Most common school admin passwords. How To Get Past my School's Admin? 2019-02-08
10 Major Challenges Facing Public Schools

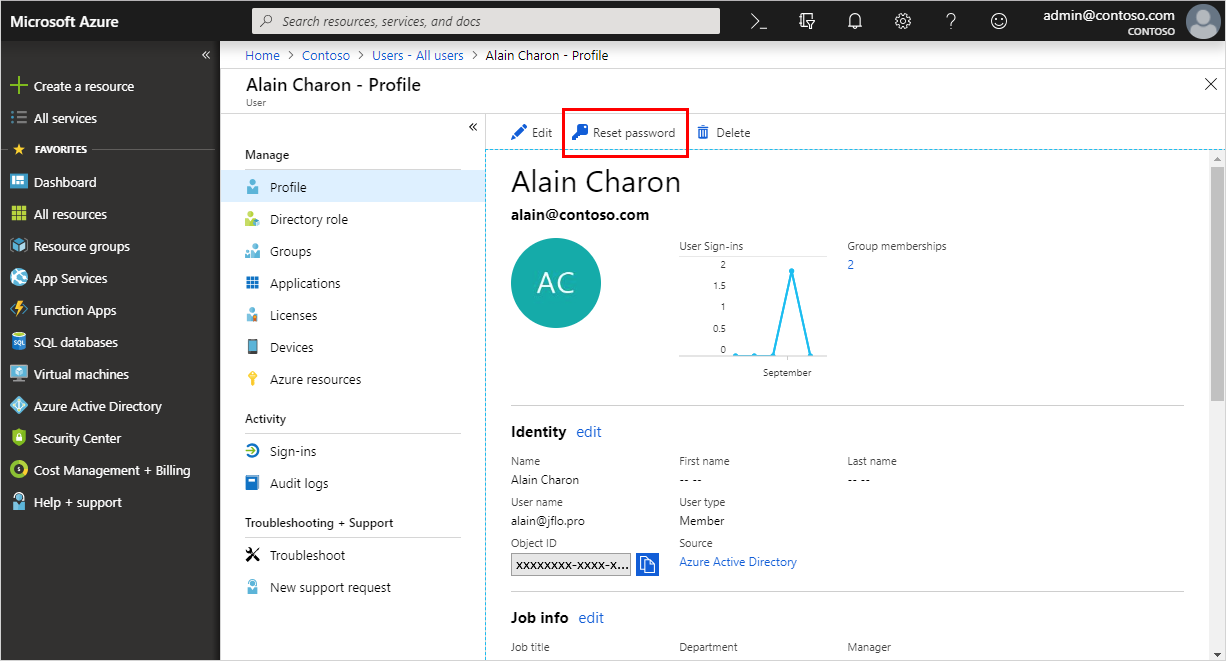
However, developing a plan to take schools in the right direction is easier said than done. With a laundry list of challenges to face, now is the time for educators, parents and lawmakers to come together and begin to find solutions — for the benefit of all students in public schools today. Technorati reported last fall that 22 percent of the children in the U. Some common requests from school users include automatically populated school- and district-level dashboards, paired with instruction-related data points like digital academic reports. If issue persists, also try this: Try to save the password in credential manager and check. Asking for administrator password that they never set.
CAPEC

To bring you the best content on our sites and applications, Meredith partners with third party advertisers to serve digital ads, including personalized digital ads. Here in Missouri unauthorized use of a network is a felony. Thank You Anup karkal I understand the frustration of some of the other users on this post. Similarly, traditional subjects for the education of society's elite would. I can understand academic sanctions, but not criminal charges. If the software is of legitimate use to the school and is properly licensed, the Admin should have no issue installing it for you. These issues were seen more frequently at the secondary school level, rather than the primary grades.
How To Get Past my School's Admin?

Right now I am trying to install Utorrent, everybody else has managed to get it on there, and I must know how!!! Unfortunately school staff need to be aware that passwords are only too easy to be copied and misused. Minority students, those living in poverty and male students appeared to benefit from smaller classroom sizes the most. Hi, Thanks for the update and response. Most schools in my area rural, decently well funded have 1 tech for every 750-1000 computers. It will serve you better than anything you learn in a trickle-down bureaucracy! One that I never set. For example, I ate all the chocolates and candies! Do not use the same password twice Never make the mistake of using the same password for all your online accounts.
Most Common Passwords list
A misdemeanor would be enough… if it came back for a round 3 then maybe a felony. However, this is a problem, because I wish to install many things that it is blocking. From bullying to book bans, this is a comprehensive look at some of the most oft-debated issues. Instead of making such a fuzz about a kid doing something like that, why not encourage him to help make a more secure computer environment? These relationships are defined as ChildOf, ParentOf, MemberOf and give insight to similar items that may exist at higher and lower levels of abstraction. Create a password that is not less than eight characters Having a long password is often the best strategy to make it difficult for the hackers or algorithms to crack it. You can find much more information about your privacy choices in.
Awecomm’s Top 10 Worst Passwords of 2017

Chances are that someday you may end up giving important information such as your credit card details, without thinking about securing your account with a strong password. Another priority is highly secure and compliant storage for personally identifiable information, financial data and fundraising activity. Press Enter and select a restore point before the account got deleted. How can consumer protect themselves? Both wireless routers and wireless computers contain transmitters that send information back and forth through the air. Now, consider that all long-term over 10 years , case-control studies on cell phones have found an increased risk of cancer.
Modern methodologies for classroom IT management: How to deploy school technology that works for everyone
It somewhat makes sense since there was never a password set up that hadnt been already tried previously. I apologize for the inconvenience caused. Many areas of the country are facing classrooms that are literally busting out at the seams. According to the , the U. In 2013 an Israeli cell phone company settled with a customer who developed brain cancer. In order to be fully transparent about the radiation emissions, not only do we need to consider the radiation emitted from routers, but we also need to examine the radiation emitted from the wireless devices that are being held near the body.
Most Common Passwords list
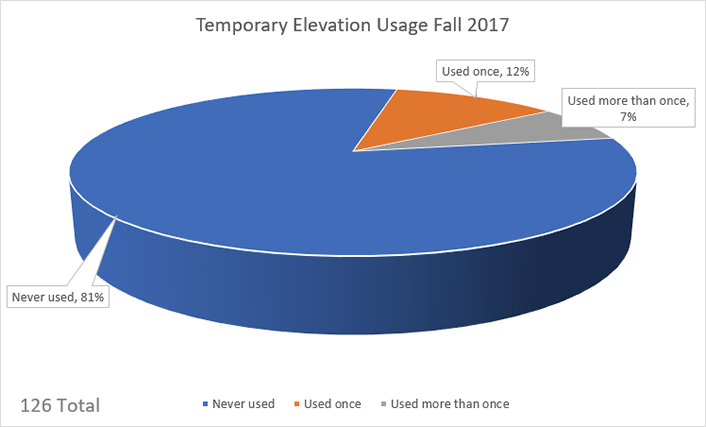
Here are few important tips that can help you create a strong password. The Likelihood provides information about how likely the specific consequence is expected to be seen relative to the other consequences in the list. If each student installed and ran uTorrent, even a ping could not get through as a bunch of P2P machines will literally crash many firewalls, as they have session limits. Accessing a prohibited system is illegal for good reasons. Refer to the steps below: 1. He could have done more.
Most Common Passwords list

Children are not just little adults, they are much more sensitive beings. Everything project Abacus needs to operate already exists in every modern smartphone. That is pretty simple, isn't it. The Scope identifies the security property that is violated, while the Impact describes the negative technical impact that arises if an adversary succeeds in their attack. In fact, it sounds like the boy has been treated as befits a kid doing dumb things.
WiFi in Schools

Original title: Locked out of Windows 10, with a twist. Hi, seen a bunch of folks locked out of their computer with Windows 10. Another problem is that users would pick very simple common passwords e. Especially risky is using the same password for entertainment sites that you do for online email, social networking, or financial service sites. Workers respond to that which is measured, thinly stretched workers even more so; monthly or quarterly reports should include some measure of intrusions, both failed and successful.
Windows 10 asks for administrator password

Hackers once know your login id they will start using passwords from the below list of most common passwords. This section features articles on school segregation, religion, over-crowding, civil rights, and green technology. Technology has given bullies even more avenues to torment their victims — through social networking, texting and other virtual interactions. Some estimates put poverty levels for public school students at 25% in the not-so-distant future. Above all else he is committed to the success of the team, helping Awecomm optimize performance and deliver exceptional results. Plus a short speech saying they should, too. None are perfect solutions, but each is better than using the same sucky passwords that make the list of worst and weakest passwords year after year.