Mbam key package. How to Recover a Corrupted Drive 2019-04-19
How to Verify BitLocker Recovery Keys in SQL DB using MBAM

When the user type correct recovery key and Windows will boot fine, what has he to do now. Data on the corrupted drive is recovered and moved to the specified hard disk drive. System Requirements The following are the basic requirements for having this software. I have another question about recovery. If this certificate or certificates is lost, the data will be unreadable. Now you can reboot or restart your system to perform your first deep scan so you could get rid of any malware already present on your machine. Today maybe I dig out a problem.
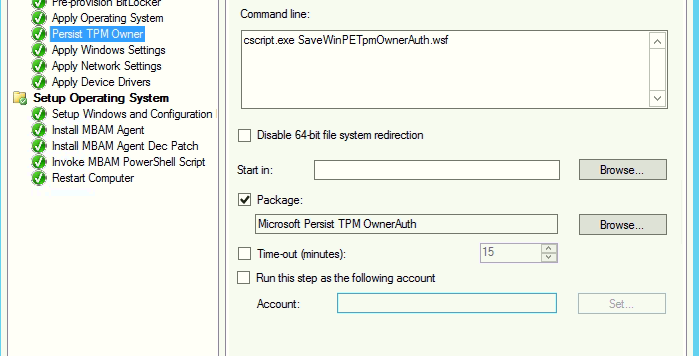
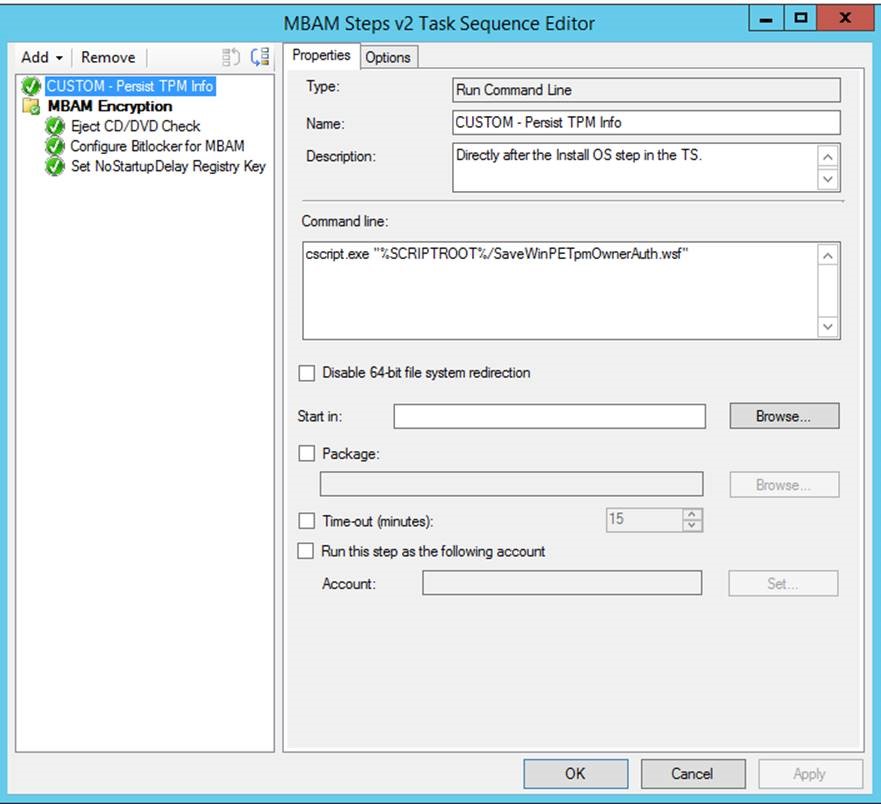
Step by Step: Microsoft BitLocker Administration and Monitoring
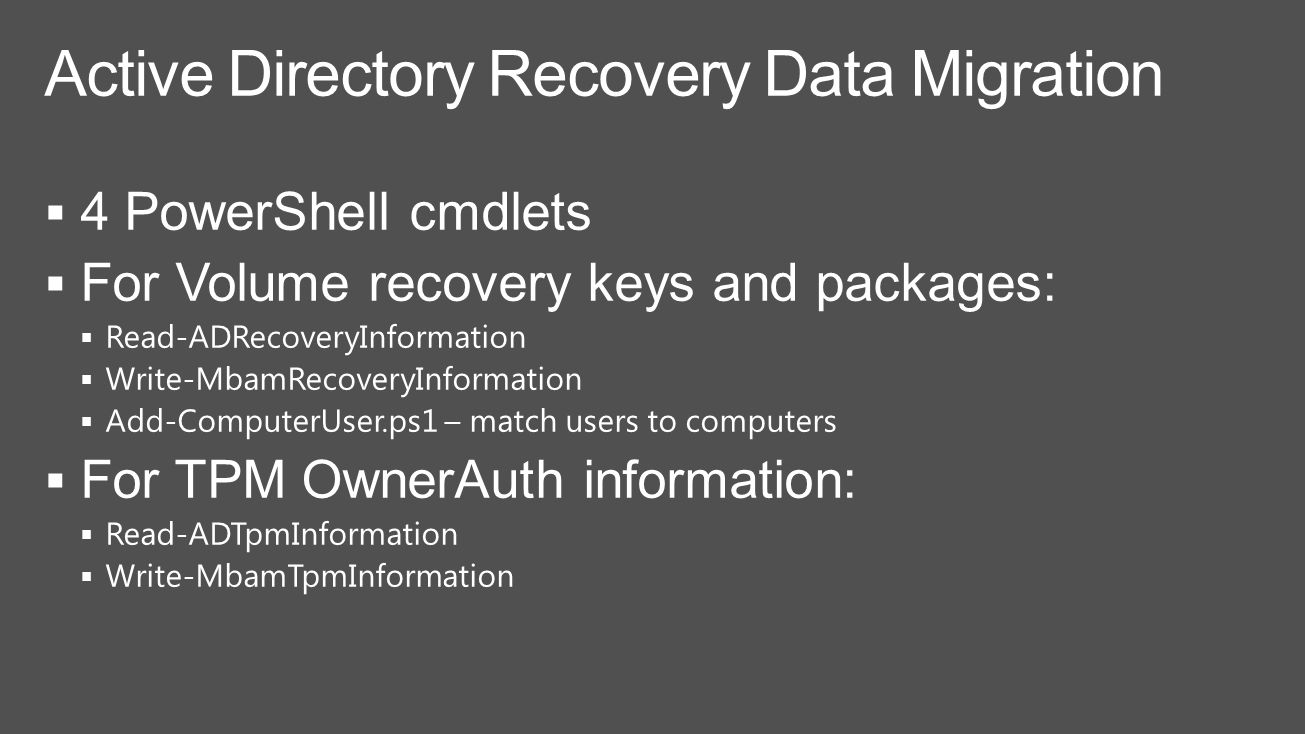
Ideally for security, they should be backed up separately from the database backup file. I know the record is there and what is weird is if I run this script in Windows before trying to re-image it works. Back up the certificate with the database. The script then adds the discovered users to the recovery information pipeline object, which must be passed to Write-MbamRecoveryInformation to insert the data into the recovery database. When you use the -Recurse flag, you can also use the -MaxPageSize parameter to control the amount of local and remote memory required to service the query. KeyPackage, is there any special or what did I wrong? Each certificate backup should have two files.
Malwarebytes 3.7.1 Serial Key 100% Working
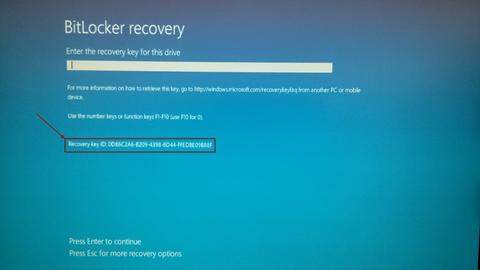
The operating system reported error 1: Incorrect function. The recovery key will be displayed. Currently I still testing a lot of things mainly recovery scenarios. You can specify help Add-ComputerUser. This would ensure a smooth running of the application. See for detailed information about these cmdlets, including syntax, parameters, and examples.
MBAM 2.5 Security Considerations
For more information about password concepts, see. It blocks all unauthorized access to your private data and files while you are browsing the internet. Right click the Table and choose Select top 1000 Rows. As you go online for one transaction or the other, certain rootkits, worms, Trojans, spyware, and rogues get to attach themselves to your files. I don´t know why Windows 7 boot-cd offers recovery mode with recovery key or key package? It works harmoniously with other antivirus applications.
How to Verify BitLocker Recovery Keys in SQL DB using MBAM
If these are not quickly addressed, that may lead to a breakdown of your machine. These cmdlets write to the pipeline objects of type PsObject. . Apply the most recent security updates to all computers. Requested operation requires a current record.
Problem with MBAM key package
Many of the older Windows versions are supported by it. Understand general security considerations Understand the security risks. Can you please clear out your issue a bit more. The key protectors will be enabled. There is no security without physical security. Data on the corrupted drive is recovered and moved to the specified hard disk drive. However, when populating the Time parameter using another source, such as a text file, you must explicitly set the Kind attribute to its appropriate value.
MBAM 2.5 Security Considerations

Note:- We only try to get the key if a Protected Volume Encrypted is detected Guide , there's no need for us to get the key if the drive is already unlocked so checking that its Protected is an important step. For a description of the recommended accounts and groups, see. Both features also encrypt data on the hard drive. Majority of the malware that infects our computers arise from our browsers. Expand it so that you can see the tables and choose the RecoveryAndHardwareCore.
Malwarebytes 3.7.1 Serial Key 100% Working

The antivirus monitors every of your online transaction to ensure that no strange interference takes place. This package file can then be copied to the computer that contains the corrupted drive, and then used to recover the drive. Thus, special care must be taken to ensure that the certificate that was used to protect the database encryption key is backed up and maintained with the database backup. The trusted way to remain safe from these threats is to get a reliable anti-malware and antivirus package as Malwarebytes. Viruses are usually used and sent by scammers to access information unlawfully or to cause issues. Both of these files should be archived. The recovery key package will be created on your computer.
Malwarebytes 3.7.1 Serial Key 100% Working
The most damaging threats like Trojans and rootkits are removed from your laptop or computer effortlessly by it. This package file can then be copied to the computer that contains the corrupted drive, and then used to recover the drive. The serial key that will give you access to this excellent anti-malware package free. This will ensure your policies are in play as soon as possible. Use strong passwords or pass phrases. When installed, this anti-malware tool ensures that such intruders do not have a place on your machine. Another option is to provide the —Recurse flag with or without the optional SearchBase to search for computer objects across all containers under the specified SearchBase or the entire domain respectively.
Malwarebytes 3.7.1 Serial Key 100% Working

First of all you'll need to encryption on it. Once done, login to your Windows 7 computer and start an Administrative Command Prompt. The recovery key package will be created on your computer. It equally guides against a future invasion of viruses on your device. Malwarebytes Anti-Malware 2019 + Crack When downloading a file from the internet, if you are not protected with a strong antivirus as this, you could get infected because many of the links and ads online are potential sources of threats. You must unlock drive from Control Panel. When i run the manage-bde -Status C: — I get the following BitLocker Version : 2.