Mifare key cracker android. How to Crack Mifare Classic Cards 2019-03-06
Mifare brute force android
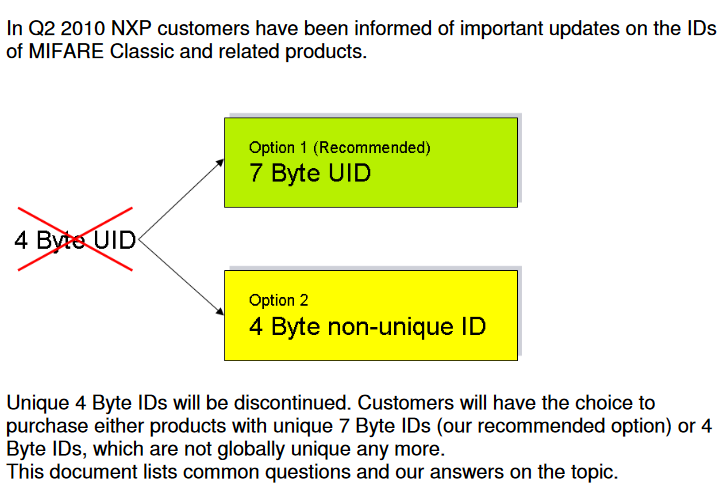
Did Mifare change the keys in any way? These are a particular type of processor-embedded cards, and are different from credit cards. A better way to do this would be to encrypt any data that you need to store on the card. If you have not updated your proxmark3 in a while, I suggest you do so. Be careful when writing a direct block because if you overwrite the last block of a sector the one containg the keys , your tag will be irreversible damaged. For connection instructions on the Raspberry Pi please refer to. There will be no brute-force attack possibility in this application.
Mifare Classic Offline Cracker
But I tend to agree that some devices are too slow! If you happen to find any information around that, please share. The decryption breach triggered a firestorm of controversy, and Dutch authorities apparently have halted the rollout and are investigating the vulnerabilities. As this is open hardware, , which have variations, such as different antenna connectors, in-built antennas, and operating from battery without a host. And an even better way would be to communicate with a server and have it validate the transaction. The malicious Android app detected as was designed to attack s and distributed online through forums and blogs. The cable will simply work after that black wire is ground.
Hacking RFID payment smartcards with an Android AppSecurity Affairs
There is also an active - active mode where both endpoints can send data and need to be powered seperately. It's easy to get the software built, but it's a significant investment to buy the hardware. Perhaps the key is passed to the driver then its decrypted? I can't give email support about this process either, or do a crack-by-mail service. There certainly was a large number of completely dead cards for a couple of weeks in 2010. Once the reading is finished, I get a Read Failed! Analyzing the case of card hacking the experts highlighted that the they were Mifare smartcards, a contactless and proximity technology that is wide spread billions of Mifare smart card chips are available on the market. On some of the transit card pages, there may be a way to check based on the appearance of the card -- but these are specific to each agency.
How to Crack Mifare Classic Cards
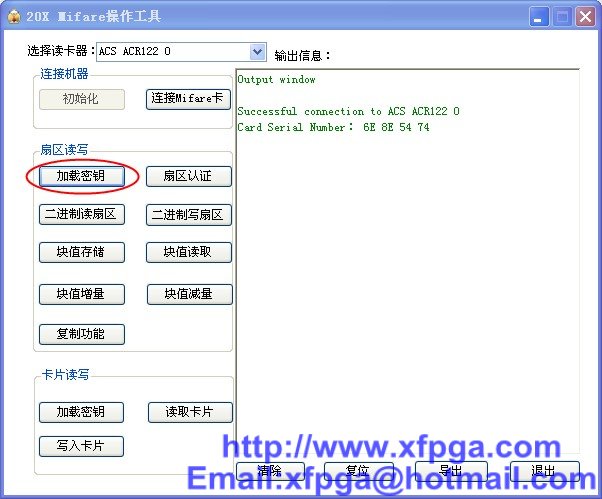
Here are the basics to set your machine up for getting the access keys. The only thing I remembered about emulating Mifare Classic on Android is this Sackoverflow post: I wish you the best for your work. I am able to perfectly read a blank mifare but where can I write blocks and bytes to modify? So far I have not managed to crack the scheme. . I've attached strace to com.
How to Crack Mifare Classic Cards

Unfortunately, there's not always an easy way to tell what card you have, so at worst you may be out some money. You need a rooted device in the least. The credits are located in sector 12 block 2 counting starts at zero. The vending machine shows you the credits left on the tag when holding it to reader. Using the write option you can write exactly one block back to the tag, or reflash a complete memory dump. You can get the latest libnfc version from. You may need to be in the dialout group in order to write to the serial device.
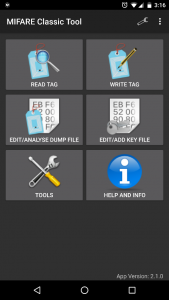
MIFARE Classic Tool for Android

The experts suggest to customers to periodically check the balances of their accounts and take care of the type of cards they are currently using. Decrypted, the cards can be counterfeited, and users' personal and bank data is exposed. At the time of writing the current version was 1. There is a newer revision of the card, Mifare Plus, which can emulate Mifare Classic cards without the with less security flaws. Sadly not every Android Phone supports these Mifare Classic tags. The active device scans for the passive one and establishes a connection on contact. That might add to the complexity if so.
How to Crack Mifare Classic Cards

It seems that you have to keep the phone and the card touching for a time, until it reads the card, that is why I got that error popup. Nohl wrote his own optical recognition to refine and clarify the images, and then patiently worked through the arrangement of the logic gates to deduce the encryption algorithm, a task made possible by the fact that the Mifare Classic relies on a secret key of no more than 48 bits. I got a trash card, a card that I have to use to open the underground trash bin, that I want to clone. If you can post new versions in this thread!!! If you are into it, any kind of help would be much appreciated. The physical limitations of the libnfc compatible usb devices, are just too slow in my experience. In your main activity's onCreate add: public void onCreate Bundle bundle {.
MIFARE Classic Tool for Android
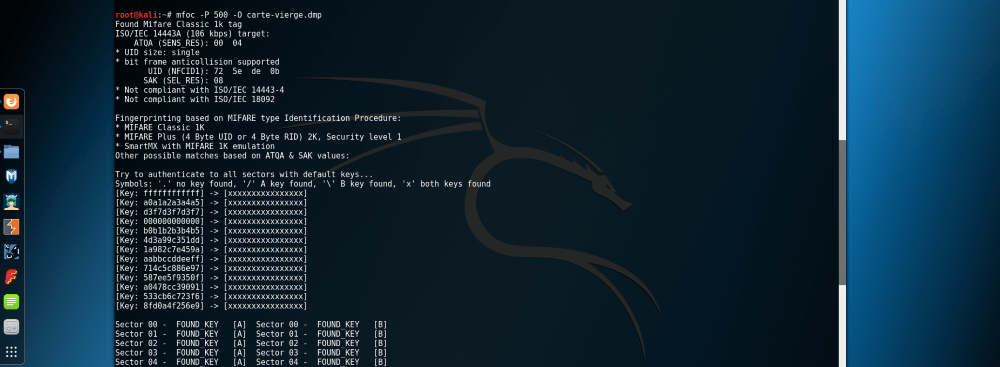
This doesn't use any of the instructions described here, instead. It allows to crack sector keys using dictionary or brutal-force attack. You'll need current libnfc for the second tool, so this will walk through building it in a different prefix. Sector: 14, type B, probe 2, distance 18502. Does anyone know of the Android Mifare Decrypted call? I'd recommend trying to build the software before committing to a hardware purchase. While the project started around 2007, it is still has active development from a small but dedicated community. How much will it cost? Block 0 88 01 00 84 00 04 b0 1a 00 00 5d 00 01 05 00 f1 Block 1 01 01 01 ee ee ee ee ee 00 00 00 00 00 00 00 00 Block 2 00 01 59 01 00 6f 00 01 00 00 00 00 8c c3 00 00 Block 3 a0 a1 a2 a3 a4 a5 1e 11 ee 5a ad 4f b3 33 88 bf We can verify this block by buying something from the machine or put some more credits on the tag and then read the appropriate sector again.
Mifare brute force android

If you happen to find any information around that, please share. On a default Android build, as is, it's not possible. Google Play can indeed be installed, but somehow it is impossible to add a Google Account to the device. Mifare Ultralight C Needs more info -- Metrodroid can't authenticate with these cards yet. That can only mean that it uses an incorrect key for this type of card.