Mpress v2.12 unpacker. How to decompress a script compressed with mpress 2019-05-08
PECompact
Its shortcomings just proved the need for people to collaborate in this project. Replace the signature value with the contents of code. Of course is much more useful where inline patching is not possible. The possibilities of open architecture compensate these limitations. Remember to free the allocated buffer! While migrating from Delphi 7, I have a program whose. You can easily see where the resource mapping was moved from the original code.
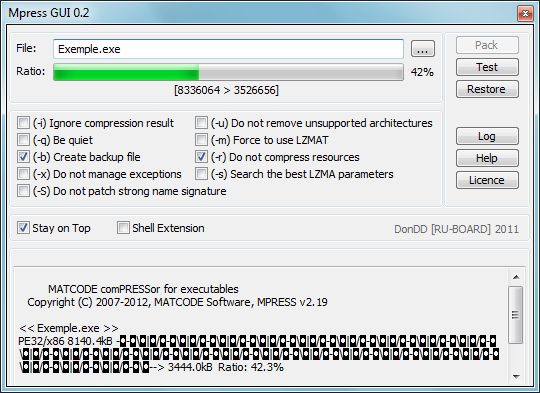
MPRESS .NET compressor

The latter is very important to me. Going to the signature element, we will retain the start attribute of ep since we require our unpacker to start from entry point ep. You must patch the header check for. It detects if your system language is english or spanish before showing you all strings. And we will describe each one in the next section.
Trustwave Unpacker Release Notes

Armadillo Version support has been removed. If so, what is wrong with mpress, or why is upx better? I love reverse engineering and more especially writing tools and articles about it. This tool rebuilds and entire relocations section whilst debugging the process. Welcome to NulledBlog Register now to gain access to all of our features. The above changes are required to give users information on the executable being scanned on the command window. Subjects such as stolen source code and pirated software are never acceptable and will always be removed.
Category:Automated Unpackers
It is ironic though that a company that aims to provide the best file analysis and reversing tools is producing superior protection tools. Is Want what I want when it comes to a build too, or has Want been found wanting at least in comparison to something else? Ok, so you want to compress, but need to pick a compressor. The cmp, je, and jmp should speak for itself. Using the command line above results to the output seen below: TitanMist Output Now, we require the memory to be dumped to a file. All troubles found when unpacking any target, please let me know in any of the reversing forums where this tool could have been released. MalZilla is a useful program for use in exploring malicious pages. If you experience any problems running the program, you may need to download and install Microsoft Visual C++ 2013 Redistributable Package x86 available here: Visual C++ Redistributable Packages for Visual Studio 2013 New BeaEngine.
MPRESS

You can safely unpack malware for further investigation without the risk of damaging the system. Compared to other executable compressors, we are either better or roughly equal in compression ratio. If the latter were true, you wouldn't be able to run it. I want to run a Delphi generated exe from php. Neither the author nor Trustwave shall be liable for any loss of profit or any commercial damages, including but not limited to direct, indirect, special, incidental, consequential, or other damages. This is a technical community, so pointing out technical flaws is certainly within the realm of discourse, but please try not to be an asshole when you do.
Unpacking mpress’ed PE+ DLLs with the Bochs plugin
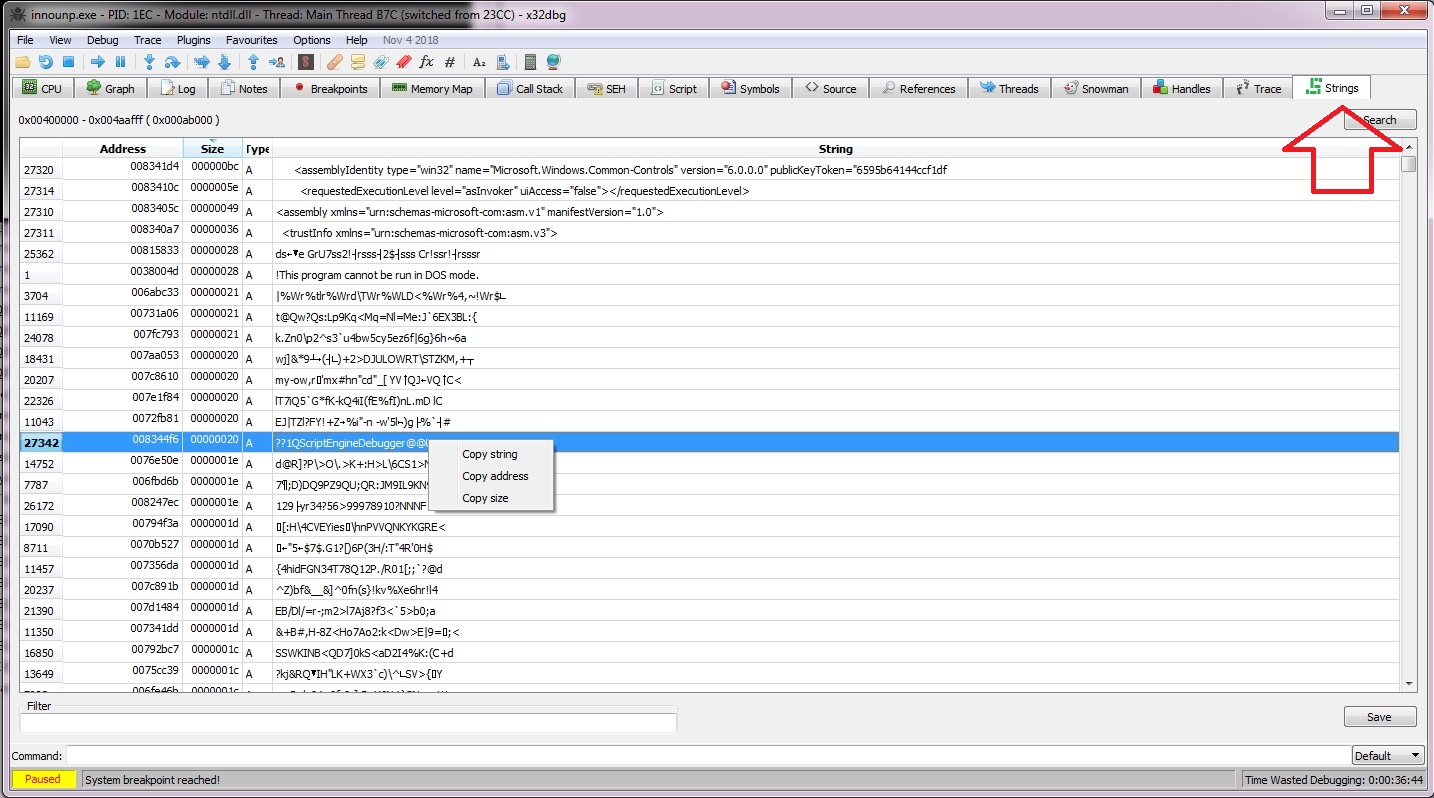
But I'm not so much worried about it, because it sometimes marks even regular executables made with Delphi as infected too. I'm happy to say that my protected executables always pass all the tests successfully that is, being reported as clean on virtustotal. The code go target is followed by two sto which represents doing F4 and two F8 in OllyDbg. That is a weird way to work, always save your code. Copy the code to C:TitanMistTitanMistunpackerstitanscriptmpress.
GitHub
New built in hex viewer. Seemed to good to be true. It's purpose is to detect exploits that target browser and browser plug-in vulnerabilities. No part of this document may be reproduced in any form or by any means without the prior written authorization of Trustwave. Imagine yourself speaking your comment in a public place to the person's face when you write it. Our goals are the same as yours; allow legitimate application use and deter illegitimate use. In its later stage, it can make some of the usual tools irrelevant and obsolete.
PECompact

First question: do you have to compile it,Yes,I can't use the script I made other way. It is really worth it and it is also open source! It monitors all the memory writes and log up to 10 previous Eips and saves the last accessed and the last modified place in memory. Name VirtSize VirtAddr SizeRaw PtrRaw Flags Pointing Directories -------------------------------------------------------------------------------------------. WriteProcessMemory, write decrypted chain into game. False reports and detection where other tools fail are history. Also listed in: More details: Tool name:. Driver also installs hook in ntos! Has an assembler and a disassembler from and to mnemonics.
PECompact

I found one more which looks promising. This document is protected by copyright and any distribution, reproduction, copying, or decompilation is strictly prohibited without the prior written consent of Trustwave. The bpgoto is used to pass the control to the assigned breakpoint handle. This keeps the bad guys from using the compressor, and maintains all the benefit for the good guys. I can think of two other applications to link into this new section. Please instead post these links to not affiliated with or endorsed by the moderators of.
MPRESS .NET compressor

With cloud and managed security services, integrated technologies and a team of security experts, ethical hackers and researchers, Trustwave enables businesses to transform the way they manage their information security and compliance programs. Our record speaks for itself. This tool is working for 1+ year now as private but suffered big and important updates along the way. The advice and strategies contained herein may not be suitable for your situation. I use Total Commander and it its internal file associations and it works for me. Detect It Easy has totally open architecture of signatures.