there is a good chance that you have an infection that is trying to stop the program from installing. From massive data breaches to ransomware attacks, businesses are experiencing what consumers have been dealing with, but on a larger scale. If you ever figure out what's going on with Malwarebytes, please post back here — I'm very curious! Acknowledgements Many thanks to and for their inputs and Vidar payload identification. Follow these procedures to scan your computer with Windows Defender: 1. Even so, new viruses that got out ahead of database updates. The result was a constant race to keep up with the evolving landscape of threats as new viruses were created and released into the wild. Both anti-malware programs ran smoothly during an active scan.
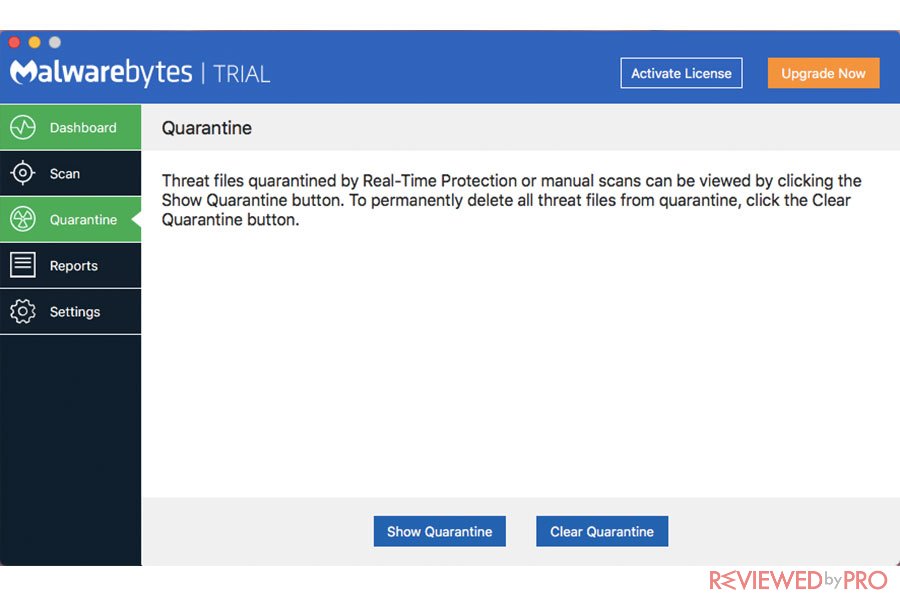
Identified Threats not being quarantined
Go to Start Repairs tab and click Start button. Either way, the resulting file must show the same behavior as the original virus. The app, known as DroidCleaner, was discovered in the Google Play app store. Although these fileless techniques have figured in targeted attacks, they have become more common in commodity malware campaigns. On a couple of positive notes, Windows Defender was able to detect and remove malware detected at the conclusion of its analysis. Carefully evaluating free software, downloads from peer-to-peer file sharing sites, and emails from unknown senders are crucial to avoiding viruses.
Trojan:Win32/Occamy.C

Malwarebytes no longer reports any threats. A user down loaded an emoticon util and a pointer changer. Ten months later in November 2016, ransomware had blossomed to account for 66% of malware payloads, an increase of 267%. We are not permitted to work on possible malware-related issues here in this section of the forum. All you have to do is visit a good site on the wrong day. The current trends with Trojans are likely to continue, while there are opportunities for criminals to exploit weak configurations and outdated assets. Both these technologies are a perfect fit for cybersecurity, especially since the number and variety of threats coming in every day are too overwhelming for signature-based methods or other manual measures.
Cyberthreats, viruses, and malware

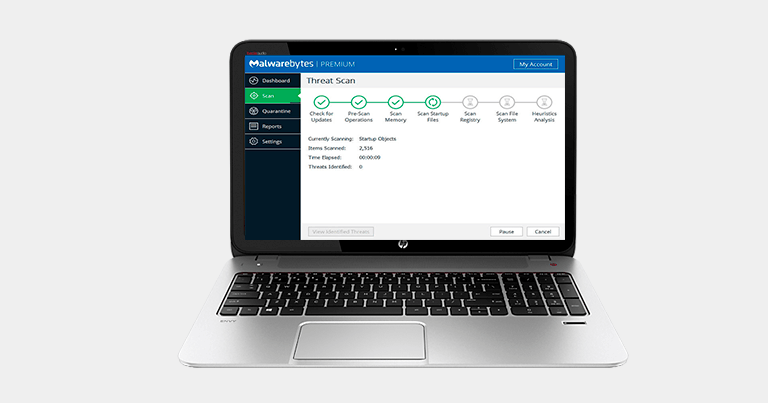
My scan has been going on for over 7 hours now and is currently scanning the Heuristic Analysis. It also has anti-rootkit removal and repair capabilities. Kovter is also able to identify and deactivate security programs that are designed to root it out. Now click on the Protection tab at the top of the screen. For this reason, it is wise to only download apps from the official store, as Google acts quickly to remove malicious apps when identified. In other words, heuristics-enabled anti-malware is proactive, not reactive. I was able to uninstall my pre-existing Malwarebytes anti-malware program, go to Malwarebytes.
2 New Malware Threats Identified

However, antivirus companies were unsure how to categorize themselves. . In the coming year, Malwarebytes is dedicated to providing the cutting-edge protection and remediation tools needed for protecting the world against the most dangerous malware now, and well into the future. After 4 scans and still not getting rid of it all, and still being unable to boot into windows, I gave up on it. From heightened risks to increased regulations, senior leaders at all levels are pressured to improve their organizations' risk management capabilities. Troubleshoot Malwarebytes Anti-Malware Below are some common errors you may run into when attempting to use Malwarebytes' Anti-Malware.
Hitman Pro vs Malwarebytes
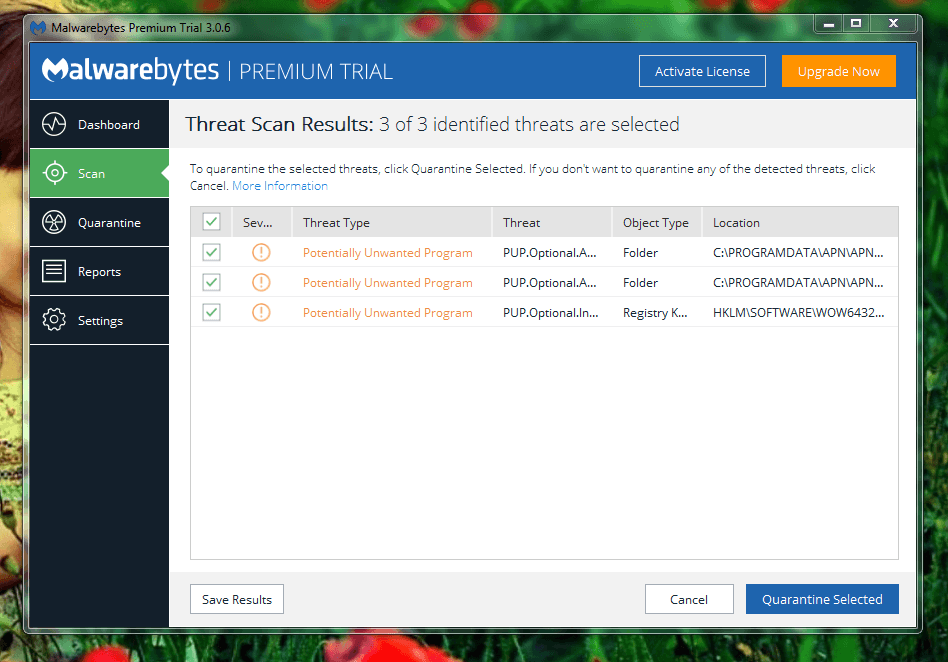
However, services used by Hitman Pro like G Data and Emsisoft have scored well in laboratory tests. Some anti-malware products can also run the suspected malware in a sandbox, which is a controlled environment in which the security software can determine whether a program is safe to deploy or not. Malwarewbytes also predicts an increase in the deployment of exploit kits that have enhanced capabilities for avoiding detection. Hello and Good Evening Everyone, I am wondering if I can possibly quarantine and delete threats detected by the Free Edition of Malwarebytes Anti-Malware. On the Home tab, click Full under Scan Options. Double Check with Malwarebytes Anti-Malware 1. Once your computer has rebooted, and you are logged in, please continue with the rest of the steps.
Types of Computer Security Threats and How to Avoid Them

Go to Step 2 and click on Check button next to 1. C is a malware that can drop malicious files onto the computer, which tend to lock files and demand payment from users in order to regain access. Ad fraud malware Ad fraud malware was also widely distributed in 2016. The attack, which specifically targeted dual-factor authentication that relies on the texting of one-time passcodes to mobile devices, proves Eurograbber's designers had an in-depth understanding of how online banking systems work. And then there's , a Trojan identified in August by Versafe. You have to have all of that information tied together. All that was saved from their abomination of a network was critical files, which were thoroughly checked before they were reintroduced to the newly built network.
Should I Delete Objects in Malwarebytes' Quarantine?
Malwarebytes came up with over 3300 infections. Save the file on your hard drive. Computer viruses have been around for decades. You may now restart Windows to complete the virus removal process. Typically, spam email messages disguising as open letter from reputable institution are used to deceive recipients.
Malwarebytes Press Center
Thanks again everyone for taking the time to share your thoughts and suggestions. In brief, signature-based antivirus is like a bouncer at the nightclub door, carrying a thick book of mug shots and booting anyone that matches. Details: The content index catalog is corrupt. As they say, prevention is better than cure. One of the program's nicest features is that it is free and easy to use.