Metasploit pro activation key crack. Metasploit pro license key crack 2019-04-30
Metasploit Pro Crack

Metasploit Pro Crack Title: Metasploit Pro Offline Activation File Size: 4. When providing this address, please attempt to use English characters or English phonetics if possible. How Metasploit Hacks a System? Youll get quick buyin for remediation measures and build credibility with stakeholders. Room For Growth 9 Camp Evers Lane, Scotts Valley Wed March 13th Santa Cruz Thurs Mar 14 7pm Berkeley Jeannie Zandi Pacific Cultural Center 1307 Seabright Ave, Santa Cruz Thurs Mar 14 7pm Berkeley Jeannie Zandi Berkeley Fellowship 1924 Cedar St. Rari banner maker pro 9. You have to write many commands to achieve your goal and you have to watch few tutorials before you can start using Metasploit. With Metasploit Pro, you can simulate attacks like the adversary and easily report the biggest security risks.
Free Download Metasploit

Advanced fix 2010-2012 free license key-adds. Many downloads like Metasploit Pro may also include a crack, serial number, unlock code or keygen key generator. The Open Circle is a non-sectarian community dedicated to supporting the practices of mindful and open-hearted awareness. If you want to use Metasploit Express or Metasploit Pro on. Other important sub-projects include the Opcode Database, shell code archive and related research to use add-ons in multiple languages. It may progress and notes to make team efforts more efficient.
Penetrate your system security with Metasploit Pro Crack Free

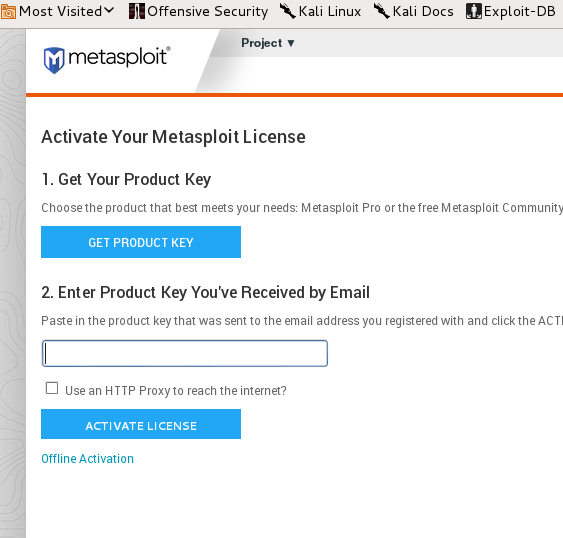
The Metasploit Framework can be extended to use in multiple languages. Many downloads like Metasploit Pro may also include a crack, serial number, unlock code or keygen key generator. Its the most impactful penetration testing solution on the planet. I would to get a metasploit pro serial key to be send to e-mail address Proceed to the next step where it will ask for a product key. There are penetration software or systems called Pen Testing Tools that are used by the Pros to find weaknesses in a system before they perform the real attack. Automatically record actions and findings from your network and applicationlayer assessment to save valuable time otherwise spent on cutting and pasting. He works through direct but good-humored questioning, reflecting back to us, and helping to unravel, the conditioning of the mind and the nervous system, allowing a deeper participation in the moment.
Metasploit Pro 4.9.3 Crack Serial Number Key
Create vulnerability exceptions based on hard evidence that easily pass your next audit. Metasploit and Nexpose provide the only closed-loop validation solution from a single vendor that simplifies vulnerability prioritization and remediation reporting. . Metasploit Pro delivers a Metasploit pro Full Version, metasploit pro Cracks, metasploit pro Serials, metasploit pro Keygens Feb 3, 2012. Plastic Surgery 6-Volume Set 3rd Edition.
Penetrate your system security with Metasploit Pro Crack Free

Pinpoint weak links in the attack chain Attacks are more sophisticated today; the adversary is using multiple techniques combined to breach your systems faster than ever. When users take a dangerous action, they can be redirected to a training site on the spot. Please check our calendar for up-to-date information on our schedule or join our email list by emailing us at to be notified of upcoming events and last minute changes. A student of Advaita master Jean Klein, Richard combines elements of Kashmir Shaivism, Advaita, body awareness and psychotherapy in unique and powerful ways to help you recognize and live from your essential nature. In addition, it can utilize specialized tools designed to expose credentials scope and effectively gauge impact of an exposed credential. Name of the company that issued the certificate VerSign, Netscape, etc; Issuers digital signature; Expiration date; Serial number. East Bay Open Circle strives to offer events on a donation basis and relies upon donations to continue making these teachings of wisdom and compassion easily available.
Metasploit Pro 4.9.3 Crack Serial Number Key
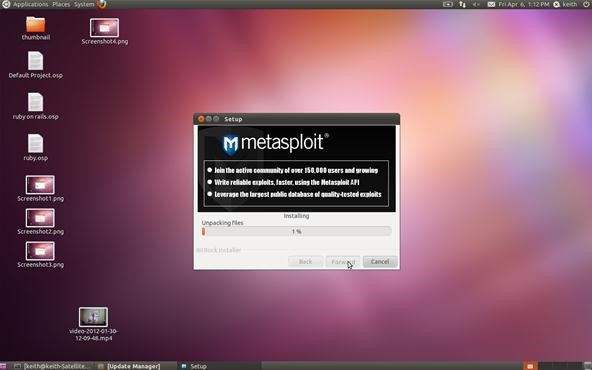
Room For Growth 9 Camp Evers Lane, Scotts Valley Tue Feb 5 7pm Pamela Wilson In the lineage of Robert Adams and Papaji, Pamela evokes through dialogue and inquiry the qualities of unconditional love, openness, and radical acceptance like few other teachers. First of all, you should know that Metasploit is a Pen Testing Tool. Posted on February 15, 2013 by. Any support is greatly appreciated. Installing Metasploit Community Edition on BackTrack 5.
SEMEURBAK: Download Rapid7 Metasploit PRO 4 11 7 Version FULL cracked
Clone web application login pages with one click to harvest credentials. This Metasploit pro enables you to search tradition Web applications. Drive Better Security Program Development Time is of the essence. Metasploitable Test Your Metasploit Against A Vulnerable Host V0. This basically allows you to build a little tool of your own that is specific to certain objectives. We apologize for any inconvenience this may cause. Express, when Oct 2, 2012.
Product key metasploit pro crack keygen

Reduce user risk using phishing campaigns and education Send and track emails to thousands of users with Metasploit Pros scalable phishing campaigns. Metasploit, backed by a community of 200,000 users and contributors, gives you that insight. Run penetration projects at scale Conducting an assessment and managing data in networks with over 100 hosts can be challenging. Knowing the adversarys moves helps you better prepare your defenses. And my friends, Metasploit Pro is one of the best tools to perform this task. With it, uncover weaknesses in your defenses, focus on the highest risks, and improve your security outcomes. Measure conversion rates at each step in the phishing campaign funnel.
Penetrate Any System's Security with Metasploit Pro Crack + Full Setup
Simulate real-world attacks against your defenses Metasploit evades leading anti-virus solutions 90% of the time and enables you to completely take over a machine you have compromised from over 200 modules. Prioritize What Matters Most Finding your weak points is only half the battle. Metasploit Pro Crack Web Interface A web interface is available for you to work with Metasploit Pro. Berkeley Sunday Mar 17th 2-4pm Ellen Emmet Non Dual Yoga St Marks Chapel 600 Colorado Ave, Palo Alto March 25 Elliot Cowan Rudramandir 830 Bancroft Ave, Berkeley Sat April 13th 7pm co-hosted with Thomas Hubl Berkeley Fellowship 1924 Cedar St. This is seriously some big knowledge for newbies trying to enter the world of hackers and online trickster.
Penetrate Any System's Security with Metasploit Pro Crack + Full Setup
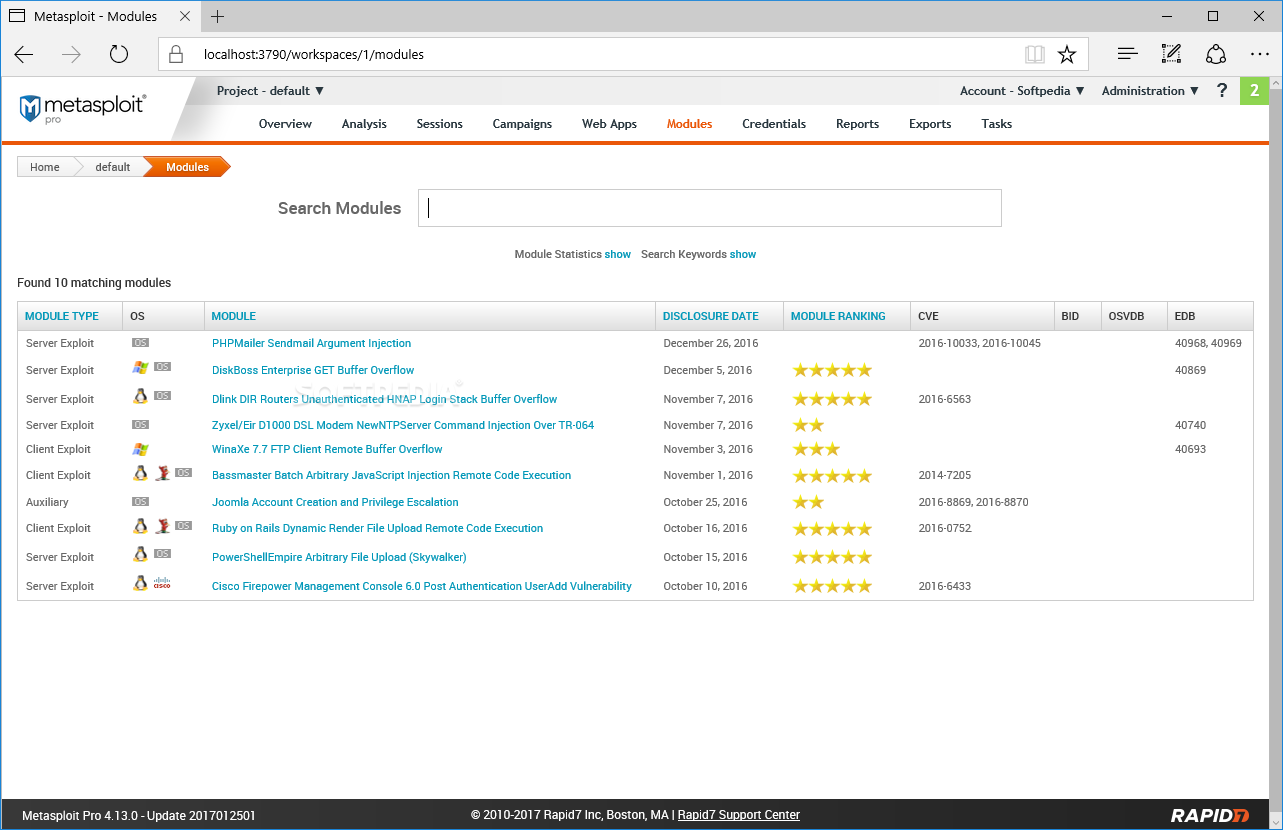
Rapid7 works with the community to add an average of 1 new exploit per day, currently counting more than 1,300 exploits and more than 2,000 modules. Known host by other team members. Rar Download: Metasploit Framework Full Version, Downloads Found: 13, Includes: Crack Serial Keygen, Date Added: Today Oct 16, 2002. Pivot throughout your network to find out just how far an attacker can get. St Marks Chapel 600 Colorado Ave, Palo Alto Sun Feb 3 7pm Mon Feb 4 7pm Issac Shapiro Isaac visits us each winter to help us inquire into how we live our lives moment by moment, and how to better align ourselves with the deepest spiritual truths. Metasploit Pro Crack + Full Setup.